A serious vulnerability in eBay’s sales platform has been just exposed by security researches at Check Point. The vulnerability enables attackers to bypass eBay’s code validation. As a result, attackers can control the code remotely and execute malicious JavaScript code on eBay users. The longer the vulnerability is left unpatched, the more likely it is for eBay users to become victims of phishing attacks and data theft.
More to Read: PayPal Fixed a Remote Code Execution Bug
Unfortunately, eBay has done nothing to fix this serious security flaw. Check Point contacted eBay on Dec 15, 2015. A couple of week later, eBay replied them that they didn’t plan to fix the flaw. It’s only natural to wonder why.
The eBay Vulnerability in Detail
The researcher who has discovered the flaw is Roman Zaikin. He disclosed that the flaw enables attackers to execute malicious code on various devices via a not-so-typical technique known as ‘JSF**’. The technique gives malicious actors the opportunity to use eBay as a phishing site and a malware distribution platform.
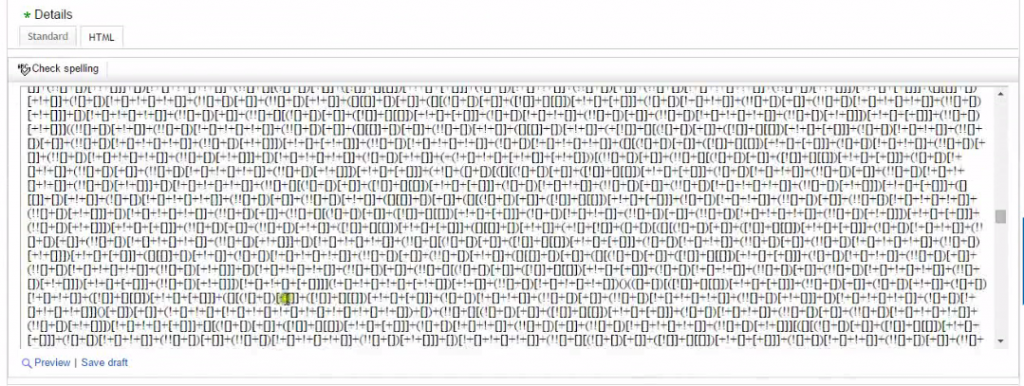
This is how the JSF** script looks like. Source: Check Point
To initiate an attack, the attacker only needs to create an online eBay store. There, he can simply post a malicious description of an item. Even though eBay is designed to prevent users from using scripts or iFrames, by using the JSF**k technique, the attackers is enabled to write a code that loads an additional JS code from his server. As a result, the attacker can insert JavaScript and control it remotely. He can also alter the JS code to create various payloads.
This is what Oded Vanunu, Security Research Group Manager at Check Point, has said:
The eBay attack flow provides cybercriminals with a very easy way to target users: sending a link to a very attractive product to execute the attack. The main threat is spreading malware and stealing private information. Another threat is that an attacker could have an alternate login option pop up via Gmail or Facebook and hijack the user’s account.
In response to the vulnerability disclosure, eBay has stated that they haven’t found any fraudulent activity based on the flaw. In addition, an eBay’s spokesperson has also said that various security filters have been implemented. No more details on eBay’s fixes were provided.


