There are many specialist Linux distributions that are designed with security in mind. Even though there are universal distributions that cater for practically all usage many administrators, concerned citizens and penetration testers usually choose specific ones. This article will reveal some of the top choices in 2019 concerning prospective distributions and the reasons why users should install them.
Security and Privacy Linux Distributions in 2019 — Overview
Security distributions are one of the main types of Linux operating systems that computer users can choose from. And even though general-purpose editions like Ubuntu and OpenSuSe can be easily used for private browsing, penetration testing or carrying penetration testing, the releases that are created for these purposes have a distinct advantage. They come pre-configured with all necessary software, in some cases optimized configurations are readily available.
What’s important about security-related distributions is that they might not have the usual end-user bloat and focus on the relevant use cases — for example a privacy-centric operating system will not include any P2P clients and services that will transmit the IP address and open ports on the machines for the purpose of sharing data.
Linux distributions catering to penetration testing or forensic investigation can include special provisions that will not tamper with the local hard disk drive when run from memory. This is very important as it allows the for the hard disk contents to remain unaltered. Only after the user has given permission to write to the disk can such actions be allowed to take place. This mechanism is also observed with privacy-protective systems, they will run from memory and have special web browser configuration settings in order to send out minimal information to the web sites and services that can track the users.
The Linux distributions that are made for penetration testing often include specific hardware optimizations in the kernel code which can allow for better wireless card performance. This is very important as some of the procedures rely on statistical information and metrics which are obtained by security scans.
Qubes OS — Security by Compartmentalization A Popular Choice
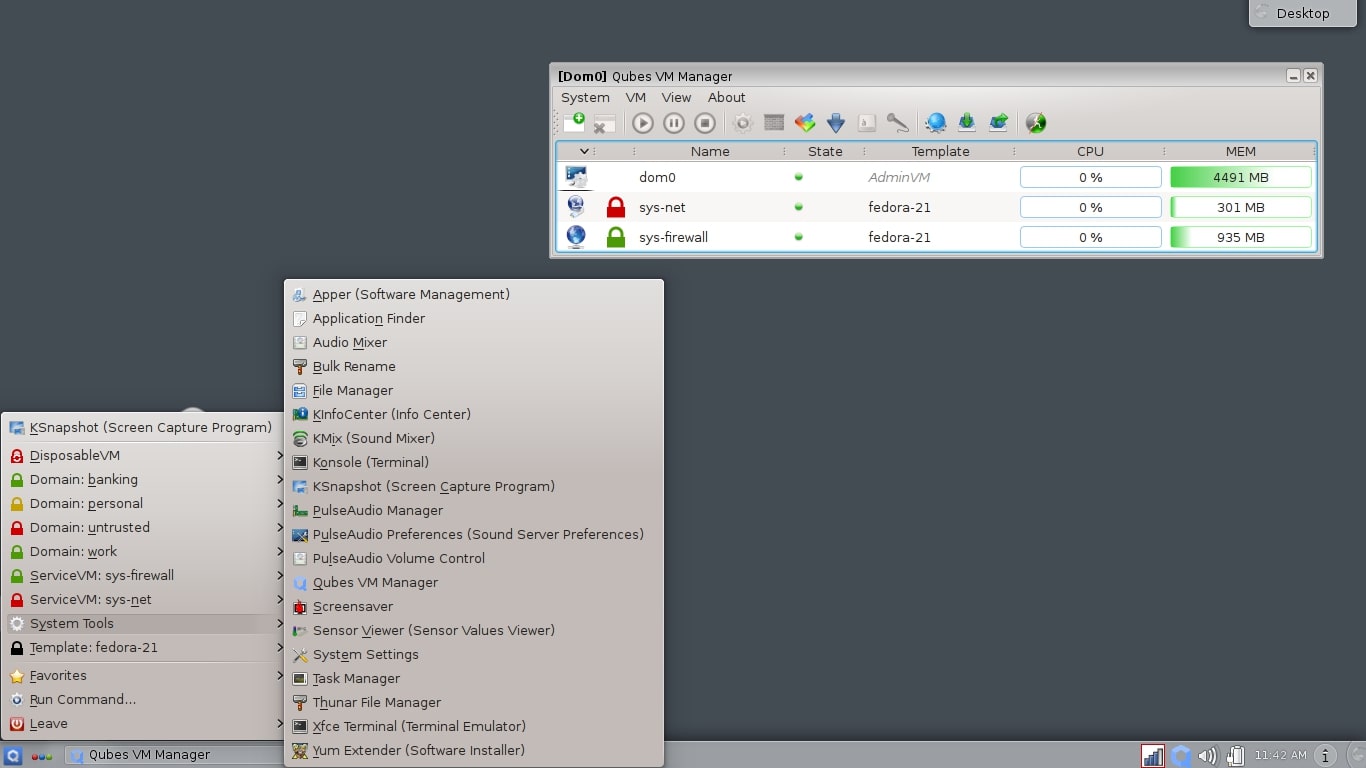
Qubes OS is a popular choice for security experts when running certain services requires that they are isolated from each other. This is done by implementing a distinct approach to virtualization called security by compartmentalization. In reality the effect is that every service or application will be executed on a separate isolated component called qube (hence the name Qubes OS). By definition this can prevent infected browsers, file viruses and other malware from accessing or altering the rest of the system.
