Have you ever received a frightening email claiming someone has compromising information about you? One such recent example is the “Security status not satisfied” scam.
Sextortion email scams, a growing concern in the digital world, involve criminals who threaten to reveal private data unless they receive payment. Often, these threats are baseless but can nevertheless lead to significant distress. This article delves into understanding sextortion email fraud, recognizing its signs, and taking proactive steps to protect yourself.
“Security status not satisfied” Threat Summary
| Name | "Security status not satisfied" |
| Type | Sextortion Scam / Phishing Email / Malware |
| Short Description | An extortion email threatening to release compromising videos unless a payment in Bitcoin is transferred. |
| Removal Time | Approximately 15 minutes to scan the whole system and remove any discovered threats |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
Understanding the Basics of the Sextortion Email “Security status not satisfied”
Sextortion email fraud involves criminals threatening to release private and sensitive information unless the victim pays a ransom. Typically, the scammers claim to have compromising photos or videos of the individual and demand payment to keep this information private. Understanding the basic operations of these scams is crucial for protecting yourself and your loved ones from becoming victims.
What Constitutes Sextortion Email Fraud?
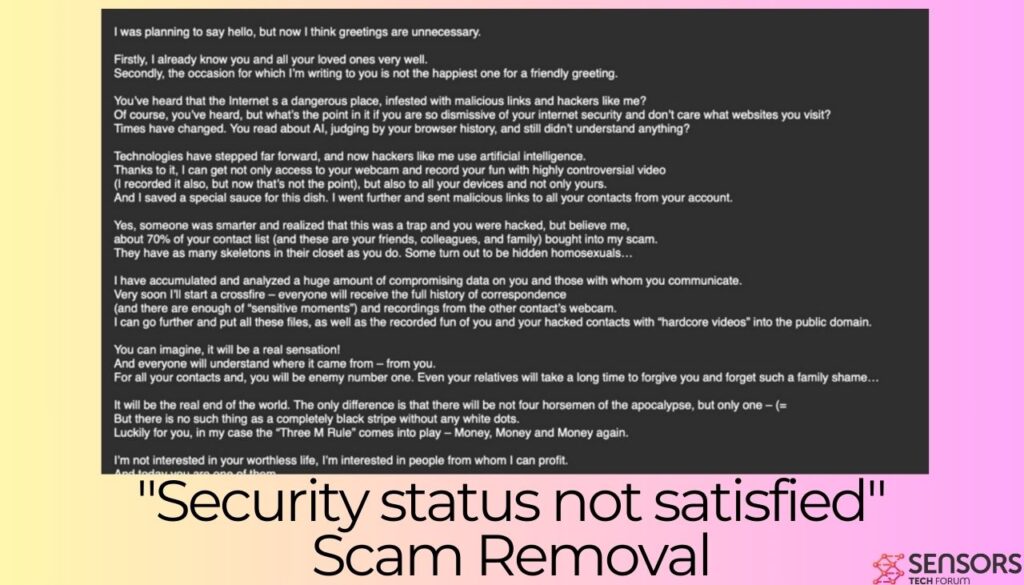
As you can see in the example that follows, sextortion email fraud takes shape through deceptive and threatening emails. The scammers intimidate victims by claiming they have obtained sensitive content that could embarrass or harm the victims’ reputations if made public. The sinister nature of these scams lies not just in the threat itself but in the fabrication. Often, these criminals do not possess such material – instead, they rely on fear and manipulation to coerce payment.
Real-Life Instances: How These Scams Have Impacted Victims
Real-life instances of sextortion email fraud reveal the devastating impacts these scams can have on individuals. Victims have reported severe emotional distress, financial loss, and in extreme cases, self-harm. The embarrassment and fear of exposure lead some to pay the ransom without realizing that doing so only emboldens the scammers. These traumatic experiences highlight the importance of addressing sextortion threats appropriately and safeguarding personal data online.
In the case of “Security status not satisfied,” the email extortionist claims to have recorded a video of the recipient while watching adult content, threatening to release it unless a payment in Bitcoin is made. Here’s the entire text of the email scam:
Security status not satisfied.
I was planning to say hello, but now I think greetings are unnecessary.
Firstly, I already know you and all your loved ones very well.
Secondly, the occasion for which I’m writing to you is not the happiest one for a friendly greeting.You’ve heard that the Internet is a dangerous place, infested with malicious links and hackers like me?
Of course, you’ve heard, but what’s the point in it if you are so dismissive of your internet security and don’t care what websites you visit?
Times have changed. You read about AI, judging by your browser history, and still didn’t understand anything?Technologies have stepped far forward, and now hackers like me use artificial intelligence.
Thanks to it, I can get not only access to your webcam and record your fun with highly controversial video
(I recorded it also, but now that’s not the point), but also to all your devices and not only yours.
And I saved a special sauce for this dish. I went further and sent malicious links to all your contacts from your account.Yes, someone was smarter and realized that this was a trap and you were hacked, but believe me,
about 70% of your contact list (and these are your friends, colleagues, and family) bought into my scam.
They have as many skeletons in their closet as you do. Some turn out to be hidden homosexuals…I have accumulated and analyzed a huge amount of compromising data on you and those with whom you communicate.
Very soon I’ll start a crossfire – everyone will receive the full history of correspondence
(and there are enough of “sensitive moments”) and recordings from the other contact’s webcam.
I can go further and put all these files, as well as the recorded fun of you and your hacked contacts with “hardcore videos” into the public domain.You can imagine, it will be a real sensation!
And everyone will understand where it came from – from you.
For all your contacts and, you will be enemy number one. Even your relatives will take a long time to forgive you and forget such a family shame…It will be the real end of the world. The only difference is that there will be not four horsemen of the apocalypse, but only one – (=
But there is no such thing as a completely black stripe without any white dots.
Luckily for you, in my case the “Three M Rule” comes into play – Money, Money and Money again.I’m not interested in your worthless life, I’m interested in people from whom I can profit.
And today you are one of them.That’s why: Transfer $1390 in Bitcoin to: 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK …within 48 hours!
You don’t know how to use cryptocurrencies? Use Google, everything is simple.
Once payment is received, I will delete all information associated with you and you will never hear from me again.
Remember one thing: my crypto address is anonymous, and I generated this letter in your mailbox and sent it to you.
You can call the cops, do whatever you want – they won’t find me, my demands won’t change, but you’ll just waste precious time.The clock is ticking. Tick tock, a minute out of 48 hours has passed right now. An hour will soon pass, and in two days your old life will pass forever.
Either goodbye forever (if I get my payment), or hello to a brave new world in which there will be no place for you.Hasta La Vista, Baby!
P.S. Almost forgot. Finally learn what incognito tabs, two-factor authentication, and the TOR browser are, for God’s sake!
The Psychological Tactics Behind Sextortion Emails Such As “Security status not satisfied”
The effectiveness of sextortion emails lies in the psychological tactics employed by scammers. These tactics include invoking fear, shame, and urgency to compel the victim to act hastily. Scammers craft emails that appear highly personal and convincing, creating an illusion of having access to one’s private life. Understanding these manipulative strategies is the first step in building resilience against them. Recognizing the signs of sextortion and knowing that these threats are often baseless can empower individuals to respond appropriately: by not engaging with the scammer, securing their accounts, and reporting the incident to authorities.
Recognizing the Signs of Sextortion Email Fraud
Sextortion email fraud can often be identified by certain red flags that are commonly found within these threatening messages. Key indicators include unsolicited emails claiming to have sensitive or compromising information about you. Authors of these emails typically demand payment, often in cryptocurrency, to prevent the release of the information. In the case of the “Security Status Not Satisfied” scam, $1390 in Bitcoin are demanded to be transferred to a particular wallet. Recognizing these signs early can help you respond appropriately without succumbing to the pressure of the extortion attempt.
Common Phrases and Threats Used in Sextortion Emails
Sextortion emails have a recognizable pattern in their language and threats. They might start with a statement that they have hacked your computer or obtained videos of you. Phrases such as “I know what you’ve been doing online,” “I’ve recorded you,” or “pay me now to prevent me from sending this to all your contacts” are common. These phrases are designed to instill fear and prompt a quick payment without questioning the legitimacy of the claim. It’s important to approach such claims with skepticism and verify any alleged breaches of your privacy before taking any further action.
Identifying Red Flags: When to Be Suspicious
Several red flags can help you identify sextortion email fraud. Be suspicious if the email:
- Comes from an unknown or suspicious email address.
- Contains numerous spelling and grammar mistakes.
- Asks for payment in Bitcoin or another cryptocurrency.
- Makes broad threats without providing specific evidence of the claimed material.
- Pressures you to act quickly, often giving very short deadlines.
These characteristics are often indicators that the email is part of a scam designed to exploit fear and embarrassment for financial gain.
Why Sextortion Emails Often Mention Compromised Security
Sextortion emails frequently mention compromised security to exploit the fear of having one’s personal information or activities exposed. The scammers claim to have obtained this information through malware or by hacking, which makes the threat seem more legitimate and frightening. This tactic aims to create a sense of vulnerability and urgency, pushing the recipient to pay the ransom without seeking verification. Just remember that these claims are, most likely, entirely baseless. Conducting a thorough scan of your computer with reputable security software, like SpyHunter, can provide peace of mind and ensure your digital safety.
Immediate Steps to Take if You Receive a Sextortion Email such as “Security status not satisfied”
Receiving a sextortion email can be both alarming and stressful. However, how you respond to this unwanted situation can significantly affect its outcome. Here are some immediate actions you should take to safeguard your privacy and reduce the situation’s impact.
Do Not Respond or Engage With the Sender
The first and most important step is to avoid any communication with the scammer. Responding or engaging in any form, even to express disapproval or threaten them, can escalate the situation. Scammers often interpret a response — any response — as a sign that your email address is active, which can lead to more aggressive attempts or variations of the scam. The safest course of action is to completely ignore the communication, but make sure to keep it for evidence purposes.
Preserving Evidence: How and What to Save
In the event of a sextortion scam, preserving evidence is crucial for a couple of reasons: it helps in reporting the incident to law enforcement, and it can aid in any legal actions that may follow. Start by taking screenshots of:
- The initial sextortion email you received (“Security status not satisfied”,
- All subsequent communications,
- The sender’s email address or online profile,
- Any URLs or links shared with you.
Document every piece of communication, including dates and times, to create a comprehensive timeline of events. This detailed evidence can be instrumental in stopping the scammer and preventing them from targeting others.
Changing Your Passwords: A Crucial First Step
After identifying a sextortion attempt, one of your first steps should be to change your passwords, especially those of your email and social media accounts. Creating strong, unique passwords for each account adds a layer of security that could prevent scammers from gaining further access to your information. Implementing two-factor authentication provides an extra layer of security, making it significantly more difficult for intruders to breach your accounts, even if they have your passwords. Doing so not only helps protect your current accounts from malicious access but also plays a crucial role in safeguarding your digital identity from future threats.
While the immediate reaction might be fear or panic, following these practical steps can help you regain control of the situation and protect yourself from further harm. Remember, tools and resources are at your disposal, and taking decisive action can make all the difference.
