The All in One Office redirect is a browser hijacker that upon infection redirects the victims to a hacker-controlled page. It has the ability to steal sensitive data from the users and install other viruses as well.

Threat Summary
| Name | All In One Office |
| Type | Browser Hijacker, PUP |
| Short Description | Upon installation the browser hijacker changes the default settings of the target applications to point to a hacker-controlled page. |
| Symptoms | Modified browser settings include the homepage, default search engine and the new tab page. |
| Distribution Method | Freeware Installations, Bundled Packages |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
| User Experience | Join Our Forum to Discuss All In One Office. |

All in One Office – Distribution
The All In One Office redirect is a browser hijacker that is actively being distributed to users worldwide. The hacker operators behind it are utilizing the most popular infection strategies in order to maximize the infection ratio.
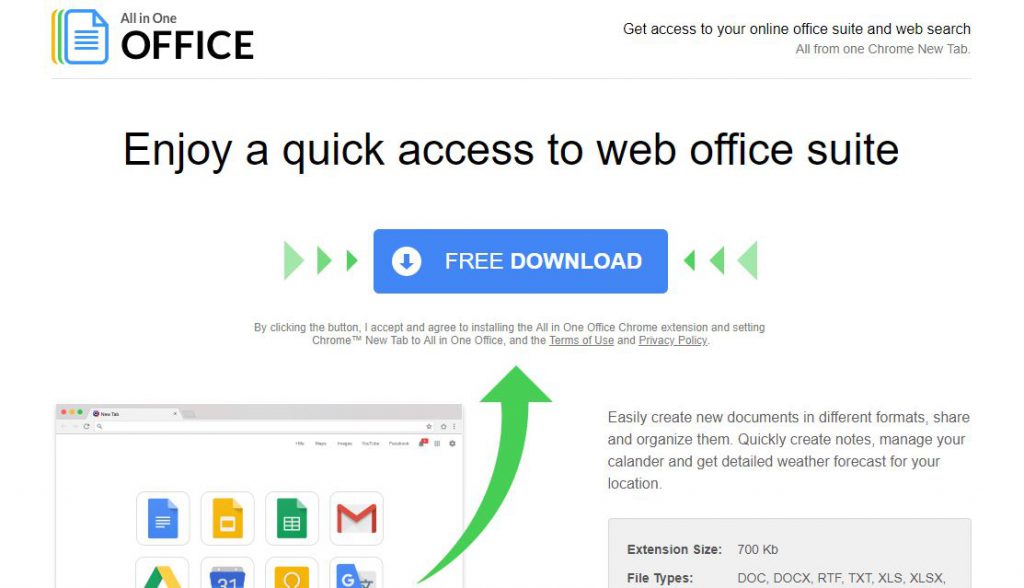
One of the main methods at the moment is the creation of malware download pages that promote the site via fraud features. Many hijackers like this one promise to add useful new capabilities or enhance already existing ones. One of the pages shows the following description:
Easily create new documents in different formats, share and organize them. Quickly create notes, manage your calander and get detailed weather forecast for your location.
Criminals can also opt to use email spam messages to spread the malware code. There are two primary ways of configuring them depending on the way the hijacker code is delivered:
- File Attachments — The All In One Office redirect can be directly attached to the messages. The body contents uses different approaches into making sure that the victim executes the file. In many cases they are placed in archives and the passwrod is placed in the body contents of the message.
- Hyperlinks — Links to hosted instances of the All in One Office redirect can be placed in the contents posing as legitimate setup files, documents or other other files of user interest.
In a similar way the attackers can also opt to utilize two other mechanisms in conjunction with the emails. One of them is the use of infected documents that contain dangerous scripts. Once the victims open them up a notification prompt appears which asks them to enable the macros (scripts). Once this is done the virus file is downloaded from a remote location and executed on the local machine.
Malware software installers can be used as well. They represent hacker-modified setup files that are created by taking the legitimate installers from the official vendors and modifying them to include the All In One Office redirect code. In similar ways they are distributed using email tactics and fake pages.
Still one of the the most effficient distribution tactics remain the spread of browser hijackers on the official software repositories such as the Chrome Web Store.

All in One Office – Information
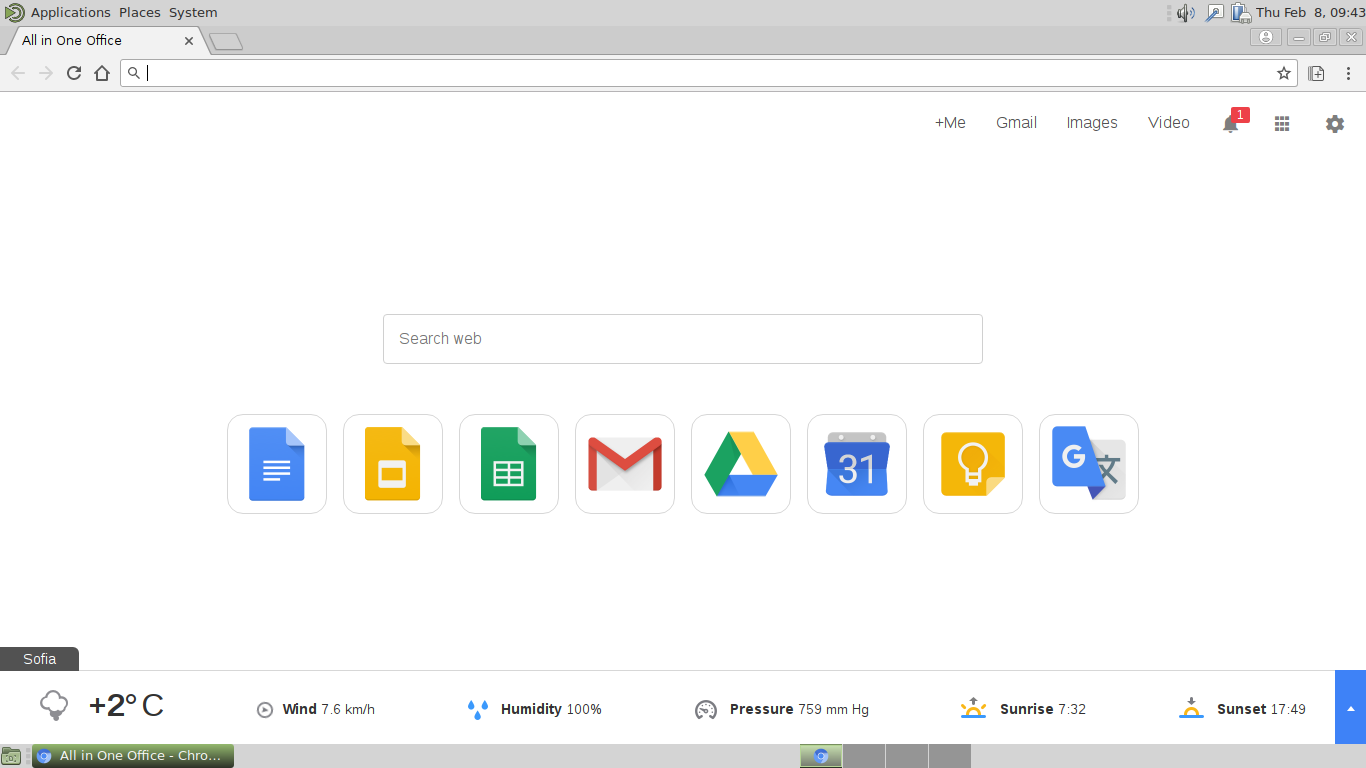
Usually browser hijackers like this one are made compatible with the most popular web browsers: Mozilla Firefox, Safari, Google Chrome, Internet Explorer, Opera and Microsoft Edge. Once the users are infected with the All in One Office redirect they will notice that a lot of their browser settings are going to be modified. This includes the default home page, search engine and new tabs page.
Immediately after this a tracking cookie is imposed on the victims which starts to gather sensitive information about the users. The security experts usually classify it in two categories:
- Personally-Identifiable Information — The gathered data can be used to expose the victims identity. Such information includes the victim’s name, address, number, preferences, passwords and account credentials.
- Anonymous Data — This type of data is made up primarily of information related to the system. It is mainly composed of data about the hardware components and software configuration.
The behavior patterns can be reconfigured depending on the target hosts. In certain cases the malware code can be used to deliver additional threats to the compromised machines. This includes all kinds of Trojans and Ransomware.
The Trojans allow the hackers to take over control of the victim machines and spy on the user while the ransomware encrypt sensitive data and blackmail the victims for a ransom sum payment.
After the infection has infiltrated the browser the victims will be redirected to the hacker controlled page. It is made up of several components that adhere to a design that imitates well-known web services and legitimate search engines.
The top menu bar lists Google services and several options that are related to the malware’s functions. In the center of the page there is the search engine with links to popular services placed underneath it. The bottom bar displays the current weather conditions .
We remind all victims that the links and services offered by the All In One Office redirect link to hacker-controlled pages. They can be used in phishing attacks by forwarding the users to scam sites. This is a popular tactic used to access their account credentials and passwords.
All search queries also deliver sponsored or ad content that does not represent the best possible outcome.

All in One Office – Privacy Policy
The privacy policy shows that the site is operated by a comapny called Axel Division LP and shows the extent of the gathered information.
As soon as the infection is caused the site starts to extract all kinds of data. A partial list includes the following entries:
- IP Address
- Referral Data
- Browser Type and Version
- Interaction Activities
- User Preferences
- Contact Information (name, e-mail address, shipping address and zip code)
- Demographic Information (age, gender, occupation and household income)
The gathered data is pooled into large databases that can then be sold to other parties such as marketing agencies.

Remove All in One Office Redirect
To remove All in One Office manually from your computer, follow the step-by-step removal instructions provided below. In case the manual removal does not get rid of the hijacker redirect and its files completely, you should search for and remove any leftovers with an advanced anti-malware tool. Such a program can keep your computer safe in the future.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove All In One Office from Windows.
