>> UPDATE: Zemana AntiMalware 2.30.2.37 is already here. This update comes with a re-written scanning engine & performance improvements. The premium version now allows the real time protection to be enabled whenever the user desires.
 The cloud anti malware programs have started gaining popularity these days thanks to the dynamic environment of the IT sector and more specifically its cyber security segment. Since a huge portion of the malware is replicating via newly updated exploit kits, JavaScript, and more importantly zero-day attacks, security updates become useless and the conventional software turns into a bunch of codes that are being updated only after a damage is done.
The cloud anti malware programs have started gaining popularity these days thanks to the dynamic environment of the IT sector and more specifically its cyber security segment. Since a huge portion of the malware is replicating via newly updated exploit kits, JavaScript, and more importantly zero-day attacks, security updates become useless and the conventional software turns into a bunch of codes that are being updated only after a damage is done.
Here comes Zemana’s AntiMalware program created to help users stop cyber threats before they even have the chance to be activated, using assistance from cloud databases and definitions. We have decided to review this program to see whether it’s capable of protecting users’ systems as promised. Stay tuned and read further:
App Profile
| Name | Zemana AntiMalware 2.21 |
| Type | Second Generation Security Solution |
| Developer | Zemana AntiMalware v2.21 |
| Official Website | Zemana.com |
| Operating System | 32-and 64-bit Windows 10, 8, 8.1, and 7 |
| License Price | $19.99 for 1 Year; $29.99 for 2 Years; $39.99 for 3 Years |
| Free Version | No, just a trial license for 15 days. |
| User Experience | Discuss Zemana Anti-Malware In Our Forum |

