March 2017 Patch Tuesday has been in the spotlight since it was rolled out. Cumulative updates caused quite the havoc. In the meantime, a privately reported flaw given the CVE-2017-0022 identifier has been patched. TrendMicro reported the vulnerability to Microsoft in September 2016.
The flaw was exploited in the AdGholas malvertising campaign and was then implemented in the Neutrino exploit kit. Researchers say that CVE-2017-0022 took the place of CVE-2016-3298 and CVE-2016-3351 in the campaign as the two flaws were addressed in previous updates.
CVE-2017-0022 Technical Overview
MITRE Description
Microsoft XML Core Services (MSXML) in Windows 10 Gold, 1511, and 1607; Windows 7 SP1; Windows 8.1; Windows RT 8.1; Windows Server 2008 SP2 and R2 SP1; Windows Server 2012 Gold and R2; Windows Server 2016; and Windows Vista SP2 improperly handles objects in memory, allowing attackers to test for files on disk via a crafted web site, aka “Microsoft XML Information Disclosure Vulnerability.”
CVE-2017-0022 Exploited in Malvertising and Phishing Attacks
If CVE-2017-0022 is exploited it could be used in phishing attacks to trick users into visiting malicious websites. If the malicious attempt proves to be successful it could lead to unauthorized access to sensitive information. The attacker could also be able to detect the type of security software running on the targeted system, especially solutions that analyze malware.
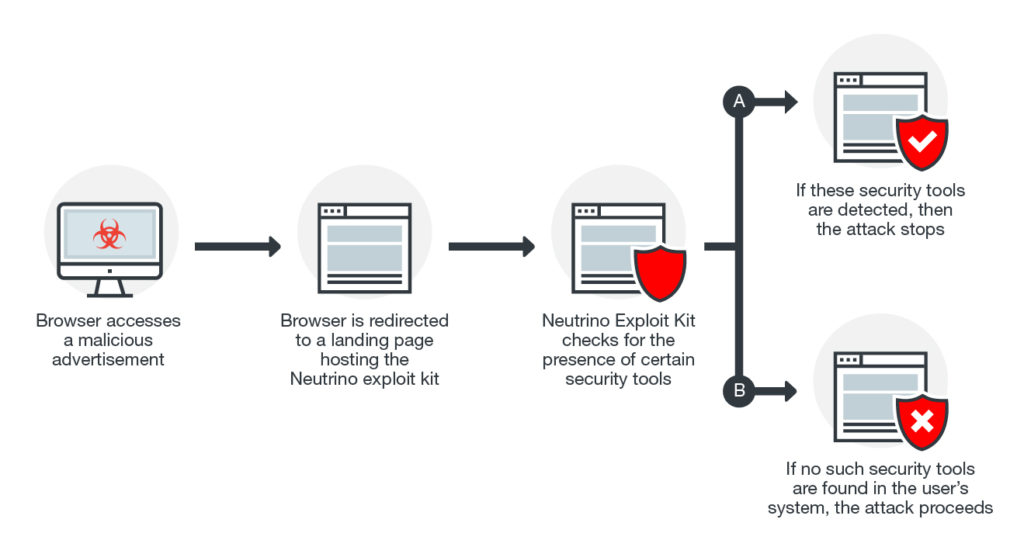
Here is how a malvertising campaign built on this vulnerability looks like:
Related: CVE-2017-0016, CVE-2017-0037, CVE-2017-0038 – What Are the Mitigations?
Other recent vulnerabilities in Microsoft are CVE-2017-0016, CVE-2017-0037, CVE-2017-0038. They brough to light the employment of Intrusion prevention system protection (IPS), as pointed out by TrendMicro researchers. IPS, also known as Virtual Patching, helps protect against vulnerabilities even in cases where patched have not been released yet. The three Microsoft flaws were located in the following components: Core SMB service, Internet Explorer and Edge browsers, and the Graphics Device Interface.