Step 1: Scan for All In One Office with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





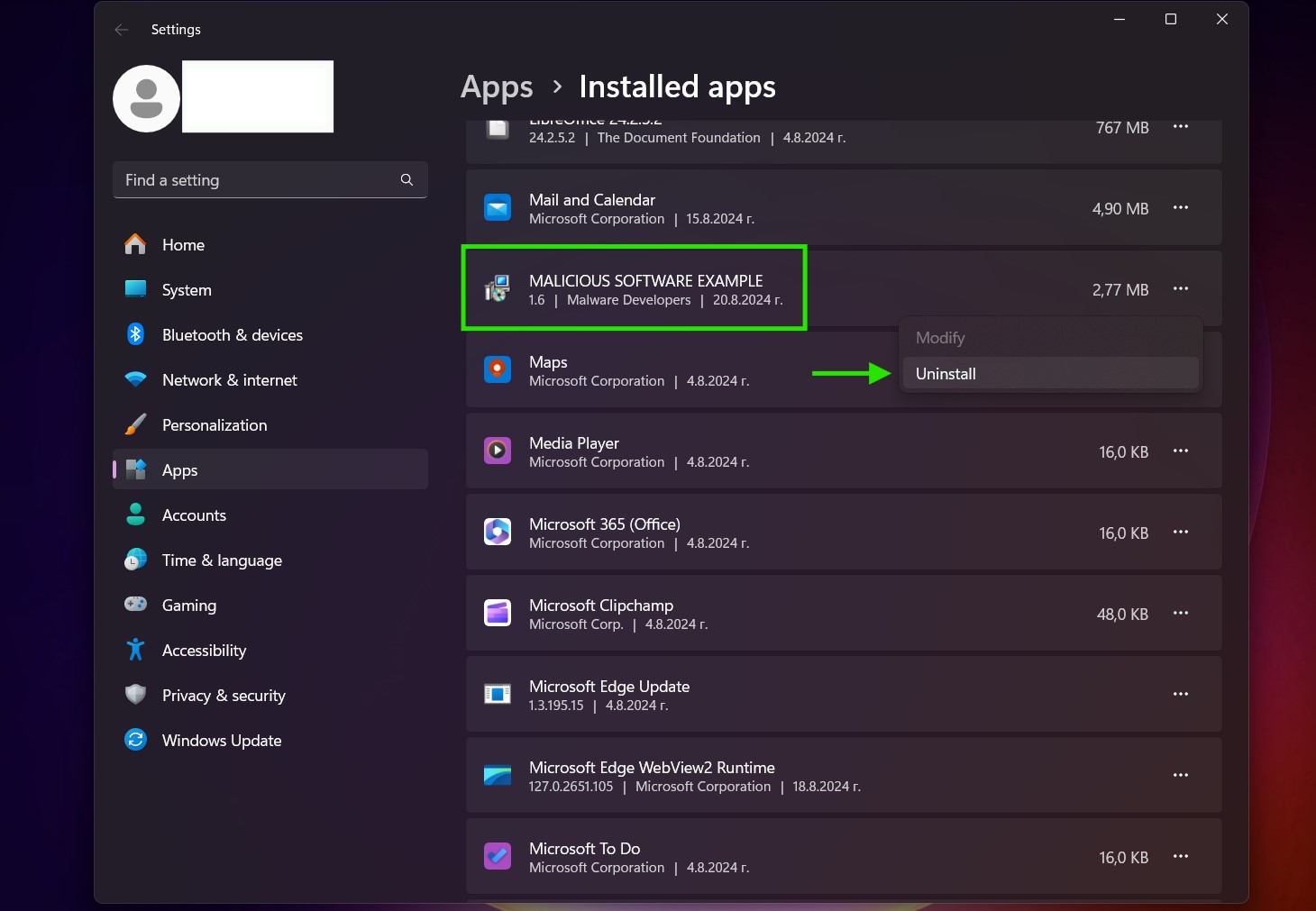
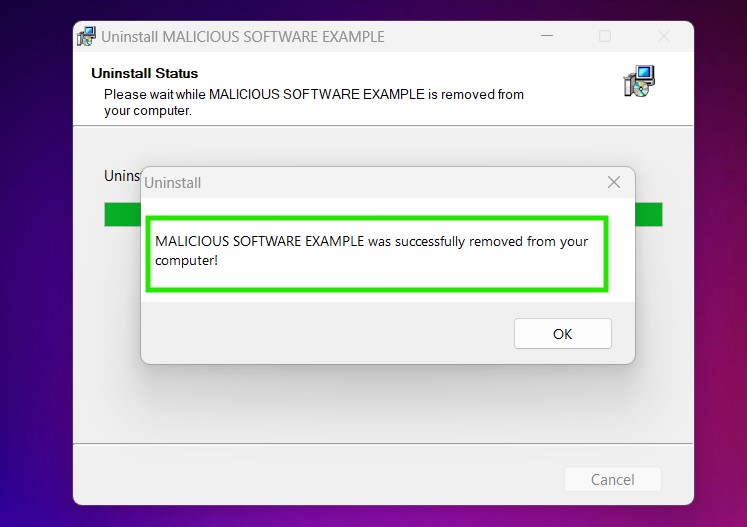
Step 3: Uninstall All In One Office and related software from Windows
Uninstall Steps for Windows 11
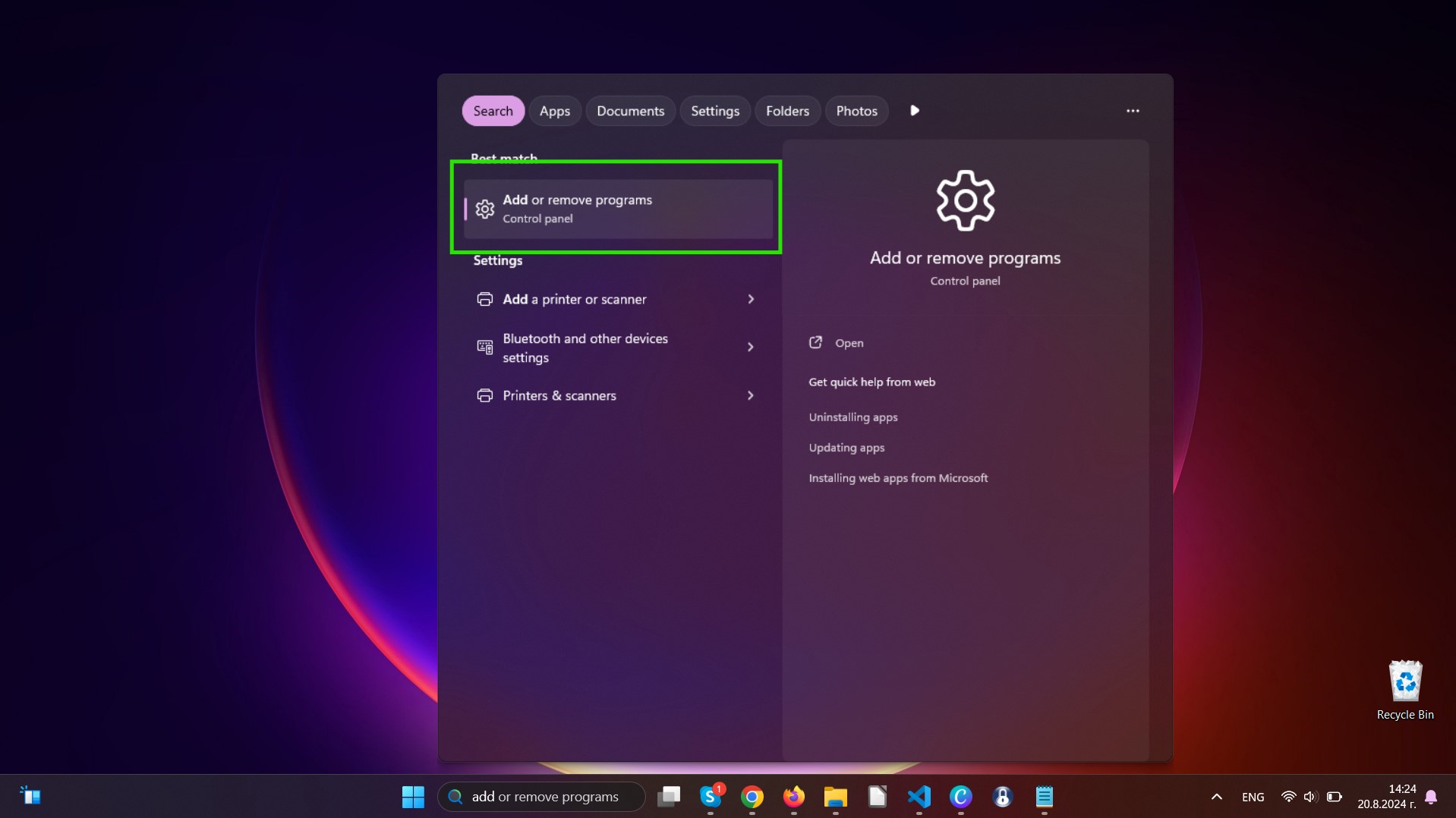
Uninstall Steps for Windows 10 and Older Versions
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by All In One Office on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by All In One Office there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for All In One Office (Windows).
Get rid of All In One Office from Mac OS X.
