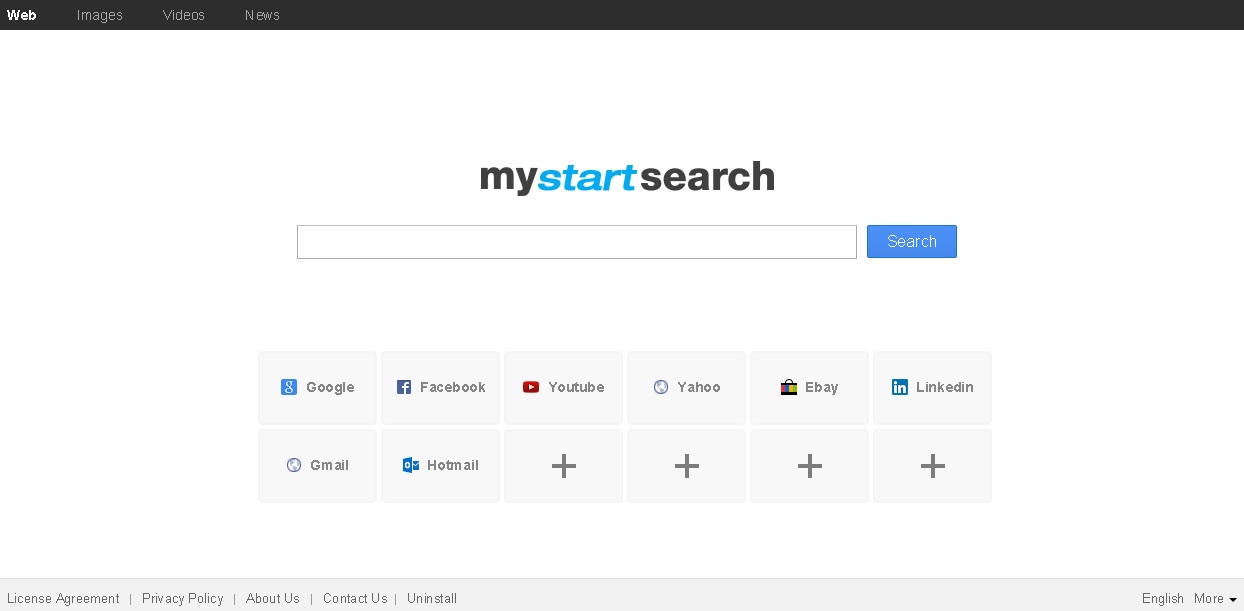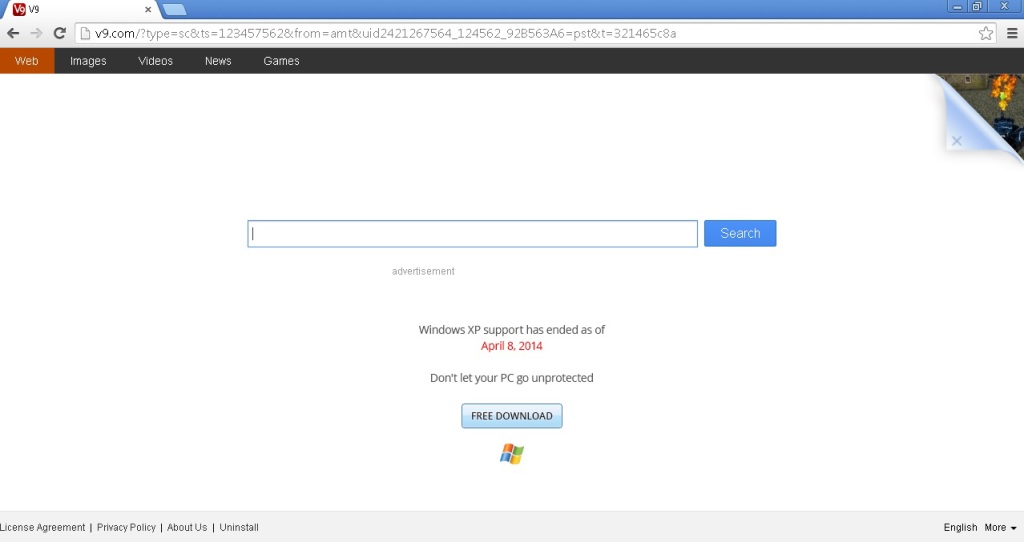
Remove Webpage.V9.com from Mozilla, IE, Chrome or Safari
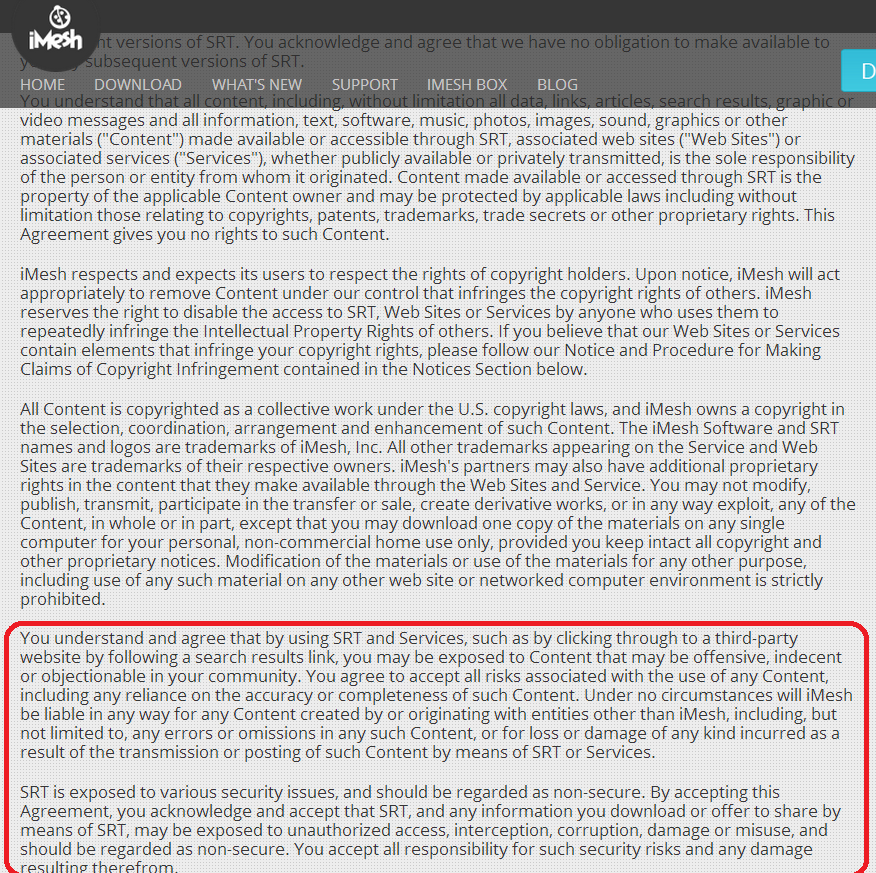
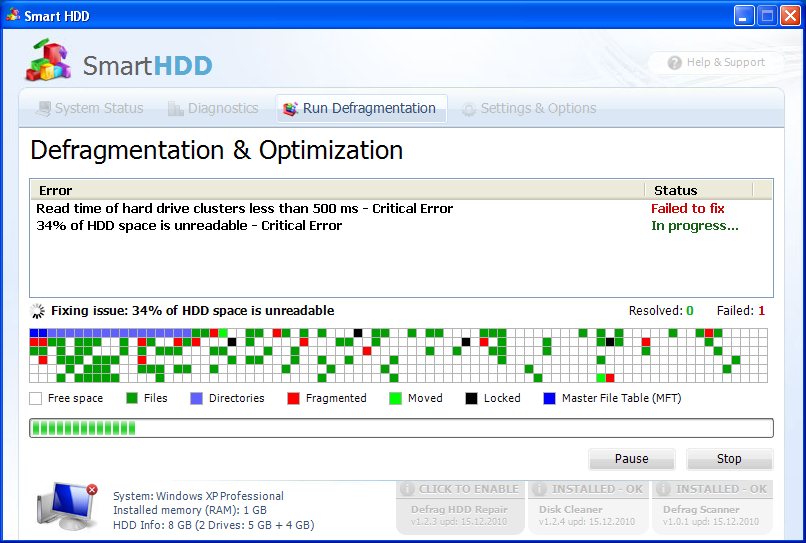
V9 Redirect Virus is a browser hijacker redirecting you to the search engine website V9.com in order to gain traffic. Malware experts recommend its removal as it may expose your system to more serious threats from the Web. How Does…