A new report by Swiss web security company ImmuniWeb focuses on the state of security of the world’s 100 biggest airports.
The results of the analysis reveal that 97 of 100 airports lack efficient protection in their systems to defend their websites, mobile apps, and public clouds.
Only three airports, Amsterdam Airport Schiphol, Helsinki-Vantaa Airport and Dublin Airport, passed the researchers’ test flawlessly with no issues detected. These three airports, the researchers said, may serve “a laudable example not just to the aviation industry but to all other industries as well.”
How was ImmuniWeb’s test on airport security carried out?
The researchers applied the same “enhanced methodology” they used in a previous research on application security of the top banking institutions. The methodology also borrows approaches taken from open-source intelligence (OSINT), such as:
– Discovery and non-intrusive security testing of public cloud storages, such as AWS S3;
– Monitoring of Dark Web exposure, such as marketplaces and forums;
– Monitoring of public code repositories, such as GitHub.
It is noteworthy that ImmuniWeb decided to investigate airport cybersecurity after the issue was acknowledged during the 2020 World Economic Forum. In a separate report on the aviation industry, the World Economic Forum urged airports to address the emerging cybersecurity issues.
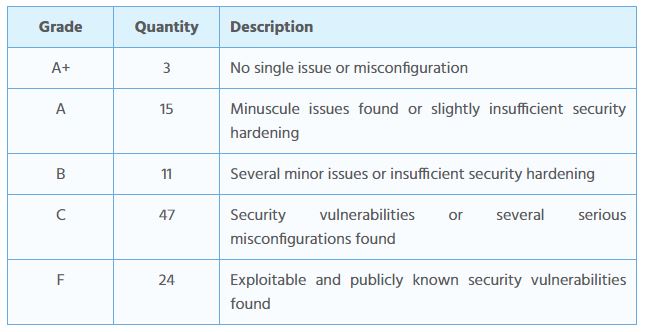
In terms of web application security, only three of the 100 airports received an A+ grade.
“As many as 24 of the main websites had a failing “F” grade, meaning that they had an outdated software with known and exploitable security vulnerabilities in CMS (e.g. WordPress) and/or web component (e.g. jQuery). Some of the websites even had several vulnerable components”, the report noted.
More details are available in the table below:
Overview of the discoveries:
Main Website Security:
97% of the websites contain outdated web software
24% of the websites contain known and exploitable vulnerabilities
76% and 73% of the websites are not compliant with GDPR and PCI DSS respectively
24% of the websites have no SSL encryption or use obsolete SSLv3
55% of the websites are protected by a WAFMobile Application Security:
100% of the mobile apps contain at least 5 external software frameworks
100% of the mobile apps contain at least 2 vulnerabilities
15 security or privacy issues are detected per app on average
33.7% of the mobile apps outgoing traffic has no encryptionDark Web Exposure, Code Repositories and Cloud:
66% of the airports are exposed on the Dark Web
72 out of 325 exposures are of a critical or high risk indicating a serious breach
87% of the airports have data leaks on public code repositories
503 out of 3184 leaks are of a critical or high risk potentially enabling a breach
3% of the airports have unprotected public cloud with sensitive data
Cyberattacks against Airports
In September 2019, the Bristol Airport in the UK became a victim of a ransomware attack. As a result, the airport’s in-house TV screens needed to display arrival and departure flight information were affected and literally blacked out.
It is very challenging for an airport to function properly without displaying arrival and departure schedules. To handle the outcomes of the ransomware infection, airport employees had to get creative. They were using paper posters and whiteboards to announce all flight information, for nearly three days.