Article Pinpoints:
-
*What are the types of Trojan Horses?
*Who is endangered by Trojans?
*What are the most notable Trojan attacks in the past years?
*How do high profile, collection-of-malware attacks happen?
What Is a Trojan Horse and How Does It Work?
Trojan horses are inceptive and stealthy, and they are often deployed to exploit network vulnerabilities and harvest sensitive information. Trojans can act as intelligence stealers and take part in sophisticated cyber-espionage platforms. When we talk about collection-of-malware type of attacks, Trojans work together with computer worms, viruses, and exploit kits. It solely depends on the purpose of the exploit and the end target.
Malware frequently attacks private organizations and public companies, but so it does with common users. If a big and rich company is being targeted by cyber criminals, a backdoor Trojan may be dropped onto the system via an exploit kit, and a rootkit may be used to conceal the exploitation.
If random computers are attacked, Trojan droppers and Trojan downloaders may be employed together with ad-supported software and potentially unwanted programs, and other malicious pieces. However, Trojan-Ransom attacks are quite popular among users as well. As a matter of fact, Ransomware is most likely the single most re-occurring malware piece of 2015.
When you think about it, in computing, Trojan horses are the real deal. They are just like shapeshifters, eager to satisfy the hunger for exploit.
So, how many Trojans are out there?
We have listed the most common Trojan types and the attacks they take part in. Let’s have a look.
Backdoors/ RATs (Remote Access Trojans)
As its name gives it away, a backdoor Trojan, or a RAT, is used to give remote access to the infected PC/ network. Thanks to backdoors, cyber criminals get to decide when to initiate the exploit, and what malicious activities will take place in the attack. Backdoors may be used to send and receive data, launch operations, display information or reboot the PC. Worst case scenario with this particular Trojan type is if the PC becomes a silent participant in a botnet or zombie network.
RAT attacks are usually initiated by phishing and social engineering schemes. Most are concealed in heavily packed binaries that are dropped onto targeted systems in the later stages of the malicious payload.
Examples of Backdoors:
Exploits
Exploits, or exploit kits, are designed to locate a network vulnerability and take advantage of it. There was a time, in 2012, when the infamous Russian BlackHole exploit kit was dubbed the most prevalent online threat. It was designed to target vulnerabilities in browsers and widely used plug-ins.
Other notable exploits:
Angler Explot Kit, Exploit:HTML/Axpergle.N
Rootkits
According to Wikipedia, the first malicious rootkit was ‘designed’ for the Windows NT operating system. It was created in 1999 and it was a Trojan called NTRootkit. By definition, a rootkit will be employed when certain objects and activities need to be concealed. Rootkits are often used in hack attacks on corporations. Because of their ability to prevent malware of being detected, rootkits take place in sophisticated, multi-level malware attacks.
Examples of malicious code rootkits:
Ransomware Trojans
Trojan Ransoms are able to modify data on the PC they have infiltrated. As a result, the compromised machine will not run as it should, or individual files may not be accessible any longer. As typical in Ransomware attacks, access to the encrypted data is only possible after a ransom is paid in bitcoins or other form of online currency. Ransomware is dubbed the most spread money-stealing attack of 2014 and 2015.
Latest Ransom Trojans:
Banking Trojans
Also known as Trojan Bankers, this type of malware will target your bank account information and money.
Dropping Trojan Bankers onto the system is one of the efficient ways to make easy money online in 2015. We have observed a vast emergence of Banking Trojans among common users. If you are an intensive online shopper, protecting your system and browser should be a priority.
Banking Trojans to keep away from:
Trojan-DDoS and DoS
Denial-of-service attacks may not occur every day, but once they do, the consequences are not pretty. Shortly described, a DoS attack is the attempt to affect a single computer or make a computer network unavailable to its users. The ‘denials’ may be temporary or indefinite. They could even suspend services of a host connected to the Internet. A distributed denial-of-service (DDoS) is when the attack uses multiple sources of unique IP addresses.
It is not a surprise that these attacks often target websites and services hosted on top-level web servers, such as banks. However, there are cases of DoS attacks launched on the basis of activism and political reasons, or even revenge.
Trojan Downloaders
They are quite common among ordinary users. Hackers use them to download and install the latest versions of malware on the PC. If your system is compromised by a Trojan Downloader, you may end up flooded with adware and PUPs. Downloaders may not be as sophisticated as other types of Trojans, but they cause enough trouble to make you anxious.
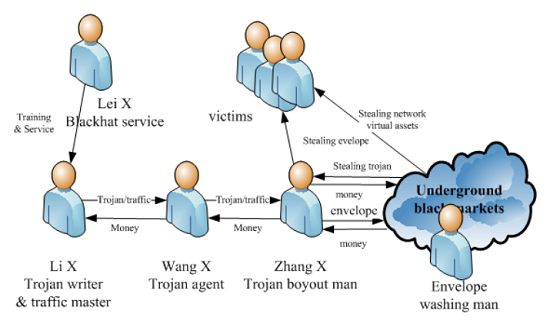
Image Description: Chinese Trojan Horses ImageSource: TrendMicro
A Trojan Downloader that has been recently detected is TrojanDownloader:AutoIt/Fadef
Trojan Droppers
Droppers seem to be a tad more refined than Downloaders. First, they are deployed to install other Trojans and viruses. Also, they can prevent the detection of malware on the system. Furthermore, not all AV solutions will be able to scan all components of a Trojan Dropper. If you spot such a Trojan, be sure that you have more malware installed.
