 During the last week, Palo Alto Networks security researchers have noticed that Dridex, the latest version of the Cridex Trojan, a data stealer also known as Feodo, Bugat and Geodo has been activated to attack bank security information through embedding automated scripts with repeating tasks into the macros of the Microsoft Office Package.
During the last week, Palo Alto Networks security researchers have noticed that Dridex, the latest version of the Cridex Trojan, a data stealer also known as Feodo, Bugat and Geodo has been activated to attack bank security information through embedding automated scripts with repeating tasks into the macros of the Microsoft Office Package.
According to the researchers the Dridex campaign has started on 21st October, 2014 beginning to send out messages claiming to contain electronic financial documents (e-invoices, etc.) from different merchants, including Humber Merchant’s Group – a company dealing in the construction field.
The Didex malware is the latest version of the Feodo / Bugat / Cridex Trojan horse, developed in Geodo. It keeps its previous versions abilities for stealing information but these are changed to users receiving attachment files containing macros on their e-mail accounts. One of the changes in the Dridex virus, noticed last week, is sending out Microsoft Word documents with macros forcing users to download malicious software on their machines.
After users receive and open the infected Word document, the macros behind start executing the tasks embedded in their scripts, having one and the same aim – stealing online bank certificates and security information, so hackers can access and empty users’ bank accounts.
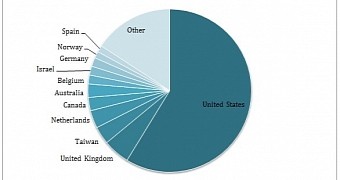
It seems that the main aim of the attack are users in the United States, as almost half of the e-mails in the researcher’s extract are based there. There were e-mail accounts registered in other countries as well though – Australia, Canada, United Kingdom, The Netherlands, Belgium, Germany, Norway, Spain., Israel and Taiwan.
Although there was no official statement on the Dridex malware from Microsoft by the time the article was written, they have taken precautions to limit the issue by turning off macros from their Office Package components. They can be activated by users any time though, so basically a good protection against the malware is to turn off macros from your Microsoft Word or any other office documents you might have such running on.
The Feodo tracker, a service offered by the abuse.ch web-site for keeping an eye on the malware command and control servers shows that there are 93 servers for Dridex communication, 12 of which currently online. Four of them are known to be located in Russia.



Very useful article, do you have any information about which AV can detect this new strain?
I tried googling for the information but nothing seems to come up..