Protecting Your Online Presence Against Sextortion
In today’s interconnected world, protecting your online presence can safeguard you from sextortion, a serious and invasive form of blackmail. By reinforcing your digital privacy and security, you create a robust barrier against potential attackers looking to exploit personal information for nefarious purposes. This section delves into actionable strategies for enhancing your digital defense against sextortion.
Enhancing Social Media Privacy to Avoid Vulnerabilities
Social media platforms are a common battleground for sextortionists. Strengthening your privacy settings on these platforms substantially reduces your risk of becoming a victim. Here’s how you can fortify your social media presence:
- Review and Adjust Privacy Settings: Regularly examine your privacy settings on all social media accounts to control who can see your posts, photos, and personal information. Opt for the highest level of privacy whenever possible.
- Be Selective with Friend Requests: Accept friend requests only from people you know personally to prevent scammers from accessing your personal information.
- Limit Sharing Personal Information: Avoid posting sensitive information that could be used against you, such as your address, phone number, or workplace details.
These simple steps can greatly diminish the chances of your information falling into the wrong hands.
Secure Your Email: Strong Passwords and Two-Factor Authentication
Email accounts are often the gateway to your digital persona. Securing your email is paramount in preventing unauthorized access to your online accounts. Here’s how to enhance your email security:
- Use Strong, Unique Passwords: Create complex passwords that are difficult to guess. Utilize a mix of letters, numbers, and symbols, and avoid using the same password across multiple sites.
- Enable Two-Factor Authentication (2FA): 2FA adds an extra layer of security by requiring a second form of verification to access your account, such as a code sent to your phone.
- Consider a Password Manager: Tools like Dashlane or LastPass can generate and store complex passwords for you, ensuring that each of your accounts has a strong, unique password.
By prioritizing email security, you significantly reduce the risk of sextortion and other forms of online exploitation.
Avoiding Risky Online Behaviors: Best Practices
Engaging in safe online behaviors is crucial for digital security. Here are some best practices to keep in mind:
- Think Before You Share: Refrain from sending or posting sensitive images or information online. Once shared, control over this content is difficult, if not impossible, to regain.
- Verify Identities: Be wary of new or unknown contacts. Sextortionists often create fake profiles to lure individuals into sharing compromising information.
- Stay Informed: Keep up-to-date with the latest online scams and threats. Being informed helps you recognize and avoid potential dangers.
Adopting these practices will help protect your privacy and reduce the likelihood of falling victim to sextortion. Remember, the best defense against sextortion is a combination of strong online security measures and cautious personal behavior.
When to Involve Authorities and Seek Professional Help
Realizing you’re a victim of sextortion is a frightening experience, one that can provoke a flurry of emotions and uncertainty about the next steps. When the situation escales to threats or the sharing of personal content without your consent, it’s critical to reach out for help. Understanding when and how to involve authorities is paramount for your safety and to ensure legal action can be taken against the perpetrator.
Reporting Sextortion to Law Enforcement: When and How
As soon as you become aware of being sextorted, your first step should be to preserve any evidence, such as messages, emails, or social media interactions. Once you have safeguarded this evidence, it’s crucial to report the incident to law enforcement. Timing is key – reporting early helps authorities take swift action and can prevent the spread of your private images. When reporting, be clear and provide all the evidence you’ve collected. Law enforcement agencies understand the sensitivity of these cases and are trained to handle them with confidentiality and care.
In conclusion, the journey to recovery from sextortion involves timely action, legal intervention, and taking diligent steps to protect your online presence. By understanding when to involve authorities and seek professional help, you can navigate this challenging time more effectively. Remember, support is available, and you don’t have to face this situation alone.
Is Your Device Secure? Conduct a Malware Scan
Regular malware scans are a simple yet effective way to protect your data and personal information against scams. This step-by-step guide will walk you through scanning and safeguarding your computer and mobile devices against malware threats.
Scan and Safeguard Your Computer with SpyHunter
Maintaining the security of your computer requires proactive measures, starting with a comprehensive malware scan. SpyHunter is a powerful anti-malware tool designed to identify and remove threats, ensuring your computer remains secure. Here’s how to use SpyHunter to protect your PC:
- Download SpyHunter from the official website and install it on your computer.
- Open SpyHunter and navigate to the Scan section to initiate a system scan. SpyHunter will update its malware definitions to detect the latest threats.
- Allow the scan to complete. This process may take some time, depending on the amount of data stored on your computer.
- Once the scan is finished, SpyHunter will display a list of detected malware and potentially unwanted programs. Review these findings and select the Quarantine option to remove the threats from your computer.
- If prompted, restart your computer to finalize the removal process.
Regular scans with SpyHunter can help detect and remove malware before it causes serious damage. It’s recommended to set a scanning schedule that fits your usage patterns for the best protection.
Protecting Your Mobile Devices Against Malware Threats and Scams
Mobile devices, just like computers, are susceptible to malware infections. Protecting your smartphone or tablet is essential for safeguarding your personal information. Here’s how you can keep your mobile device secure:
- Install a reliable anti-malware app for Android. Ensure you download it directly from the official Play Store to avoid counterfeit applications.
- Open the app and complete the setup process, granting the necessary permissions for the app to scan your device effectively.
- Run a full scan to assess your device for any existing threats. This will help identify and remove malware, adware, and other unwanted programs that could compromise your device’s performance or security.
- Review the scan results, and if any threats are detected, use the app’s instructions to remove or quarantine them.
- Consider setting up regular automatic scans to ensure continuous protection against new threats.
By taking these steps to protect your mobile device, you can minimize the risk of malware infections and keep your personal information safe.
Prevent Future Attacks: Building a Defense Against Sextortion Fraud
Building a powerful defense mechanism against scams such as “Security status not satisfied” involves a multi-layered strategy that begins with education and spans across the implementation of state-of-the-art cybersecurity measures. By fortifying our digital lives with knowledge and tools, we carve out a fortress that’s considerably more challenging for sextortionists to penetrate.
Education and Awareness
Knowledge is power, and in the fight against sextortion, it’s your most effective shield. Understanding the common tactics sextortionists use, such as psychological manipulation and technological deception, can significantly reduce the risk of falling victim. Awareness campaigns and educational programs can enlighten individuals about the importance of privacy and the risks associated with sharing personal or intimate information online. Familiarizing yourself with the signs of a sextortion attempt ensures you’re always a step ahead of the perpetrators.
- Recognize phishing emails or messages that might look legitimate but ask for personal information or contain dangerous links.
- Stay informed about new types of online scams and threats by following reputable cybersecurity news sources.
- Discuss online safety with friends and family, especially younger people who may be more vulnerable to digital threats.
Implementing a Comprehensive Cybersecurity Strategy
Incorporating a comprehensive cybersecurity strategy is essential for protecting against “Security status not satisfied” and other sextortion scams. This includes employing a powerful antivirus solution, like SpyHunter, which scans for and removes malware that could be used to exploit victims. Regularly updating software and using strong, unique passwords across all accounts further bolster your defenses. Additionally, enabling two-factor authentication wherever possible adds an extra layer of security that can deter attackers from gaining access to your personal information.
- Install reputable security software that offers real-time protection against malware and ransomware.
- Utilize password managers to create and store complex passwords, minimizing the risk of account breaches.
- Regularly update all devices and applications to protect against the latest vulnerabilities.
Addressing the Emotional Impact of Sextortion: Seeking Support
The psychological impact of falling victim to sextortion can be profound, with many experiencing stress, anxiety, and a sense of isolation. It’s essential for victims to understand that emotional support is available and seeking help is a sign of strength. Engaging with emotional support groups, mental health professionals, or hotlines can provide the necessary guidance and reassurance to navigate this challenging time. Resources like Thorn and the National Suicide Prevention Helpline offer judgment-free zones where victims can find solace and strength. Additionally, turning to trusted family members and friends for support can provide a critical emotional lifeline, helping victims reclaim a sense of normalcy and control over their lives.
In situations where mental health is adversely affected, professional help from psychologists or psychiatrists can be instrumental in addressing long-term impacts like depression and anxiety. These specialists can offer strategies to manage emotional distress, fostering a path towards recovery. Remember, it’s crucial to prioritize your emotional well-being and seek out supportive communities and professional help to navigate the recovery process successfully.
Conclusion
Scam emails such as “Security status not satisfied”, employing tactics of fear, urgency, and deception, exploit human psychology to elicit swift, unthinking responses. These tactics include creating a false sense of familiarity, shocking the recipient into compliance, and crafting scenarios of dire consequences should the recipient fail to act. This manipulation bypasses critical thinking, leveraging the raw emotional reactions of fear, uncertainty, and haste.
To safeguard against these insidious threats, it is crucial to adopt protective measures. Ensuring the use of separate email accounts for personal, business, and other activities can help compartmentalize and protect important information. While major email service providers offer robust anti-spam technologies, supplementing these with specialized software like SpyHunter provides an added layer of security. SpyHunter is engineered to detect and neutralize threats, offering peace of mind in the face of the ever-present danger posed by scam emails and other malicious digital content. By staying informed, vigilant, and equipped with effective tools, users can navigate the digital world with confidence and security.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove "Security status not satisfied" from Windows.
