The article will help you to remove Findgofind.com effectively. Follow the browser hijacker removal instructions at the end of this article.
A dangerous browser hijacker called Findgofind.com has been found to infect computer users worldwide. The victims report serious security and privacy issues when accessing the malicious service. It is linked with other criminal services that are used to harvest sensitive data from the victims.

Threat Summary
| Name | Findgofind.com |
| Type | Browser Hijacker, PUP |
| Short Description | Every browser application which is on your computer will get affected. The hijacker can redirect you and show you lots of advertisements. |
| Symptoms | Browser settings that get changed are the start page, search engine and the new tab page. |
| Distribution Method | Freeware Installations, Bundled Packages |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
| User Experience | Join Our Forum to Discuss Findgofind.com. |

Findgofind.com – Delivery Methods
Computer users can acquire the Findgofind.com redirect by falling victim to one of the typical infection strategies. The used depends depend on the criminal organization behind the attacks. The reported instances so far do not give a clear outlook on the main method, as such we suspect that the hackers are using the most popular distribution ways.
Usually the redirect is applied to web browsers using malicious extensions, also known as hijackers. They are made for the most popular web browsers including: Mozilla Firefox, Google Chrome, Microsoft Edge, Safari, Internet Explorer, Opera and others. When the users acquire them they will see that important settings have been changed. The majority of the extensions modify the default home page, search engine and new tabs page to reflect the hacker-provided address. In addition they may cause other security and privacy issues including the following:
- Information Harvesting ‒ Browser hijackers have the ability to harvest sensitive and private information from the compromised applications. They can steal stored bookmarks, history, account credentials, passwords and settings. When the data is sent back to the hackers via the existing servers it may be used for crimes such as identity theft and financial abuse.
- Windows Settings Modification ‒ Advanced browser extensions can change Windows registry and other important settings which may lead to performance or stability issues.
- Additional Malware Infection ‒ Browser hijackers can cause several infections at once or in a hacker-specified chain of actions.
- Persistent Installation ‒ Some certain strains can perform a persistent installation. This is an advanced infection technique that actively counters manual removal methods.
Such browsers hijackers are usually advertised using spam email messages. In the majority of cases social engineering tricks are used to make the users infect themselves. There are two main types of spam campaigns:
- Embedded Malicious Links ‒ The criminals seek to insert links in the body contents that lead to dangerous executables. Once they download and start the downloaded program the browser hijacker is automatically started.
- Direct File Attachments ‒ The emails contain instructions on downloading and running attached files that contain the malicious instance. Depending on the case the hackers can resort to infected documents that serve as payload downloaders. They are usually office files (spreadsheets, rich text documents or databases) that contain built-in scripts (macros). When they are run the browser hijacker is downloaded from a remote server and executed on the local computer. In other cases the email host the malware directly.
Other infection sources include software installers downloaded from hacker-controlled sites. Hackers utilize P2P networks like BitTorrent where pirate content is usually found. The Findgofind.com browser hijacker can also be obtained from various fake Chrome Web Store extensions and other application repositories. Likewise the Findgofind.com can be found in the relevant software stores of other browsers as well.

Findgofind.com – In-Depth Overview
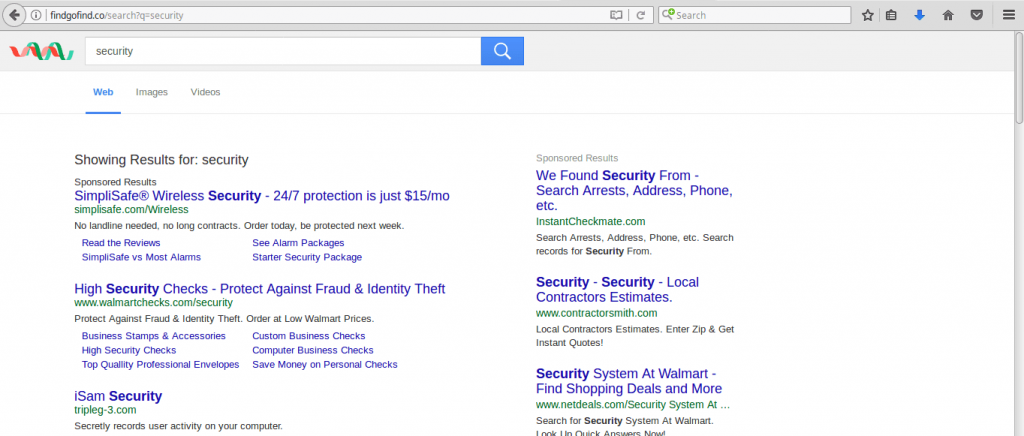
When the users are redirected to the Findgofind.com redirect page they are shown a familiar looking user interface. A search engine box is placed in the center along with links posted underneath it. There is a top menu bar that links to various well-known services.
Even though it may appear as a legitimate and safe website the users must beware that the use of the site imposes a tracking cookie. This has severe consequences on the privacy and security of the visitors. When the users interact with the site via the search engine they are shown sponsored results above everything else. As the operators of the site make money from affiliate links and partner networks the shown results do not represent the best results. In certain cases usage of Findgofind.com may even lead to redirects or downloads that result in dangerous virus infections.
The home page lists services that might be useful to the visitors as they point to Google-powered sites. However the users need to remember that each click and keyboard input may be monitored by the scripts. This means that the use of the browser hijacker and the website redirect can potentially leak sensitive accounts to the operators.
The site home page lists a “Contact Us” page that provides the following information about the company behind it:
Clever App, S.L.
Calle Irún 23, 1º, 1
28008 Madrid
España

Findgofind.com – Privacy Policy
The Findgofind.com redirect privacy policy is available from the site’s home page. It reads Clever App, S.L. Terms of Service and Privacy Policy showcasing that it is linked with other services controlled by the same party. It is possible that the affiliate links found in the search results redirect to other sites hosted by the company.
The document reads that when the users enter the site they agree to be bound by the services listed in the policy. Some of the dangers to the security and privacy of the victims include the following by harvesting private data. According to the policy the site and all affiliated services can collect personal information. The site does not specify the type of data. We suspect that this includes a wide variety of possibilities such as: web browsers version, operating system type and version, IP Address, your Internet service provider (ISP), geographical location, names, email or mailing addresses or other data that can identify a site visitor.
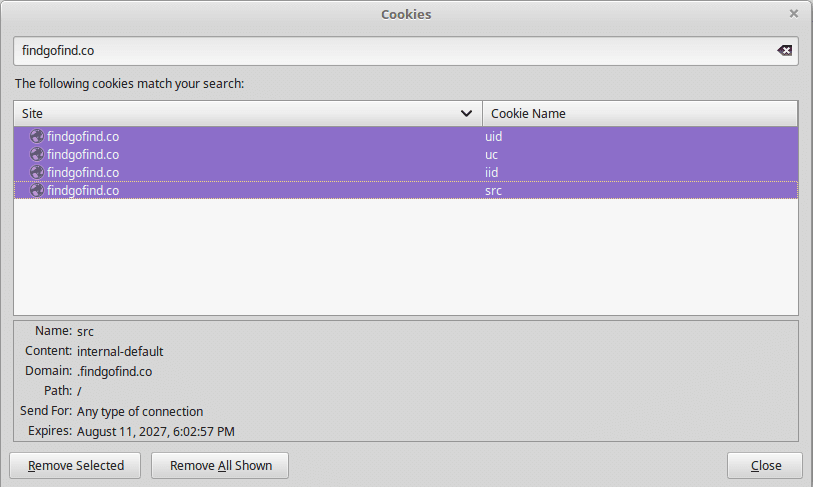
The privacy policy does not list other cases, including how it handles the data or if it shares it with third parties. While the home page itself does not infiltrate the victim computers with a tracking cookie. Several ones are used if the victims use the search engine. We have discovered that the service automatically assigned a unique user ID which starts to create a profile of all users. Using the harvested information and the search queries it starts to build a database of their interests in an attempt to better present affiliate links as search results.

Remove Findgofind.com Effectively
To remove Findgofind.com manually from your computer, follow the step-by-step removal instructions provided below. In case the manual removal does not get rid of the hijacker redirect and its files completely, you should search for and remove any leftovers with an advanced anti-malware tool. Such a program can keep your computer safe in the future.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove Findgofind.com from Windows.
