If you’re one of those conscious users who acquaint themselves with the software before they install it onto their computers, Microsoft security updates included, then this article is for you. When you pay attention to the small print, and in the case of Windows updates – knowledge base (KB) descriptions, you will definitely come across:
- Elevation of privilege
- Remote code execution
- Security feature bypass
- Information disclosure
Those are the issues that Microsoft security bulletins regularly address on Patch Tuesdays, and accordingly fix. However, elevation of privilege and remote code execution are sensibly preferred by attackers. If your knowledge in the Windows operating system (or any OS) is above average, you are most definitely acquainted with these security terms and their definitions. And you can navigate away from this page (but first you can share it with the lesser-educated).
In case you go through the bulletins on a regular basis but feel like your knowledge is not sufficient enough, continue reading.
What Is Elevation of Privilege?
As explained by Microsoft, elevation of privilege happens whenever an attacker is given authorization permissions beyond those initially granted. For instance, this attack happens when an attacker with a privilege set of read only permissions somehow elevates the set to include read and write.
Elevation of privilege is also known as vertical privilege escalation. This is when a lower privilege user (or application) suddenly has access to functions or content meant for higher privilege users or apps.
In nearly every monthly security bulletin released by Microsoft, there are updates addressing elevation of privilege.
In the language of security experts, how is an elevation of privilege attack described?
This attack is a type of network invasion that takes advantage of programming errors or design flaws (vulnerabilities, or CVEs) to authorize the attacker with elevated access to the network and its associated data and applications.
We mentioned vertical privilege escalation. What about horizontal?
Like we said, vertical privilege escalation happens when the attacker grants himself higher privileges. This type of network intrusion is usually carried out by performing kernel-level operations that enable the attacker to run unauthorized code.
Horizontal privilege escalation, on the other hand, demands the attacker to use the same level of privileges he already has, while undertaking the identity of another user with similar privileges. For instance, horizontal privilege escalation is when an attacker is obtaining access to another person’s online banking account.
A recent example of a dangerous elevation-of-privilege security vulnerability in Windows 10 is the so-called HiveNightmare, assigned the CVE-2021-36934 identifier. According to Microsoft’s official description of the issue, it is an elevation of privilege flaw caused by an “overly permissive Access Control Lists (ACLs) on multiple system files, including the SAM (Security Accounts Manager) database.
Once the vulnerability is exploited successfully, the attacker could run arbitrary code with SYSTEM privileges. Once this is achieved, the attacker could install programs, view, change, or delete data, or create new accounts with full user rights.
What Is Remote Code Execution (RCE)?
Shortly said, the ability to trigger arbitrary code execution from one computer on another (mostly via the Internet) is widely known as remote code execution. Again, what enable attackers to execute malicious code and gain control over the compromised system is (surprise, surprise) vulnerabilities. Once the system is under the attackers’ control, they can elevate their privileges. That being said, the best way to prevent remote code execution attacks is by never allowing vulnerabilities to be exploited. Unfortunately, remote code execution flaws are very often favored by attackers, and that is what makes keeping your operating system up-to-date crucial.
Sadly, there are many cases of vulnerabilities being exploited in the wild before the adequate release of a patch. Because of their severe character, zero-day vulnerabilities are often rated critical. Windows is also prone to zero-day exploits, such as CVE-2015-2545 from 2015, found in Microsoft Office 2007 SP3, 2010 SP2, 2013 SP1, and 2013 RT SP1. Luckily, Microsoft patched this vulnerability soon after it was disclosed.
Two example for remote code execution vulnerabilities are CVE-2020-1425 and CVE-2020-1457 in several Windows 10 and Windows Server versions. Both flaws were reported to Microsoft by vulnerabilities analysis manager Abdul-Aziz Hariri via Trend Micro’s Zero Day Initiative.
The critical CVE-2020-1425 vulnerability is described as a remote code execution vulnerability which exists in the way that Microsoft Windows Codecs Library handles objects in memory. An attacker who successfully exploited this vulnerability could obtain information to further compromise the user’s system, Microsoft says in the official advisory. The vulnerability can be exploited under the condition of a program processing a specially crafted image file.
The CVE-2020-1457 vulnerability is also related to remote code execution, and it also exists in the way that Microsoft Windows Codecs Library handles objects in memory. The exploitation of the vulnerability is similar to the other flaw, as it also requires that a program process a specially crafted image file.
What Is Security Feature Bypass?
This type of attack can happen on a local level. Local attackers can exploit such a flaw to bypass specified security restrictions and perform malicious activities. Such vulnerability in Windows Kernel was disclosed by Microsoft on May 12, 2015. The update that was released to patch it is KB 3050514. In Microsoft’s language, “the vulnerability could allow security feature bypass if an attacker logs on to an affected system and runs a specially crafted application”.
To understand security feature bypass, let’s take another look at some older vulnerabilities patched on March 8, 2016.
This specific security update for the .NET Framework addressed security feature bypass. The security feature bypass was found in a .NET Framework component that did not correctly validate certain elements of a signed XML document.
What Is Information Disclosure?
Information disclosure is a term used by Microsoft to describe vulnerabilities that intentionally or unintentionally disclose information to an attacker that is not authorized to have access to it. However, a more relevant way to describe such a threat is information exposure.
Even though information disclosure is frequently used in vulnerability databases, the word ‘disclosure’ isn’t always associated with security issues. The disclosed information can be sensitive to the particular software’s functionalities, or can reveal details about the software’s environment. If such information is leaked, it could be useful to an attacker in many attack scenarios.
No matter what you call it – information disclosure or information exposure, such flaws can be both resultant and primary. A resultant information disclosure can happen via a PHP script error that reveals the full path of an application. A primary ID may happen due to timing discrepancies in cryptography.
The severity of an ID flaw depends on the type of information that is made available to attackers.
An example of an ID flaw in Windows is the vulnerability from October 15, 2014. The flaw was found in SSL 3.0 and was patched with the KB 309008 update.
Threat Modeling against Vulnerabilities
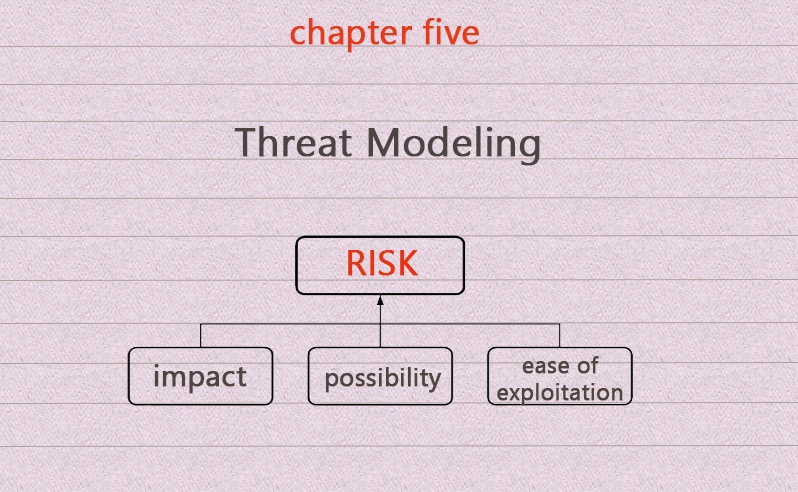
According to the Open Web Application Security Project, threat modeling is one way to prevent vulnerability exposure in any application:
Threat modeling is an approach for analyzing the security of an application. It is a structured approach that enables you to identify, quantify, and address the security risks associated with an application. Threat modeling is not an approach to reviewing code, but it does complement the security code review process. The inclusion of threat modeling in the SDL (software development lifecycle) can help to ensure that applications are being developed with security built-in from the very beginning.
Microsoft has developed several tools that ease the SDL process and help prevent security flaws from being exploited:
- Attack Surface Analyzer 1.0
- Microsoft Threat Modeling Tool 2016
- MiniFuzz basic file fuzzing tool
- Regular expression file fuzzing tool
For more information, visit Microsoft’s official page.
One question remains, though…
Why Does Windows Have So Many Vulnerabilities?
There is one easy and quite obvious answer: Windows is probably the most widely used operating system. Being popular has its downside. Even the believed-to-be-invincible Mac has become prone to ransomware attacks.
Overall, Microsoft continues to release software that has lots of security flaws, which have not been predicted by the developers. The KB patches are full of security fixes that address the unforeseen vulnerabilities (described in this article). An example of a bad security practice is Windows XP’s autorun feature that would run anything within the autorun.ini file from external drives. Of course, newer versions of Windows are continuously improved.
And let’s not forget that attacks happen because there are too many vulnerable (not regularly patched, not supported by MS anymore, or worse, pirated) versions of Windows out in the wild. That, and the fact that many people, including employees in various business sectors, know little about threat prevention and lack sufficient knowledge in the current threat landscape.
So, in a nutshell, employ a powerful anti-malware, an external firewall, spam filters, and keep all of your software up-to-date at all times. And pray you don’t become a victim to vulnerability exploits.


