 The new year has started with a new strain of enterprise ransomware, and now a cryptocurrency malware. Discovered in December, ElectroRAT is a “wide-ranging operation targeting cryptocurrency users” on all major operating systems (Windows, macOS, and Linux).
The new year has started with a new strain of enterprise ransomware, and now a cryptocurrency malware. Discovered in December, ElectroRAT is a “wide-ranging operation targeting cryptocurrency users” on all major operating systems (Windows, macOS, and Linux).
The malicious operation is quite elaborate in its mechanism, consisting of a marketing campaign, custom applications related to cryptocurrencies, and an entirely new Remote Access Tool (RAT).
The extensiveness of the ElectroRAT operation
According to Intezer researchers, the campaign consists of the following components:
- Domain registrations;
- Websites;
- Trojanized applications;
- Fake social media accounts;
- Previously undetected RAT.
“It is rather common to see various information stealers trying to collect private keys to access victims’ wallets. However, it is rare to see tools written from scratch and used to target multiple operating systems for these purposes,” the researchers shared in their report.
How has the ElectroRAT campaign tricked its victims?
The attackers behind the operation have been luring cryptocurrency users to download trojanized apps. For this purpose, online forums and social media platforms were used. The researchers believe that thousands of users fell victim to the approach, judging by the number of unique visitors to the Pastebin pages locating the command-and-control servers.
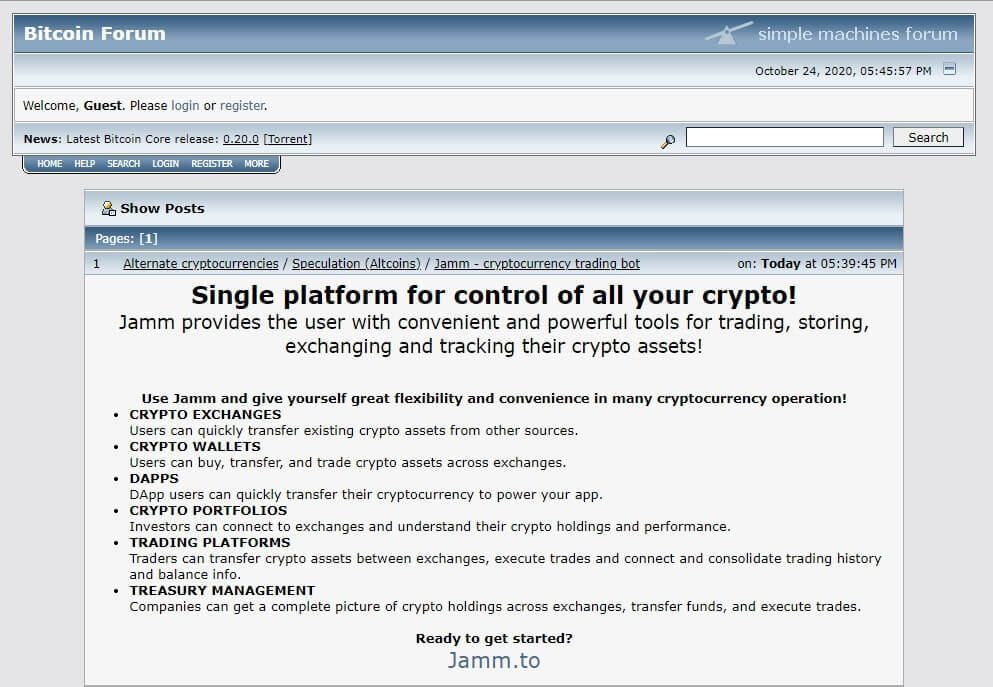
The attackers created three separate trojanized apps related to cryptocurrency, each targeting macOS, Windows, and Linux users. Moreover, the binaries were hosted on websites explicitly designed for the operation. Two of the applications, Jamm, and eTrade, are related to cryptocurrency trade management, and DaoPoker is a crypto poker app.
To increase the success rate, the attackers promoted them on crypto- and blockchain-specific
forums such as BitcoinTalk and SteemCoinPan. The promotional posts were published by fake users, luring potential victims to browser the apps’ dedicated web pages:
Successful interaction leads to downloading malware rather than the promised cryptocurrency app.
Furthermore, the attackers also created Twitter and Telegram profiles for the DaoPoker app and paid a social media influencer with over 25 thousand followers to advertise the eTrade app.
In technical terms, the threat actors developed the three applications via Electron, a platform for application building. ElectroRAT is embedded in all three apps. Once the user is tricked into running the app, “an innocent GUI” opens while the malware runs silently in the background as “mdworker.”
In Conclusion
Seeing such a multi-platform RAT targeting cryptocurrency users is relatively uncommon. The malware is “extremely intrusive,” capable of keylogging, taking screenshots, uploading and downloading files, and executing commands on the victim’s console. These capabilities are present in all three variants.
Since the detection rate of ElectroRAT on VirusTotal is still very low, cryptocurrency users should be extremely vigilant while visiting their favorite forums.
A previous example of a malware targeting cryptocurrency wallets is the InnfiRAT. Discovered in 2019, the malware included a sophisticated cryptocurrency theft module. It was written using the .NET framework, and was targeting Windows systems in particular.