With the release of the latest Iphone7, Apple has again become the center of attention, making people look for their web pages more while surfing online. Having realized this, cyber criminals have created multiple phishing web pages that have different aims, all of them malicious. We at SensorsTechForum have decided to follow up on that and see what exactly is behind the cyber-criminals’ mind.
With the release of the latest Iphone7, Apple has again become the center of attention, making people look for their web pages more while surfing online. Having realized this, cyber criminals have created multiple phishing web pages that have different aims, all of them malicious. We at SensorsTechForum have decided to follow up on that and see what exactly is behind the cyber-criminals’ mind.
SIDENOTE: This post was originally published in September 2016. But we gave it an update in August 2019.

What Risks Are Out There
Phishing pages may be created with different levels of risk in mind – it depends on what the cyber-criminals are thinking.
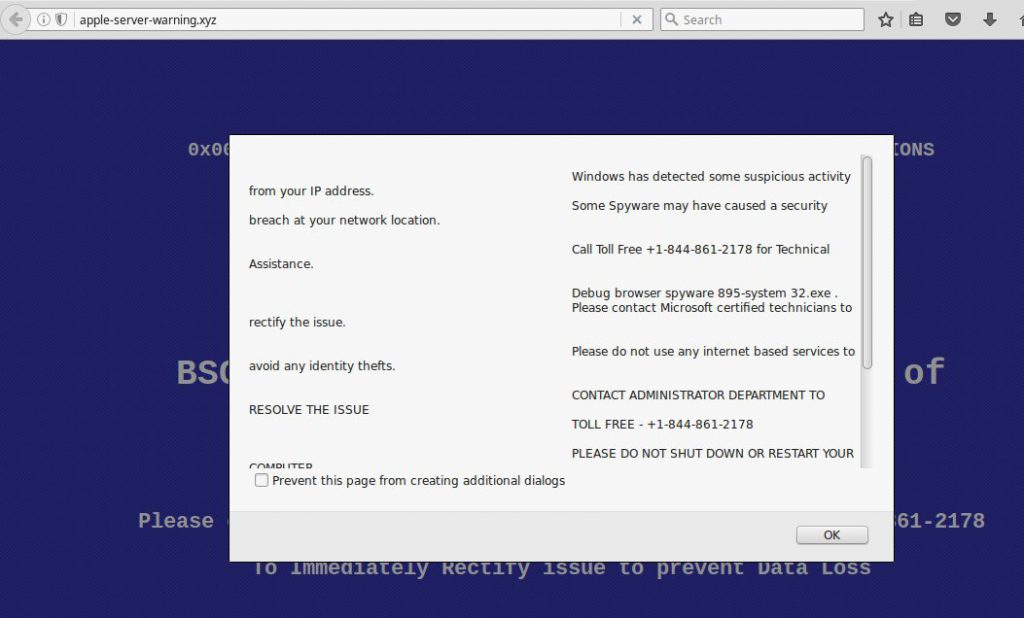
One phishing web page may promise to users that they may receive a free iPhone if they fill out their personal details. There are other phishing web pages that may be presented to users of Apple devices, claiming that there is a problem with their phone, MacBook or other Apple device and adding a tech support caller number like the one on the picture below:
This is known as tech support scam, and it aims to get users to make expensive phone calls to non-existent tech support representatives, resulting in having to pay large phone bills.
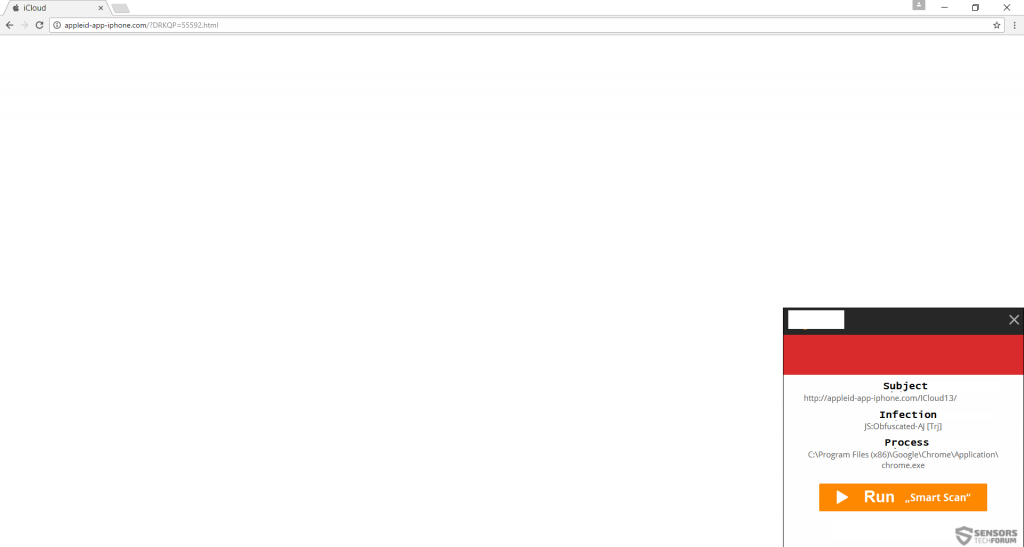
The most dangerous type of phishing web pages, however, are the ones that are infested with malware, such as applied-app-iPhone(.)com that attempted to infect us with an obfuscated malware, via a malicious JavaScript.