End users can distinguish each isolated application by setting out colored window browsers — an easy way to visually identify individual software. In practice even if a virus outbreak occurs it will be limited only to the respective color container.
What’s important about it is that the individual qubes are disposable — they can easily be stopped and removed from the hard drive contents and memory resulting in a clean host on which various applications and services can be run. The containers can isolate both the software and hardware. As a result common attack vectors will be contained within a distinct area of the operating system and prevent wider infection.
Useful functionality of the Qubes OS operating is the ability to sanitize PDF documents and the optional Whonix addition which enables easy access to the TOR anonymous network.
Due to the fact that Qubes can be used for various purposes it is ranked among the most popular Linux distributions which are useful not only for security and privacy-minded users, but also for other cases as well.
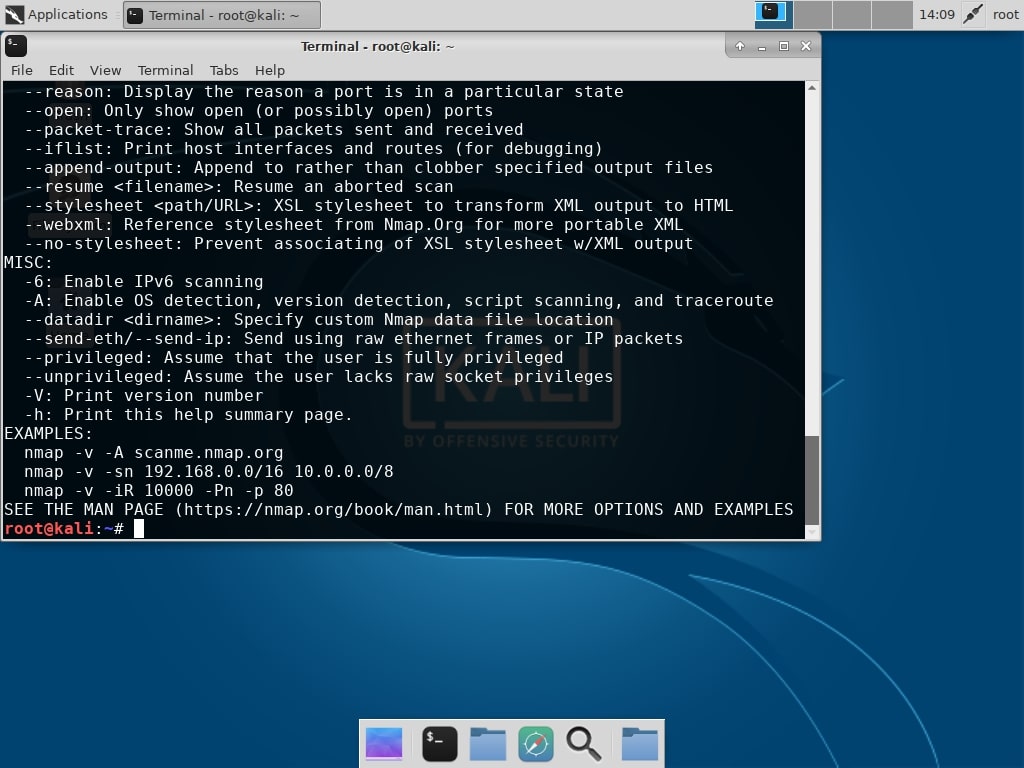
Kali Linux — The Industry-Standard for Penetration Testing
When penetration testing is concerned one of the most commonly listed distributions is Kali Linux. Throughout the years it has turned out to be trusted both by amateurs and experts from both hackers and security experts. This is evident from the fact that most of the penetration testing tutorials and security guides on the Internet and demonstrated in specialist courses exhibit this particular distribution. Not only is the distribution optimized for these use cases it additionally offers some unique features which set it apart from other projects.