Step 1: Scan for Findgofind.com with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





Step 3: Uninstall Findgofind.com and related software from Windows
Uninstall Steps for Windows 11
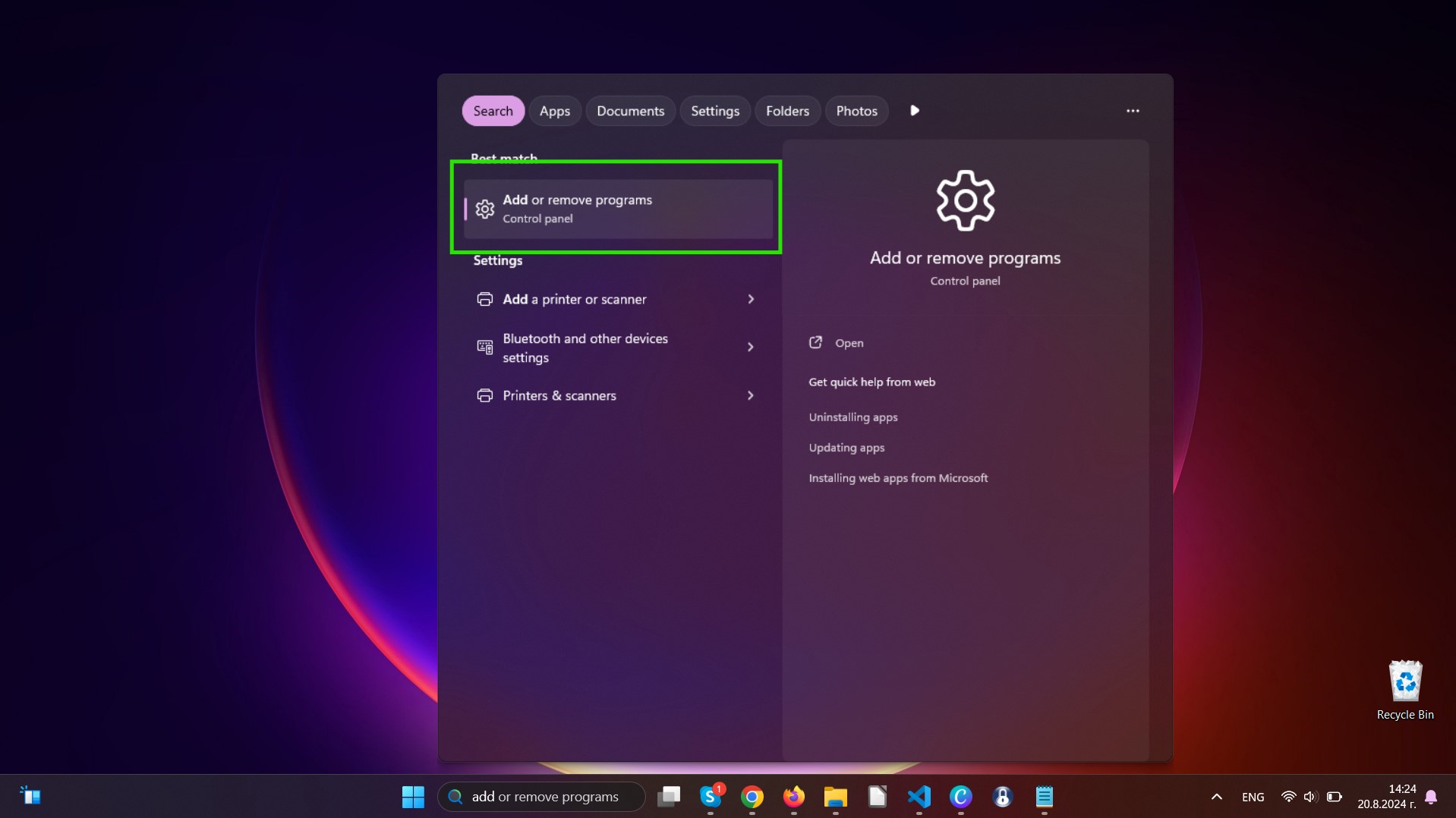
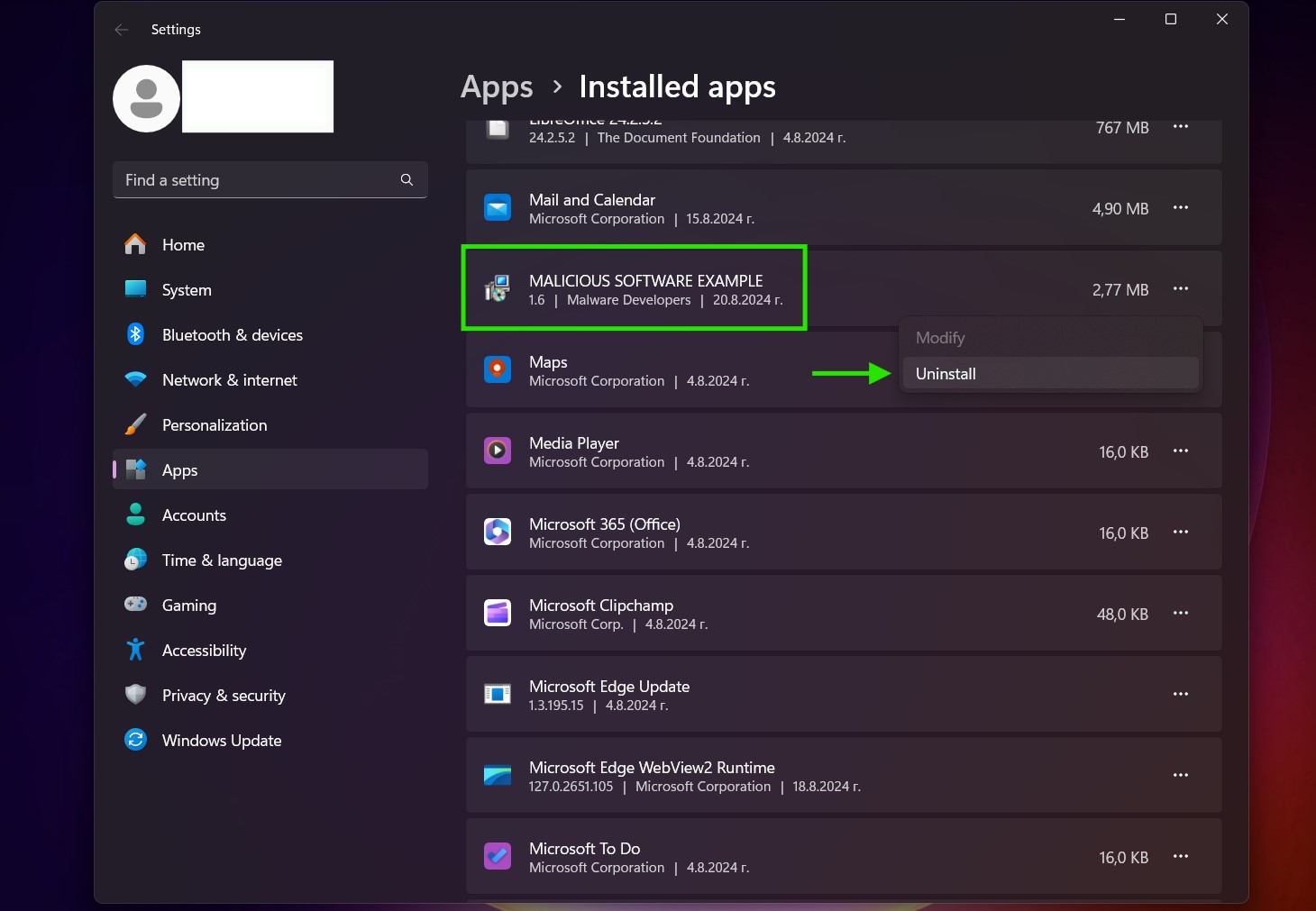
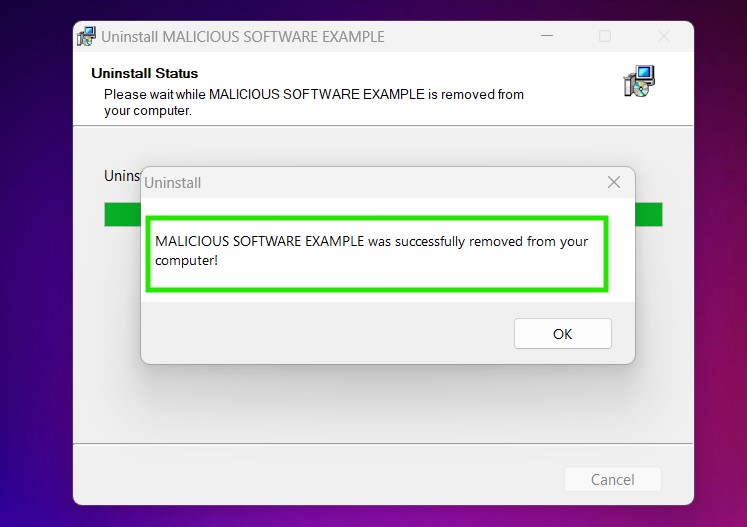
Uninstall Steps for Windows 10 and Older Versions
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by Findgofind.com on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Findgofind.com there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for Findgofind.com (Windows).
Get rid of Findgofind.com from Mac OS X.