Step 1: Scan for "Security status not satisfied" with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





Step 3: Uninstall "Security status not satisfied" and related software from Windows
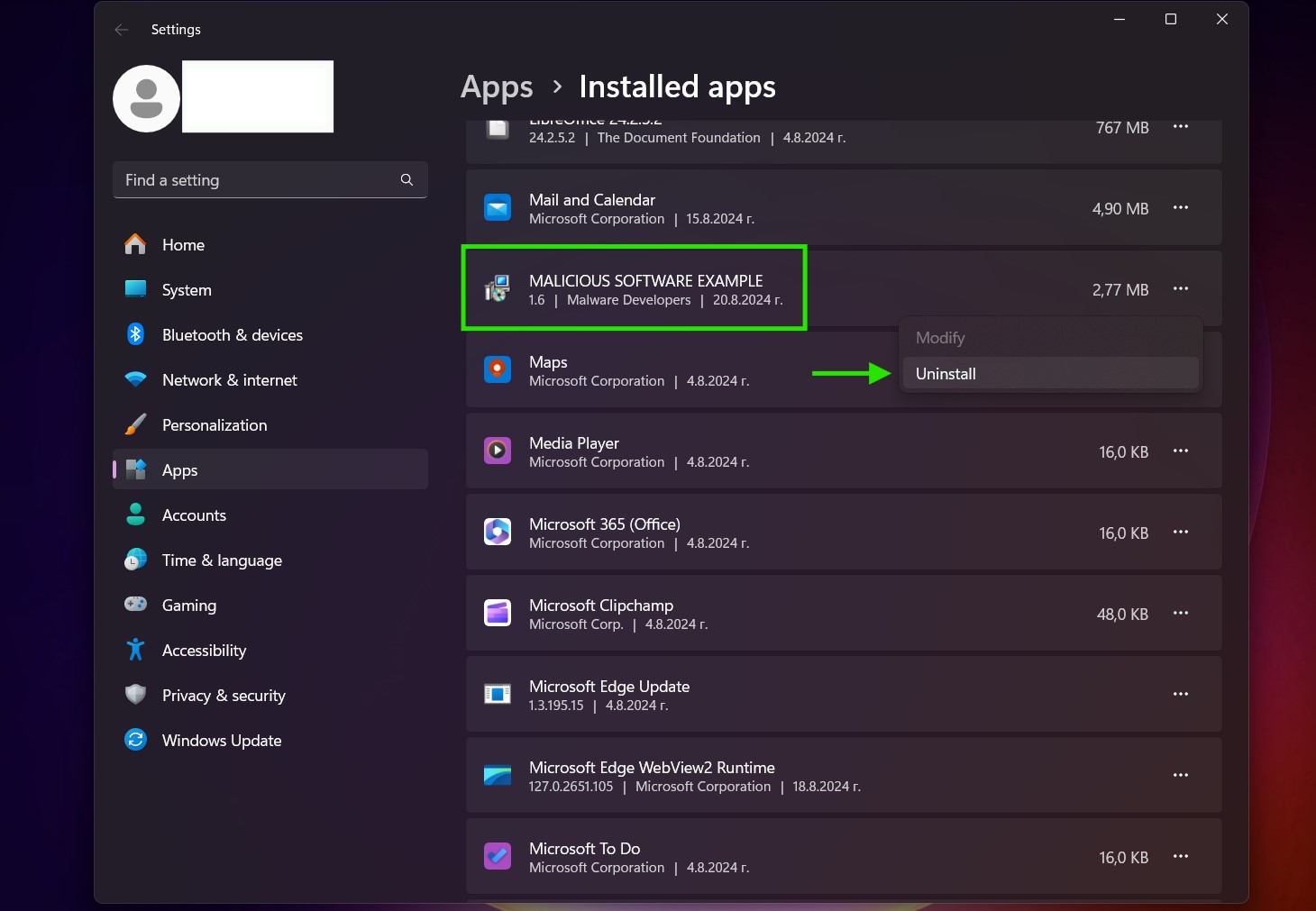
Uninstall Steps for Windows 11
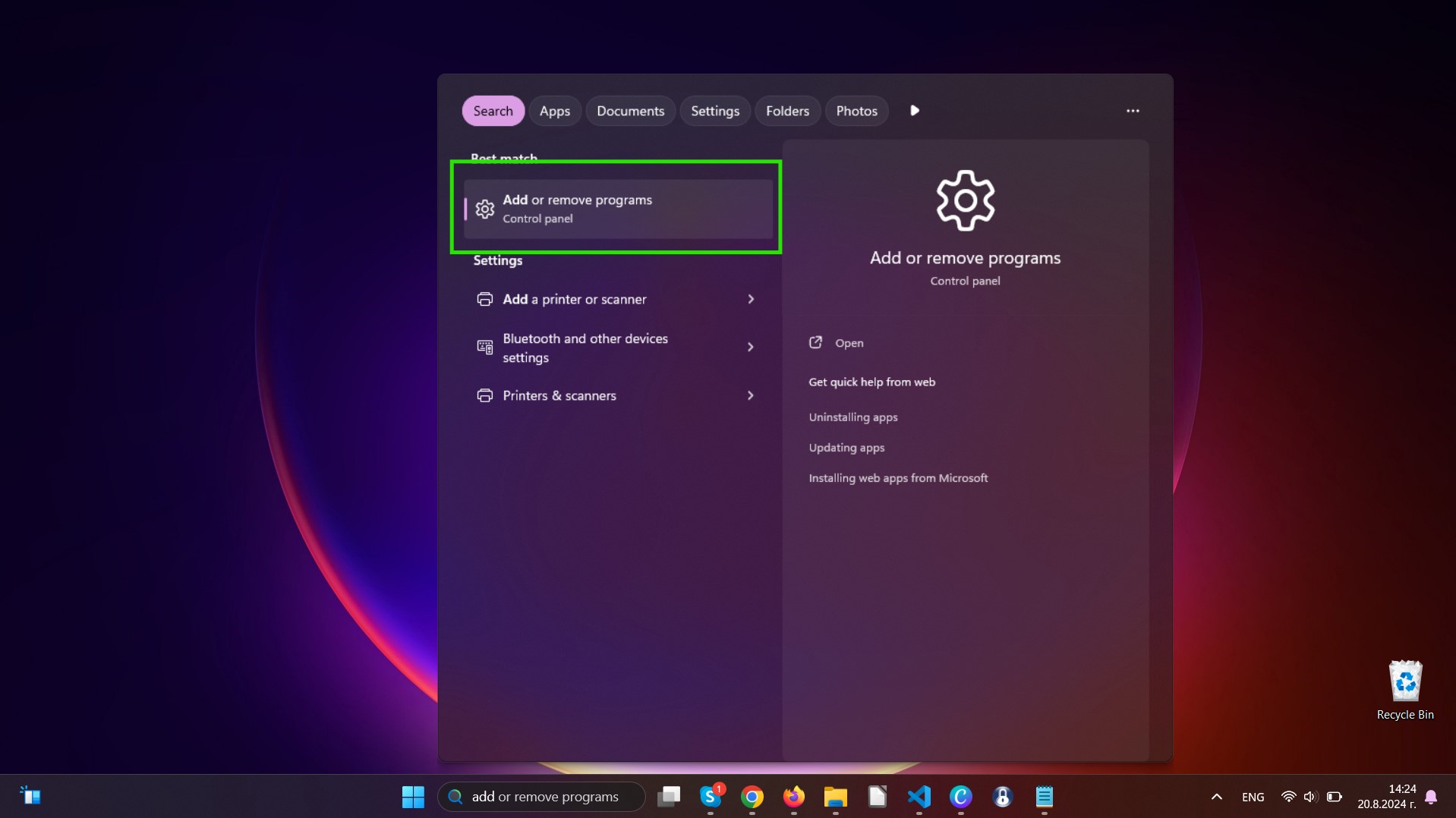
Uninstall Steps for Windows 10 and Older Versions
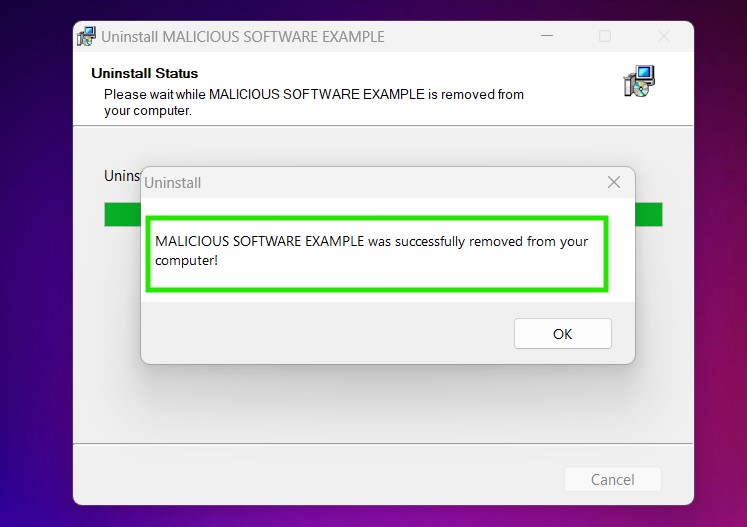
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by "Security status not satisfied" on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by "Security status not satisfied" there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for "Security status not satisfied" (Windows).
Get rid of "Security status not satisfied" from Mac OS X.
Step 1: Uninstall "Security status not satisfied" and remove related files and objects
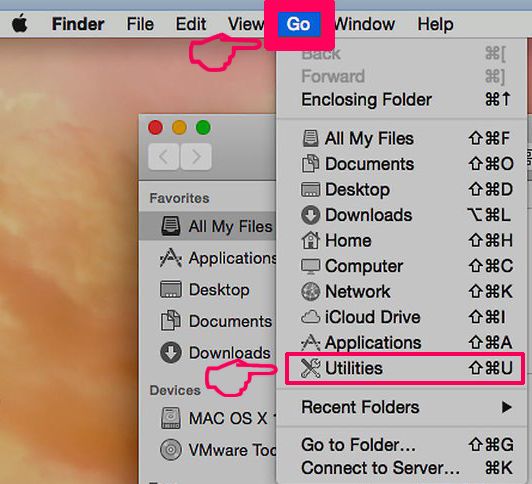
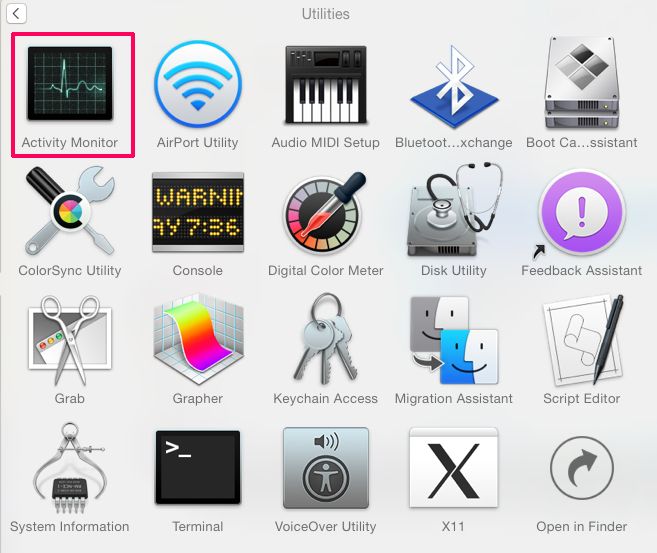
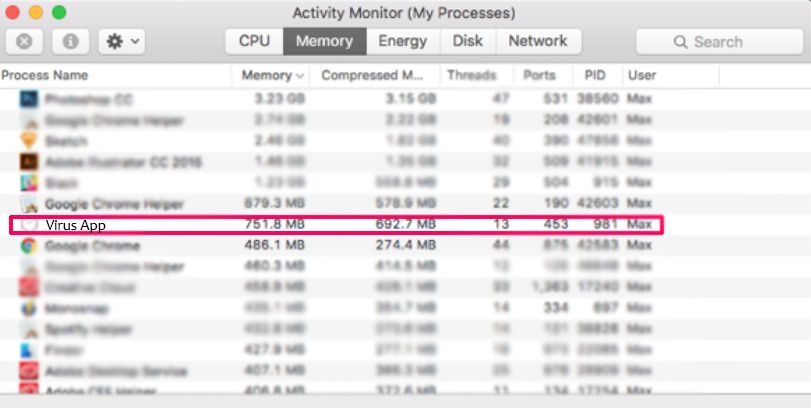
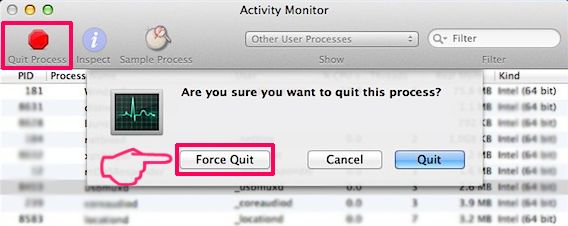
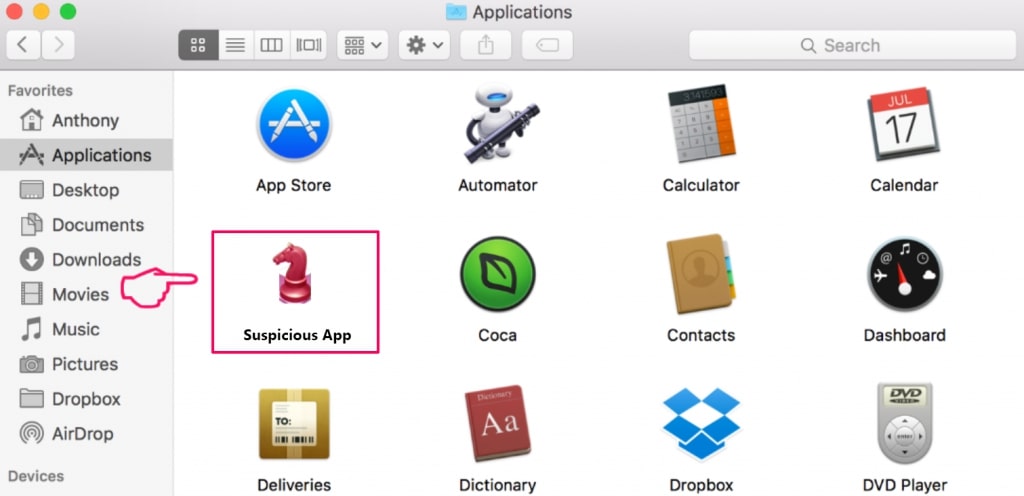