Zemana AntiMalware – Overview
Similar to other second-generation antimalware software, like Heimdal Pro, Zemana uses a common cloud-based infrastructure from which it feeds its data and definitions. To simplify that, imagine that a computer on the other side of the world is infected with Cerber Ransomware virus and its files are encrypted. As soon as this infection happens, this information is uploaded into Zemana’s cloud databases and therefore if your computer is attacked by ransomware virus, it should stop it before even it even enters your system. This type of fast response may significantly decrease the infection rate of a given virus and is a good objective for second generation antimalware programs.
On another note, according to “In-the-wild Ransomware Protection Comparative Analysis 2016 Q3” report conducted by MRG Effitas, Zemana AntiMalware has been rated first in ransomware protection against other popular antimalware products on the market such as BitDefender Anti-ransomware 1.0.12.1, Cryptoprevent 7.4.21.0, MalwareBytes Anti-Ransomware Beta 0.9.16.484, 1.0.0 and Hitmanpro Alert build 3.1.10 373. The reason behind is that Zemana works differently to the other generic ransomware detection tools as it uses its cloud reputation system to check for unknown binaries. See the full report.
Zemana AntiMalware – Technical Details
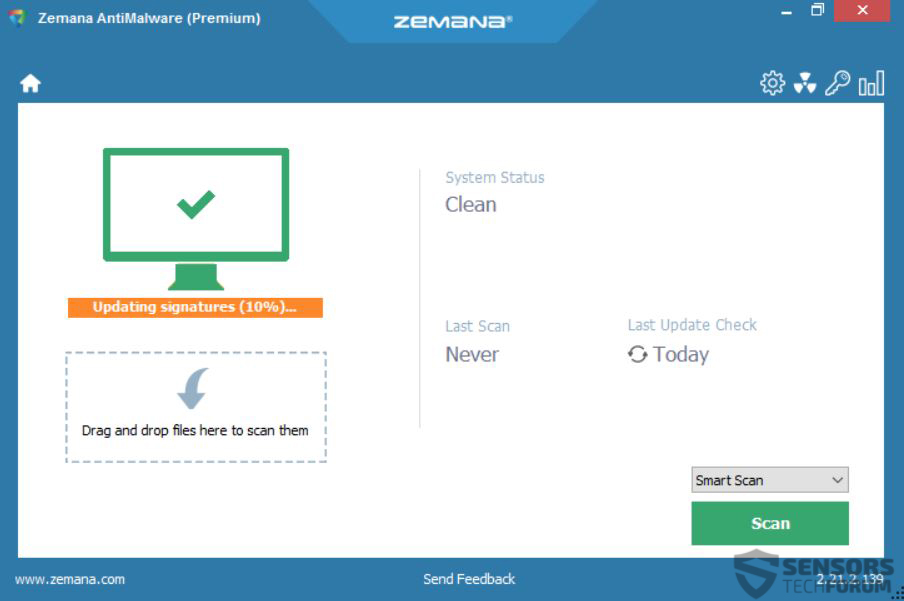
Similar to Zemana’s AntiLogger program, their AntiMalware software is also small in size, due to its cloud functionality – just around 5 MB. Also, the program has a very optimized and simple design which additionally contributes to the lightness:
Zemana AntiMalware is also optimized on how it receives updates, making its update process almost twice as fast than the average conventional antivirus software.
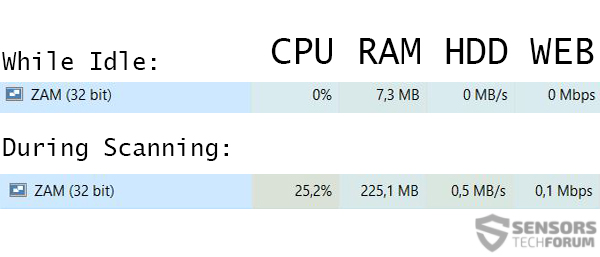
Another interesting detail is the lightness of this antivirus software while it is idle. This makes it a perfect program to have while performing heavy activities like video conversion, rendering, photo editing and heavy gaming activities:
During activation and scanning, the program takes up system resources from the computer, but this is for a good cause. It’s smart scanning feature took only 2 minutes on our test device to complete. In addition to this, the software also has the traditional settings for most anti-malware programs:
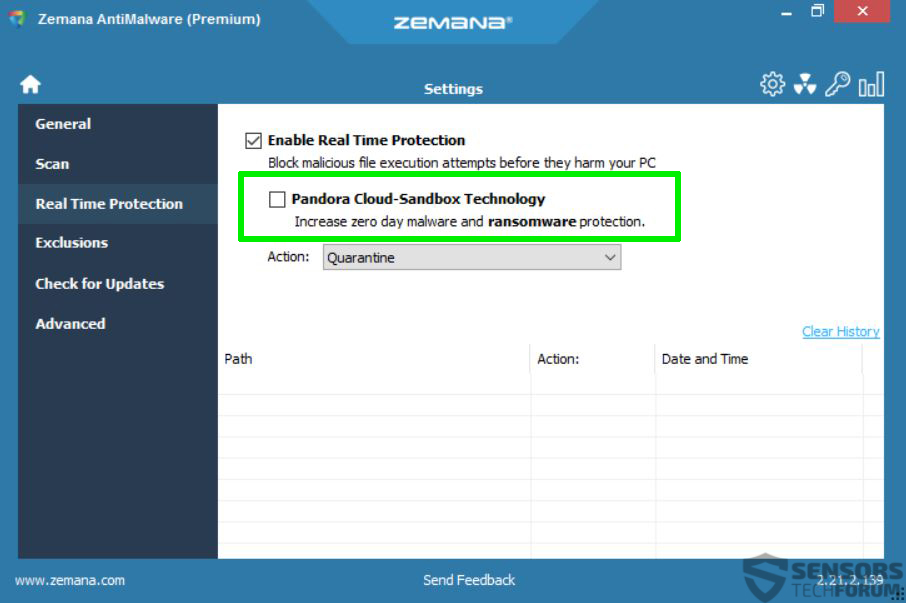
An important detail which caught our eye was Pandora’s Cloud-Sandbox technology which is a relevant protection against zero-day attacks and file-encryption malware.
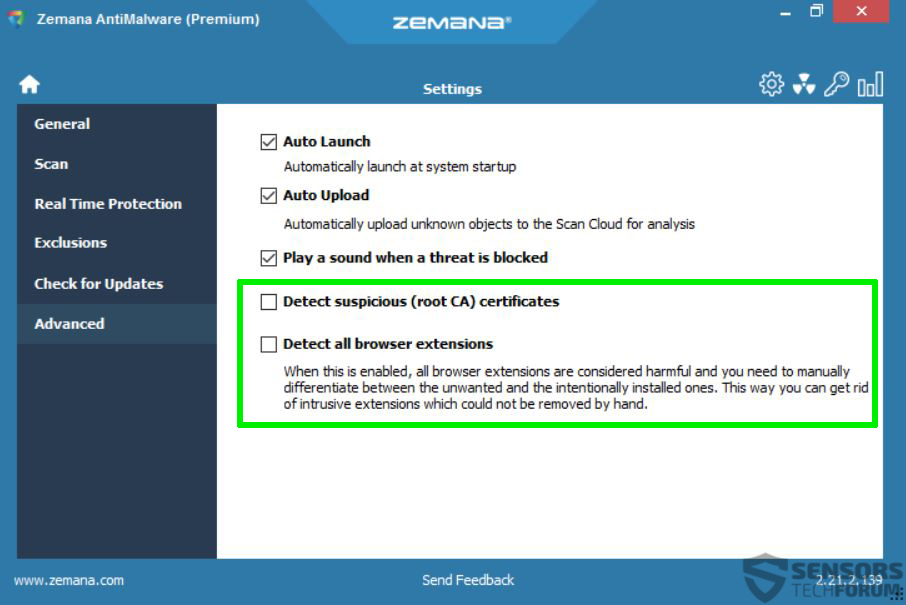
Also, we found some quite intriguing Advanced Settings in Zemana AntiMalware, such as detecting suspicious CA (certificates) and also scanning for various browser extensions which is a good method to catch Potentially Unwanted Programs (PUPs), which are installed via bundled downloads.
Furthermore, we also noticed that Zemana AntiMalware provides statistics of infections it collects and uploads to the cloud. Not only this, but it detected several portable applications without certificates, meaning Zemana AntiMalware is being very sensitive about suspicious programs as well.

What We Like
- Еxtremely light while idle.
- Fast during update and scanning process.
- Compatibility with almost any other security application.
- Very simple and user-oriented design of the interface.
- Тaps into the web browsers to look for browser extensions’ legitimacy.

What Is Missing
- There could have been more information about the cloud databases and the threats(like dangerous domains to avoid, for example) when they are detected.

Conclusion
 Zemana AntiMalware is shaping up to be a decent anti-malware tool which can compete with the best programs out there and can even surpass them in some aspects. We like the program because it is light, easy to use and at the same time has clearly shaped settings. Thus, we recommend purchasing this program and using it to protect your system.
Zemana AntiMalware is shaping up to be a decent anti-malware tool which can compete with the best programs out there and can even surpass them in some aspects. We like the program because it is light, easy to use and at the same time has clearly shaped settings. Thus, we recommend purchasing this program and using it to protect your system.