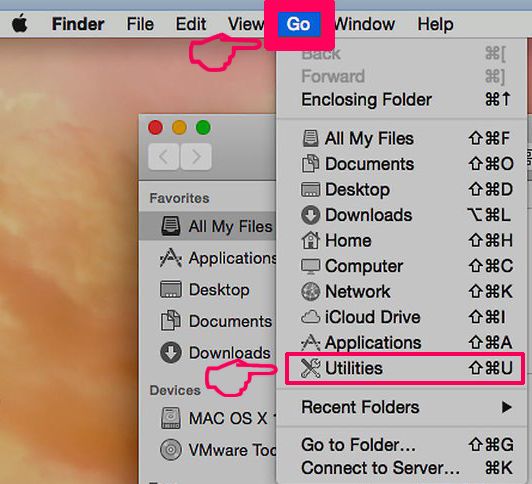
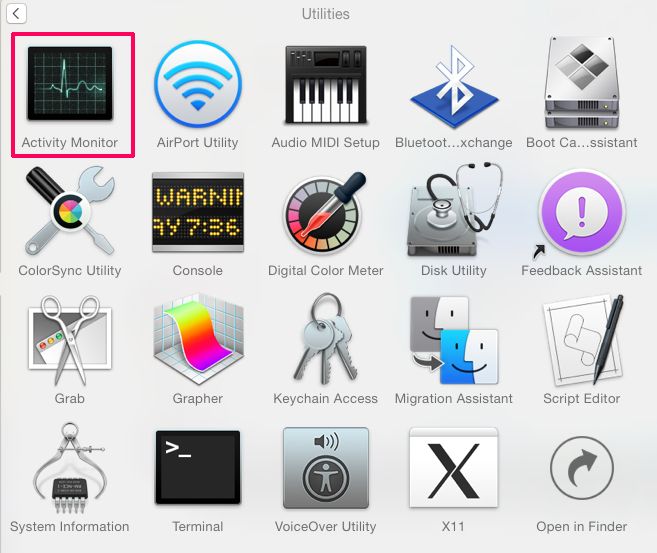
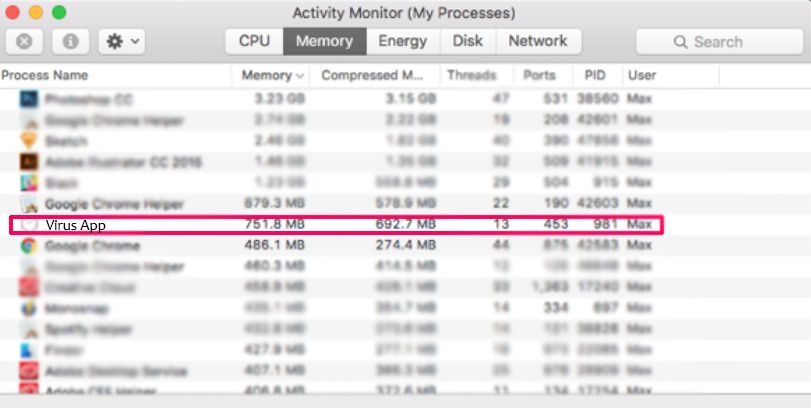
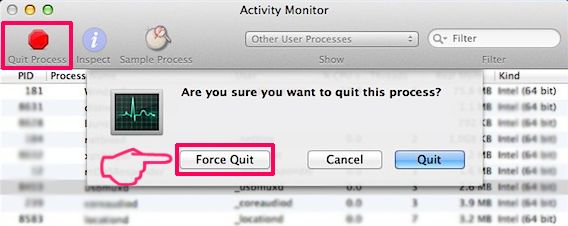
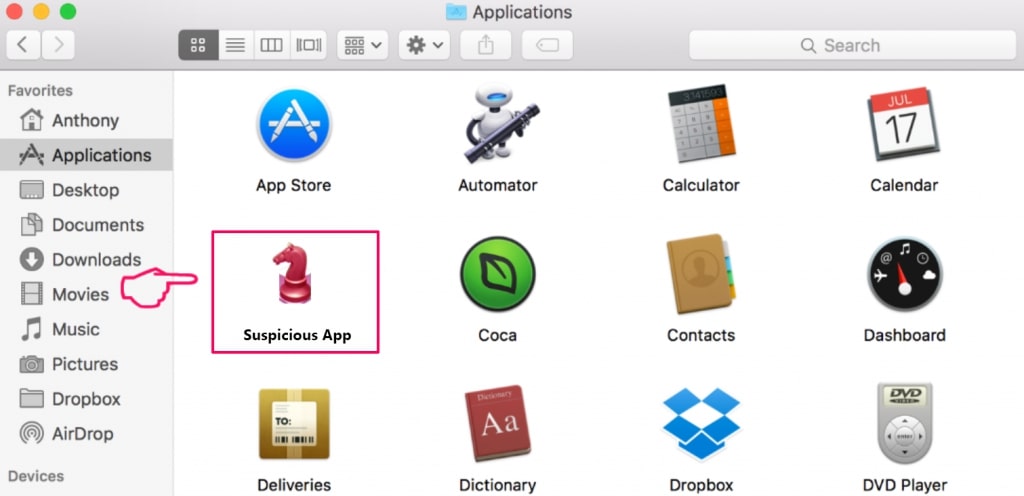
Step 1: Uninstall All In One Office and remove related files and objects
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to All In One Office. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove All In One Office via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
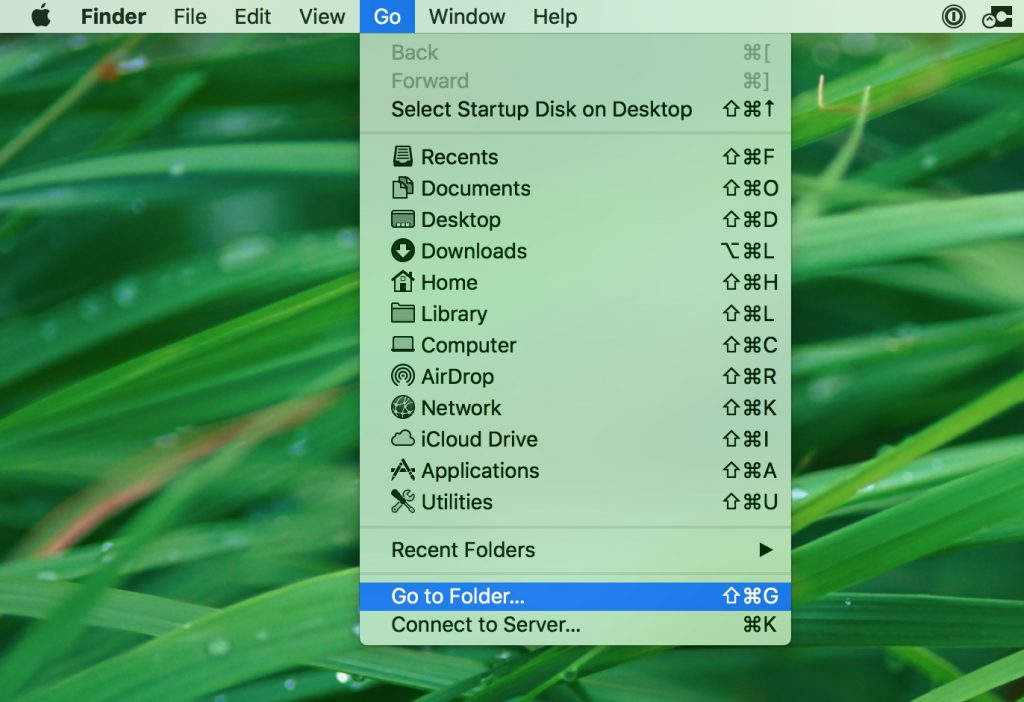
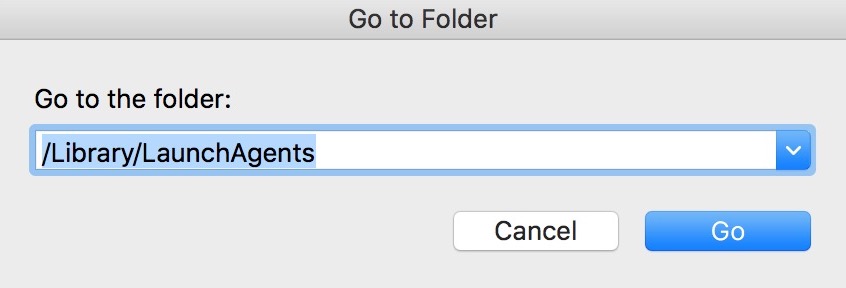
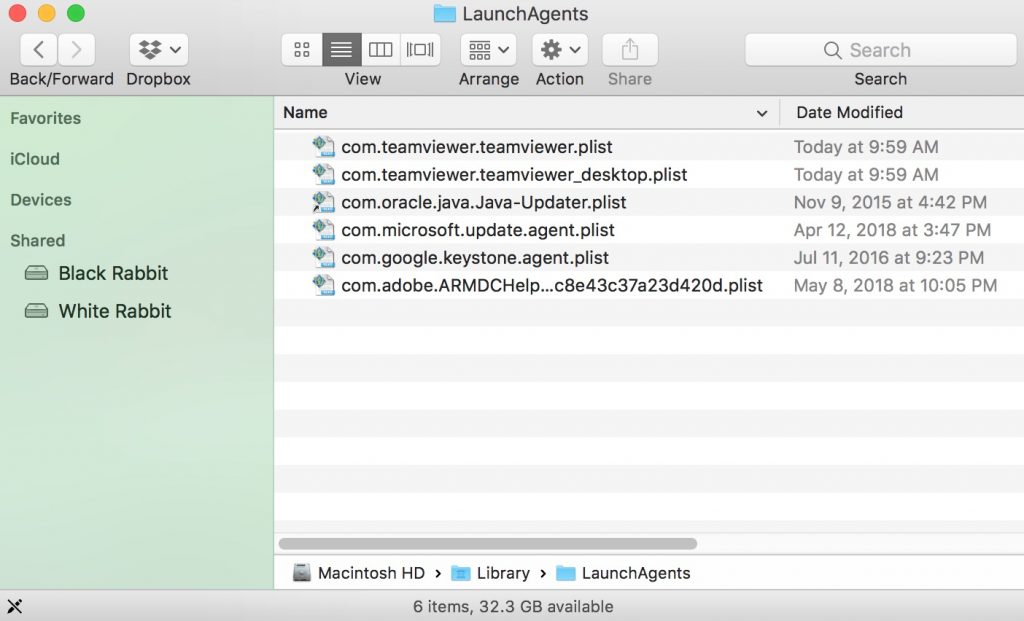
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove All In One Office files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as All In One Office, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for All In One Office (Mac)
Remove All In One Office from Google Chrome.
