It’s a secret to no one (in the infosec world) that the exploit kit market has been rearranged to meet the current needs of malware distributors.
Just several weeks ago, there was a notable malvertising incident on the popular website answers.com which has about 2 million visits daily. The scenario was very similar to both Angler and Neutrino but it was in fact RIG doing the work. It used the domain shadowing technique and the HTTPS open redirector from Rocket Fuel.
The researcher behind Malware Don’t Need Coffee (MDNC) observed a mid-August transition of many malicious operations towards the RIG exploit kit. The campaigns were distributing more geo-focused banking Trojans and less CryptXXX ransomware. During his investigations, MDNC also came across a (possibly) new exploit kit.
MDNC was “trying to understand that move”, all along suspecting the presence of an internal TDS (Traffic Distribution System) inside RIG Exploit Kit, a suspicion which was later confirmed.
This specific feature is believed to have appeared initially in the EK market with Blackhole, and it disappeared with Nuclear and Angler.
What is the TDS feature all about?
The TDS feature allows the exploit kit operator to attach multiple payloads to a unique thread. It is indeed a key feature to a payload seller. Furthermore, the payload is adapted to the GEO and OS settings of the target. However, there is the condition that “you have to create one Exploit Kit thread per payload, use an external TDS (like Keitaro/Sutra/BlackHat TDS/SimpleTDS/BossTDS, etc…) and from that TDS, point the traffic to the correct Exploit Kit thread (or, if you buy traffic, tell your traffic provider where to send traffic for each targeted country)”.
Eventually, many malware-dropping operations switched to RIG. Towards the end of September, 2016, the Neutrino advertisements and banners disappeared from underground forums.
Is there a new exploit kit being shaped at this very moment?
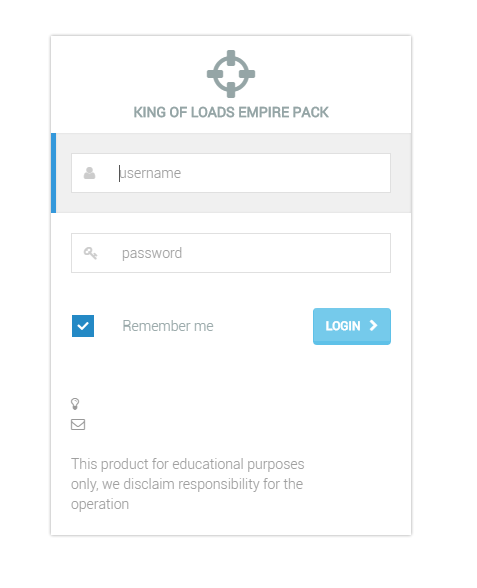
Having in mind all the changes in the EK market, perhaps it is not a coincidence that a new exploit kit is currently discussed in the underground forums – Empire Pack. These discussions are held privately and the EK is not public (yet?).
The interface, as noted by MDNC, is very familiar and hints at RIG. The researcher speculates that the Empire Pack launch could be related to the first wave of RIG-powered attacks. Perhaps the Empire Pack is a RIG instance managed by a reseller/payload seller?
For full technical disclosure, jump to the original research.