The ISO files can be completely customized using recipes and tools, this is especially handy for teams and companies that can design Kali for certain environments and/or tasks. A good example is the so-called ISO of doom which is set-up to boot a self-installing, reverse VPN auto-connecting, network bridging image of Kali. In the majority of cases the users will boot it up using one of the live disk images — a persistent run option is available, as well as full disk encryption. As such the image can house several store profiles.
A “nuke option” is available in the live disk images which will safely delete all data found on the accessible hard drives. This ensures that they cannot be recovered as the wipe functions use strong algorithms that will completely zero-out the contents.
The Kali Linux distribution includes metapackages in its repositories that pull out collections of toolsets (applications and services) useful for orchestrating certain camapigns or carrying out specific tasks. It is also one of the few distributions that implement advanced accessibility features — both voice feedback and braille hardware is supported.
The distribution includes several specialist versions for platforms and devices including the following:
- Unattended PXE Installation — Kali Linux images can be deployed over the internal network using the PXE boot option. This is possible for both the original image and any customized versions that the users can create.
- Raspberry Pi and ARM Device — The Kali Linux developers provide images for board computers such as the Raspberry Pi allowing it to be used in various environments, including IoT devices and low-power computers.
- Kali Linux NetHunter — This is a special ROM overlay for ASOP and Nexus line of phones.
- Kali Linux on Android — A specialist app called Linux Deploy allows for Kali Linux to be installed in a chroot environment on Android systems.
- Cloud Packages — The distribution can be deployed in a cloud environment as Kali Linux has released Amazon EC2 images.
All of these arguments prove that Kali Linux is usually the preferred distribution when conducting penetration testing on computers and networks. It is adopted by both hackers, security specialists and also used as example in education and training of professionals.
Related: Kali Linux – This Is What You Need to Know Before You Start
Tails Linux — Anonymous Browsing for Everyone

The Tails Linux distribution is a specialist release that aims to preserve both privacy and anonymity when browsing. It is most widely known for being one of the main tools to circumvent censorship by connecting to the worldwide anonymous TOR network. The established connections are tunneled through servers and endpoints across the planet, the sites that are accessed have no way of knowing who exactly is visiting it.
The way it works is that it runs from a live CD medium and does not leave any traces on the hard drive contents, all programs are executed from memory. Email communications and instant messaging protocols are secured using state-of-the-art cryptographic tools that are available in the bundle.
Users can choose to use the distribution as it is pre-configured to connect to the Tor anonymous network by default. The security rules block all direct connection to the Internet sites that are not routed through TOR for security reasons. It is particularly useful for journalists and whistleblowers as it bypasses most of the Internet censorship that is administered by the state and Internet service providers in some countries. Using the anonymous networks allows the site visitors to conceal their location and access Internet sites and services that may otherwsise be inaccessible. Another advantage is that the TOR networks can actually protect against certain types of cyber attacks due to the way the connections are established.
Tails Linux distribution is configured not to leave any traces — even if a swap partition is identified it will not write data to it in order to avoid any forensics experts from being able to tell what the distribution was used for. It runs only from the RAM of the computer which is automatically erased as soon as the operating system is stopped.
Parrot Linux — A Distribution with Security in Mind

Parrot Linux is a Debian-based distribution which is designed to be a portable “laboratory” both for security specialists and forensics experts. It is based on the Testing branch of Debian which ensures that up-to-date packages are released at regular intervals bringing all required tools with adequate features and still offering stable operations. The distinct characteristic of the system is that it is sandboxes with two solutions along with a custom security profile. This means that user applications and data is protected even if the system is compromised by hackers.
Penetration testers will also benefit from Parrot Linux as it integrates all commonly used tools which are pre-configured with easy root access and the relevant security configurations so that work can start immediately. There are several distinct features that are found in Parrot Linux:
- Debian Testing Based Releases — This is one of the few specialist distributions that are based on the “Testing” branch of Debian. As described by the project itself this is the ongoing development state of the next stable release. This means that the packages contained in Parrot’s repository will be newer than the the ones found in “stable” and run without any critical bugs.