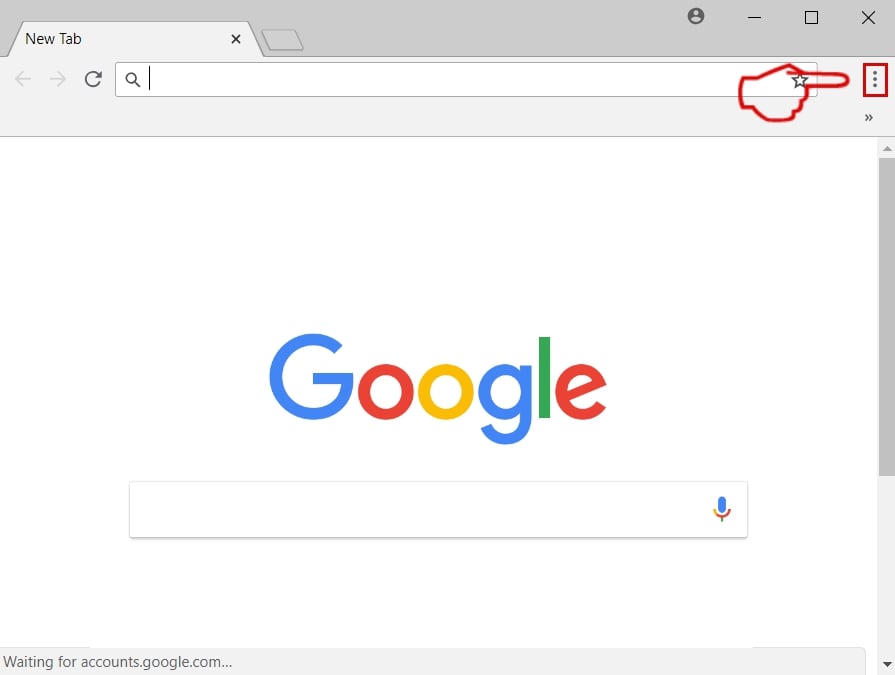
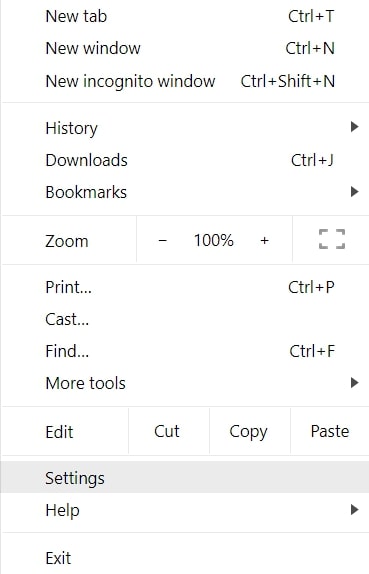
Step 1: Start Google Chrome and open the drop menu
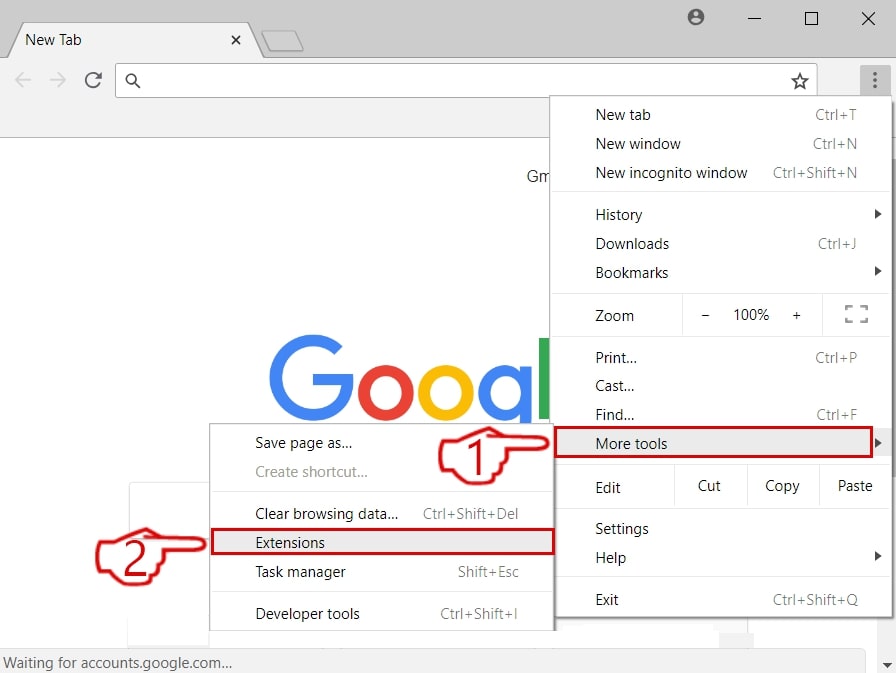
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
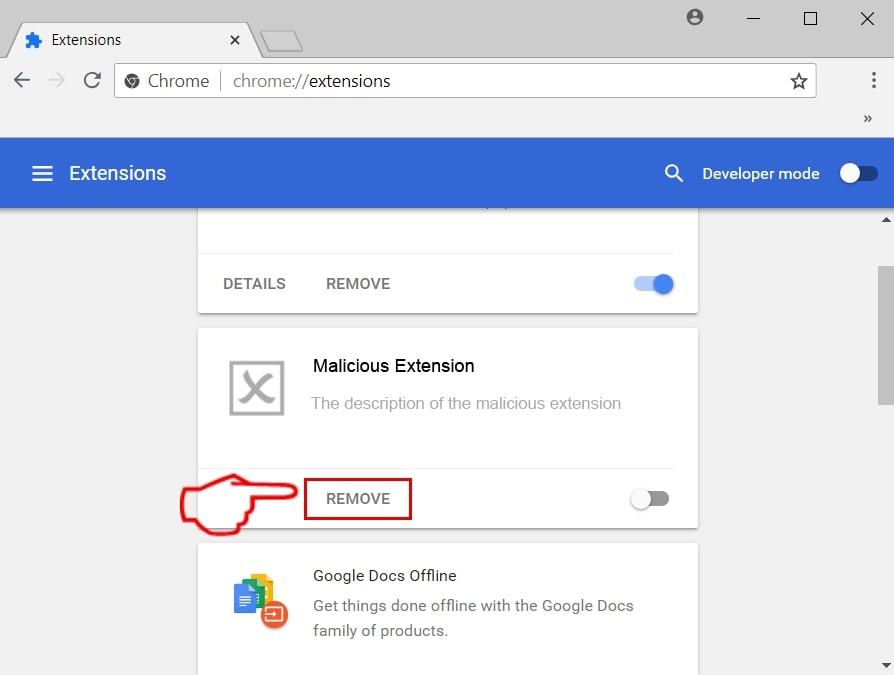
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase All In One Office from Mozilla Firefox.
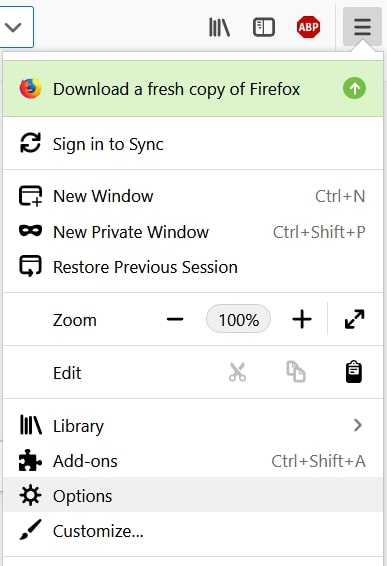
Step 1: Start Mozilla Firefox. Open the menu window:
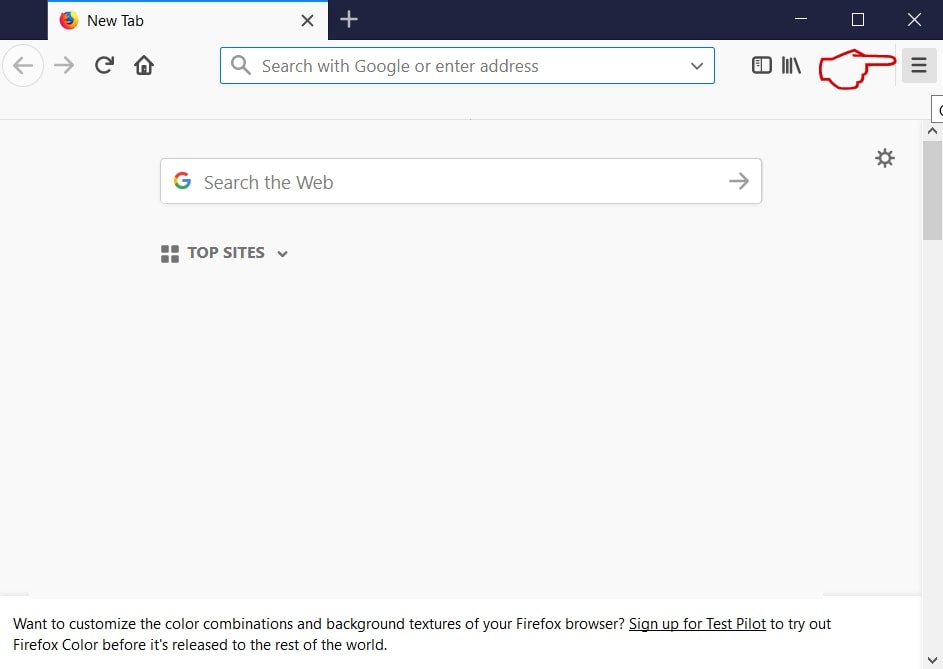
Step 2: Select the "Add-ons" icon from the menu.