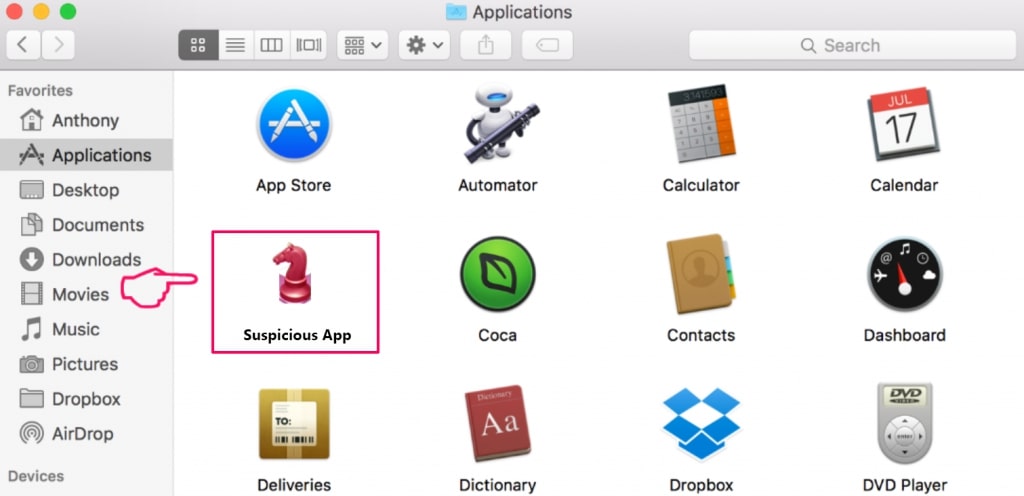
Step 1: Uninstall Findgofind.com and remove related files and objects
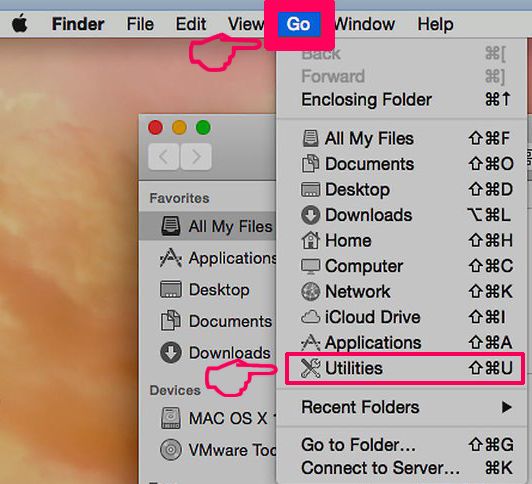
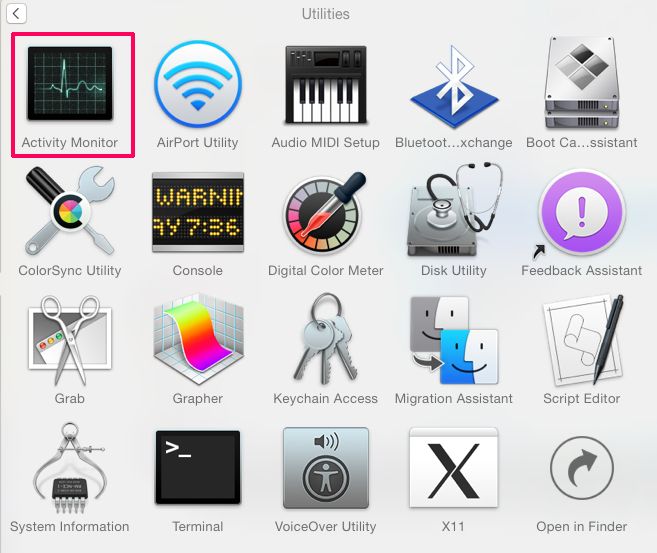
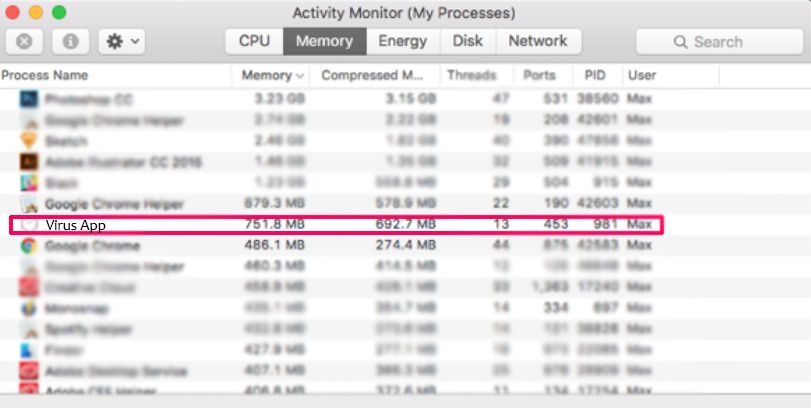
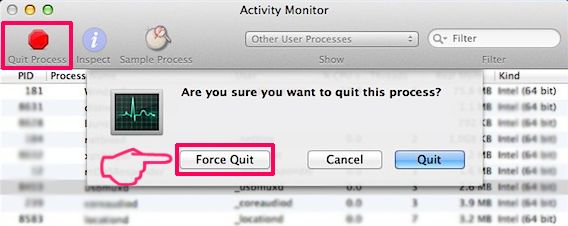
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Findgofind.com. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Findgofind.com via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
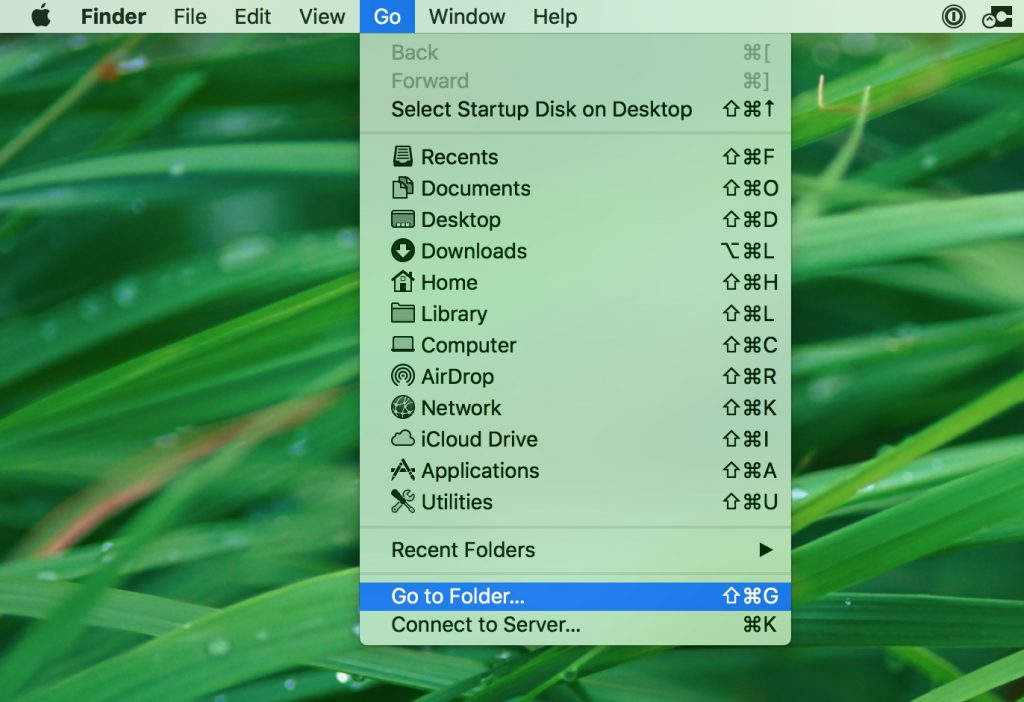
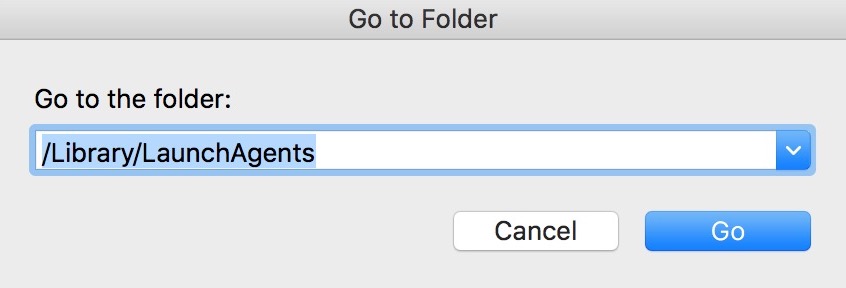
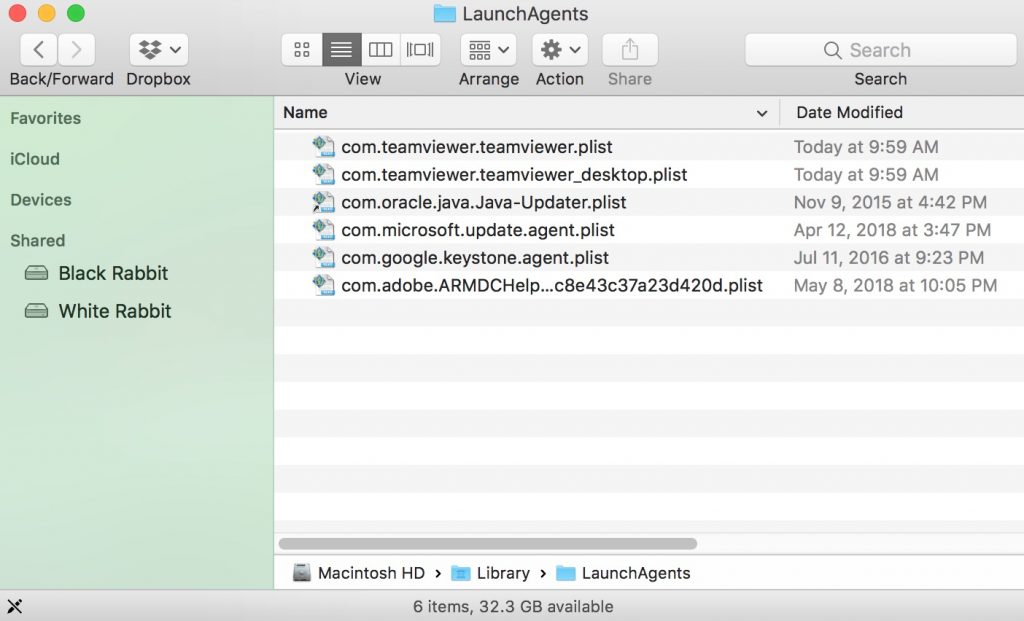
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove Findgofind.com files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Findgofind.com, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for Findgofind.com (Mac)
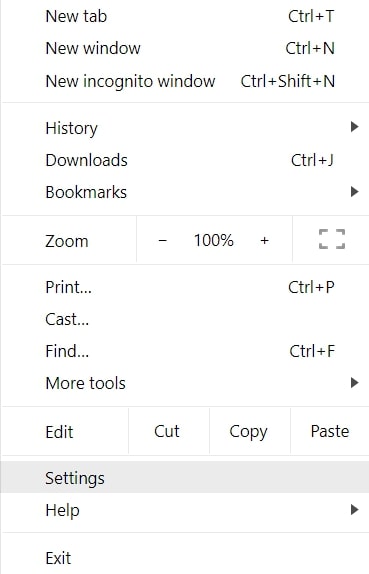
Remove Findgofind.com from Google Chrome.
