A new lucrative method for generating profits in digital currencies has been created and used for a while now. It is known as Digital Currency Mining, and everyone can participate in it. However, this type of profit generating via using the resources of your PC can hide some risks. In this review of Digital Currency Mining, we have decided to explain what it is and why is it so lucrative to cyber-individuals who do not obey the rules.
What is Digital Currency Mining
The usage of digital currencies has arisen a lot the past couple of years. Since the financial crisis, the most widely used digital currency has fallen and sharply risen going from 5 USD to around 400 USD per 1 BTC. The strength in digital currency is that it is encrypted and safe regarding that it does not exist in physical form, like cash. The seriousness of Digital Currency has pushed a lot of organizations to create other Digital Currencies(https://www.cryptocoinsnews.com/most-popular-digital-currencies/) that also became popular and used.
Here comes the term Digital Currency Mining. To best explain it, we will look into the process of how Digital Currency is traded online. This is done by forming a chain of data blocks that travel from the source to the destination, similar to the figure below:
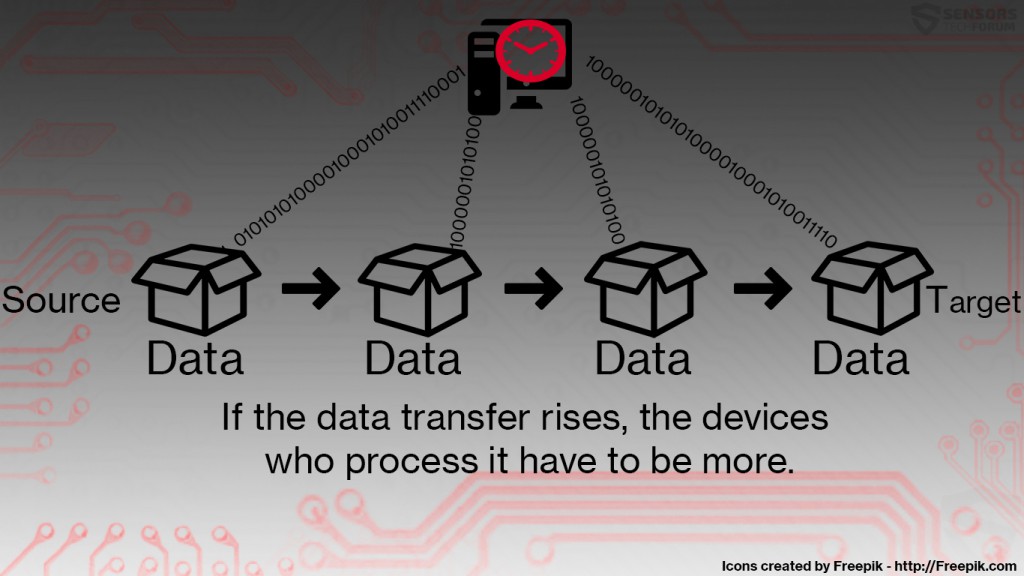
However, these data blocks have to be processed by computers, and since digital currencies have become massively used. And this means that more powerful devices are required to analyze that data. This is where most cryptocurrency companies have shortage of resources because it takes significantly more time for one device to process the data, especially in its peaks:
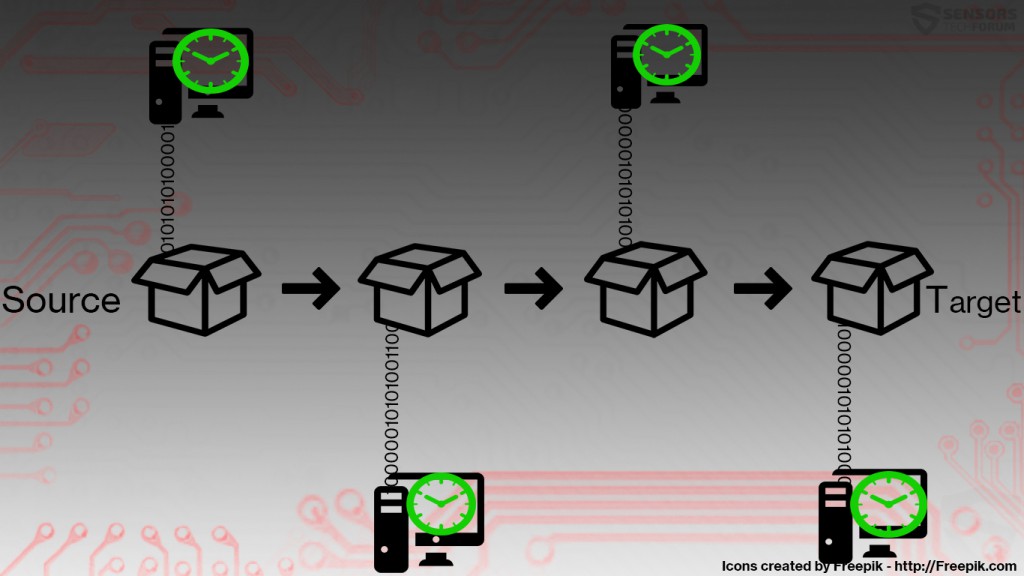
To counter this, external devices are being used in return for a fee or financial reimbursement. These computers are known as miners, and when they process the same data in a decentralized manner, they cope with the situation:
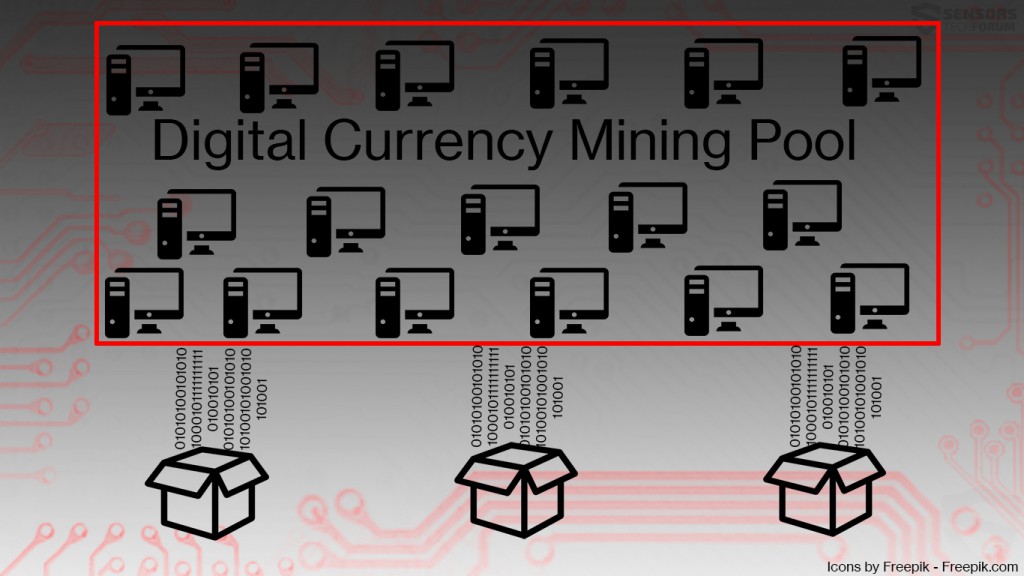