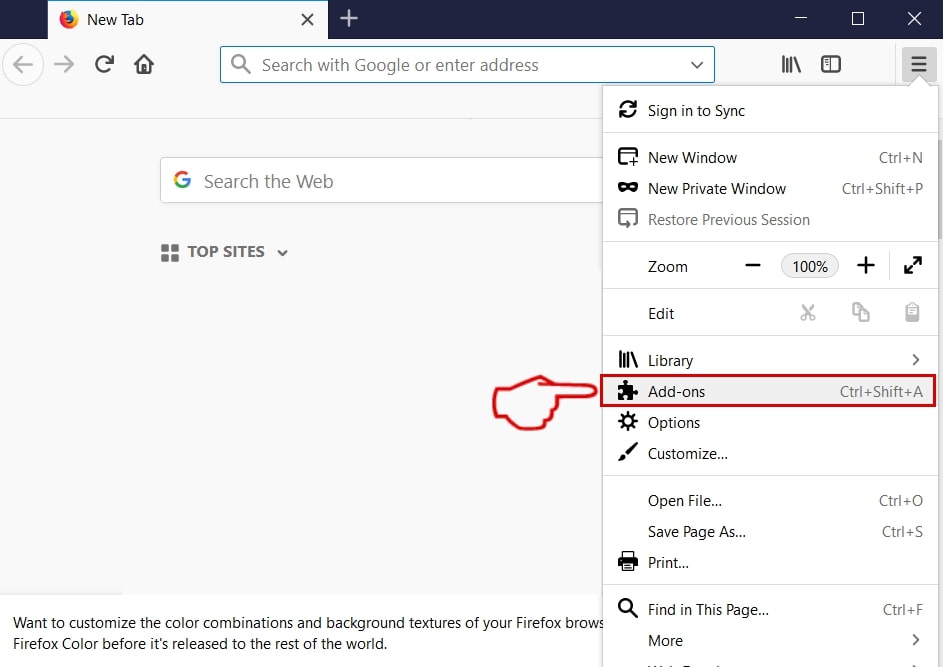
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
Uninstall All In One Office from Microsoft Edge.
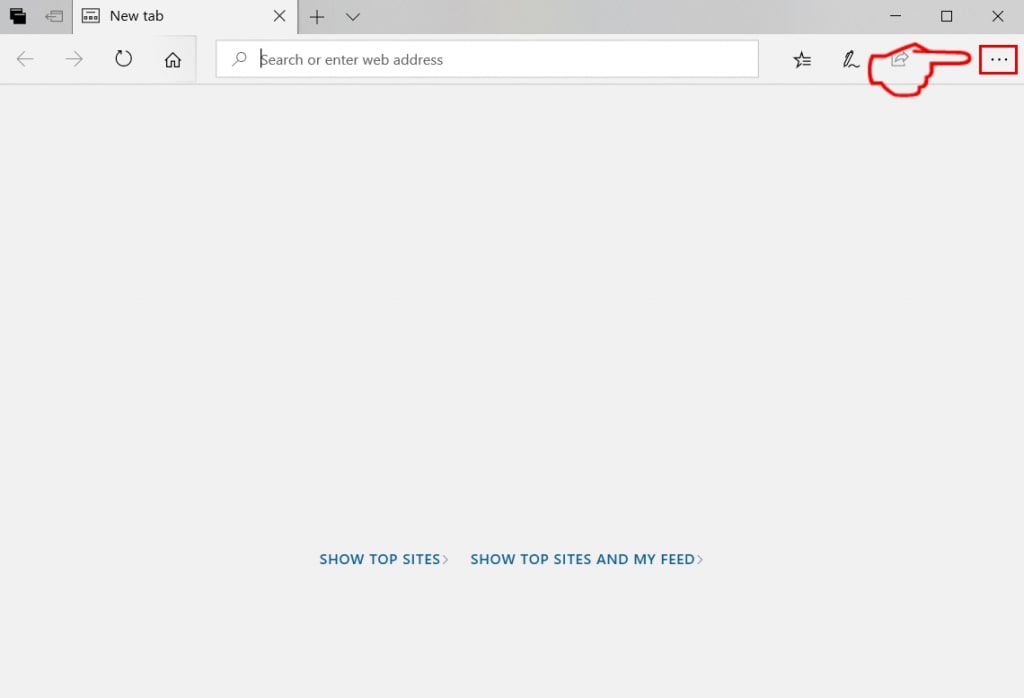
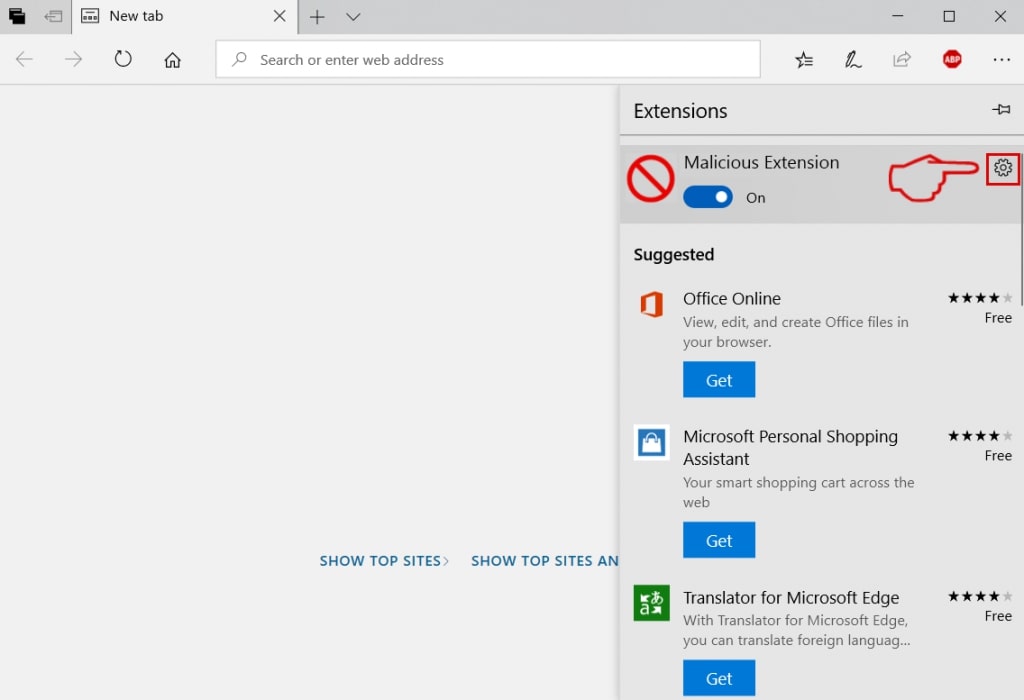
Step 1: Start Edge browser.
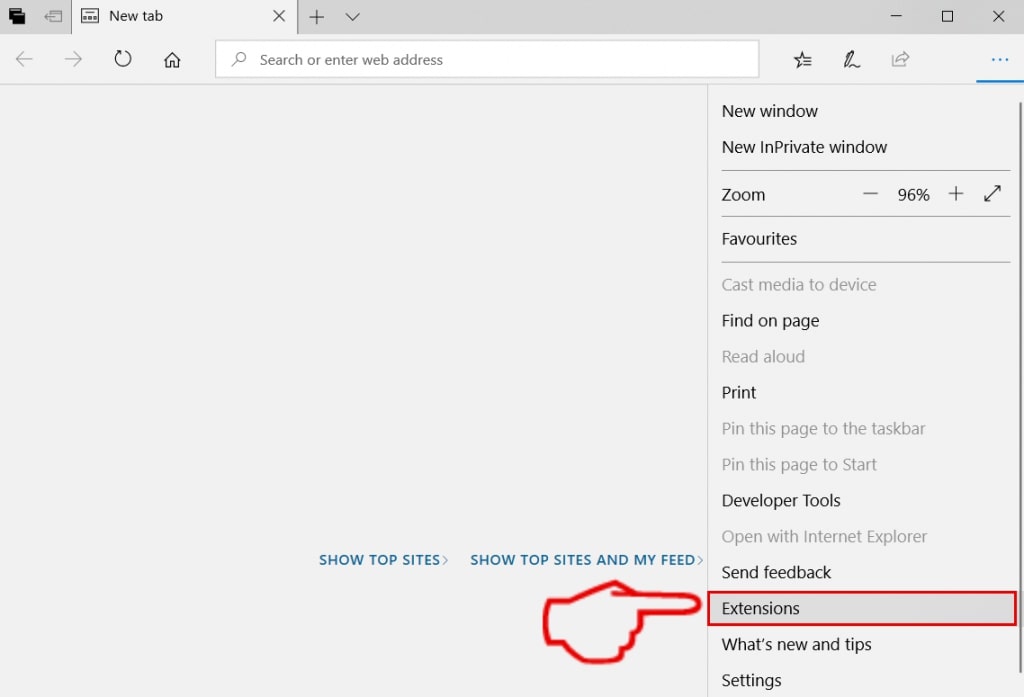
Step 2: Open the drop menu by clicking on the icon at the top right corner.
Step 3: From the drop menu select "Extensions".