Step 1: Start Google Chrome and open the drop menu
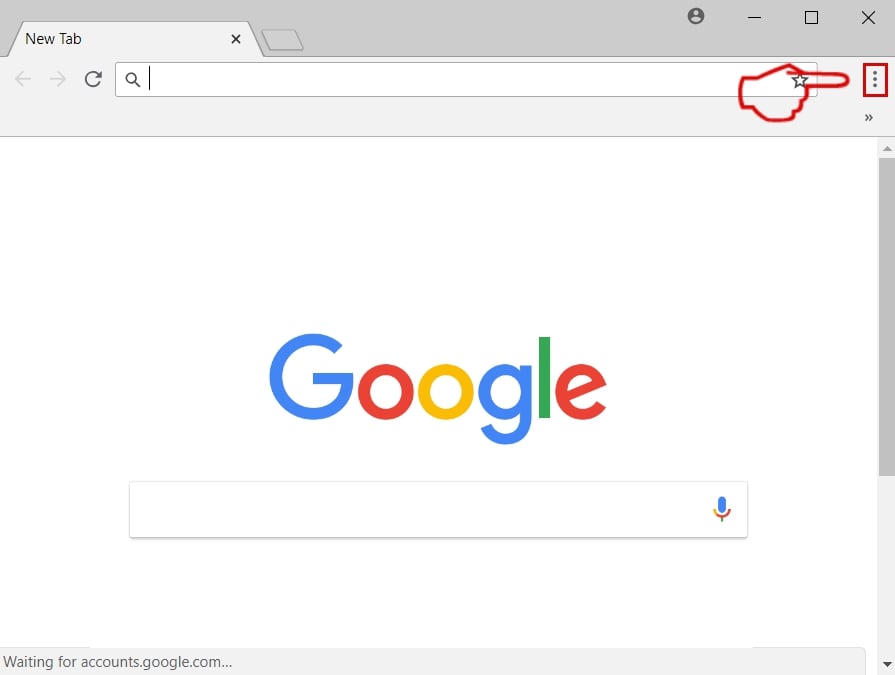
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
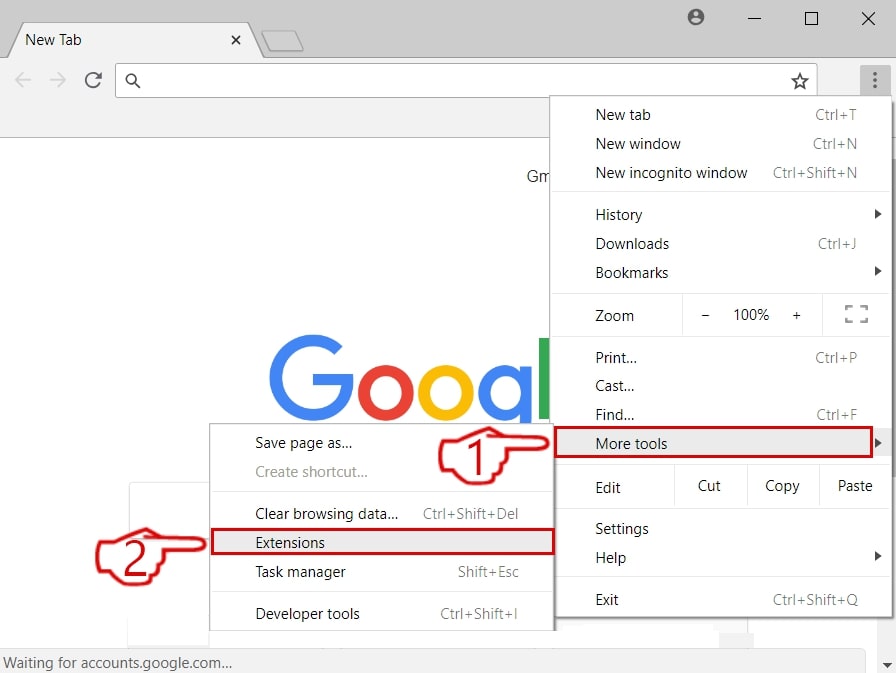
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
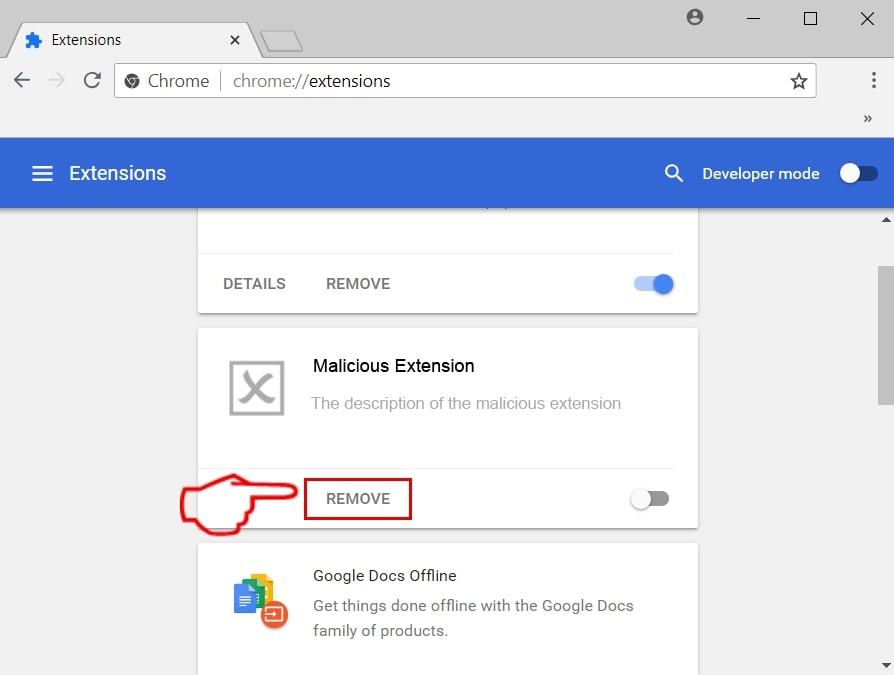
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase Findgofind.com from Mozilla Firefox.
Step 1: Start Mozilla Firefox. Open the menu window:
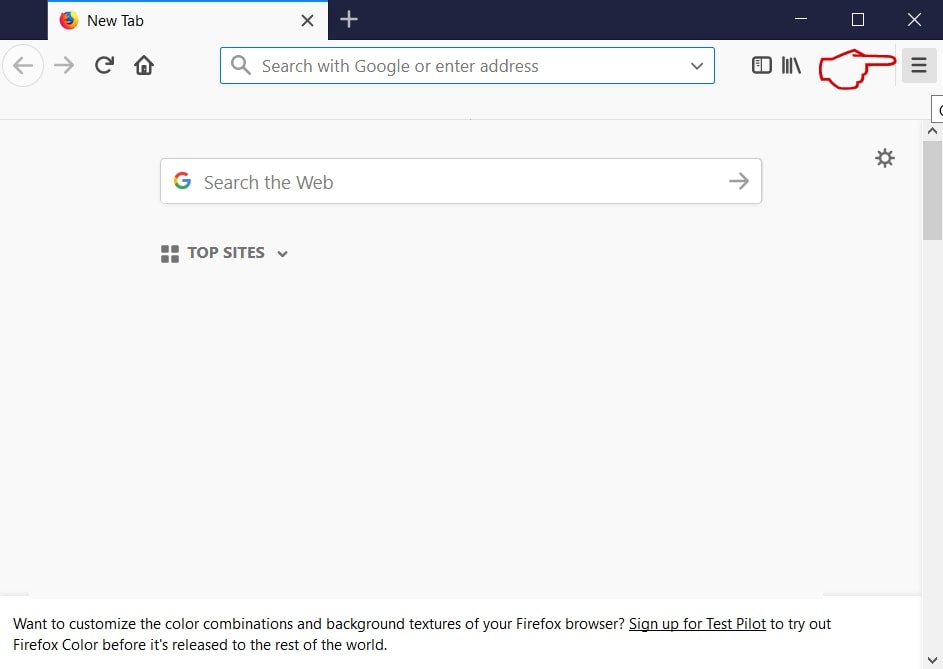
Step 2: Select the "Add-ons" icon from the menu.