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to "Security status not satisfied". Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove "Security status not satisfied" via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
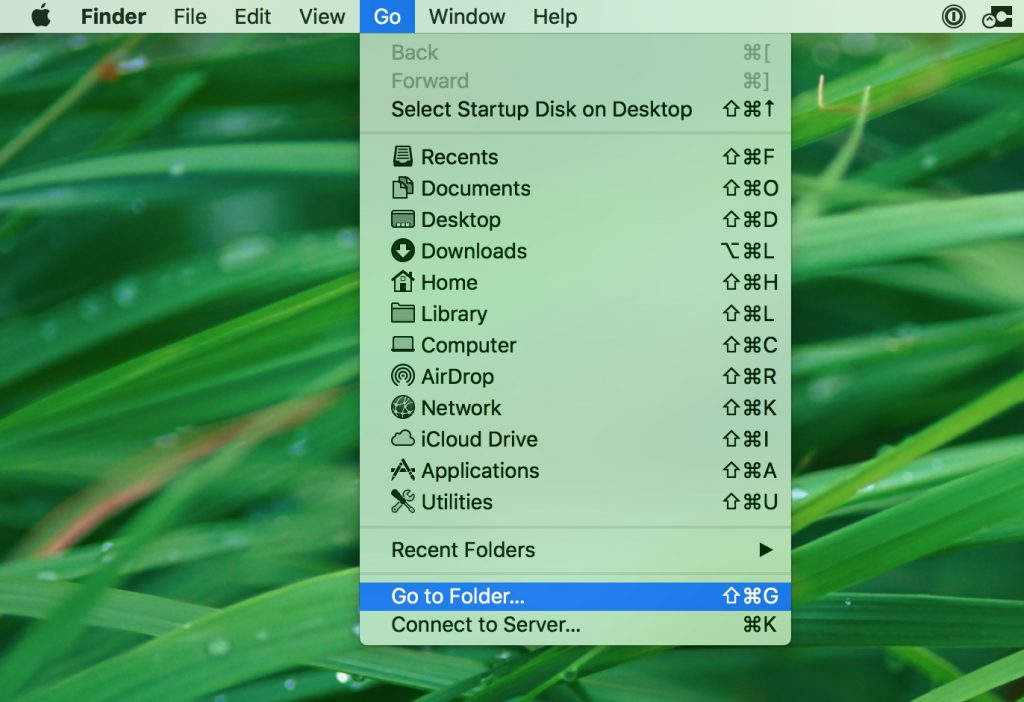
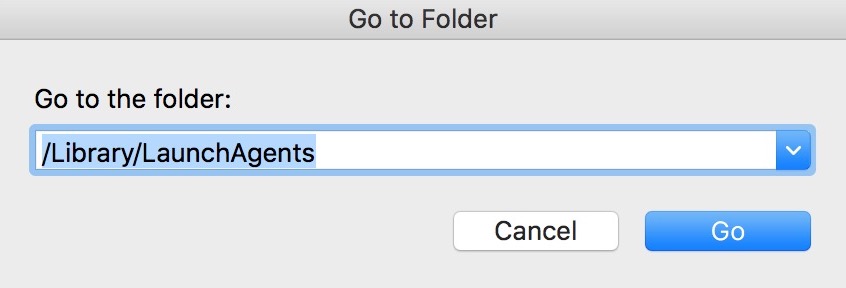
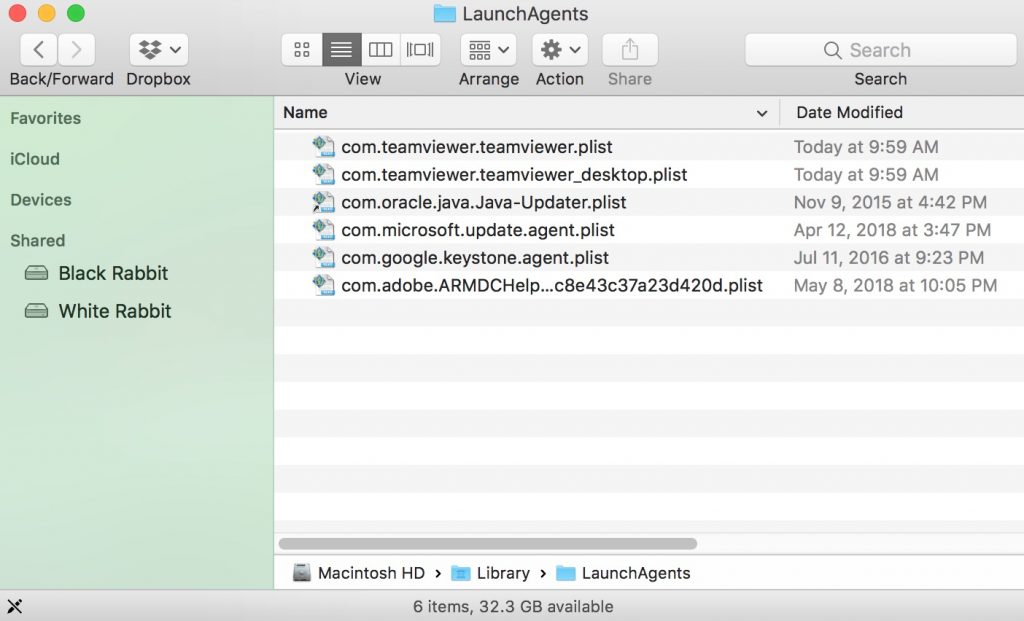
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove "Security status not satisfied" files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as "Security status not satisfied", the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for "Security status not satisfied" (Mac)
Remove "Security status not satisfied" from Google Chrome.
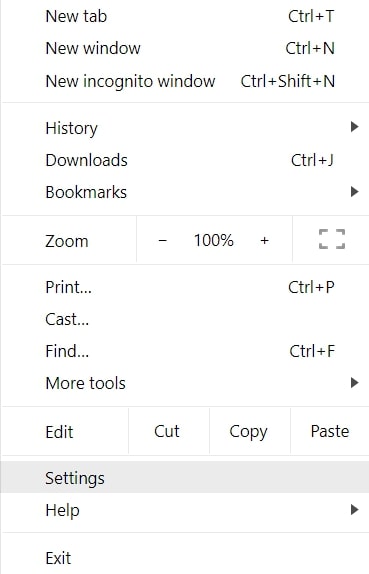
Step 1: Start Google Chrome and open the drop menu
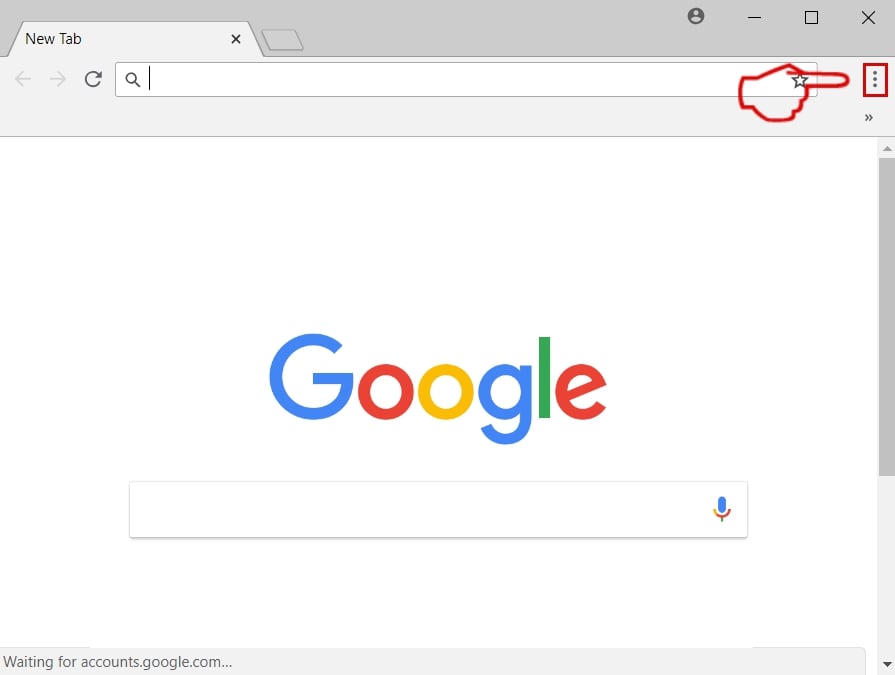
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
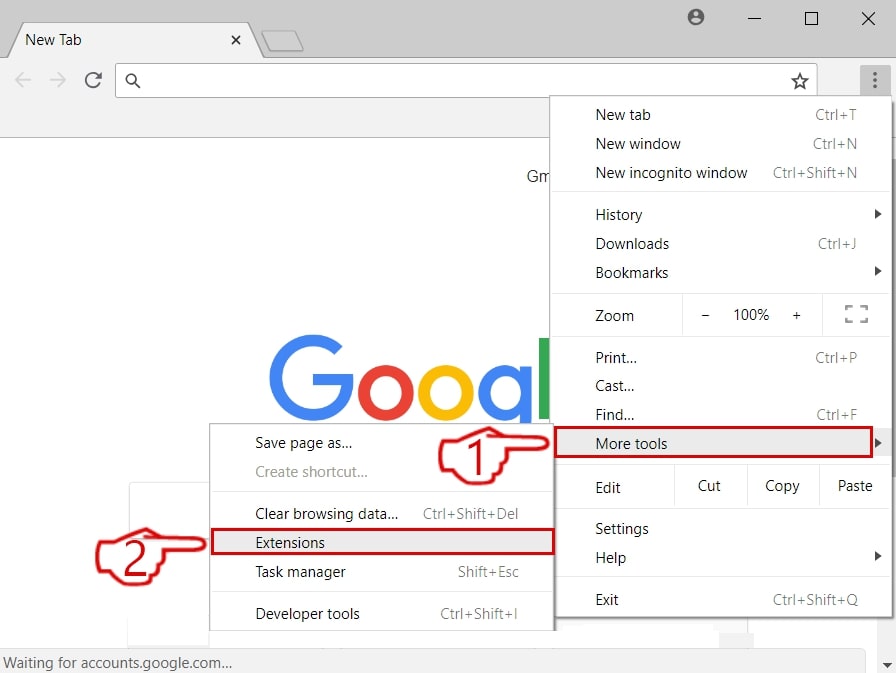
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
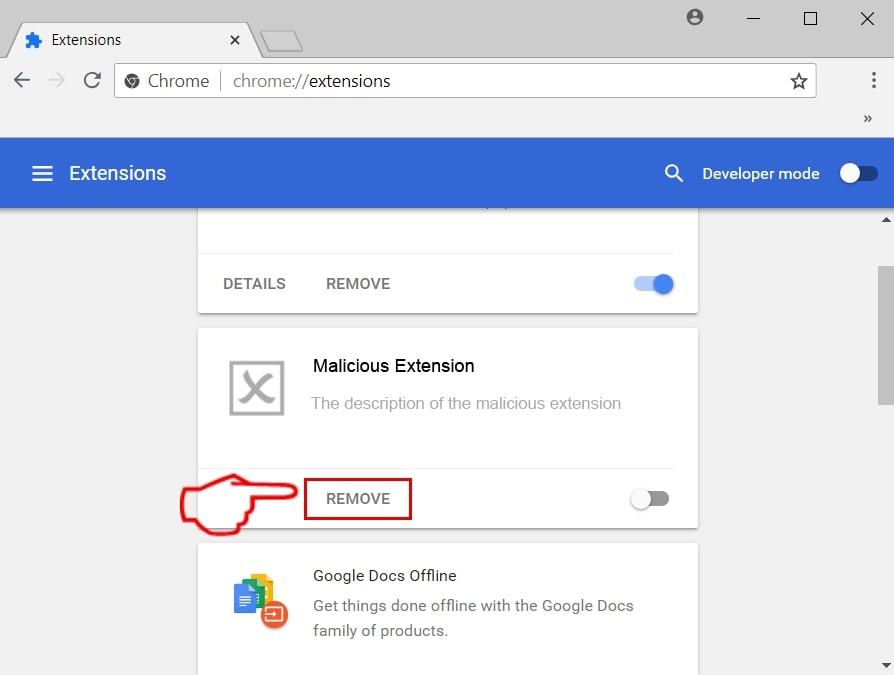
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase "Security status not satisfied" from Mozilla Firefox.