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
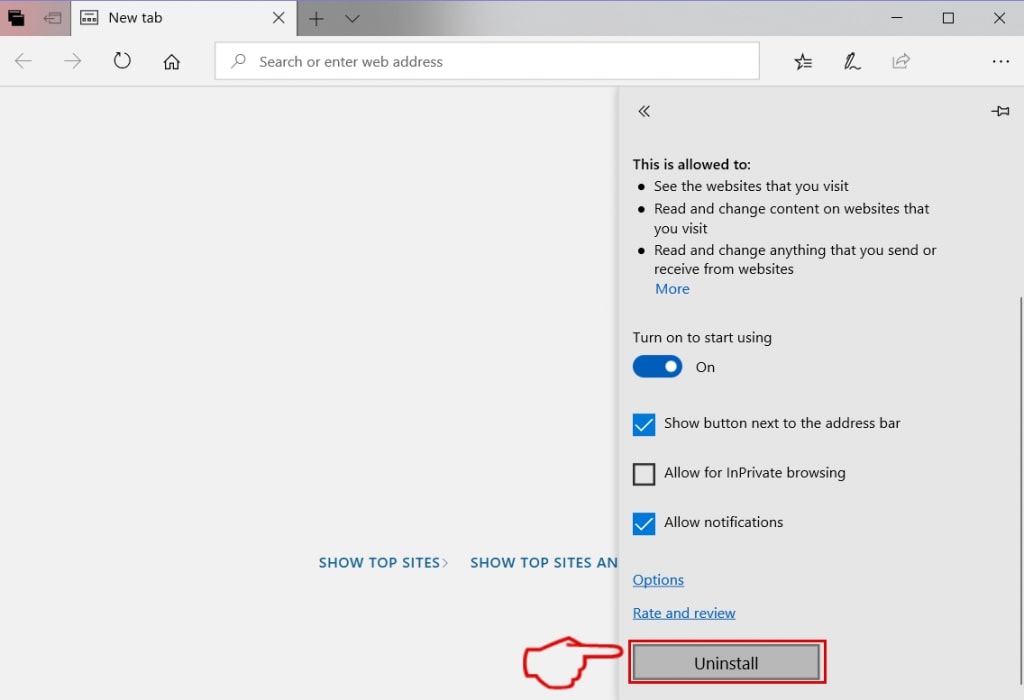
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
Remove All In One Office from Safari
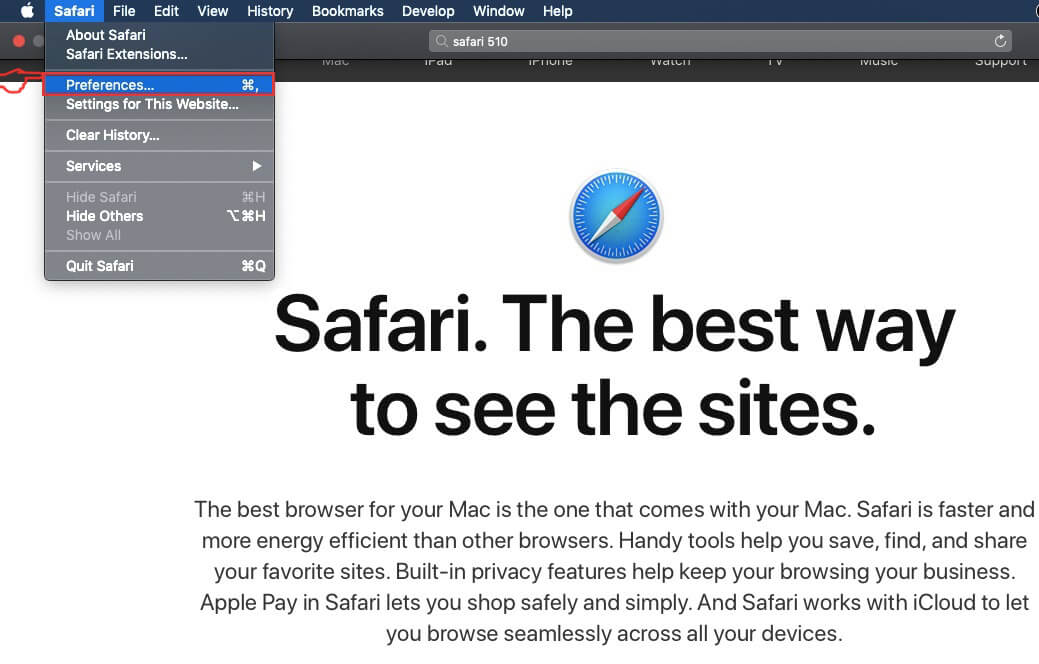
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
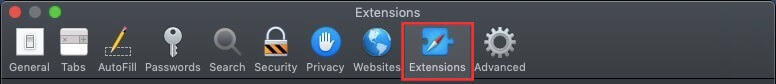
Step 4: After that, select the 'Extensions' Tab.
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
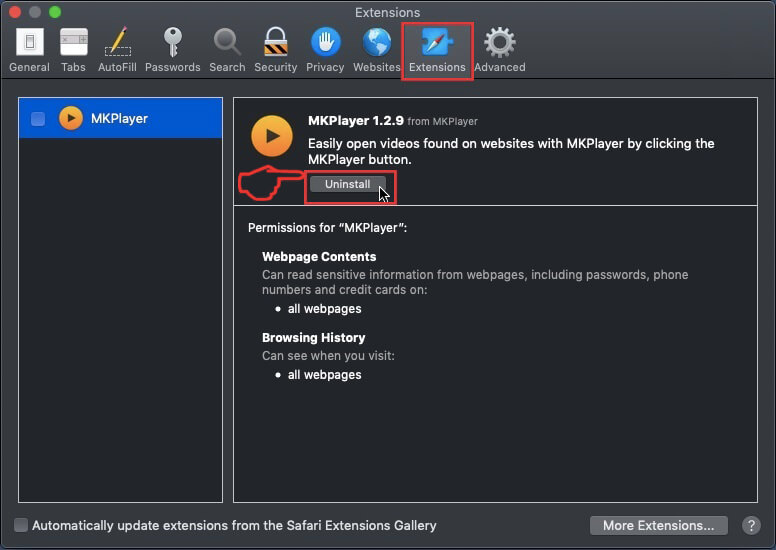
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the All In One Office will be removed.
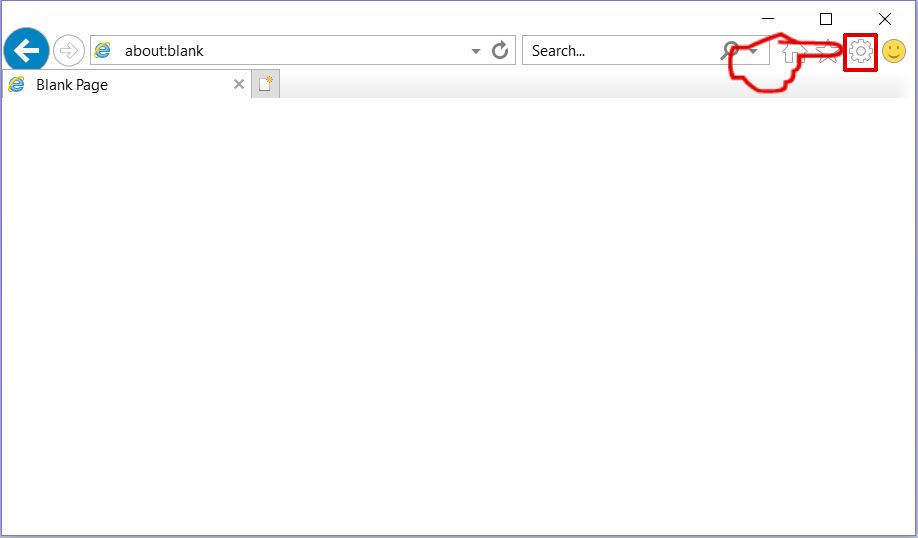
Eliminate All In One Office from Internet Explorer.
Step 1: Start Internet Explorer.
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
Step 3: In the 'Manage Add-ons' window.
