 Earlier this year the malware researcher Neil J. Rubenking published a review concerning Tiranium Premium Security 2014. After the review was published, he got a message from a user claiming that Tiranium abused different online websites associated with malware checks websites in order to increase its detection rate. The researcher, Mr. Rubenking made a check with VirusTotal, however he was declined a comment. That is why the researcher had to find out for himself whether this was a problem.
Earlier this year the malware researcher Neil J. Rubenking published a review concerning Tiranium Premium Security 2014. After the review was published, he got a message from a user claiming that Tiranium abused different online websites associated with malware checks websites in order to increase its detection rate. The researcher, Mr. Rubenking made a check with VirusTotal, however he was declined a comment. That is why the researcher had to find out for himself whether this was a problem.
The nature of VirusTotal
VirusTotal is a website where the user can upload a certain file and check if it is malicious or not. VirusTotal acts in the following way – it generates hash for the file and if this hash is in the database, it returns the results that are stored. In case the hash does not exist in the database the website checks the file with approximately 50 of the largest antivirus engines. The user then gets reports on which antivirus engines have marked the file as being malicious.
VirusTotal was acquired by Google approximately 2 years ago and its service goes beyond the file checking. The aim of VirusTotal is to assist in the improvement of the security and antivirus industry and to help in the efforts of the company to turn Internet into a safe place through using free services and tools. According to the website of VirusTotal, the public services and applications are not allowed to be used in commercial products or for business purposes. This means that the products that use the results from VirusTotal without verifying that the file is malicious would be actually violating the terms of service.
WhiteShark
The user who sent a message to Neil J. Rubenking, mentioned above, stated that Tiranium checks a suspect file by its local client and then if no match is to be found, the file is checked on VirusTotal. In case there is no result from VirusTotal, then the file invokes its own scanner of behavior.
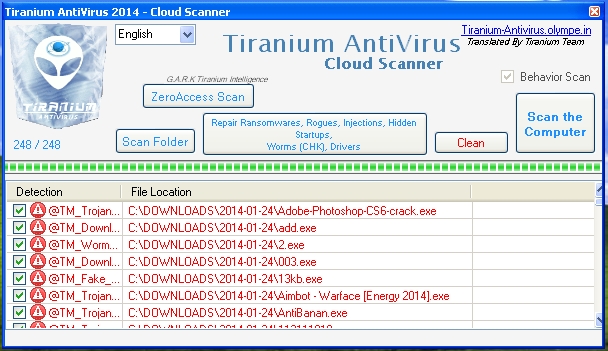
Rubenking has created new and modified version of his malware collection by changing the file size and the file names, and using certain non-executable bytes. The hash on each file has been checked with VirusTotal, in order to make sure they all are not in the database.
Then Neil J. Rubenking used the network traffic tracing utility WireShark and started a scan with Tiranium of the folder which contains these files. The scan lasted for many long hours and was not able to finish. The number of the file scanned showed zero. This was so as the behavioral cloud server was down for in that time frame. No evidence was found of a direct connection to VirusTotal or the rest of the servers.
Circumstantial Evidence
Then the malware expert Rubenking set some of the test files in a different folder and then initiated a VirusTotal check. Most of the antivirus engines detected these files as being malicious and others got almost unanimous recognition as being malware.
After doing that, the expert scanned the files in the folder using Tiranium and they were immediately recognized as malware. Even with no direct connection between VirusTotal and the computer, there was a chain of causality.
Is that OK or not?
The expert contacted specialists working in the antivirus industry to hear what they think about the situation. One of the specialists said that the antivirus companies can get in contract with VirusTotal in order to receive automatically the samples that others detected but their product missed. Even so, this did not describe the current situation.
The specialist at Tiranium confirmed the usage of VirusTotal. Saying that his company is analyzing the samples sent just as other companies in this sphere do. He also confirmed that the time for new samples analyzes does vary.
On the credits page of VirusTotal are enumerated the vendors who contribute to the integration of tools or products in VirusTotal. These vendors have signed an agreement, accepting the best practices policy. However, Tiranium is not one of these companies and it does not receive samples from VirusTotal.
Neil J. Rubenking realized that the messages sent by the user concerning Tiramium misusing VirusTotal are real. The expert has evidence that the application is connected directly to VirusTotal, which is an abuse.
Is Tiranium Potentially Unwanted?
Several other experts also express their concern about Tiranium. Some popular antivirus products have also detected Tiranium as an application that is potentially unwanted and needs to be removed. ESET, Kasperski and Fortinet, and als BrightCloud all identify the website of Tiranium as being malicious.
Why Tiranium is considered malicious?
Rubenking contacted again experts from Kaspersky to find out why Tiranium is considered malware. The experts made a research and confirmed that Tiranium website is using more than five different obfuscators for their code and have no digital signature. There was also malware like behavior spotted and traffic from the server with reference to VirusTotal, Anubis, and VirScan, or in other words reliance on third-party sources. Naturally, all this does not look legitimate.
The experts from BrightCloud could not give reason why was Tiranium accepted as risky, however they showed the IP address, which was shared with different phishing websites.
Neil J. Rubenking, being an expert, thinks that Tiranium has to improve its product in order to be transparent and to regain the specialists’ trust. The improvement should include fixing of the grammar and spelling errors, digital signature and integration with the Windows’s Action Center. In addition the company should refrain from third-party products and from servers that host malware.

