Sundown exploit kit was detected in active malvertising campaigns last September. Back then, the exploit kit was delivering the CryLocker ransomware, together with the RIG EK. Unfortunately, security researchers at TrendMicro have discovered that Sundown has been recently updated meaning that an uptick in ransomware and malware attacks should be expected. Considering the nature of the hack tool, it may continue to be deployed in the distribution of both ransomware and malware. In the latest campaign, researchers detected Chthonic banking Trojan being the payload of the operation.
Related: Locky Ransomware Befriends the Bizarro Sundown Exploit Kit
Sundown exploit kit latest activity was detected on December 27, 2016, where attackers used PNG images to store the harvested information and the exploit code. In September’s attacks with the payload being the CryLocker ransomware, PNG files were also used to pack harvested user information. The images were then uploaded to an Imgur album so that cybercriminals could avoid detection.
Sundown Exploit Kit Steganography Capabilities
TrendMicro researchers have reported that the exploit kit was recently updated with steganography techniques. As a result, the PNG files are now used not only to store harvested information but also designed to hide the exploit code:
On December 27, 2016, we noticed that Sundown was updated to use similar techniques. The PNG files weren’t just used to store harvested information; the malware designers now used steganography to hide their exploit code.
What is steganography? It is an advanced technique deployed to hide malicious code into an image to bypass signature based detection. It’s a popular technique seen in malvertising attacks based on exploit kits. The GooNky malvertising campaign is a good example as it used multiple tactics to conceal the traffic, such as moving part of the malicious code into images to escape detection.
In this new Sundown exploit kit instance the attackers didn’t really conceal the data in the picture itself – they appended the malicious code at the end of the file, researchers explain.
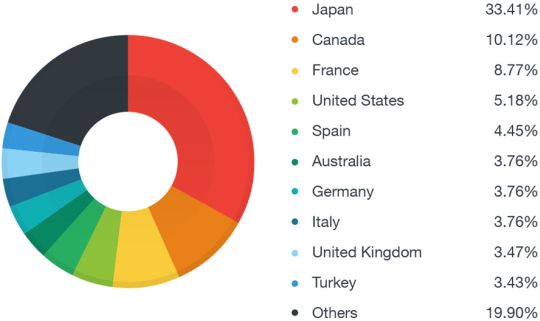
The updated EK was seen in malvertising campaigns distributing malware in Japan, Canada, and France, with Japanese users accounting for more than 30 percent of all the targets. See image below (by TrendMicro):
In this updated version, the exploit kit’s malvertisement creates a hidden iframe that automatically connects to the Sundown landing page. The page will retrieve and download a white PNG image.
CVE-2015-2419 Leveraged in Latest Sundown Exploit Kit Attacks
Researchers also uncovered that the exploit code within the PNG image also included an exploit code targeting the CVE-2015-2419 vulnerability.
CVE-2015-2419 Description
JScript 9 in Microsoft Internet Explorer 10 and 11 allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption) via a crafted web site, aka “JScript9 Memory Corruption Vulnerability.”
In addition, a Flash exploit for CVE-2016-4117 was also retrieved by the exploit code. The landing page itself includes an exploit targeting another Internet Explorer (IE) vulnerability, CVE-2016-0189, researchers note.
Interestingly, all of the above mentioned exploits have been patched and have been used by other exploit kits throughout 2016.
Related: Top 3 Vulnerabilities Used in 2016 Exploit Kit Attacks
Protection against Sundown Exploit Kit and Other EKs
Exploit kits have been used on an industrial scale. They are automated toolkits that scan a user’s web browser, and analyze it for flaws to leverage before delivering the malicious payload. This means your browser should always be fully patched – never estimate the importance of security updates. Users should immediately install security fixes for all their software – as soon as patches are released.
In case a patch is not yet released, an attack relying on this vulnerability can still be deflected by up-to-date anti-malware software. Most such programs will detect and intercept the exploits attempting to take advantage of a flaw.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter