Computer hackers are leveraging a novel phishing messages technique that is used to deliver dangerous malware to the target computers.
The hackers are creating special sites and sending out email messages that are designed accordingly. It is very possible the hackers are very experienced as they have copied the typical error message design.
Security Certificates Global Phishing Campaign Used To Leverage Trojans
A new phishing tactic leveraging various Trojan payloads has been detected by security researchers. There is no information available about the identity of the group — we anticipate that they are experienced enough to have created this new strategy. The hackers are creating special phishing messages and sites that imitate common browser errors and operating system-like notifications. This means that the sites will be hosted on domain names that sound very similar to the services and companies which are shown.
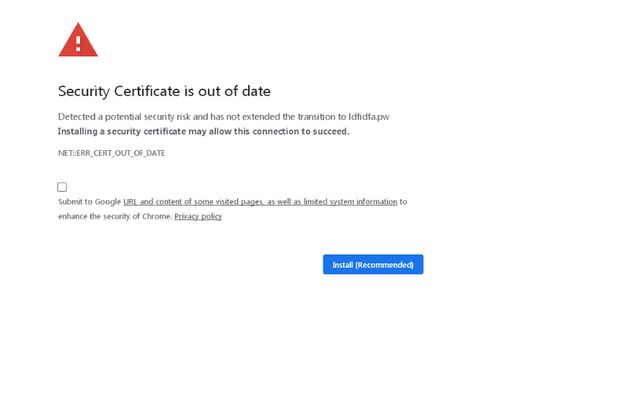
Here’s an example of a browser error related to a security certificate:
Links to the sites and the emails can be sent using different mechanisms. This includes the hosting of landing pages which are hosted on domain names that sound very similar to the companies which are impersonated. They can be linked in different online communities — online forums, chatrooms, social networks and etc.
When such a page is opened by the victims an error notification will be shown which will prompt the users to “update” the definitions. This is an intentional placement — the contents is placed in an iframe which loads a JavaScript code hosted on a third-party site. This means that infection will be loaded from another domain while at the same time the users will not see an address change. If the victims interact with the shown page a malware will be downloaded onto their computer. At this moment there are two particular threats which are delivered via this mechanic — the Mokes Mac Trojan for MacOS and the Buerak Trojan for Windows.