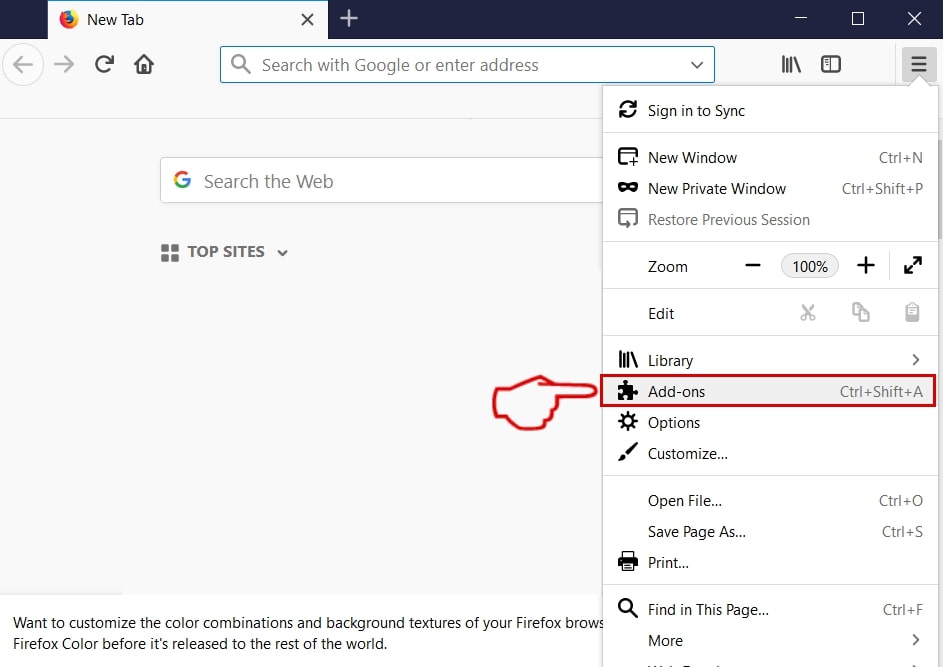
Step 1: Start Mozilla Firefox. Open the menu window:
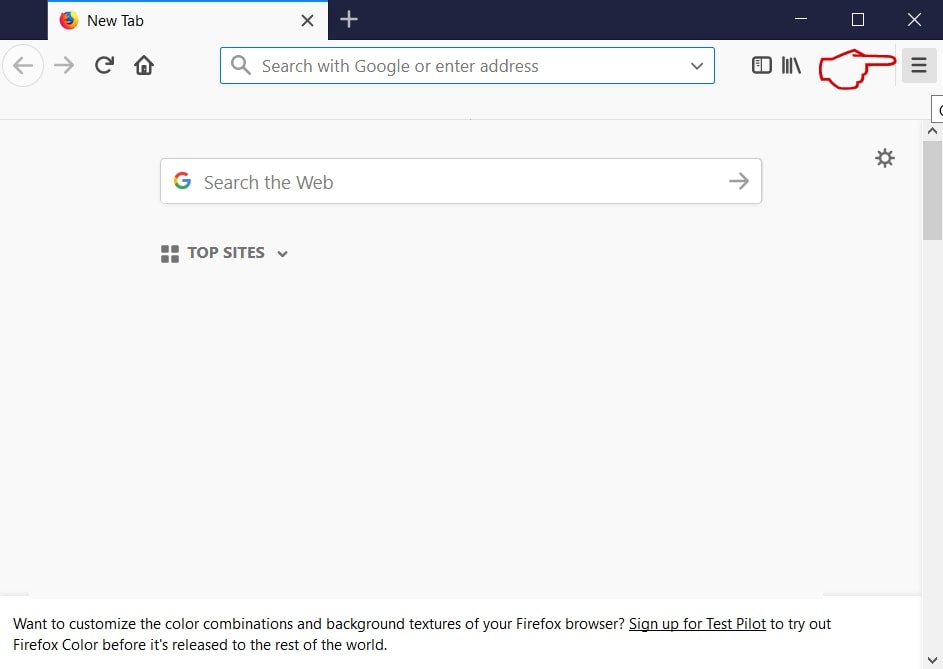
Step 2: Select the "Add-ons" icon from the menu.
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
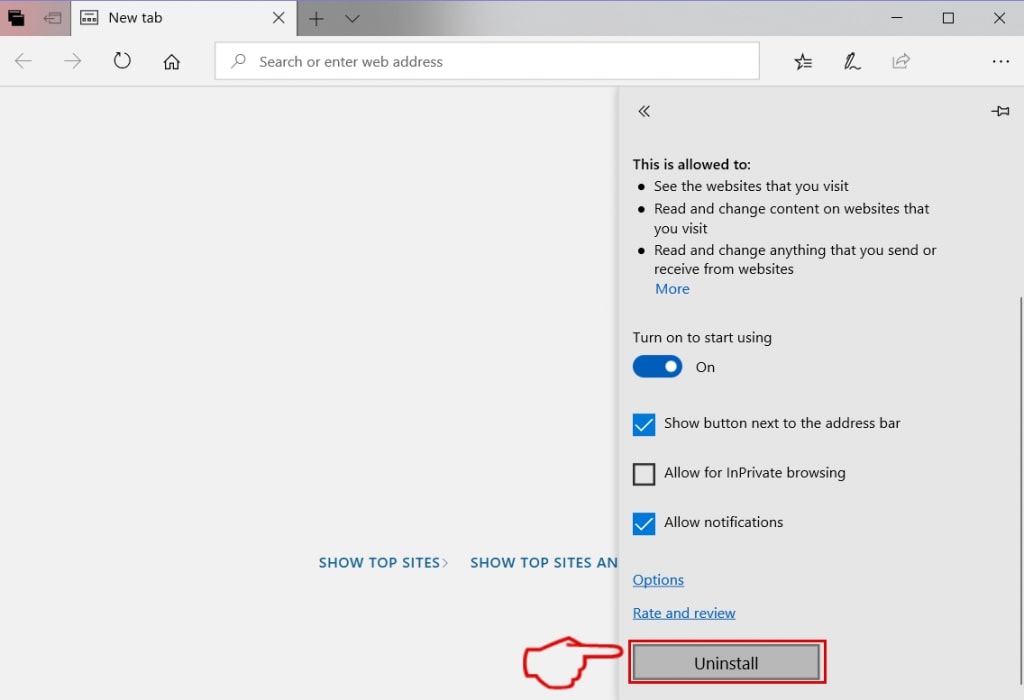
Uninstall "Security status not satisfied" from Microsoft Edge.
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
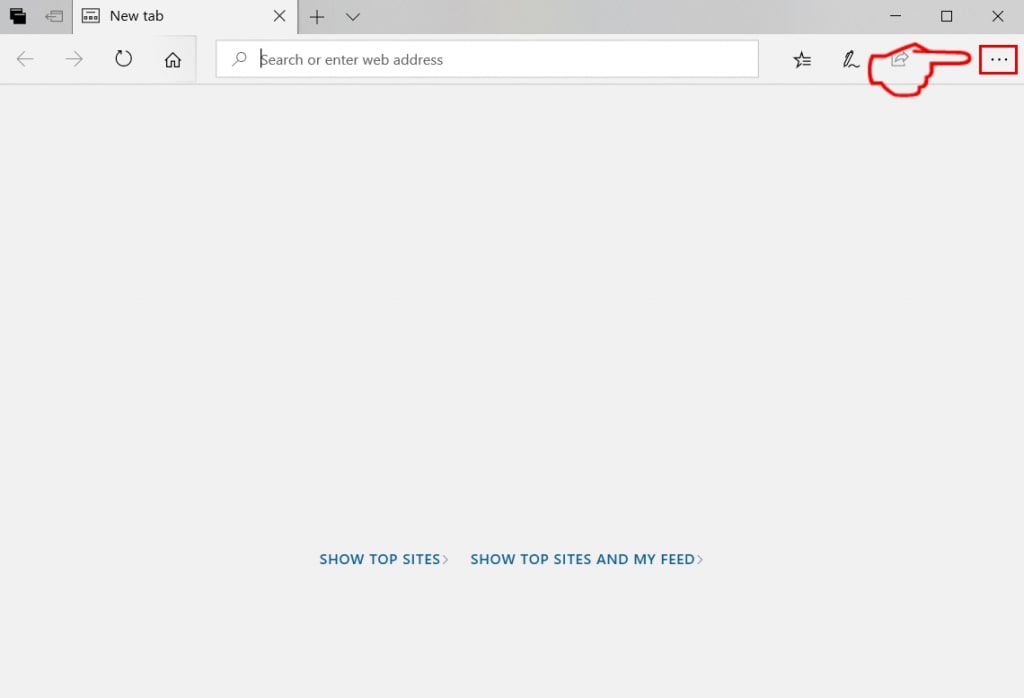
Step 3: From the drop menu select "Extensions".
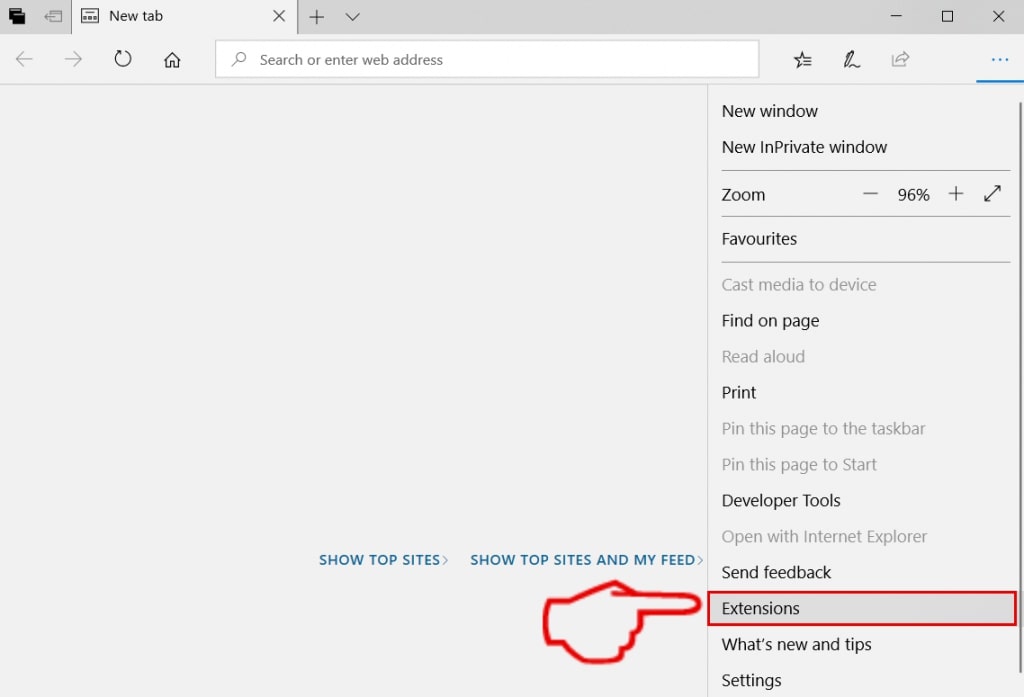
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
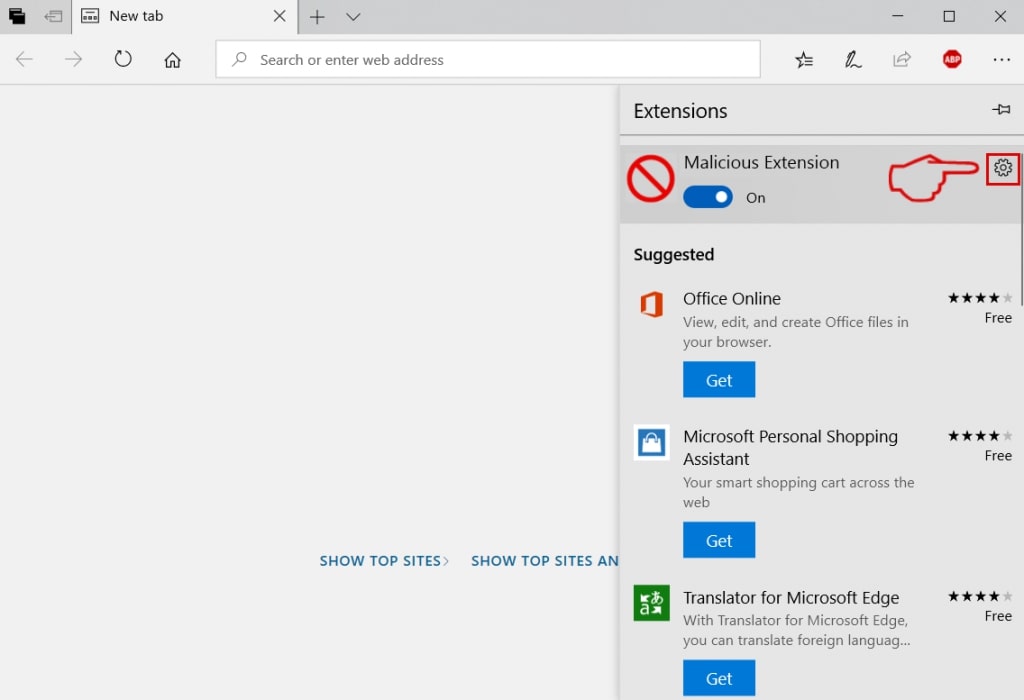
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
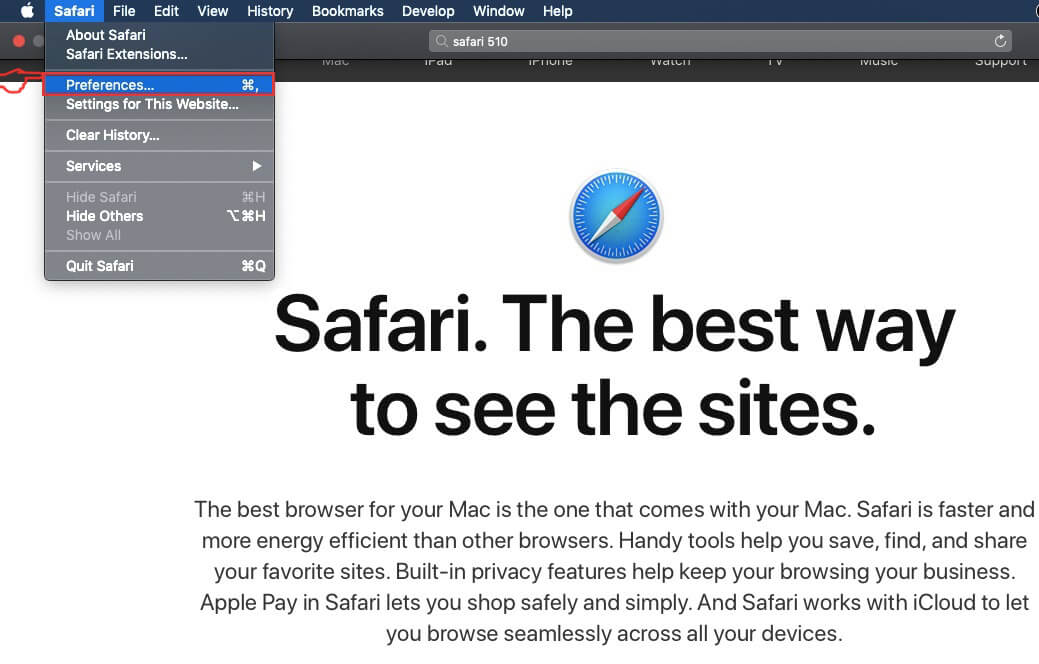
Remove "Security status not satisfied" from Safari
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
Step 4: After that, select the 'Extensions' Tab.
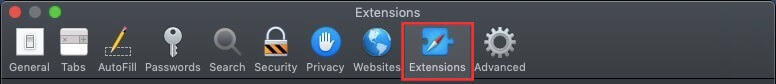
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
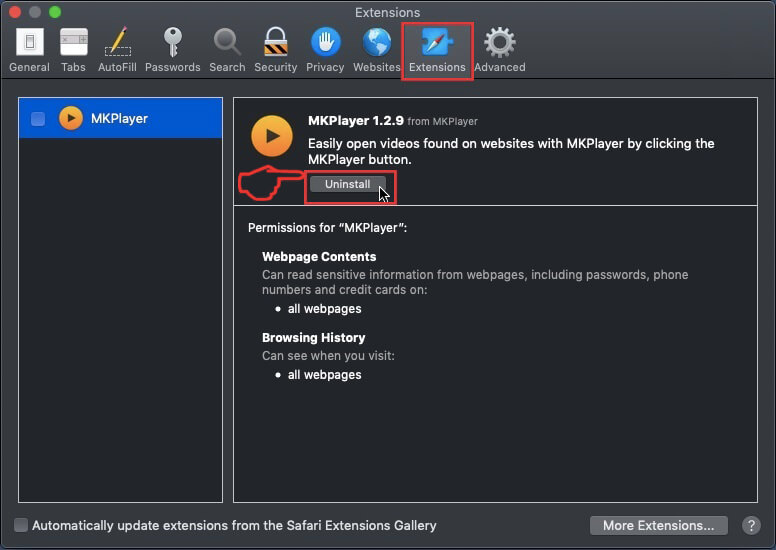
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the "Security status not satisfied" will be removed.
Eliminate "Security status not satisfied" from Internet Explorer.
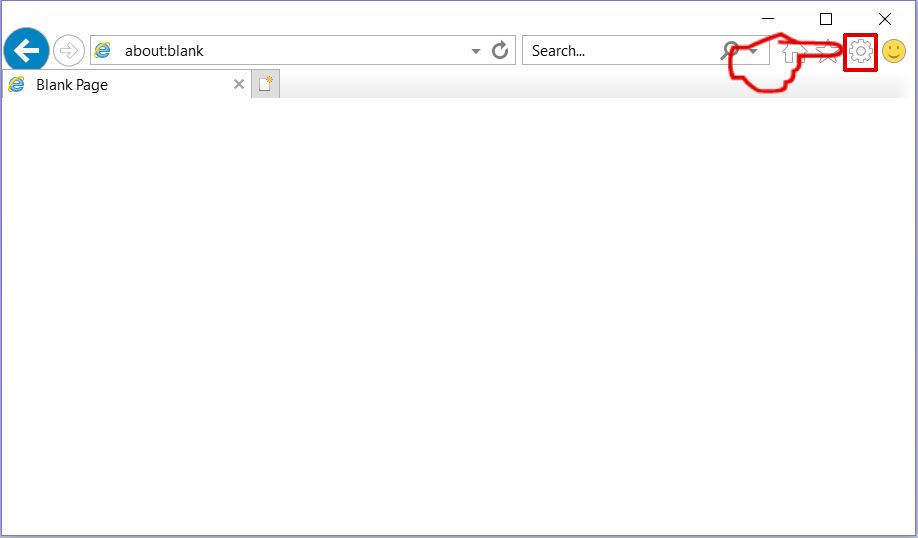
Step 1: Start Internet Explorer.