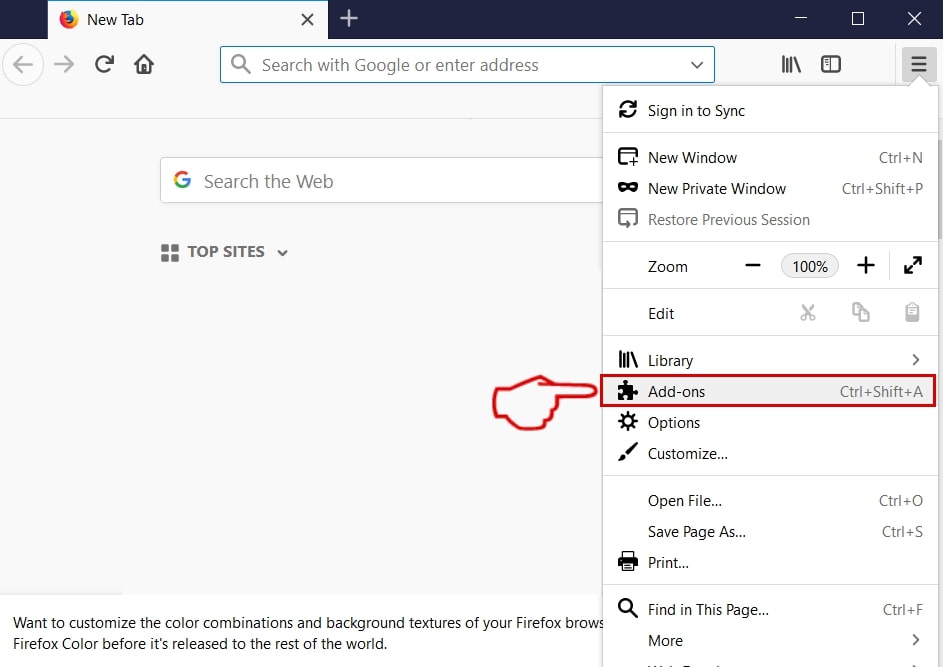
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
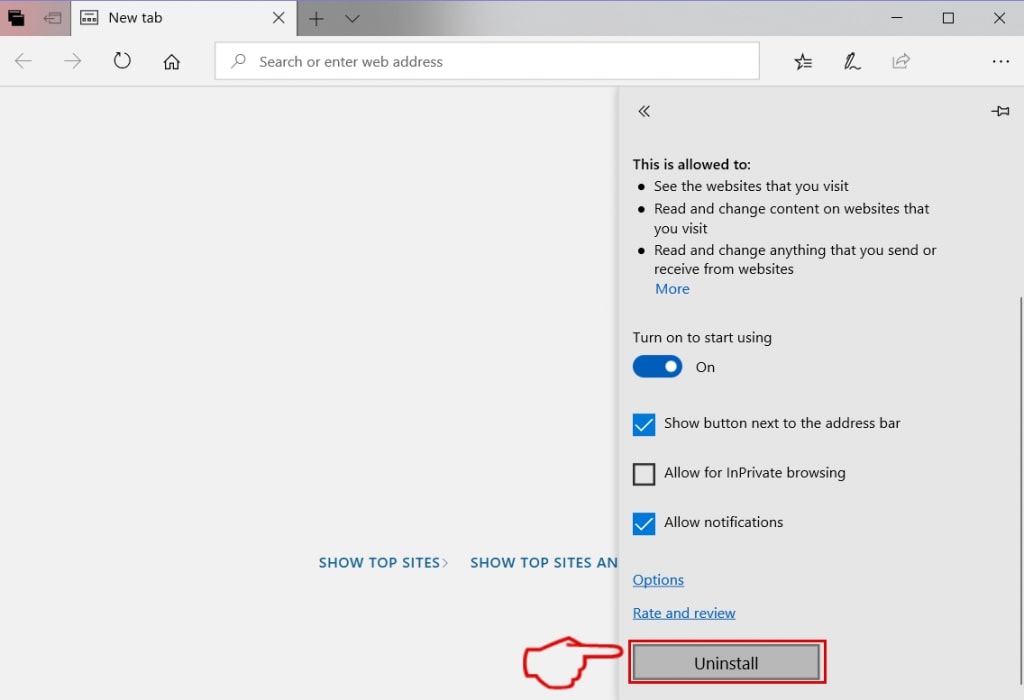
Uninstall Findgofind.com from Microsoft Edge.
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
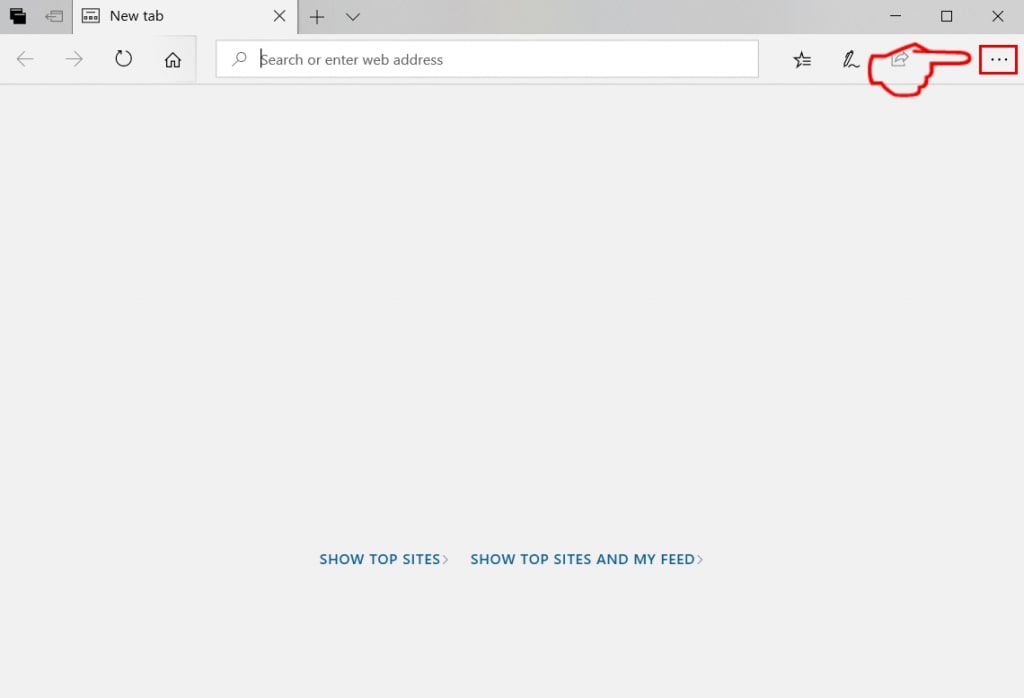
Step 3: From the drop menu select "Extensions".
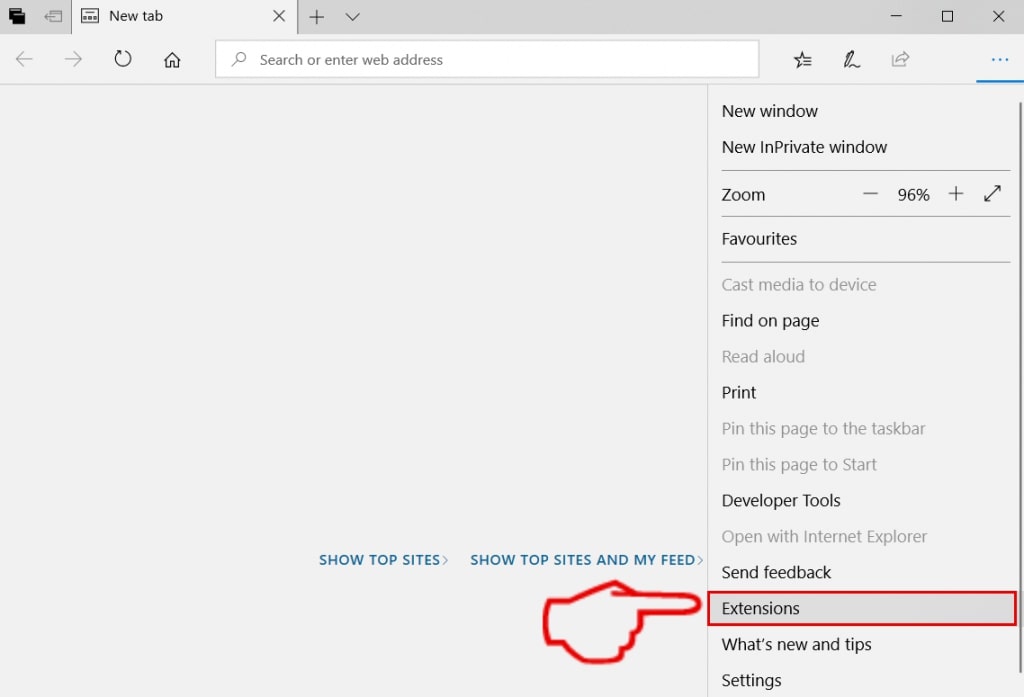
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
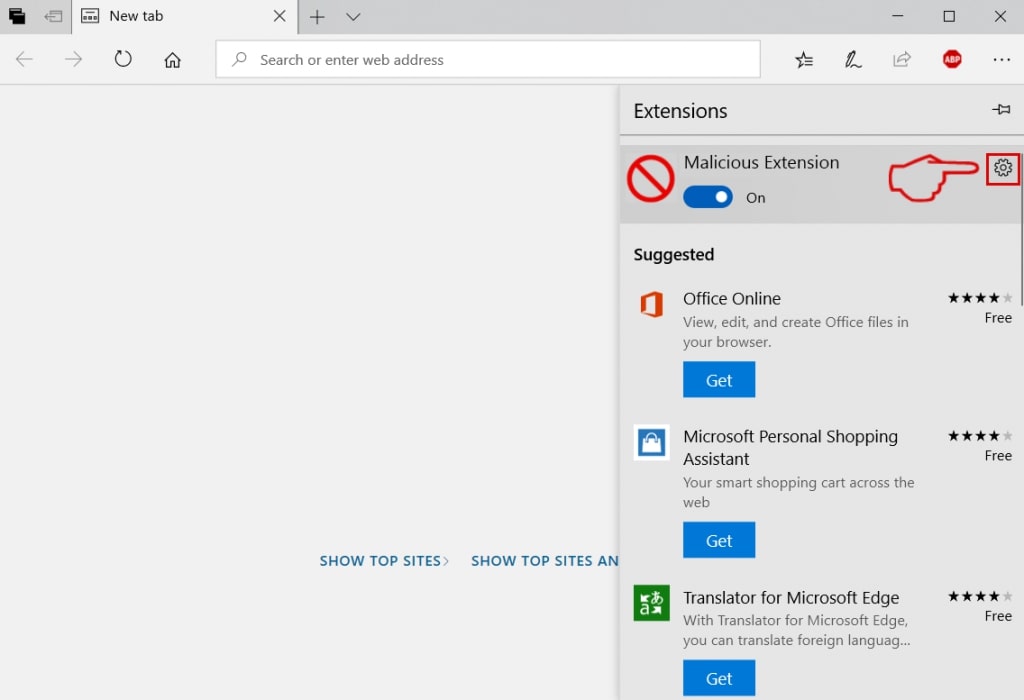
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
Remove Findgofind.com from Safari
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
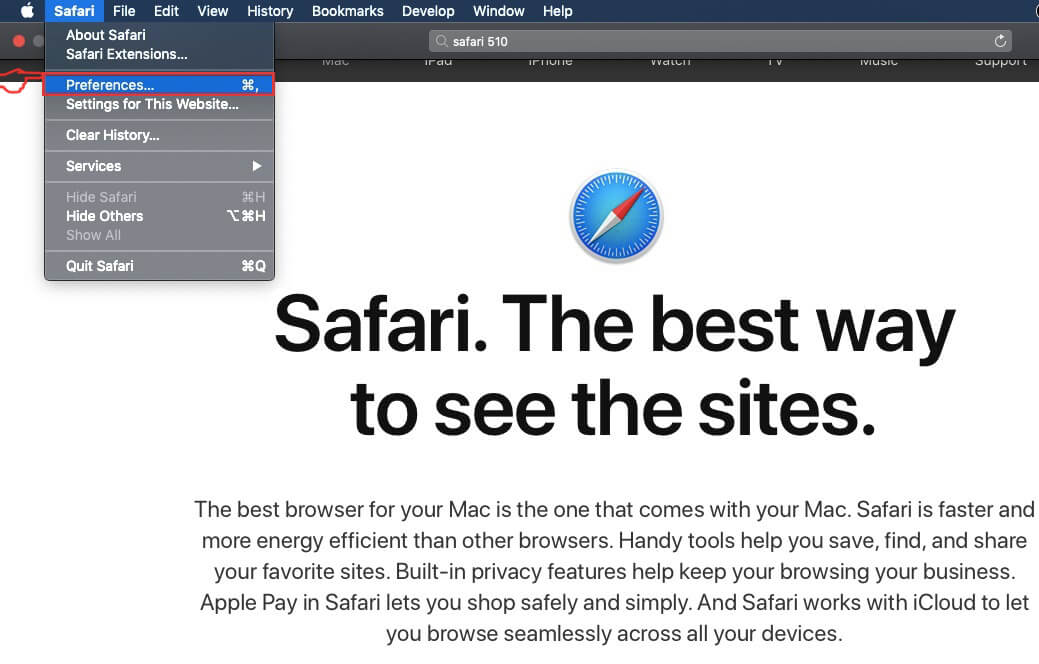
Step 4: After that, select the 'Extensions' Tab.
