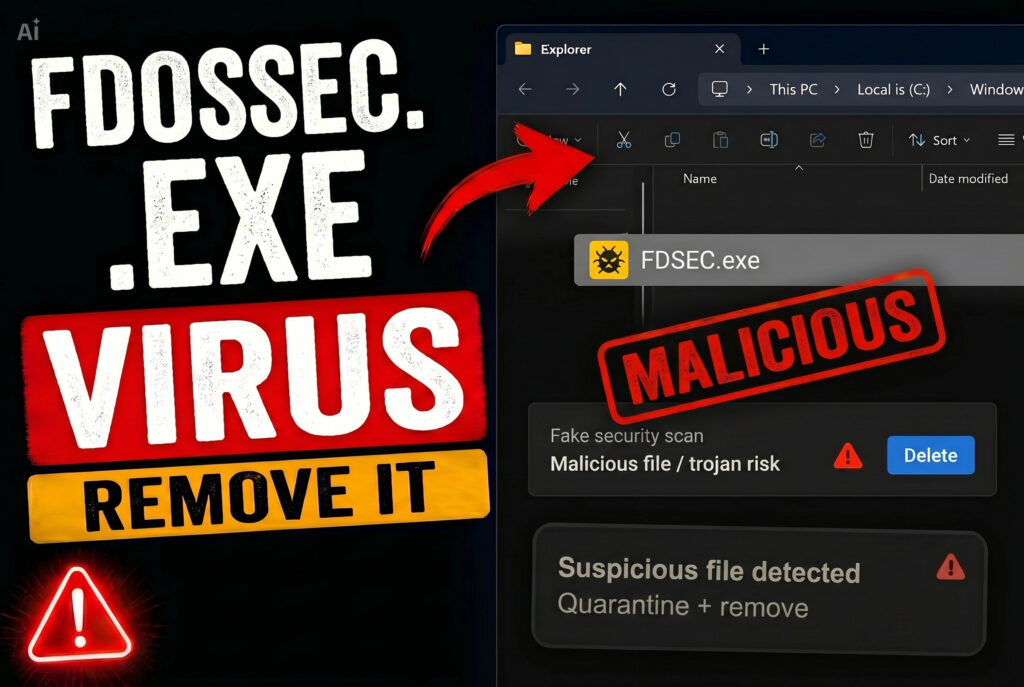
FDSEC.exe Virus – How to Remove It
What is FDSEC.exe? Your antivirus flagged FDSEC.exe, or you found it running in Task Manager and you’re not sure whether it belongs there — read this article right now before doing anything else. The name alone should raise a red…


![Iplogger.org Virus – How to Remove It [Fix] iplogger.org virus removal](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/iplogger_org_virus_removal_fix_article_hero.jpg-1024x687.png)
![Borderlands 2 Spyware – How to Remove It [Guide] Borderlands 2 Spyware - How to Remove It [Guide]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/Borderlands-2-Spyware-How-to-Remove-It-Guide-1024x576.png)
![Graphite Spyware – Detect and Delete It [Steps] Graphite Spyware - Detect and Delete It [Steps]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/Graphite-Spyware-Detect-and-Delete-It-Steps-1024x576.png)

![Trojan.Agent.H – How to Remove It [Fix] Trojan.agent.h malware removal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/trojan-agent-h-malware-how-to-remove-it-1-1024x683.png)
![Backdoor.Agent.SW – Removal Guide [Solved] Backdoor.Agent.SW Detection and Removal](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/Backdoor.Agent_.SW-Detection-and-Removal-1024x683.png)
![Trojan:HTML/Redirector Virus – How to Delete It [Fully] TrojanHTMLRedirector Virus - How to Delete It](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/TrojanHTMLRedirector-Virus-How-to-Delete-It-Fully-1024x683.png)
![AsyncRat Virus – How to Remove It [Solved] AsyncRat-Virus-How-to-Remove-It-Solved](https://cdn.sensorstechforum.com/wp-content/uploads/2026/05/AsyncRat-Virus-How-to-Remove-It-Solved-1024x683.png)
![Hugamb.at – Is It Safe? [Scam/Malware] Hugamb.at - Is It Safe? [Scam/Malware]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/Hugamb.at-Is-It-Safe-ScamMalware-1024x683.png)
![Trojan Win32/JScealTaskExec – How to Remove It [Solved] Trojan Win32/JScealTaskExec - How to Remove It](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/Trojan-Win32JScealTaskExec-How-to-Remove-It-Solved-1024x683.png)
![Gayfemboy Malware – How to Remove It [Fix] gayfemboy-malware-removal](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/gayfemboy-malware-removal-guide-1024x576.jpg)
![Lumma Malware [Stealer] – Removal Guide [Fix] lumma malware stealer removal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/lumma-malware-stealer-removal-guide-fix-1024x576.jpg)
![Rabbit Virus Malware – Removal Guide [Fix]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/rabbit-virus-how-to-remove-it-1024x576.jpg)