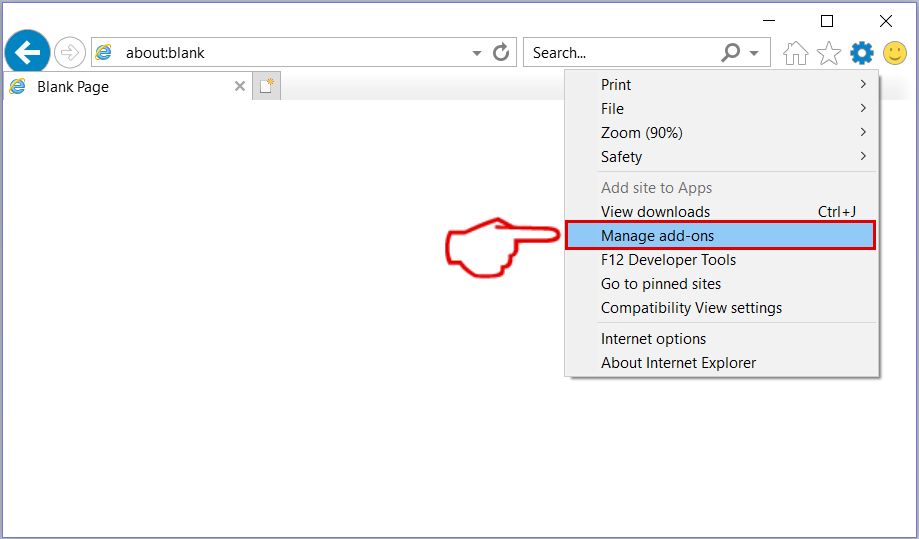
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
Step 3: In the 'Manage Add-ons' window.
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
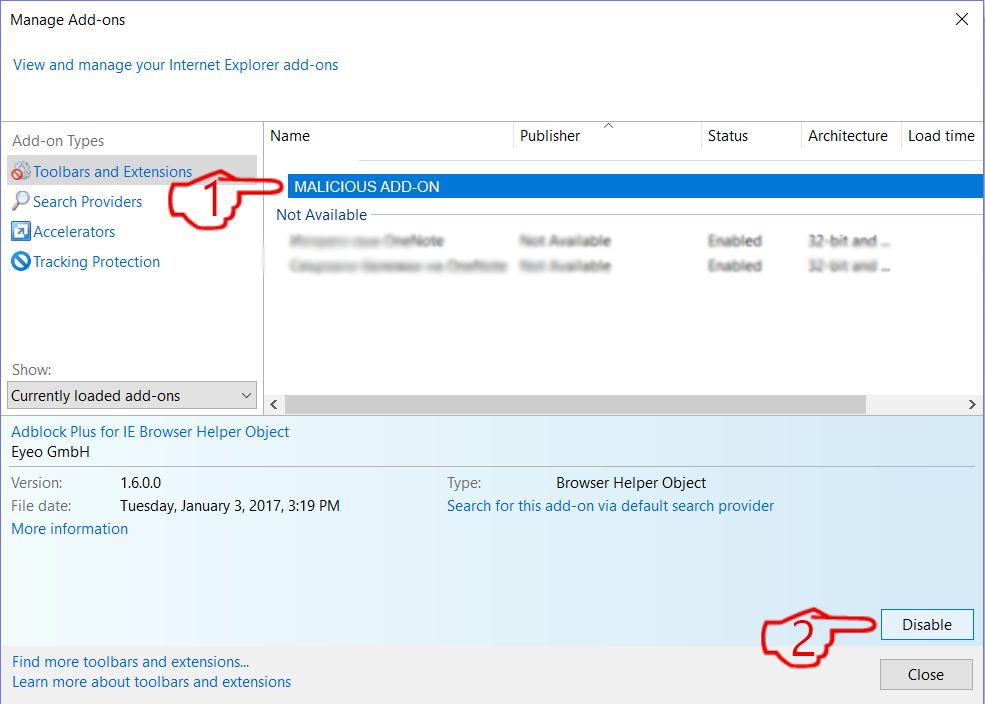
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
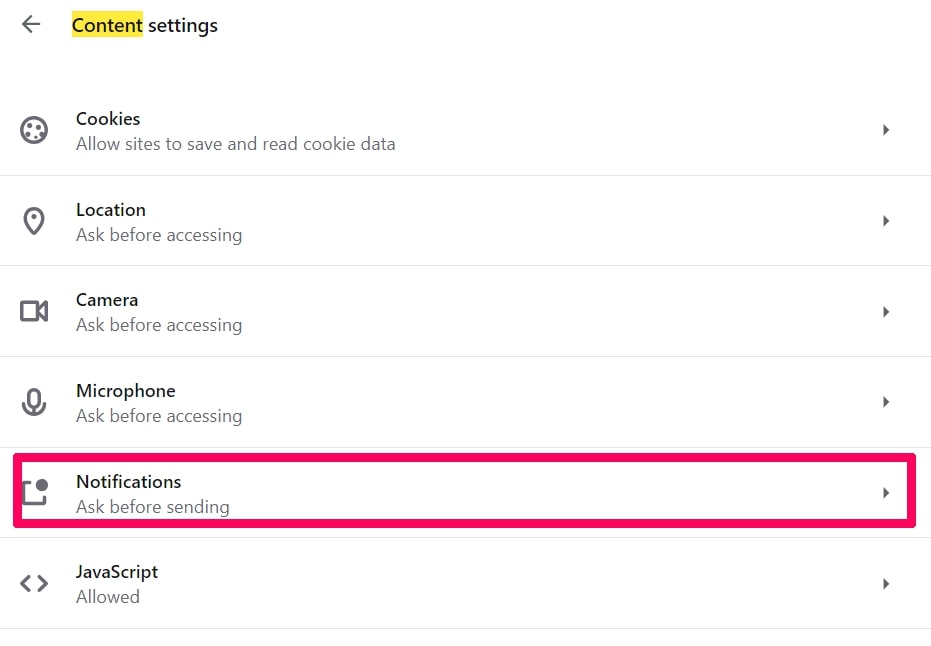
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
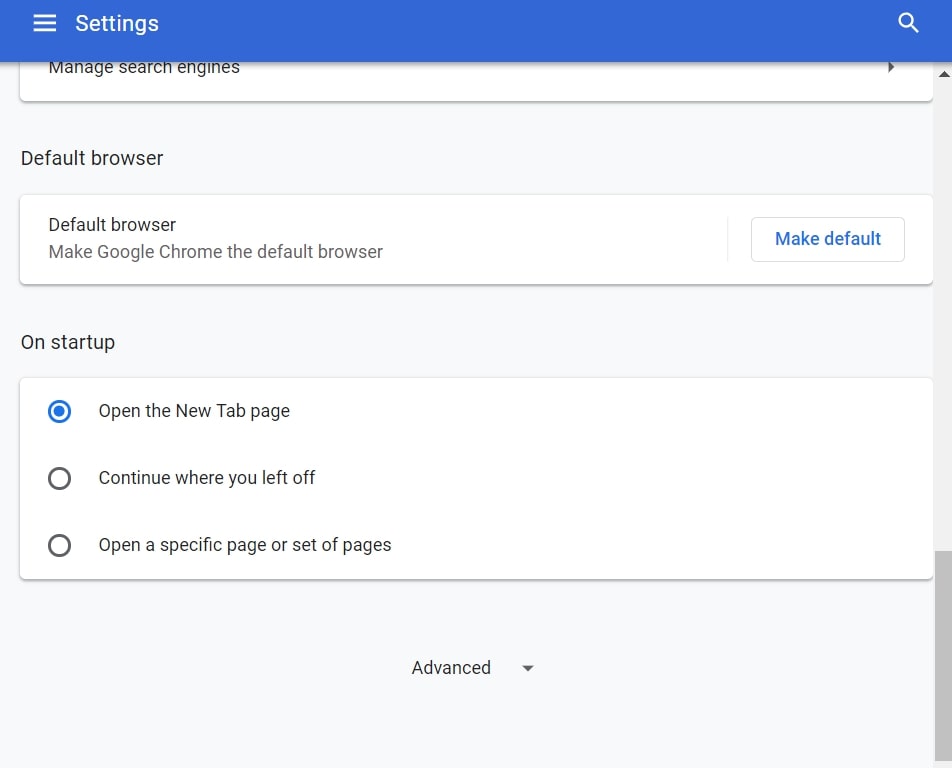
Step 3: Click “Content Settings”:
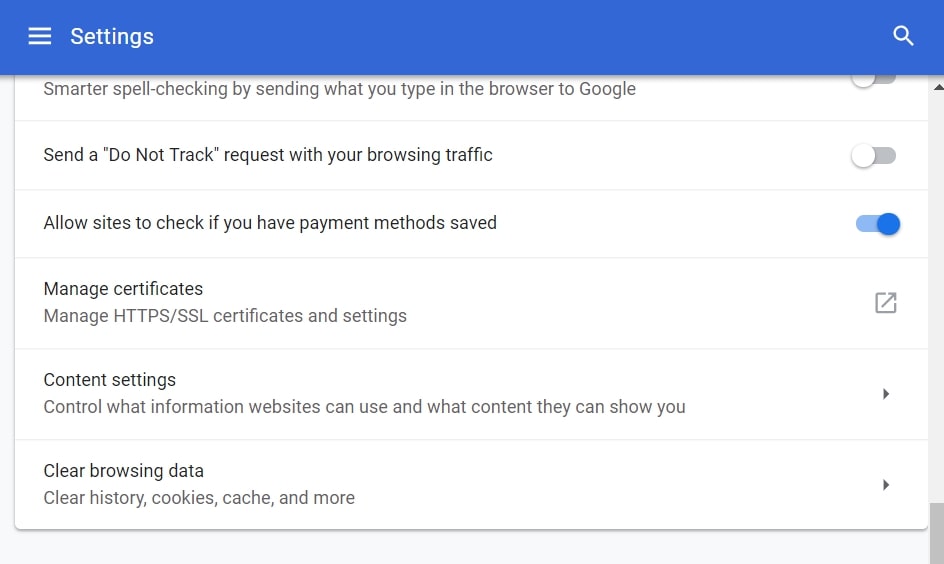
Step 4: Open “Notifications”:
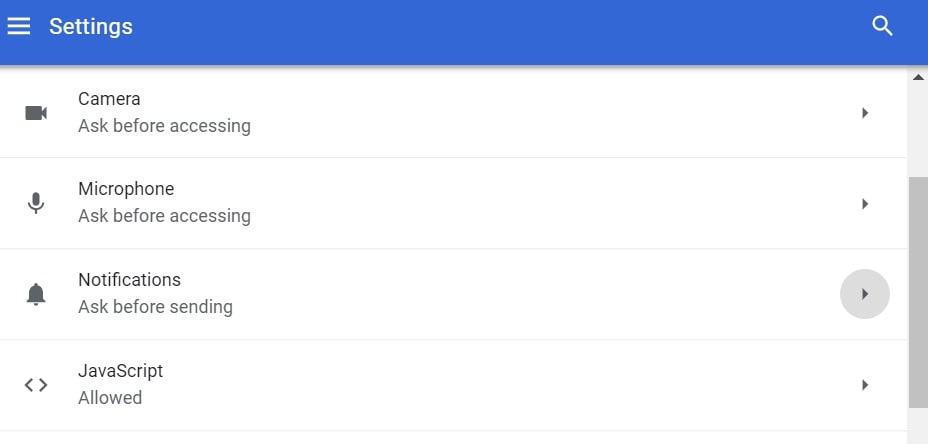
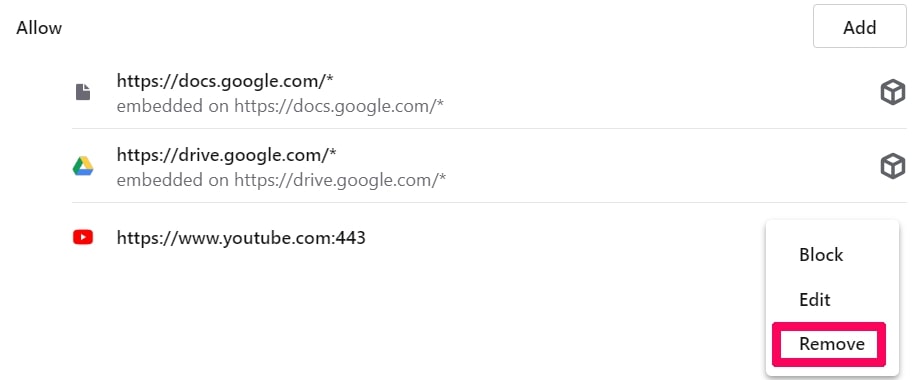
Step 5: Click the three dots and choose Block, Edit or Remove options:

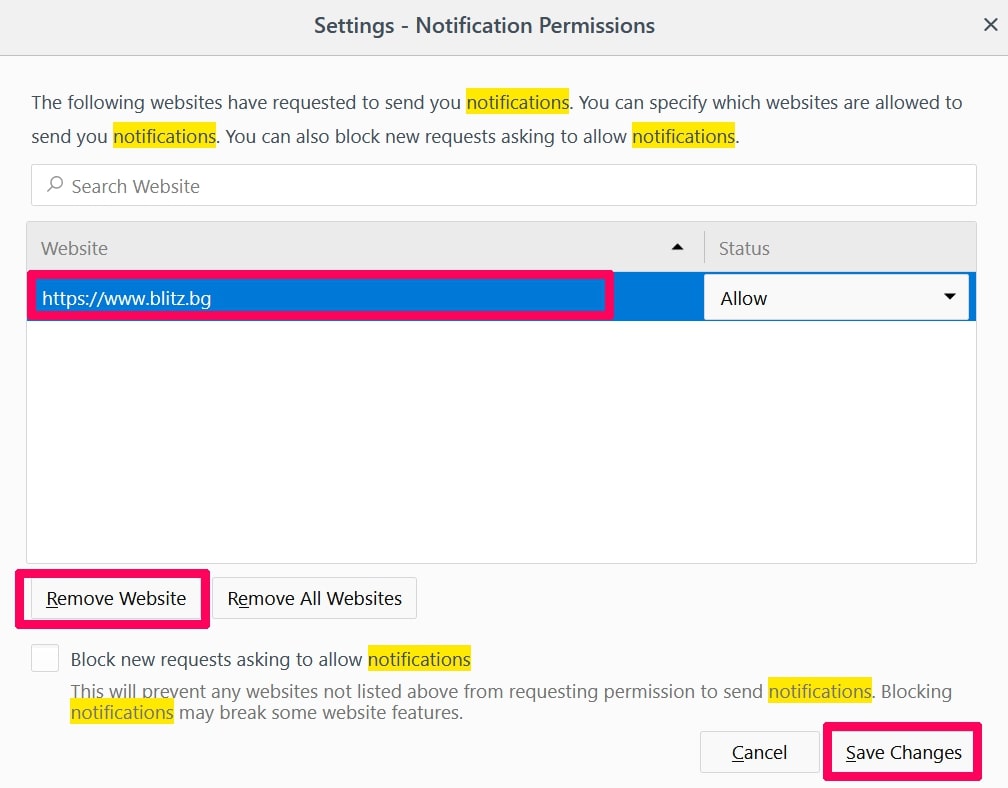
Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
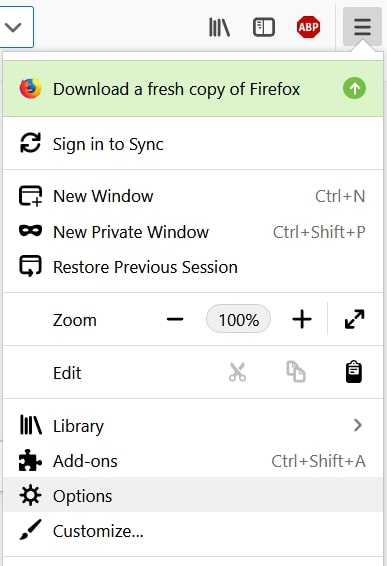
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
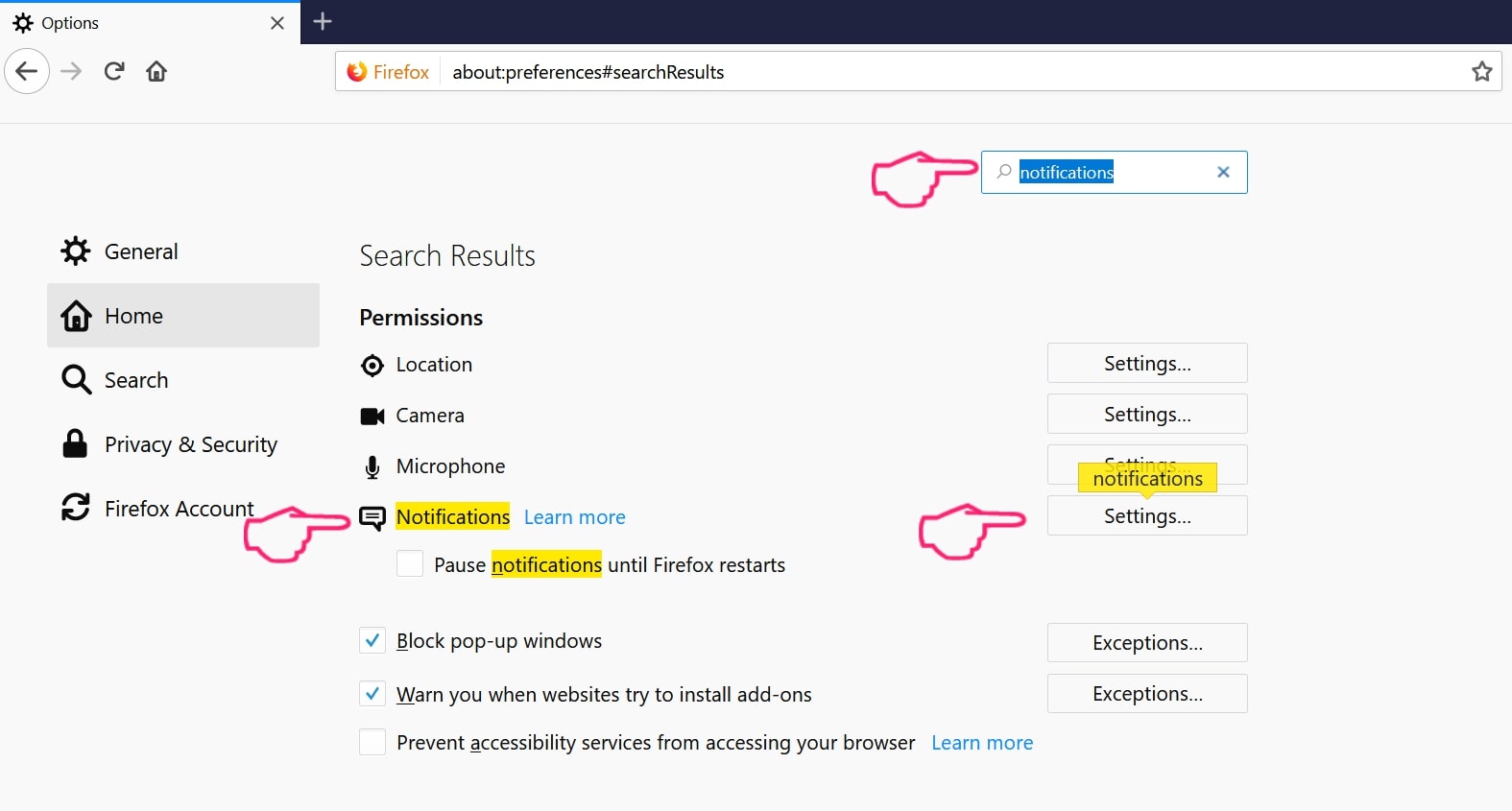
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
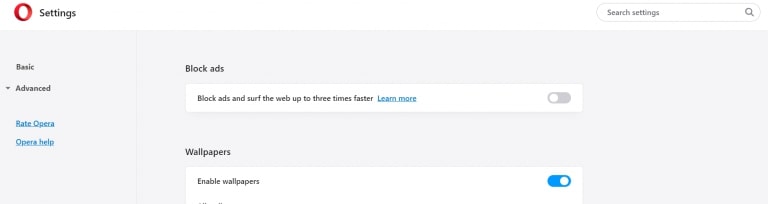
Step 2: In Setting search, type “Content” to go to Content Settings.
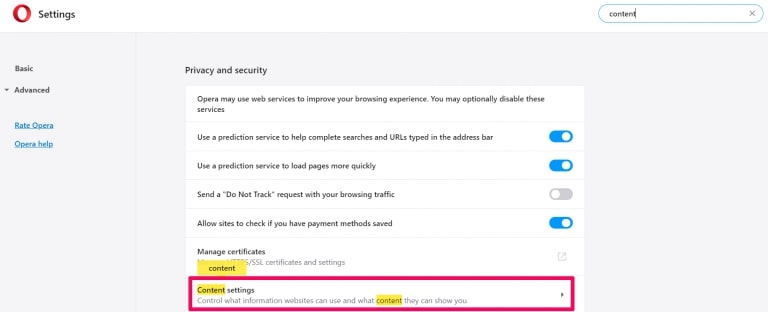
Step 3: Open Notifications:
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
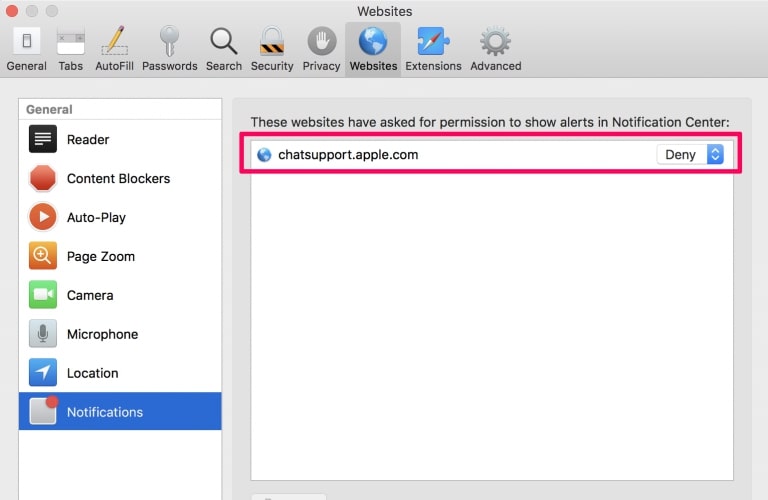
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
"Security status not satisfied"-FAQ
What Is "Security status not satisfied"?
The "Security status not satisfied" threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of "Security status not satisfied"?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like "Security status not satisfied"?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does "Security status not satisfied" Work?
Once installed, "Security status not satisfied" can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
"Security status not satisfied" can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is "Security status not satisfied" Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the "Security status not satisfied" Research
The content we publish on SensorsTechForum.com, this "Security status not satisfied" how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on "Security status not satisfied"?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the "Security status not satisfied" threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.