- Automount Functions Disabled By Default — Advanced forensics tools will not tamper with the hard disk contents in any way which is why automounting partitions or devices is not considered a proper procedure.
- Sandbox Environment — The distribution has implemented two distinct sandbox systems by combining the use of Firejail and AppArmor along with custom security rules.
- Network Services Disabled by Default — This is done to maintain a low memory footprint and avoid unnecessary network exposure in a given network. Services that require opening up a port will need to be manually started.
- Update Reminders — When the distribution is installed on a given system a custom update reminder service will be activated which will prompt the user to check for system and package updates at regular intervals.
We highly recommend Parrot Linux for both amateur and professional users as it provides a stable platform for carrying out all kinds of tasks related to security and privacy. The distribution caters to a wide range of users including the following: security experts, digital forensics experts, engineering and IT students, researchers, journalists, activists, wannabe hackers and police officers.
Related: The 10 Best Methods on How to Improve Linux Security
BlackArch Linux — A Versatile Penetration Testing Option

BlackArch Linux is one of the well-known derivatives of Arch Linux which is designed with penetration testing in mind. It will launch a custom low-resources optimized environment that include more than 2000 tools used by security experts for practically any situation or task. What’s interesting is that it is available as an unofficial user repository. Effectively this means that Arch Linux users can easily transform their existing installations into BlackArch by downloading the requisite packages using the guide available on the distribution’s site.
The BlackArch Linux disk images are 64-bit only allowing the developers to built optimized packages for all modern computers. Conveniently they have also created an image that is compatible with all popular virtual machine hosts. The standard way of deploying the operating system is to download and run the live CD and from there start the setup procedure.
The associated website lists all tools bundled with the current release along with a small description, version number and the category under which it is grouped. This is convenient for users that want to check if their required package is available in the distribution.
BlackArch Linux users have also managed to create a welcoming community spanning across the most widely used platforms: GitHub, Twitter, Youtube, IRC, Discord and the project’s blog.
Whonix Linux — For Anonymous Surfing
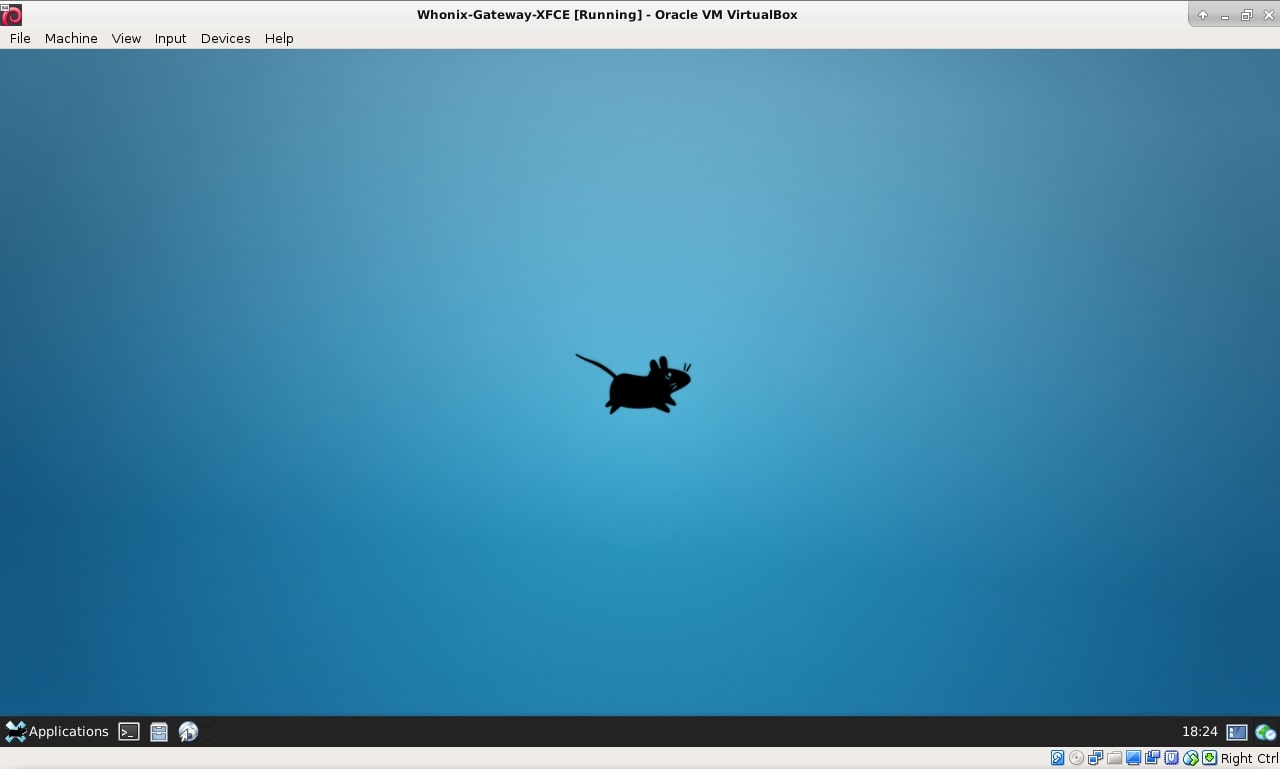
Whonix Linux is a popular alternative to Tails Linux by offering a safe environment allowing the users to surf the Internet using the TOR anonymous network. The secure connection not only guarantees the privacy of the Internet users, but also provides protection from certain types of cyber attacks like man-in-the-middle. The operating system is based on Debian and the desktop environment is run from multiple virtual machines. This ensures that several layers of protection are added to guard the users from malware and IP address leaks. This feature also stops certain ransomware from running — those that include a blacklist for detected virtual machine hosts. These advanced malware threats will automatically stop running when such an engine is detected.