Such web links are a very often met method of infections, and they may not only be phishing for information and display fraudulent claims, but they may also infect your computer with ransomware viruses, banking malware, Trojans and other viruses.
During our researcher we have also stumbled upon multiple phishing web pages that were not only fake but some of them represent an actual threat to computers:
Applelocationticloud(.)com
Icloud-server-apple-verify(.)com
Information-appleid-apple-icloud-safe(.)com
My-account-apple(.)com
Resolved-idapple(.)com
Apple-server-warning(.)xyz
verified.apple.com.confirm.account.information.glitterfarms.com/Apple
pc-mac-defender1(.)info/message-from-apple
apple-tech-support(.)online
forget-idapple(.)com
id-sign-apple(.)com
applied-iphone-id(.)com
apple-icloudiphone-security(.)com
apple-icloudiphone-support(.)com
apple-os9-icloud-server(.)com
appleinc-iphone-gps(.0com
findmyappleiphone(.)com
localizer-appleicloud(.)com
mydevice-apple(.)com
apple-app-gps(.)com
apple-app-store-icloud-id(.)com
apple-find-myiphone(.)com
apple-icloud-server-verify(.)com
inc-apple-ios(.)com
phone-apple-id(.)com
support-myapple(.)com
login-findmydevice.com
applied-iclouddu(.)com
applid-map(.)com
apple-ios9-lid(.)com
iclduod(.)com
apple-icloud1(.)com
icloud-rescure(.)com
located-apple(.)com
apple-icloudappid(.)science
fd-id-apple(.)com
findiphone-apple(.)com/verify/
appleidsupport(.)com
apple-icloud-myios(.)com
id-iclloudd-appplle(.)com
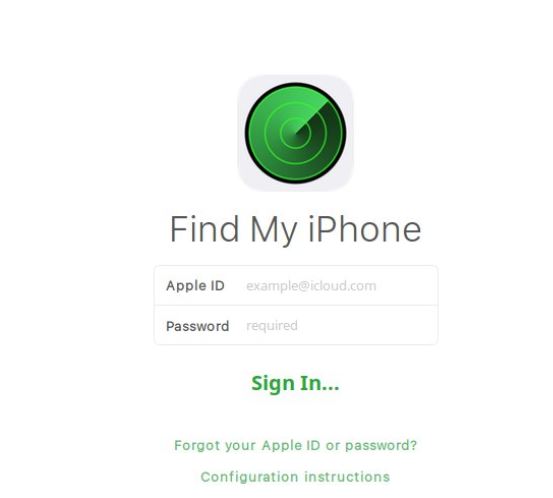
This is just a very small portion of of the domains that are fake and phish for different information. Most of them were representing fake iCloud web pages that aim to steal login details from Apple iCloud accounts:
However, there were also other interesting web pages, like the “revolutionary” fake iPhone finding web page, that claims it can locate your iPhone:

How to Protect Yourself from Phishing
It is important to know how to protect yourself from phishing web pages. To do that, besides having a reliable anti-malware program and a browser extension that actively blocks phishing web pages, you should also know how to identify a phishing web page. Websites such as Scamadviser offer protection against phishing pages by simply telling you how risky a web page you are visiting actually is. Not only this, but you should also take a look at the URL of the web page and check in on websites such as CqCounter to establish the actual owner of the domain, it’s location and even it’s ISP and IP addresses as well as other domains associated with it.