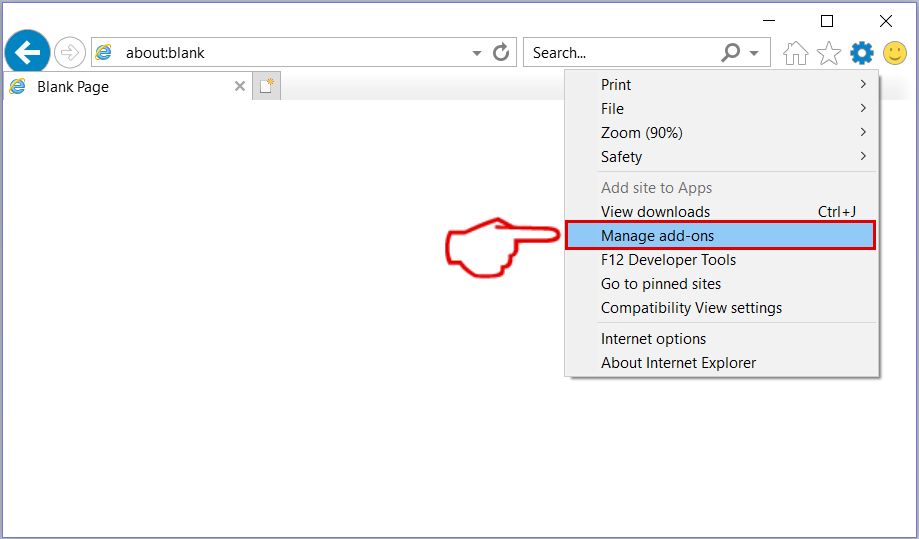
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
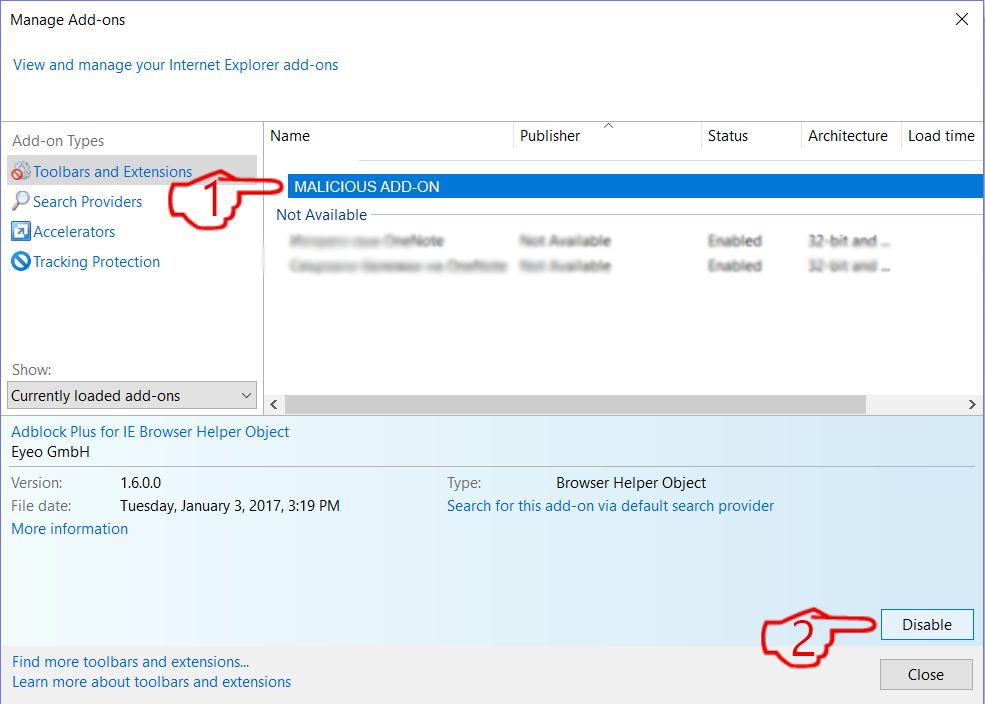
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
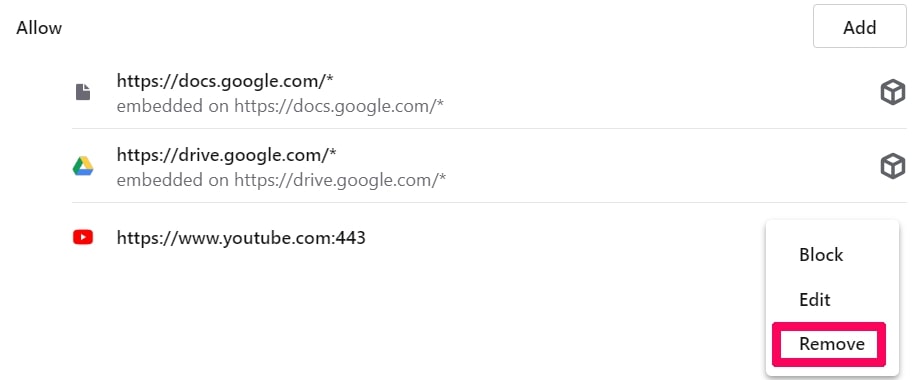
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
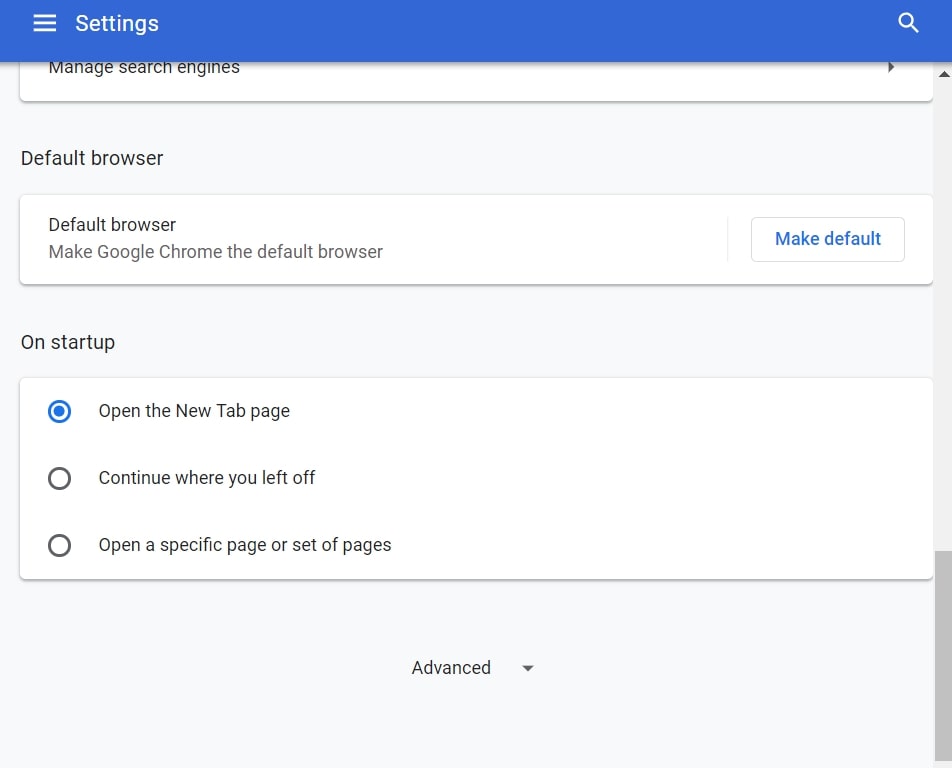
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
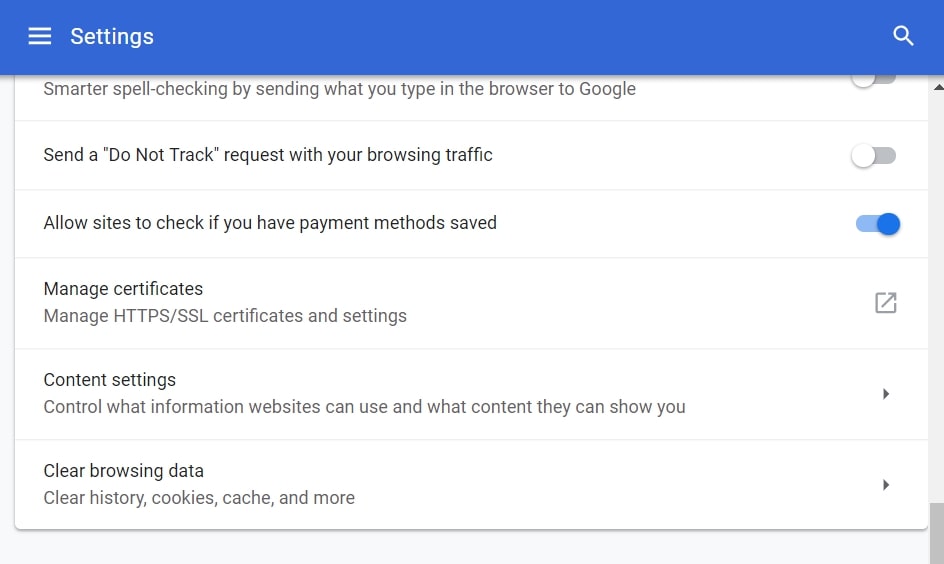
Step 3: Click “Content Settings”:
Step 4: Open “Notifications”:
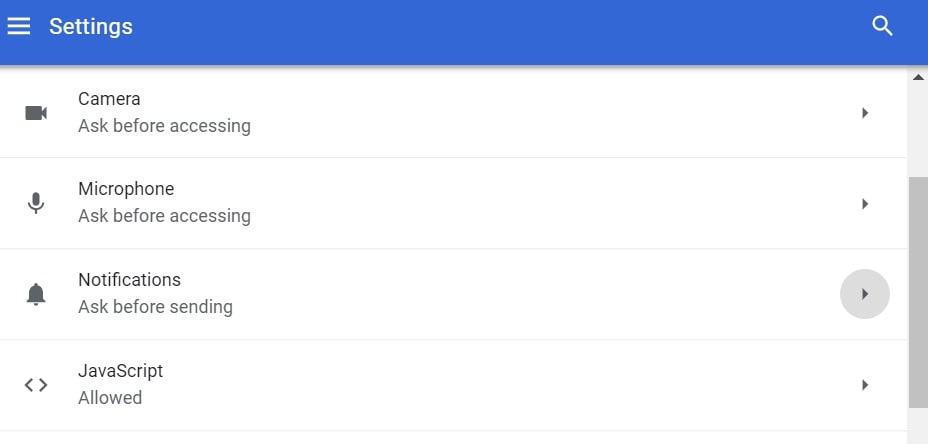
Step 5: Click the three dots and choose Block, Edit or Remove options:

Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
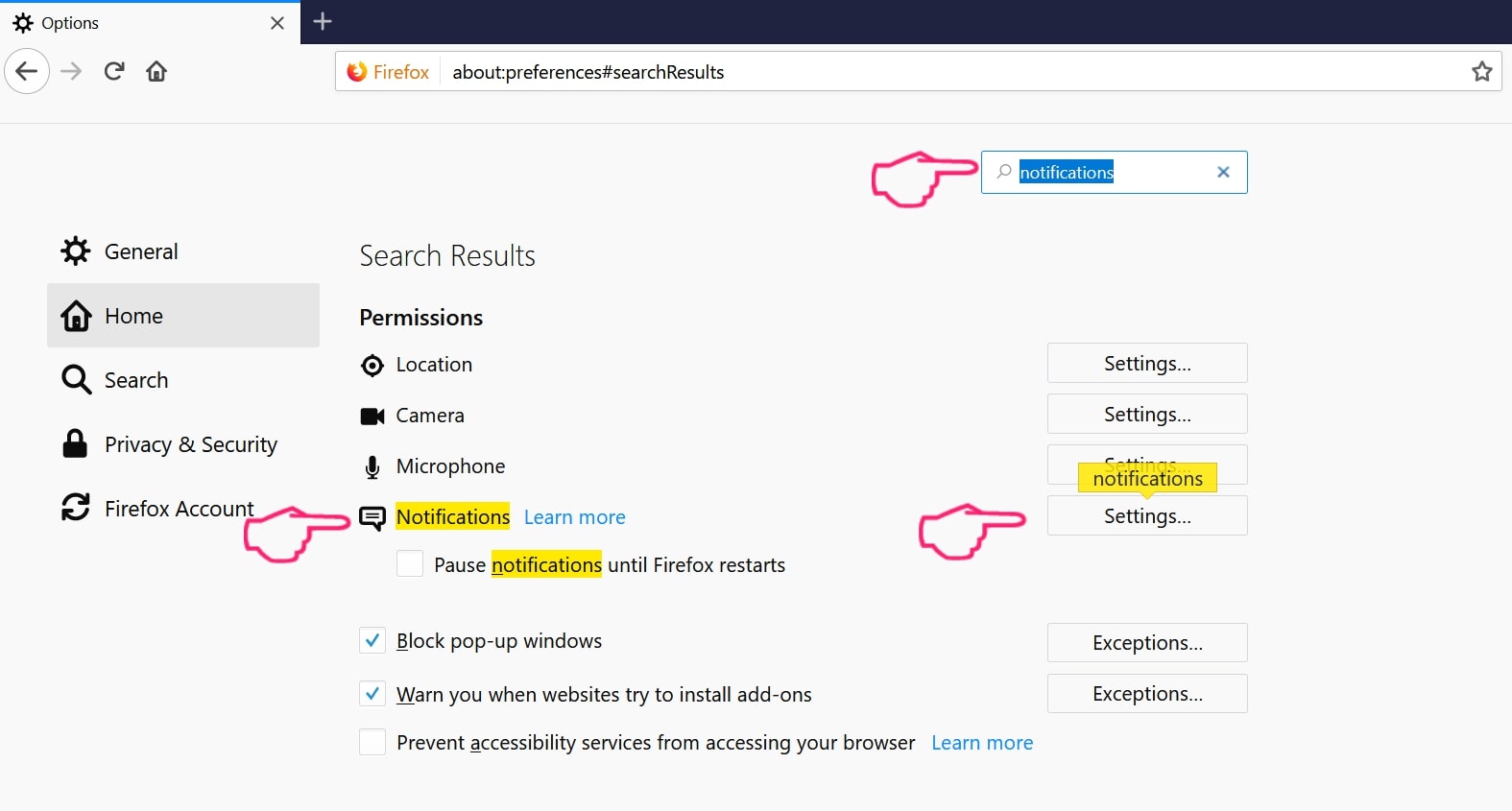
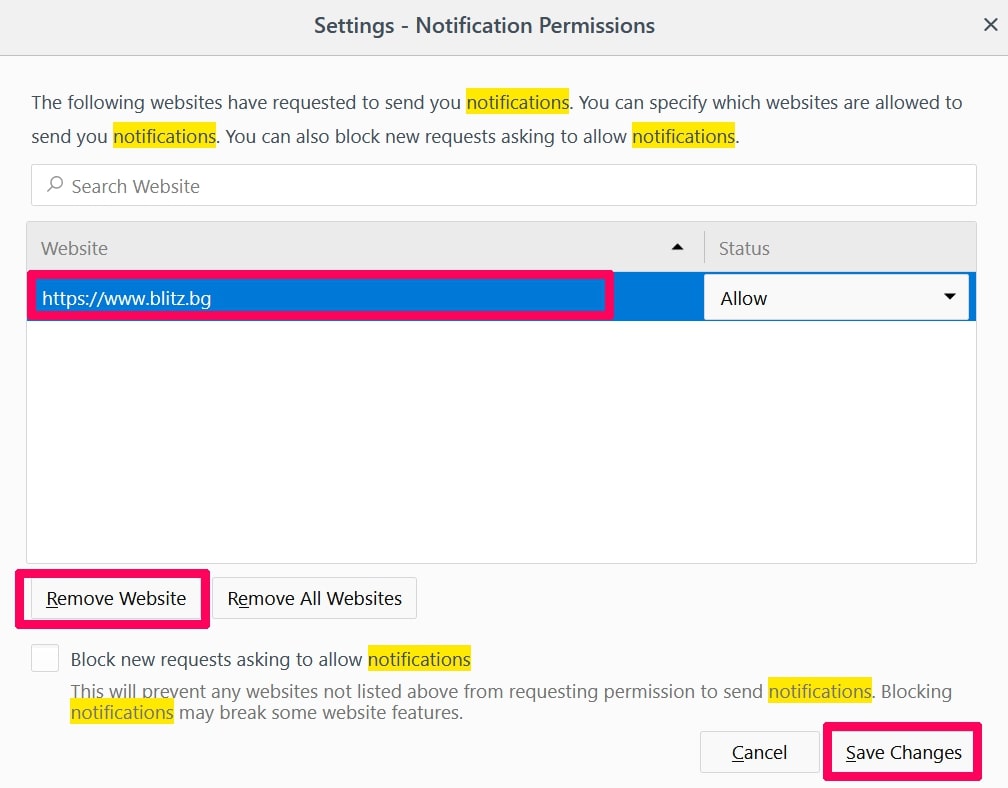
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
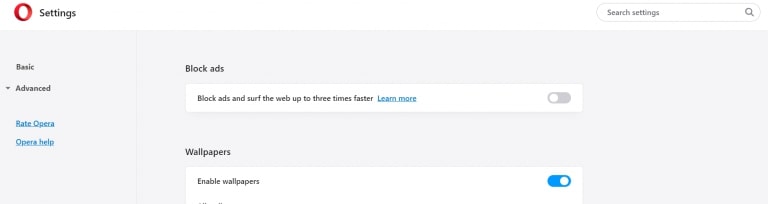
Step 2: In Setting search, type “Content” to go to Content Settings.
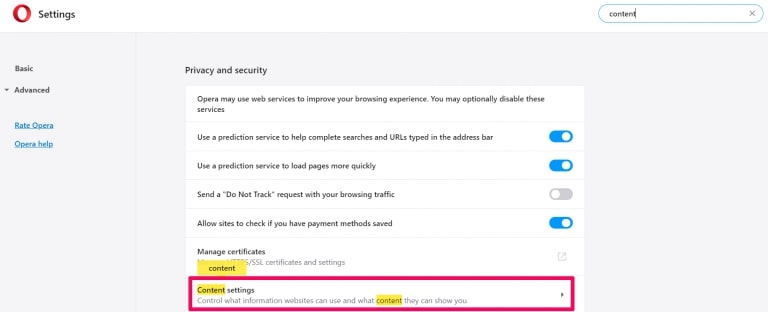
Step 3: Open Notifications:
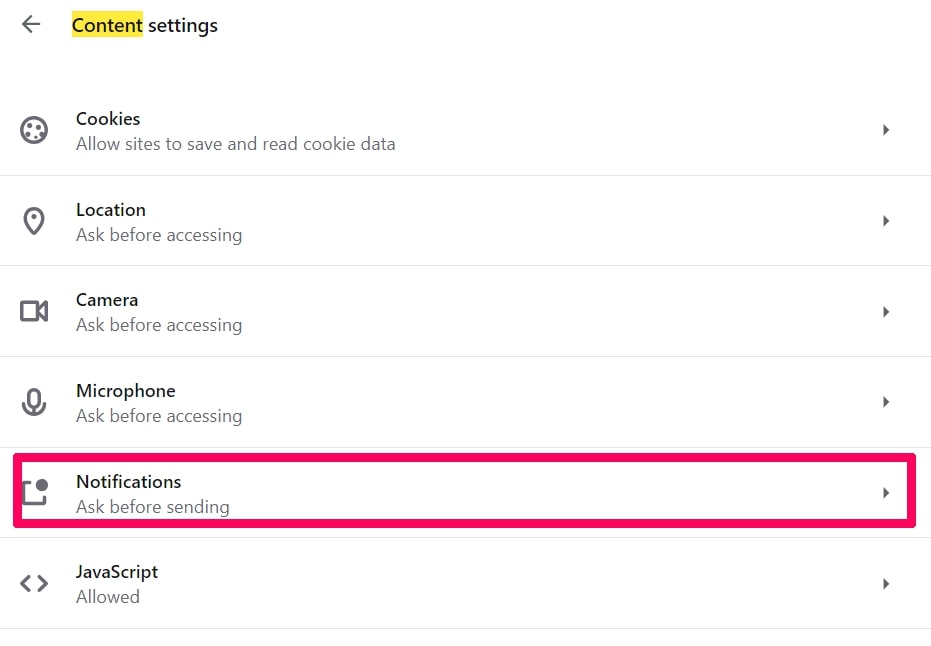