All popular Internet tools will be pre-installed in the live disk image so that the users will not need to install any packages. According to the developers this is the only operating system that is custom-designed to be run inside a VM and paired with the TOR anonymous network client. This practically makes it impossible to cause DNS Leaks and even malware that have infected the system with root (administrative) privileges cannot discover the true IP address.
The virtual machine based engine provides both network and hardware isolation. What’s more important is that a snapshots feature is available, the users can easily revert back to previous saved states. Multi-level security is ensured by allowing the users to use multiple OS clones, disposable virtual machines and etc.
The live disk images can be run in a non-persistent state which means that all memory contents will be erased as soon as the operating system has stopped running. In addition if the OS is powered down all remnants of critical information wil be impossible to retrieve.
CAINE Linux — The Trusted Forensics Solution

The CAINE distribution stands for Computer Aided INvestigative Environment and is one of the most famous digital forensics projects. This is not a standard distribution that has been customized with scripts and a graphical makeover, instead it is made to be a complete forensics environment that integrates all necessary applications and modules used in this line of work. According to the design objectives there are three main goals in which CAINE should aspire to uphold:
- An interoperable environment that supports the digital investigator during the four phases of the digital investigation
- An easy-to-use graphical user interface
- User-friendly Tools
Following the established routine of engagement the distribution will block write permissions to hard disk drives and removable devices. This is done so in order not to damage any files and preserve the environment. To allow write procedures to be run the users will need to unblock the chosen devices using the graphical tools available on the disk.
The distribution includes scripts that can examine file and data structures, as such analysis on key contents including the following:
- Databases
- Internet History and Web Browser Data
- Windows Registry
- Deleted Files
- EXIF Data from Images and Video Files
The environment includes a live preview option which simplifies access to administrative functions and evidence output. A distinct addition to CAINE is the built-in Windows IR/Live forensics tools featuring a complete array of software used to analyze the operating system environment.
Related: The Best Linux Server Distributions in 2017
Conclusion
Whatever Linux distribution is chosen from this list, it will serve the users well as these are the top picks used by both amateurs and professionals. They are made by teams of committed developers and the simple fact that they have established communities of users shows that these projects will continue to play an important role in security and privacy protection.
Depending on the needs of the individual users this guide will give a good foundation for building any kind of tool and service. The advantage of using one of these ready-made distributions is that they are tailor-made for the specific use cases. Guides, courses and tutorials will usually focus on one single distribution when performing penetration testing versus the commonly used distributions.
We continue into 2019 with an even more alarming sense of security weaknesses and constant privacy leaks generating an ever-increasing interest in these types of Linux distributions. Its important to note that simply running them will not guarantee that the users will be protected from danger — they will need to uphold the best security practices as advised by security staff and guidelines.