Multiple reports have been issued regarding newly emerged online scams that are currently infecting users. These scams are relying on the names of well-known companies like Amazon and DHL to trick users into interacting with them.
The scams are usually distributed via spam email messages and may lead to various outcomes, malware infections included. However, the good news is there are ways to recognize the scams and prevent them from harming your computer and personal information. See how below.
This article will introduce you to the currently active online hoaxes that are plaguing users worldwide, and will also link you to specific instructions for each of the scams.
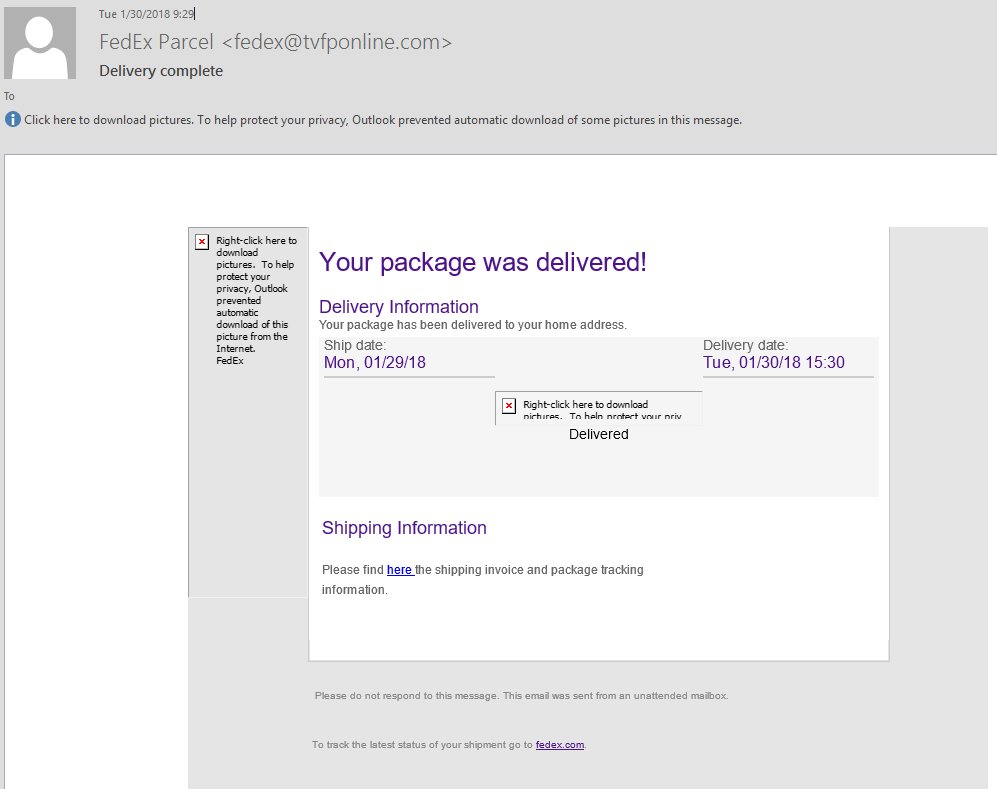
The FedEx Parcel Scam
The FedEx Parcel Scam is an active infection that is currently being distributed in a mass email campaign. The hackers behind it have hijacked the template used by the FedEx company, including the relevant graphics and text in order to spoof them as much as possible. The senders’ email addresses may also resemble real email addresses used by FedEx as they may use familiar-sounding domain names.
Another tactic would be the use of browser hijackers that represent malware plugins made for the most popular applications. They are usually compatible with Mozilla Firefox, Safari, Internet Explorer, Google Chrome, Opera and Microsoft Edge. They can be uploaded to the software repositories of the relevant browsers by posing as feature additions or enhancements.
Once they are installed, dangerous changes are made to the browsers, including redirects to hacker-controlled pages. Scammers can also spread the malware via infected software installers. These installers are frequently made by taking the legitimate setup files from the official vendors. Then they are modified to include the malware code as soon as the installers are launched.
