How dangerous are software supply chain attacks?
The European Union Agency for Cybersecurity, shortly known as ENISA recently analyzed 24 recent attacks, discovered between January 2020 and early July 2021, only to conclude that strong protection is not sufficient enough.

Some of the attacks the agency analyzed include the cases of Kaseya, SolarWinds Orion software, CDN provider Mimecast, Codecov, Apple Xcode, Accellion.
“Based on the trends and patterns observed, supply chain attacks increased in number and sophistication in the year 2020 and this trend is continuing in 2021, posing an increasing risk for organizations. It is estimated that there will be four times more supply chain attacks in 2021 than in 2020,” ENISA said.
One of the reasons for the increase of supply chain attacks may be the robust security protection organizations have been using lately. This has made attackers move towards suppliers and managed providers, causing “significant impact in terms of downtime of systems, monetary losses and reputational damages.”
First of all, what is the definition of supply chain?
Supply chain is an ecosystem that includes processes, people, organizations, and distributors dedicated to the development and delivery of a final solution or a product. In terms of cybersecurity, supply chain refers to a wide range of software and hardware resources, cloud or local storage, distribution mechanisms such as web applications, and management software. Here are the four key elements of a supply chain:
Supplier: is an entity that supplies a product or service to another entity.
Supplier Assets: are valuable elements used by the supplier to produce the product or service.
Customer: is the entity that consumes the product or service produced by the supplier.
Customer Assets: are valuable elements owned by the target.
What is a supply chain attack?
ENISA says that “a supply chain attack is a combination of at least two attacks. The first attack is on a supplier that is then used to attack the target to gain access to its assets. The target can be the final customer or another supplier. Therefore, for an attack to be classified as a supply chain one, both the supplier and the customer have to be targets.”
Supply chain attack taxonomy
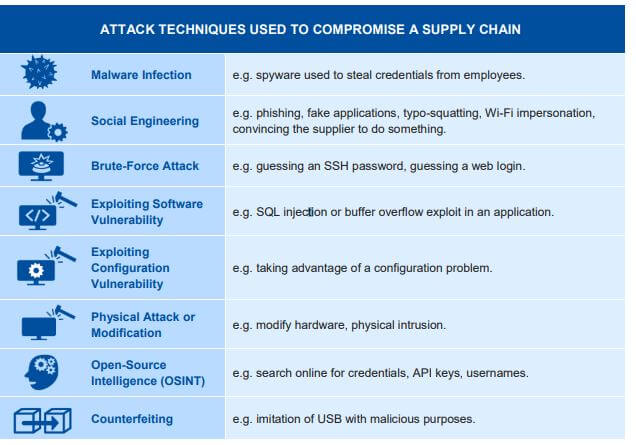
According to the taxonomy of a supply chain attack proposed by ENISA, when attacking a supplier, cybercriminals can use malware, social engineering, brute forcing, software or configuration vulnerabilities, and open-source intelligence. When supplier assets are targeted, cybercriminals target pre-existing software, software libraries, code, configurations, data, processes, hardware, people, and the supplier.
On the customer’s side, attack techniques used to compromise the customer include trusted relationship, drive-by compromise, phishing, malware infections, physical attack or modification, and counterfeiting. Customer assets targeted by the supply chain attackers include data, personal data, intellectual property, software, processes, bandwidth, finances, and people.
“Supply chain attacks can be complex, require careful planning and often take months or years to execute. While more than 50% of these attacks are attributed to APT groups or well-known attackers, the effectiveness of supply chain attacks may make suppliers an interesting target for other, more generic, types of attackers in the future,” he agency noted in the report. Thus, it is critical for organizations to focus their security not only within their own infrastructure but also on the suppliers. This is especially true for cloud service providers and MSPs, as evident by recent attacks.