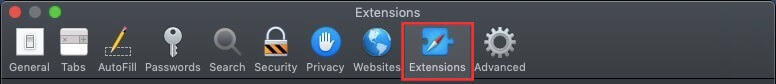
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
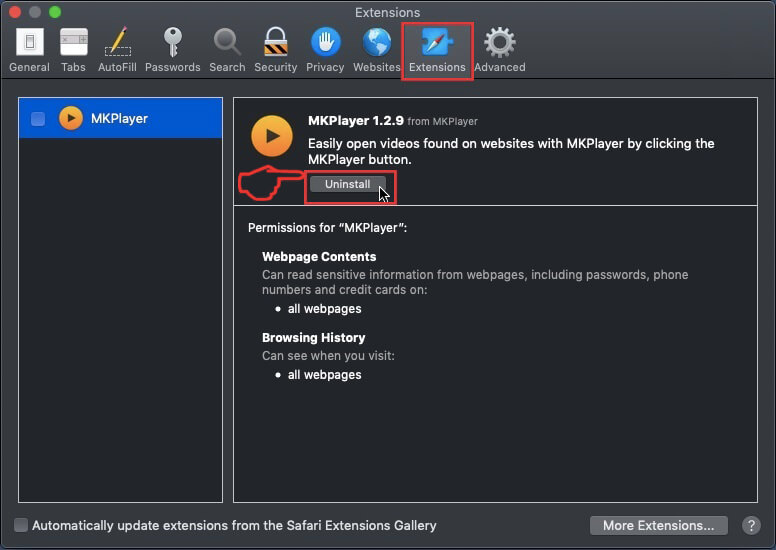
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the Findgofind.com will be removed.
Eliminate Findgofind.com from Internet Explorer.
Step 1: Start Internet Explorer.
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
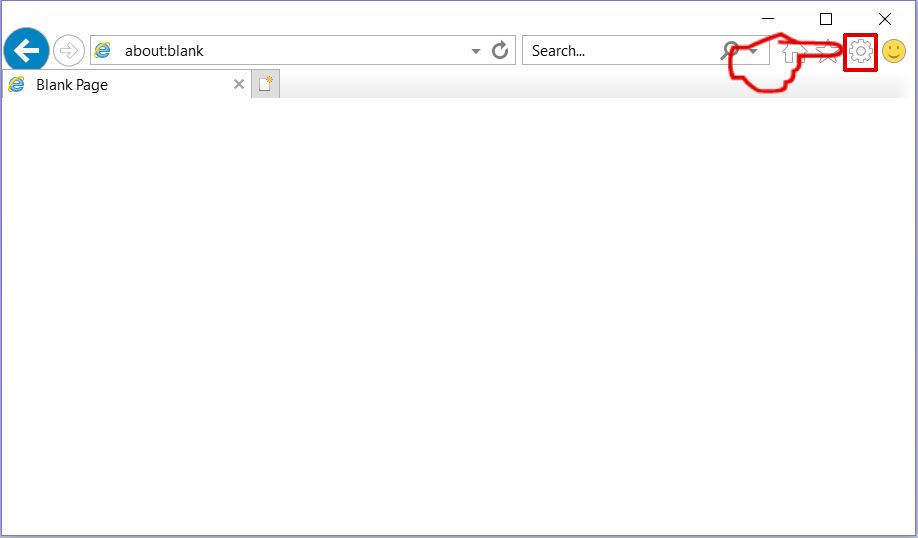
Step 3: In the 'Manage Add-ons' window.
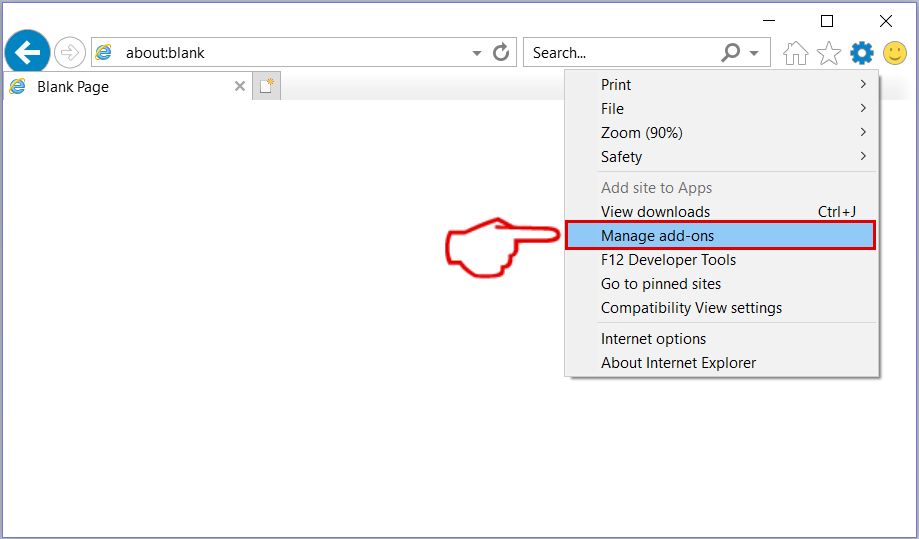
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
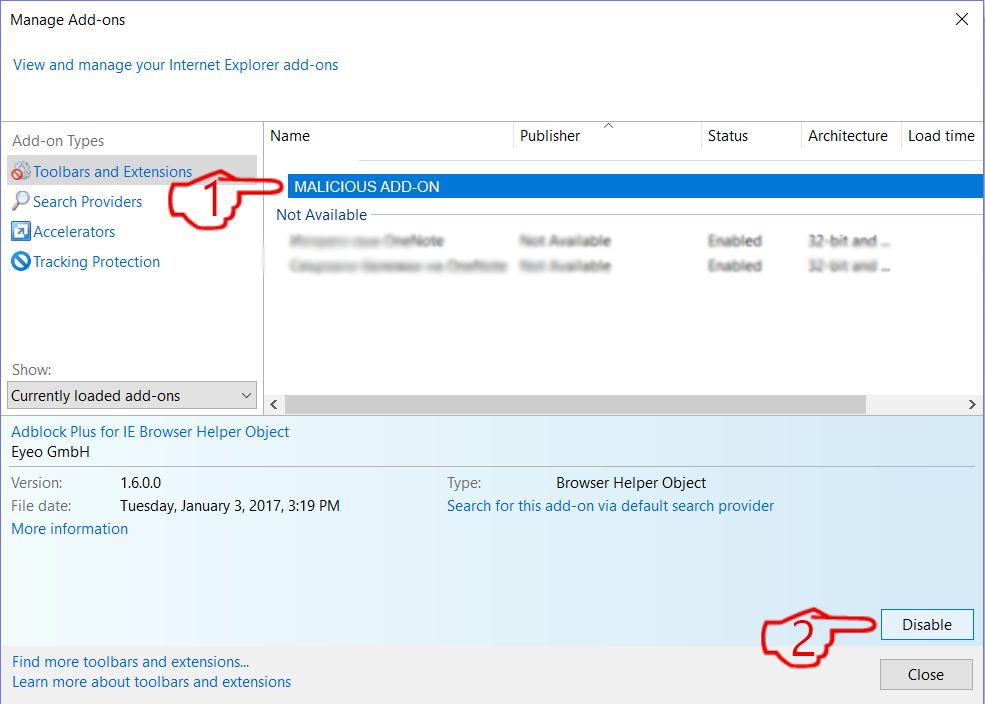
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
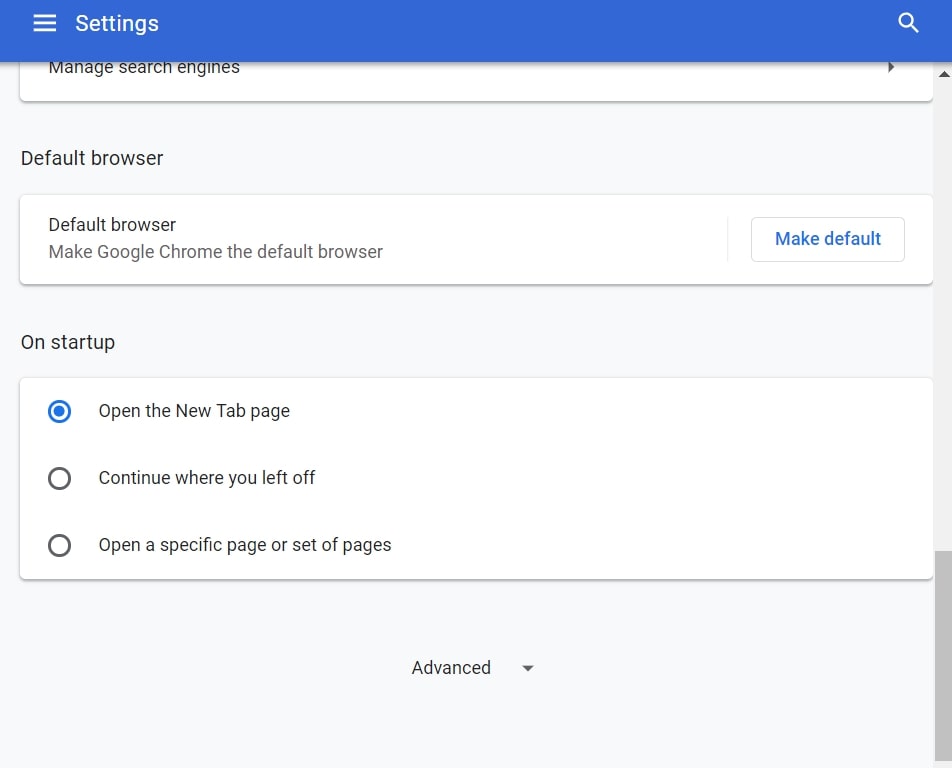
Step 3: Click “Content Settings”:
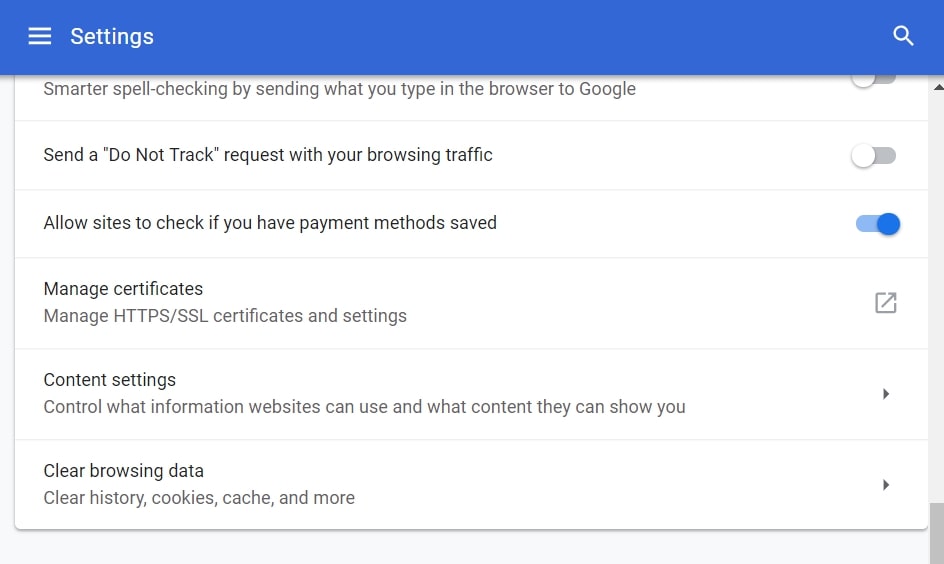
Step 4: Open “Notifications”:
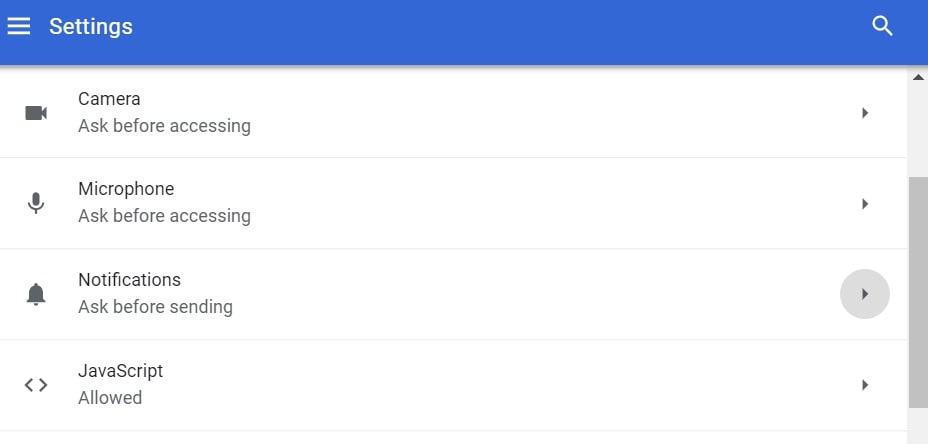
