| Name | Moker |
| Type | RAT (Remote Access Trojan), APT (Advanced Persistent Threat) |
| Short Description | The RAT has unique features and can bypass AV engines detection. |
| Symptoms | Sensitive data theft, exploitation of OS vulnerabilities. |
| Distribution Method | Not discovered yet. |
| Detection tool | Download Malware Removal Tool, to See If Your System Has Been Affected By a Trojan Horse. |
A new unique RAT (Remote Access Trojan) and APT (Advanced Persistent Threat) has been just discovered by researchers at enSilo. The malicious threat, dubbed Moker, has features that haven’t been observed before, and can go completely undetected by the 65 anti-virus programs hosted on VirusTotal.
As tech-savvy readers probably know, enSilo is a cyber-security company that provides a real-time, exfiltration prevention platform against threat actors targeting networks. enSilo’s service blocks malicious outbound communications, and allows employees to continue working even after their machines are compromised. Interestingly enough, the company spotted the RAT in one of their clients’ corporate network. As their research indicates, the RAT is most likely designed to execute covert operations inside enterprise networks and avoid detections.
Learn More about RATs and Trojan Horses
Moker RAT Technical Specifications
Researchers at enSilo named the RAT Moker after the description in its executable file. The attack method employed by the malicious piece is not clear yet. What is known so far is that the RAT is installed in two stages. The two-stage installation is used by the attackers to make sure that RAT remains undetected.
First, a ‘dropper’ component is planted. The tool drops the malware in a sophisticated manner and bypasses corporate security measures.
Then, the dropper proceeds towards installing the second component of the attack – the ‘payload’. It is downloaded from the Internet or another local source. Typically, the payload contains the malicious code that compromises the network.
Besides bringing the two stages into action, the Moker malware is designed to exploit design vulnerabilities in the Windows operating system:
- Moker can tap into the OS’s processes.
- Moker can go around the UAC feature.
- Moker can give itself system-level privileges.
After the two-stage infiltration and payload, and taking advantage of the OS’s flaws, Moker contacts the Command & Control server. According to researchers at enSilo, the server is traced back to Montenegro. However, the server’s location doesn’t necessarily apply to the attackers’ nationality.
What is intriguing about Moker is the fact that it can be controlled by its author, even when the Internet access is restricted. Even when corporate networks do not allow outside communications, Moker will proceed with the attack thanks to its local control system. It permits hackers to monitor and control their tool from the local network. It is also possible that the hacking team has members infiltrated in the company which is targeted.
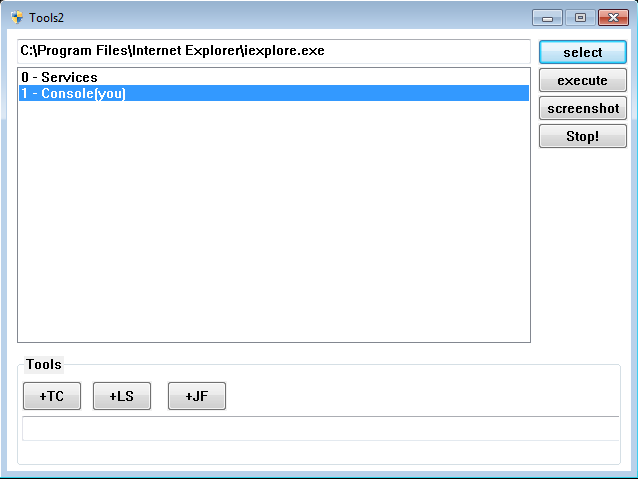
Image Source: blog.enSilo.com
Why Has Moker Been Created?
Typically, RATs are designed with the purpose to infiltrate a system and steal valuable information. In that sense, any kind of corporate data can be endangered by Moker. Aside from data theft, Moker can be employed to do any or all of the following:
- Create a new user account and operate from it without being disrupted.
- Change security settings.
- Change data and files.
- Employ a keylogger, take screenshots.
- Transfer data to the C&C server.
- Deceive reverse engineering by AV software.
As pointed out by SoftPedia, corporate networks should stay alert, since Moker can avoid common security debugging tools, virtual machines, sandboxed environments, and AV programs.
How Can I Stay Protected against RATs and Malware?
Both company employees and regular users should educate themselves about the dangers of malicious online threats. Even though latest malware pieces can be quite sophisticated and can bypass AV detection, security experts still advise on supporting an anti-malware program. Users and employees can also refer to the following tips to improve their security:
- Make sure to use additional firewall protection. Downloading a second firewall (like ZoneAlarm, for example) is an excellent solution for any potential intrusions.
- Make sure that your programs have less administrative power over what they read and write on your computer. Make them prompt you admin access before starting.
- Use stronger passwords. Stronger passwords (preferably ones that are not words) are harder to crack by several methods, including brute forcing since it includes pass lists with relevant words.
- Turn off AutoPlay. This protects your computer from malicious executable files on USB sticks or other external memory carriers that are immediately inserted into it.
- Disable File Sharing – it is recommended if you need file sharing between your computer to password protect it to restrict the threat only to yourself if infected.
- Switch off any remote services – this can be devastating for business networks since it can cause a lot of damage on a massive scale.
- If you see a service or a process that is external and not Windows critical and is being exploited by hackers (Like Flash Player) disable it until there is an update that fixes the exploit.
- Make sure always to update the critical security patches for your software and OS.
- Configure your mail server to block out and delete suspicious file attachment containing emails.
- If you have a compromised computer in your network, make sure to isolate immediately it by powering it off and disconnecting it by hand from the network.
- Make sure to educate all of the users on the network never to open suspicious file attachments, show them examples.
- Employ a virus-scanning extension in your browser that will scan all the downloaded files on your computer.
- Turn off any non-needed wireless services, like Infrared ports or Bluetooth – hackers love to use them to exploit devices. In case you use Bluetooth, make sure that you monitor all of the unauthorized devices that prompt you to pair with them and decline and investigate any suspicious ones.
- Employ a virus-scanning extension in your browser that will scan all the downloaded files on your computer.
- Employ a powerful anti-malware solution to protect yourself from any future threats automatically.

Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter