Remove Segurazo Antivirus
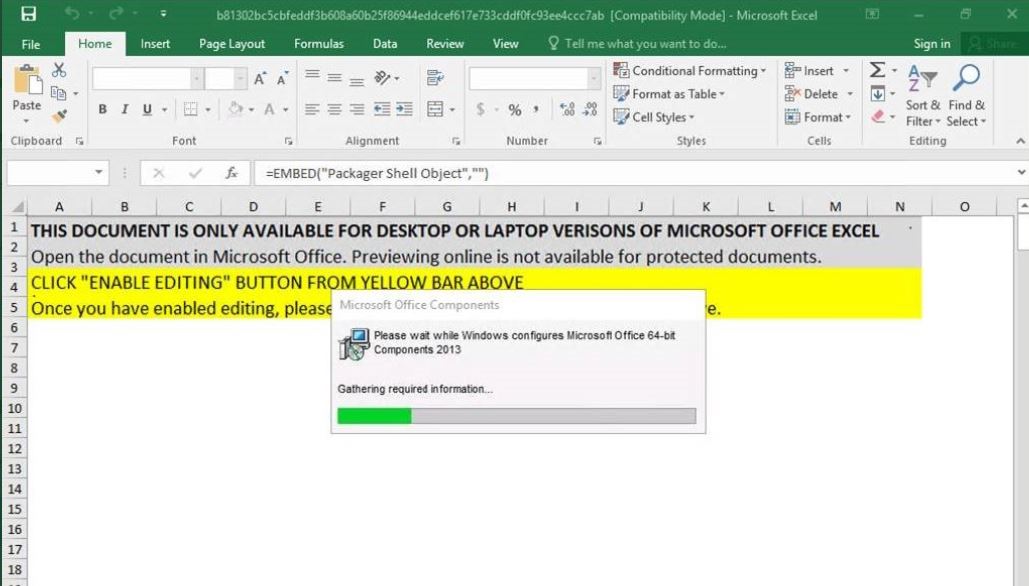
What Is Segurazo? What is Segurazo Antivirus? What does Segurazo Antivirus do? Is Segurazo Antivirus safe? Can you trust Segurazo Antivirus? Is Segurazo Antivirus a virus? The Segurazo Antivirus is a dangerous weapon used against computer users worldwide. It infects…