The “Firefox requires a manual update” Scam
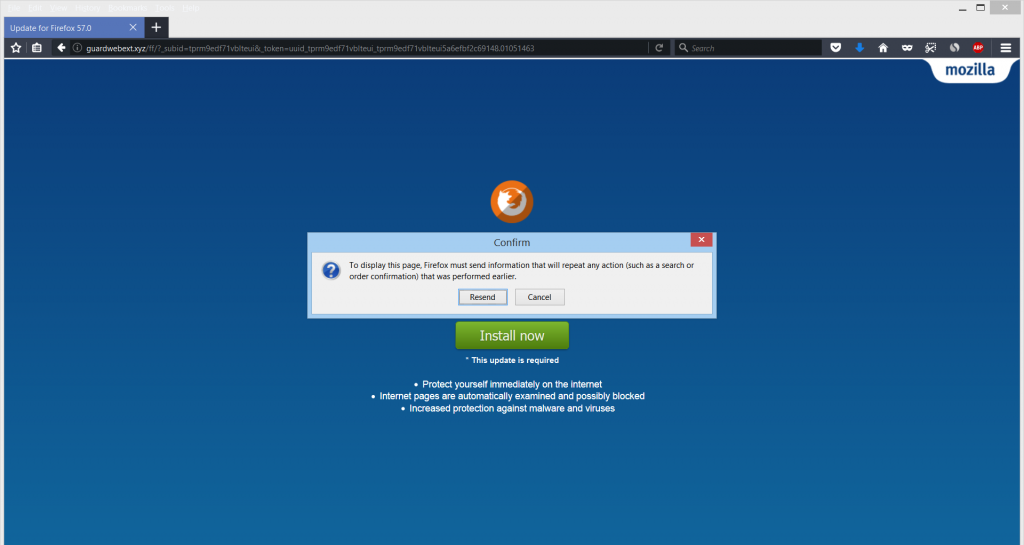
A new web page, claiming to be an update for the latest version of Mozilla Firefox has been reported to harass users, asking them to share their username and password to authenticate. Malware researchers believe that this suspicious web page is introduced to victims’ computers as a result of having a potentially unwanted program. Such programs are known to alter browsers and affect their performance.
Since this is a suspicious web page, there may be more than one ways to come in contact with it. One method is by visiting the corresponding web page as a result of an unwanted redirection, which is set to insert JavaScript that causes your web browser to open a new tab.
Another distribution method is via the installation of an unwanted program in the form of freeware. Potentially unwanted programs are mostly spread via software bundling. Software bundling is a method by which the adware application comes standard with a free program you may be trying to download, like a driver for your PC, a torrent downloader program or the setup of any other free software.
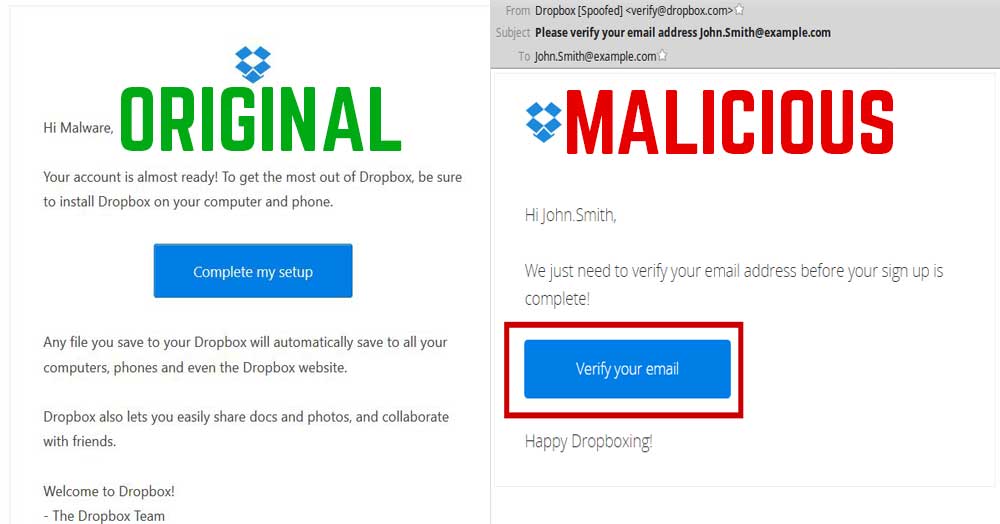
The Dropbox Phishing Scam
Spam distributed via email often abuses the names of popular companies to increase the chance of tricking users. Dropbox is yet another name that has been deployed in such spam campaigns.
