A worrisome trend has been spotted recently of continuous DDoS attacks. After the Lizard Squad attack against Destiny and Call of Duty servers, the researchers confirmed a high volume of attacks that happened in the first six months of 2014. The players that suffered the attack were booted from the servers right in the middle of their game, when an error message occurred. The access to the game was restricted for several hours and the players complained about it, threatening to ask for their money back.
The trend of these DDoS attacks is likely to go on for two main reasons – the access to DDoS service solutions and the widespread coverage of the attacks. That is why the website operators need to put up defenses against the DDoS attacks.
DDoS attack duration
These attacks are short in duration and are repeated on a frequent basis. Approximately 90 % of the attacks that have been detected during that period of time lasted for less than half an hour. According to the experts, the ongoing trend is for attacks towards latency-sensitive websites including hosting service, online gaming and eCommerice. That is why these websites should apply different security solutions with rapid response.
DDoS attack strength
The attacks are of high rate and high volume. For example the DDoS traffic volume increased with one third reaching more than 500Mbps. Five percent of the DDoS traffic volume even reached up to 4Gbps. In the first half of 2014 more than 50% of the DDoS attacks were above 0.2Mpps, which is a 16 % increase. At the same time more than 2% of DDoS attacks were started at 3.2Mpps rate and above.
DDoS attack methods
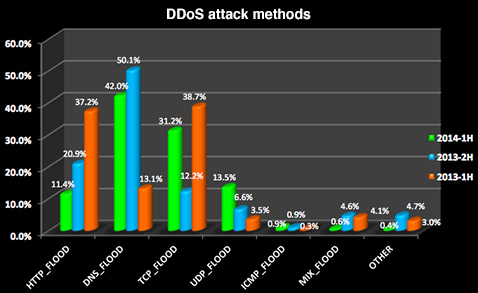
DDoS attacks are characterized with three main methods, namely DNS Flood, TCP Flood and HTTP Flood. The top three attack types form 85 % of all the attacks. The most popular method used are the DNS Flood attacks making 42 % of all the attacks noticed. The number of the HTTP Flood and the DNS Flood attacks has decreased, while at the same time the TCP Flood attacks grew substantially.
The ISPs attacks
The researchers found out that the number of the ISPs attacks has also increased by 87 %, the online gaming attacks increased by 60 % and the enterprises attacks increased by 100 %.
DDoS attacks of high-frequency
The DDoS attacks turned out to be one of the largest and longest, as well as the ones with highest frequency. The longest of all single attacks lasted for almost 12 days, while the largest single attack as far as packet-per-second was hit at 23 million pps volume.
At the same time, more than 40 % of the victims were targeted by the attack many times, and one in every 40 victims was hit repeatedly for more than 10 times. The highest frequency of attacks that has been noticed by one victim reached 68 separate DDoS attacks.
DDoS attack future
Recently, the founder of DDoS protection leader GigeNET, Ameen Pishdadi, said that the most popular attacks were DNS reflection and NTP. He further noted that in the beginning of 2014 NTP was strong and now that it has already been plugged in many servers, the frequency and the size of the attacks will eventually go down.
These results are according to the key observations and the statistical analysis, based on data from DDoS attacks actual incidents in the first six months of 2014. The data information was taken from Internet service providers and Internet hosting companies, global enterprises and regional telecom operators.

