A new version of the dangeorus RIG exploit kit used to conduct successful infections via taking advantage of exploits in Windows has been detected out into the wild. The exploit kit has been reported to contain new script files and features to conduct a successful infection. The creators of the kit have made several Action scripts and in addition to this have changed several changes that are displayed in it’s flash file.
A new version of the dangeorus RIG exploit kit used to conduct successful infections via taking advantage of exploits in Windows has been detected out into the wild. The exploit kit has been reported to contain new script files and features to conduct a successful infection. The creators of the kit have made several Action scripts and in addition to this have changed several changes that are displayed in it’s flash file.
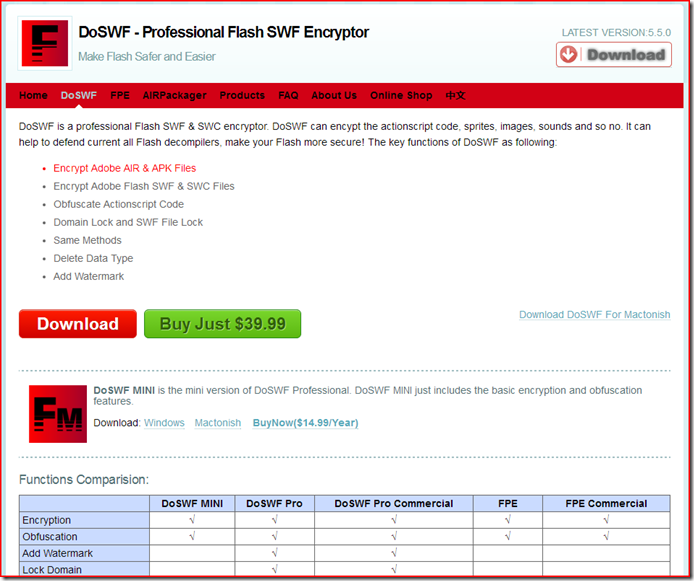
When malware researchers at PC Xcetra Support have investigated deeper into the flash file’s source code they have discovered that a tool called DoSWF tool has been used to obfuscate this exploit kit. The tool is currently believed to be in version 5.5.0, and the researchers have even managed to discover that the tool is publicly available for sale via it’s website:
Rig EK was the kit that replaced the Angler EK, and it is using exploits In Adobe’s Flash Player to conduct a successful infection. But on the 20th and 21st of August malware, researchers have detected the new version that had other features and exploits that can be used as well.
This very new version was reported to cause infections via taking advantage of Microsoft software. One of those exploits was reported by Eduard Kovacs at Secrutiyweek.com to be the CVE-2016-0189. This type of vulnerability allowed for a remote execution type of attack which took advantage by executing JavaScripts as well as VBScripts.
Microsoft was able to patch the flow, but it is not known for certainty whether the similar attack can be conducted via Internet Explorer instead.
News also broke out that the ones behind the RIG exploit kit may also be working on new updates to the exploit kits and they might also be conducting tests that can ensure the successful operation of malware which is joined with this kit.
Not only this but malware researchers have also discovered some elements related to the usage of a Silverlight exploit which is a Microsoft software exploit. Researchers at Cyphort also report this exploit to be used for the first time by RIG.
Not only does the RIG exploit kit have new exploits to use for a successful infection, but it has also been reported that it changed it’s communication with servers as well. Unlike the previous communication methods that were easier to track down and foreseen, malware researchers have detected that the devs of RIG have been conducting tests on new and safer methods for communication.

Rig EK Summary
This tendency of developing exploit kits is not only limited to the Rig. Many malware coders are also attempting to discover new vulnerabilities and bundle them in their kits. The truth is that exploits have become a lucrative business, and their discovery has become crucial regarding security for black hat hackers and IT companies that want to patch vulnerabilities in their software.