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
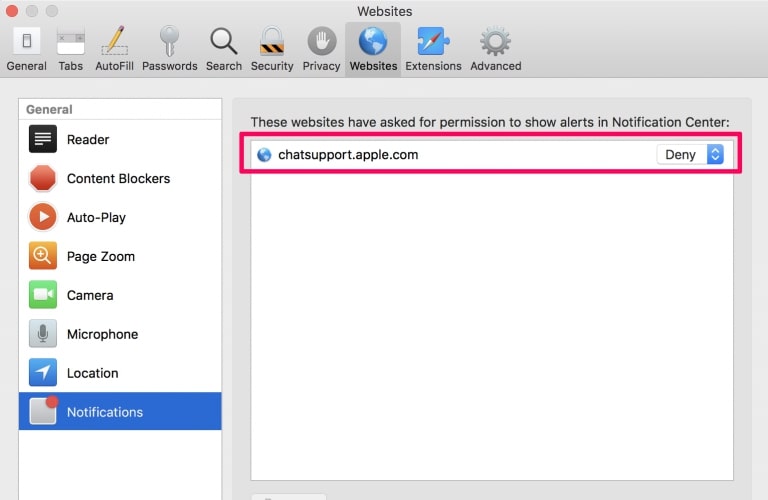
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
All In One Office-FAQ
What Is All In One Office?
The All In One Office threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of All In One Office?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like All In One Office?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does All In One Office Work?
Once installed, All In One Office can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
All In One Office can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is All In One Office Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the All In One Office Research
The content we publish on SensorsTechForum.com, this All In One Office how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on All In One Office?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the All In One Office threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.