 CVE-2019-14287 is a new vulnerability discovered in Sudo.
CVE-2019-14287 is a new vulnerability discovered in Sudo.
Sudo is considered one of the most important and widely used programs for Unix- and Linux-based operating systems that allows a permitted user to execute a command as the superuser or another user, according to the security policy. The program is “shipped” as a core command on nearly all Linux systems.
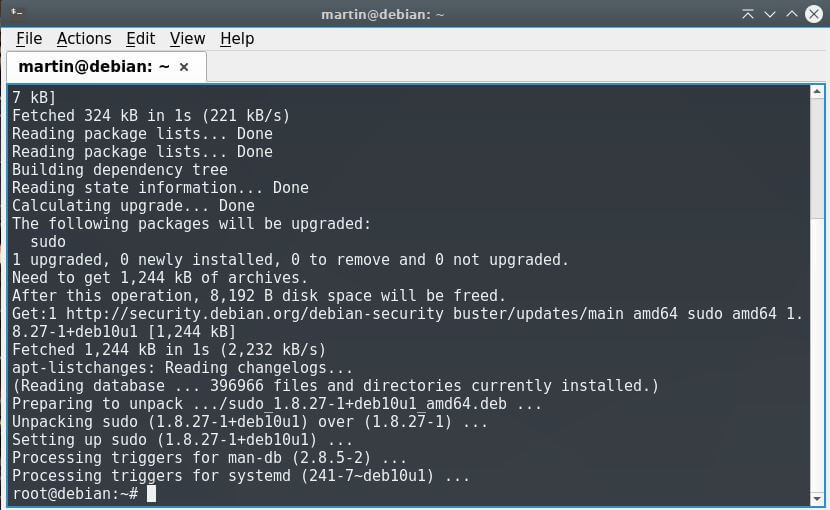
Note: Screenshot by my colleague Martin who already updated his distro. You should do the same.
CVE-2019-14287
The CVE-2019-14287 vulnerability involves the way Sudo implements running commands with arbitrary user ID. Sudo versions prior to version 1.8.28 are all affected. According to the official RedHat advisory, if a sudoers entry is written to allow the attacker to run a command as any user except root, this flaw can be used by the attacker to bypass that restriction.
It should be specified that exploiting the bug successfully requires the user to have Sudo privileges that allow them to run commands with an arbitrary user ID. Usually, this means that the user’s sudoers entry has the special value ALL in the Runas specifier. If a sudoers entry is written in a way to allow the user to run a command as any user except root, the vulnerability can be used to avoid this restriction.
What does this mean?
On nearly all Linux distributions, the ALL value in RunAs specification in the /etc/sudoers file enables users in the admin or Sudo groups to run commands as any valid user. Because privilege separation is a rudimentary security principle in Linux, admins can configure a sudoers file to determine the type of commands specified users can run. Even in cases when a user has been restricted to run commands as root, the flaw could enable the user to circumvent the security polity to hijack the control of the system.
As explained by the developers of Sudo, “this can be used by a user with sufficient Sudo privileges to run commands as root even if the Runas specification explicitly disallows root access as long as the ALL keyword is listed first in the Runas specification.”
The good news is that the bug is fixed in sudo 1.8.28.
Did you know?
Another serious vulnerability was unearthed in Sudo in 2017. CVE-2017-1000367 was a severe root Linux bug discovered by Qualys Security researchers. The flaw resided in Sudo’s “get_process_ttyname()” function for Linux and could allow a user with Sudo privileges to run commands as root or elevate privileges to root.




Hi guys,
The tool github.com/TH3xACE/SUDO_KILLER allow you to detect the CVE-2019-14287 and also propose how to exploit it. There is also a docker with different sudo exploitation scenarios including the CVE-2019-14287. Just run the following command for the docker :
service docker start
docker pull th3xace/sudo_killer_demo
docker run –rm -it th3xace/sudo_killer_demo
cd SUDO_KILLER
./SUDO_KILLERv1.3.7.sh
Just scroll down and look for CVE-2019-14287, it will tell you how to exploit CVE-2019-14287.
If you want to check for other CVEs, just run with -c argument.
A +1 star please if you like the project.