 A vulnerability used by the trojan horse Dridex to infect computers has been detected and reported to take advantage of Microsoft Word files.
A vulnerability used by the trojan horse Dridex to infect computers has been detected and reported to take advantage of Microsoft Word files.
A large e-mail campaign spreading the Dridex trojan horse using a new Microsoft Word exploit has been detected. The threat takes advantage of a bug in Microsoft Word which enables attackers to hack a computer via an RTF type of file. These type of attacks include the concealing of malicious code. When this code is activated the virus connects to server of the cyber-criminals and then downloads the malicious files on the infected computer.
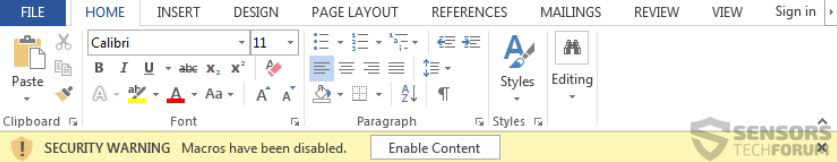
The Dridex trojan itself is actually an evolved version of another Trojan horse also known as the Cridex Trojan. This particular type of malware was mainly created to target bank account information on infected computers and extract it to remote servers. The reason why this trojan became so widespread was that it became concealed within macros of important documents such as Invoices, Confirmation Letters and others. More: Dridex: New Form of Cridex Trojan Rises Again
In addition to this, researchers at the company Proofpoint claim that the bug includes multiple different spam e-mails massively sent all over the world, despite the fact that the virus infected users form the southern hemisphere more.
Proofpoint have also reported that Dridex spammers previously had relied on macros and hidden documents in macros which convince victims that they need to open the attachment and look up what is In it. And the vulnerability is oriented exactly towards this type of attack, however relying on a new zero-day exploit to conduct it.
A patch has been created to fix this vulnerability, Microsoft researchers report. The patch is included in the latest Microsoft Office update and users are strongly advised to update swiftly. But since we live in a dynamic world, it is not known what types of other vulnerabilities exist out there and are yet to be discovered, so we strongly suggest all users to safely store their data in multiple copies and be extremely cautions what information they share online.