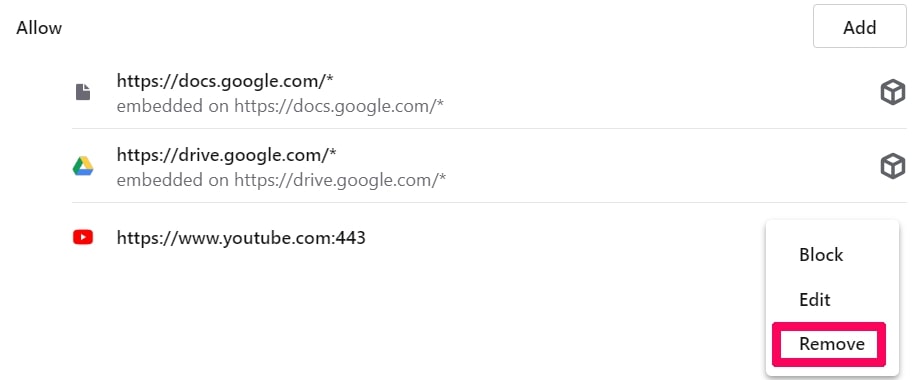
Step 5: Click the three dots and choose Block, Edit or Remove options:

Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
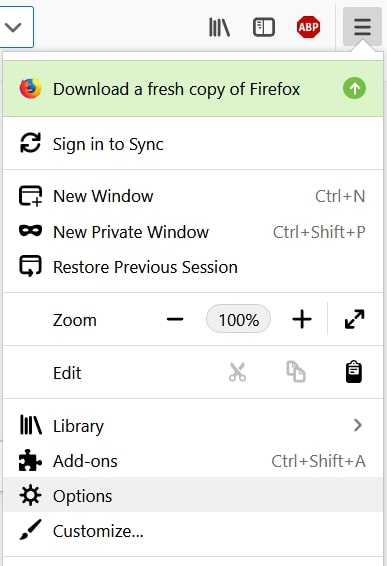
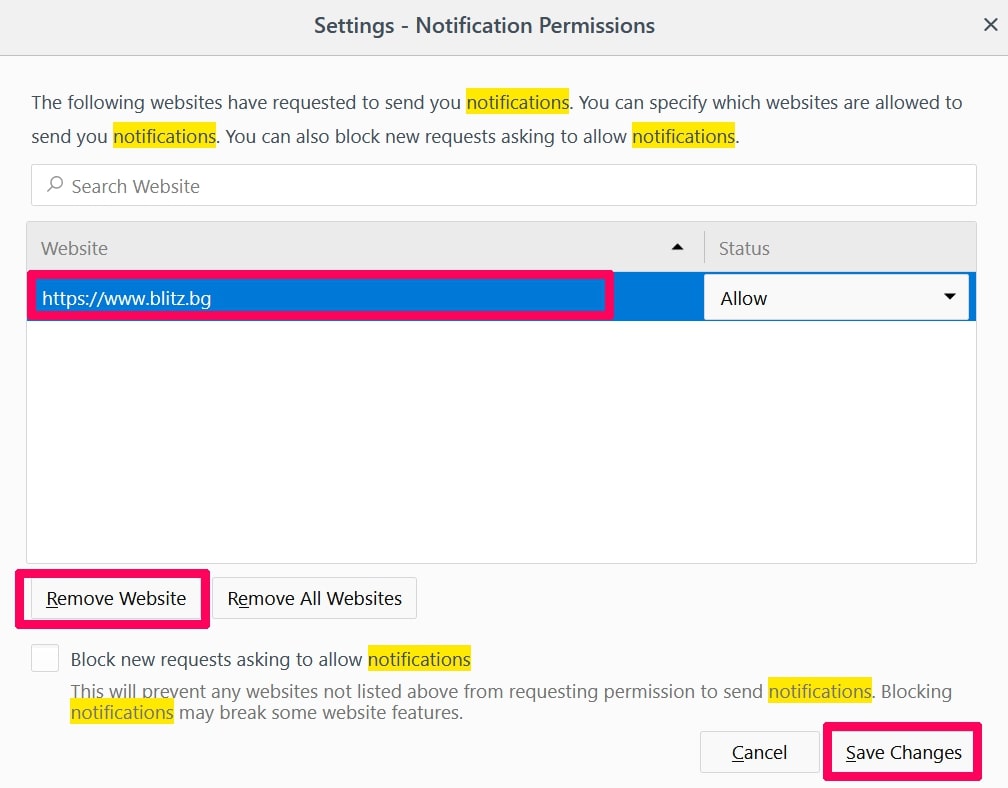
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
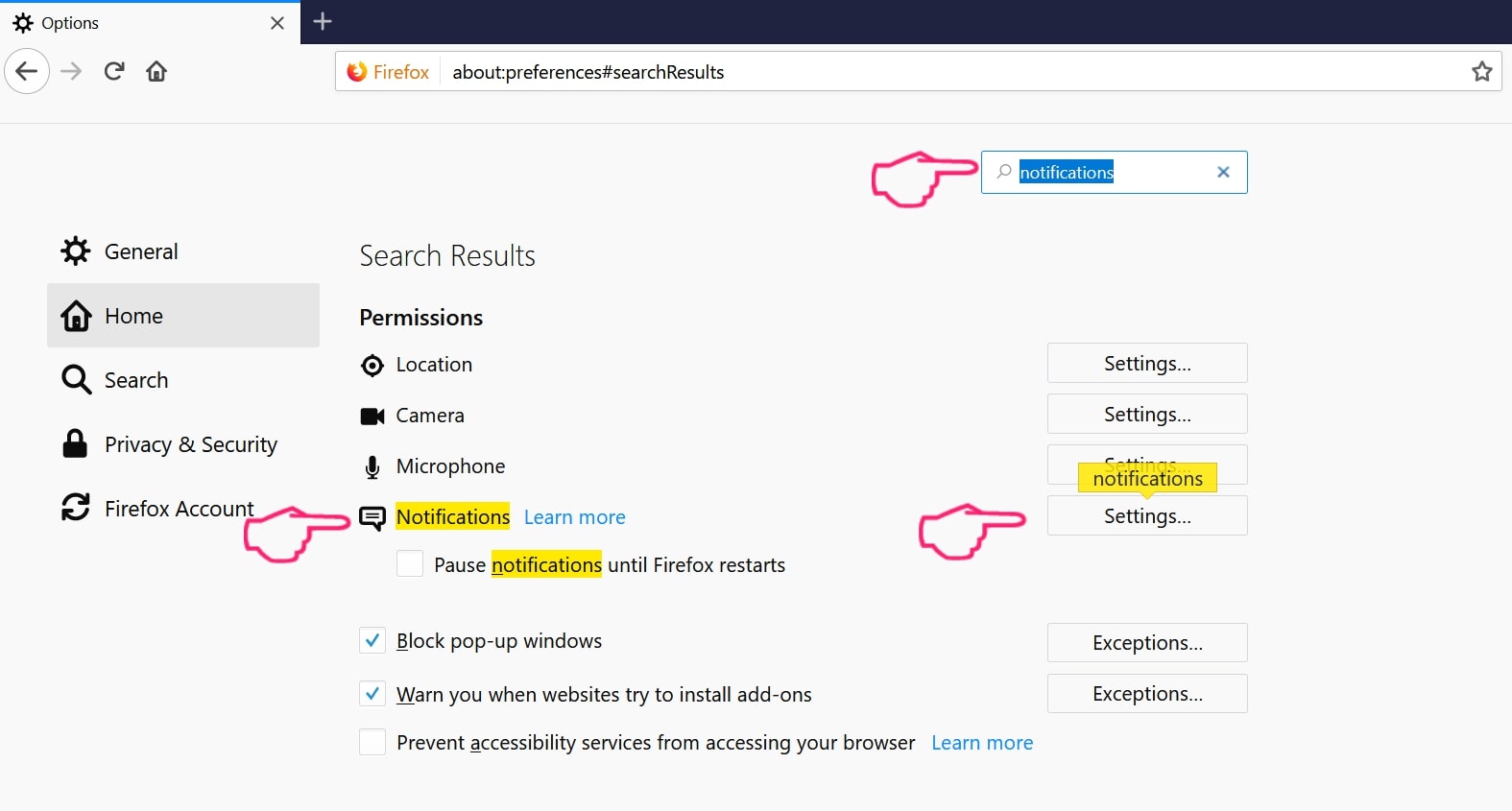
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
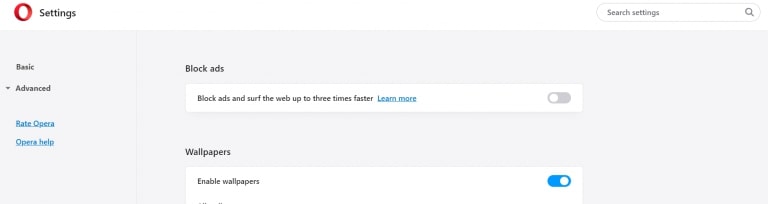
Step 2: In Setting search, type “Content” to go to Content Settings.
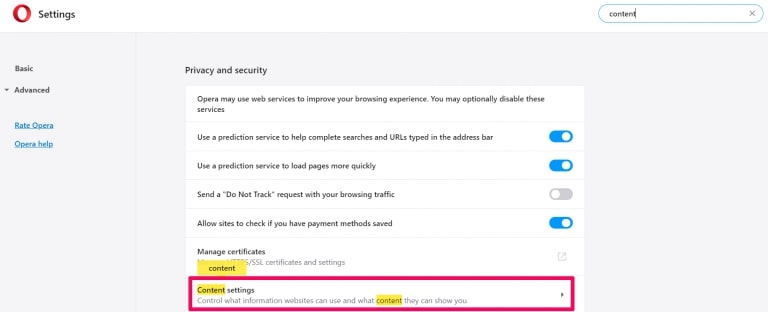
Step 3: Open Notifications:
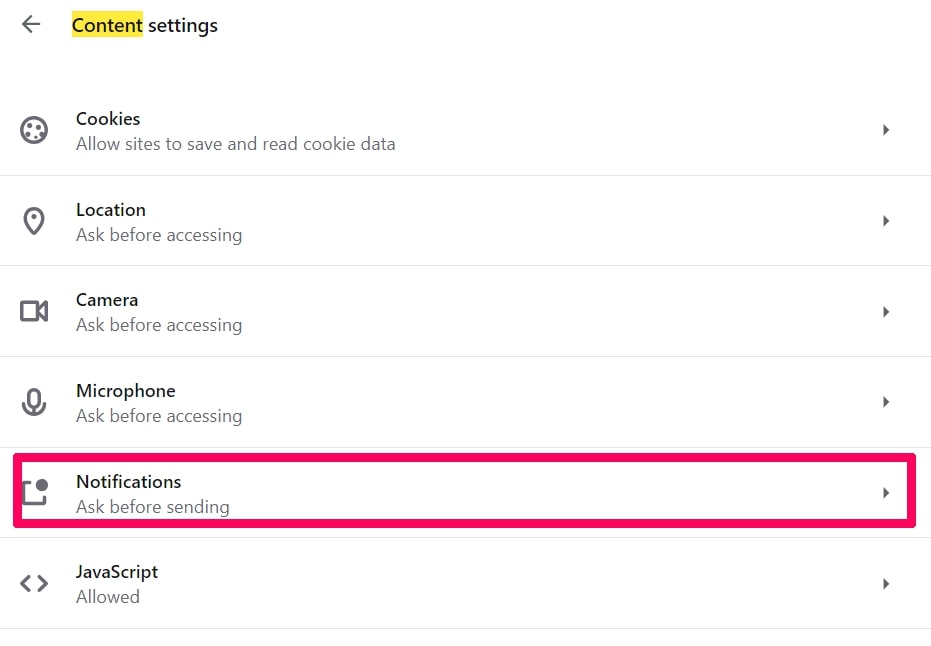
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
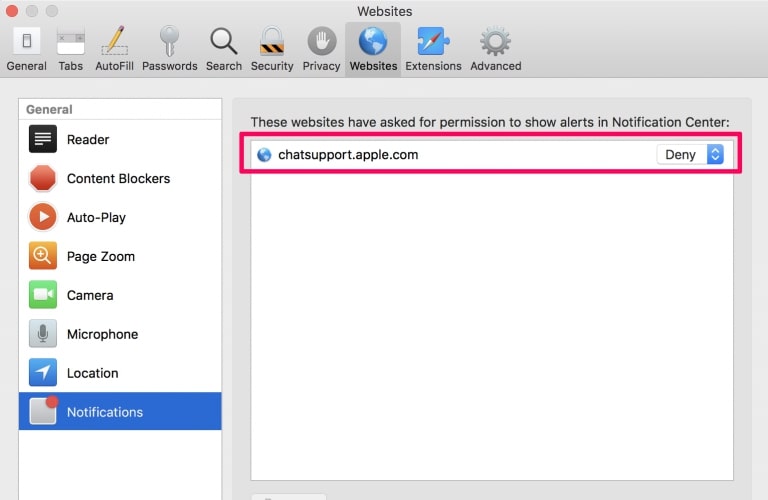
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
Findgofind.com-FAQ
What Is Findgofind.com?
The Findgofind.com threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of Findgofind.com?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like Findgofind.com?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does Findgofind.com Work?
Once installed, Findgofind.com can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
Findgofind.com can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is Findgofind.com Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the Findgofind.com Research
The content we publish on SensorsTechForum.com, this Findgofind.com how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on Findgofind.com?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the Findgofind.com threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.