 The creators of GandCrab ransomware do not sleep as the virus has been detected to infect users via what appears to be game and other software cracks, according to recent reports.
The creators of GandCrab ransomware do not sleep as the virus has been detected to infect users via what appears to be game and other software cracks, according to recent reports.
The GandCrab ransowmare has been steadily updated with more and more improvements to it’s methods of infection and to the malware itself. The virus has passed several internal version and is now officially in its 4.4 version as researchers have recently detected. And the virus has had several features removed while others have been added to it, but most of them have remained the same, aside from the fact that the GandCrab 4 malware now uses the .exe files of cracks for games or licensed software to infect victims.

GandCrab 4 Targets Users from Low-Rep Sites, Offering Cracks
During the course of their investigations, researchers have detected the virus to use WordPress sites which are often used by malware authors. This is due to the fact that they are easy to set up and easy to exploit. On one of the websites, the researchers found web pages, containing the download web links of the GandCrab 4’s executable file, masked as cracks for the following programs:
- Merging Image to PDF 2.8.0.4
- Securitask 2005 1.40H
- SysTools PST Merge 3.3
Researchers at Fortinet have even detected the pages to be well-written and well-structured with a detailed description of the program the user is looking a crack for with the main idea behind it being the fact that the user should trust the site In order to download and run the crack.
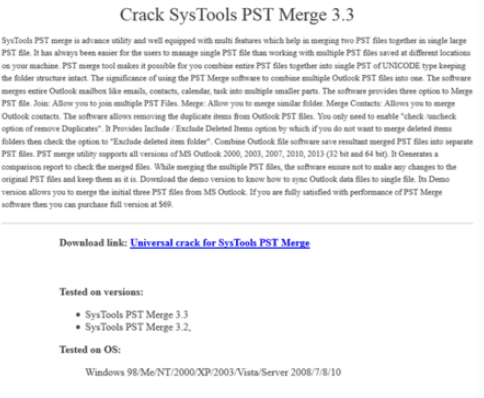 Image Source: Fortinet
Image Source: Fortinet
Significant Change in GandCrab 4’s Encryption
The virus has undergone several changes here and there, like the wallpaper no longer being used and several of it’s features removed. The biggest change however was the way GandCrab encrypts the files on the compromised computers.
Related: GandCrab Ransomware Updated – Targets Windows XP and Older Servers
The ransomware has chosen to use the Salsa20 encryption instead of the one it used so far, called RSA-2048. Unlike Salsa20, the RSA cipher has become mainstream for ransomware viruses and researchers believe that the main reason for switching to Salsa20 is that the encryption time is much faster than it would gradually be with RSA-2048, used with it’s previous versions. The Salsa20 encryption algorithm is also known In the cyber-security world as it was used in a virus that caused a major outbreak during 2017 – Petya Ransomware.
The new version also uses a more advanced obfuscation as well, able to evade most traditional antivirus programs. The hackers are also very fast in managing their download URLs on the compromised WordPress sites as well, changing URLs often in order to continue the spreading of GandCrab 4.
GandCrab 4 ransomware has been infecting users since late 2017 and the virus was one of the first htat demanded victims to pay hundreds of dollads in DASH cryptocurrency tokens. The malware is likely ran by a big hacking entity as it is not an easy virus to stop, since crooks often find different methods to bypass traditional security software, making GandCrab what appears to be the most impactful ransomware of 2018 so far.