FakeAV Trojans
Trojan-FakeAV may be detected by your AV program. Different AV solutions have different detection names for such Trojans. FakeAV Trojans will simulate the activity of an anti-malware program and will extort money from you. Sounds familiar? Rogue security software has been around for quite some time. It will generate fake system alerts about viruses, but it is not to be trusted. If you detect such presence in your system, make sure to remove it via professional AV software.
IM Trojans
Such malicious programs will aim at your login credentials and passwords for Instant Message programs like Skype, AOL IM, ICQ, and MSN. Once obtained, cyber crooks may initiate intrusive spam link campaigns and try to drop malware onto your contacts.
GameThief Trojans
This particular Trojan detection targets active gamers and attempts to obtain user credentials. Trojan-GameThief may not be a common threat but it a nightmare to the gamer.
Sms Trojans (mobile threat)
A Trojan-SMS will cost the victim a lot of money – it is designed to send tech messages from the compromised mobile device to premium rate phone numbers. Just another mischievous way to steal money in the 21st century, isn’t it?
Spy Trojans
A Trojan-Spy detection should serve to inform you that you are currently being spied on. Spying malware often employs keylogging techniques to capture the victim’s passwords and keyboard strokes. It can also take screenshots and get hold of the PC’s currently running applications.
Mailfinding Trojans
ATrojan-Mailfinder AV detection means that a Trojan is actively collecting email addresses from the PC. Once the email addresses are obtained, they can be used in spam email campaigns.
Some of the Trojan Horses we have listed may be combined in one single attack. For instance, a Trojan Dropper may drop several different Trojans onto the system, depending on the information cyber criminals are after. When we talk about sophisticated hack attacks on corporations, such as the ones presented in Mr. Robot’s first season, things get a bit more complicated…
Top Trojan Attacks in Recent Years
Cyber criminals often employ Trojans to steal money from common users and business owners. Thus, RATs, or Remote Access Trojan attacks, are among the most re-occurring attacks in 2015. According to security research, at least 21.5 million Americans had their social security numbers and other sensitive details stolen in a second breach to OPM’s background check database. The attack is of such magnitude that OPM Director has given in her resignation letter. What appears to be behind the malicious attack is the Sakula RAT.
Sakula Malware Family and RAT
Sakula, also known as Sakurel and VIPER, is a well-known malware family. Even though the malware piece was written back in November 2012, it has been recently revived and took part in hack attacks in 2015.
Sakula is designed to enable an adversary to run commands and download and execute additional components. It uses HTTP GET and POST communication for command and control. Network communication is baffled with a specific, single-byte XOR encoding.
Researchers at CTU have observed a copy of Sakula while being delivered in a strategic web compromise (SWC) that exploited a single vulnerability – CVE-2014-0322. The latter was a zero-day vulnerability in Internet Explorer. During this specific attack, a subset of Sakula variants were digitally signed and as such, could bypass security controls.
Agent.BTZ/ComRat a.k.a. Uroburos – the King of RATS
Agent.BTZ is believed to be among the most vicious RATs with worm capabilities the online world has seen. According to many independent security researchers, the RAT is developed by the Russian government to target ICS European networks. Agent.BTZ is being spread via phishing. It is known to use advanced encryption mechanism to protect itself from being analyzed. Once dropped onto the system, it will give full administration rights and will send extracted sensitive data back to the Command & Control server. In short, the RAT uses sophisticated anti-analysis and forensic methods.
Agent.btz was first introduced in 2007. Because it was employed to infect US military networks, it was broadly covered by the mass media around the globe. The protection against Uroburos was dubbed Operation Buckshot Yankee, and it led to the establishment of the US Cyber Command.
It all started when an infected USB flash drive was left in the parking lot of Department of Defense facility at a Middle East base. The USB contained malicious code. It was put into the USB port of a laptop attached to the US Central Command.
According to data compiled by SecureList, Agent.btz was detected 13.832 times in 107 countries across the world… only in 2013.
It is only logical to ask yourself…
How Can I Stay Protected against Trojan Attacks? Security Tips
Here are some security pinpoints against Trojan Horses:
- Use a reliable anti-malware program.
- Use a secure ISP (Internet Service Provider).
- Enable automatic Windows updates.
- Be smart with email attachments.
- Be alert with p2p file sharing.
- Frequently update your browser to avoid zero-day exploits.
- Avoid unsafe browsing.
- Backup your files regularly.
- Enable the Windows Firewall.
Now, to make sure that your system is running flawless, you can scan it via antivirus software you trust. And remember – cyber criminals often target people. Even the most sophisticated hack attacks begin with a simple phishing scam.