Dropbox’s name has been used in phishing e-mails to get victims to click on suspicious e-mails in order to become infected with Dropbox malware. These e-mails may not all be fake, and most of those may also lead you to the actual Dropbox website where most victims usually download infection files of different malware. There are ways, however, to identify original from fake Dropbox e-mails, and to learn how to block the fake ones directly in your e-mail.
The DHL Phishing Scam
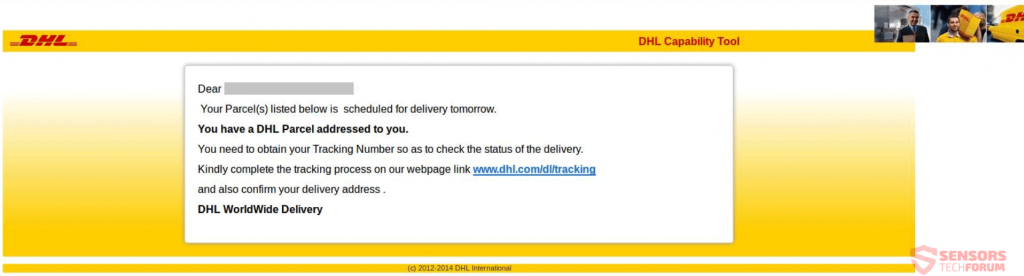
DHL Phishing scams are quite widespread across the world. From specially crafted websites that push such scams, to specific messages sent to targeted email addresses, the DHL brand has been used in phishing scams for nefarious reasons. Such reasons include the stealing of DHL credentials, personal information or pushing malware with a hidden agenda in most cases.
More and more users fall victim to these scams as they are recurring and keep reappearing every few months. That is due to the fact that every new variant of a scam tends to mimic DHL closer than before, making it more believable with each new attempt. Ultimately, you will be asked to login or visit a URL address and do some action or pay for a shipment via another service. You should avoid any links other than the official DHL ones.
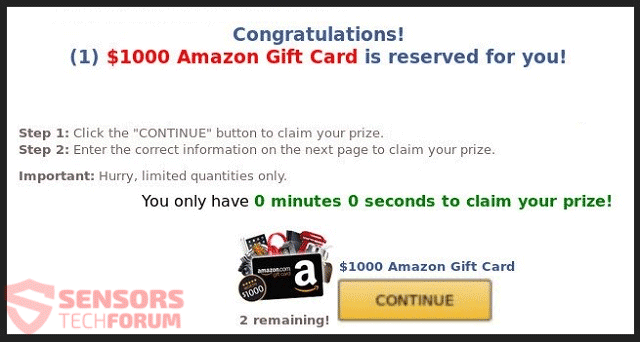
The $1000 Amazon Gift Card Scam
The so-called $1000 Amazon Gift Card scam has many variants and has been circling around the web for quite some time. With every new version of the scam that pops up, more and more users fall victim to it. The scammers behind it are getting better at mimicking the Gift Card provided by Amazon.com, Inc.
One of the latest forms of this scams comes in the shape of an adware that keeps showing pop-ups with the message $1000 Amazon Gift Card is reserved for you. Many different domains host a web page with that version of the scam. Older versions are still found across the Internet and there are also videos promoting the $1000 Amazon Gift Card Scam on YouTube. Adverts will be pushed on your browsers, and thus the scam is also recognized as adware.

How to Prevent Online Scams from Infecting Your Computer
In many cases, it is enough to ignore the scam message, never respond to it and delete it instantly. However, other more sophisticated scams require a bit of action, since they may affect your system or personal information in many ways.If you have encountered any of the scams described in this article, it’s highly advisable to thoroughly scan your computer with a professional program to determine whether you have malware components pushing spoofed messages to your computer, browser or email address.
Online users should scan their systems regularly for active infections using a an anti-malware program. Such a program would prevent malicious actions and stop malware from distributing to more computers.
SpyHunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter



Leave a Comment