Since some crypto-currencies, such as BitCoin use SHA256, which is practically impossible to be processed by few computers, some companies have figured out a method to boost Digital Currency analyzing speeds. They have formed pools of many computers, home or office to analyze more data for shorter time spans:
Everyone can become a data miner, and the cost for that is taking up of the computer’s resources for conduction calculations. This results in way higher CPU (Processor) and GPU (Video Card) usage. The good side about it is that users are rewarded with digital money for providing digital currency mining services.
What Are the Risks of Digital Currency Mining
The Risks for the user are not many and not often occurring. The worst case for the user is that if his computer works for extended periods of time to mine Digital Currencies, its hardware components may break. Not only this but the life of the component is being reduced as the usage time increases.
But there are some organizations that create Data Currency pools by installing bundled programs to unsuspecting user PCs. These programs start analyzing digital currencies without the user’s consent. A perfect example of such programs is “Vnlgp Miner”. It generates income to a website which is a Currency Mining Pool. The user does not even know that the software is essentially stealing the resources of its victim’s computers. And this is the main risk associated with Digital Currency Mining. And what is worse is that organizations do not mind to use such services as long as they get the job done, and the software itself is not really malware, because it does not infect the computer, only uses its resources to calculate data blocks.
Conclusion
Digital Currency Mining is surely a method of generating income, especially if you have a lot of computers at your disposal. However, there are some cyber-crooks that steal the resources of other computers and unsuspecting users, and this is where digital currency organizations are powerless. The only viable solution for the average user to protect himself from such programs is by installing an advanced anti-malware protection which will assist with blocking such type of low-risk Digital Currency Mining programs.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter