A Facebook bug was just discovered by security researcher and bug hunter Tommy DeVoss who got awarded $5,000. The flaw allowed him to view the private email address of any user of the social media. Moreover, the hack made it possible for him to gather as many email addresses as possible, regardless of how private users thought they were.
The bug hunter came across the vulnerability on Thanksgiving and reported it to the Facebook bug bounty program. It took the company several weeks in order to verify the flaw and pay the researcher the award of $5,000.
Related: Facebook Messenger App and Chat Vulnerable to Simple HTML Exploits
The Facebook Bug Explained
The bug stemmed from the user-generated Facebook Groups feature which enables users to create affinity groups on the platform. The researcher discovered that being an administrator of a group he could invite any Facebook member to have Admin Roles via Facebook’s activities such as edit post or add new members.
Facebook handled the invitations and they were sent to the invited user’s Messages Inbox and to the user’s email address tied to the account. What DeVoss discovered was that he could gain access to any user’s email address no matter if he was friends with them or not. The privacy settings of the accounts weren’t an obstacle.
DeVoss further found that upon cancelling pending invitations of the users invited to be admins a glitch happened. “While Facebook waits for the confirmation, the user is forwarded to a Page Roles tab that includes a button to cancel the request,” he explained.
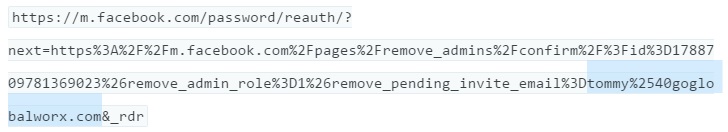
Next on his list was switching to Facebook’s mobile view of the Page Roles tab where he could view the full email address of anyone he wished to cancel from becoming an admin of Facebook group. He noticed that by clicking to cancel the admin invite on the mobile page he was redirected to a page with the email address in the URL. He only had to pluck the plaintext version of the otherwise private email address directly from the URL. Here’s how this looks like:
What’s the Impact of the Facebook Bug?
The impact of the vulnerability may vary. To begin with, collecting email addresses like that contradicts Facebook’s privacy policy and could lead to targeted phishing attacks and various malicious activities.
Facebook confirmed the flaw hasn’t been leveraged in the wild. A fix has already been implemented to prevent the issue from being exploited in the future.