Image Source: https://blog.checkpoint.com
Facebook is far from invincible. In fact, it may be way too easy for attackers to exploit vulnerabilities, especially when it comes to its standard chat function and its separate Messenger app. This is exactly what CheckPoint researcher Roman Zaikin recently discovered. The security firm contacted Facebook immediately, and the company was able to patch the flaws shortly after.
If exploited, the flaws in Facebook’s chat and Messenger app could enable an attacker to take over any sent message, modify its contents, spread malware and implement automation techniques to baffle security mechanisms.
What Does an Attacker Need to Do to Exploit the Facebook Chat Vulnerabilities?
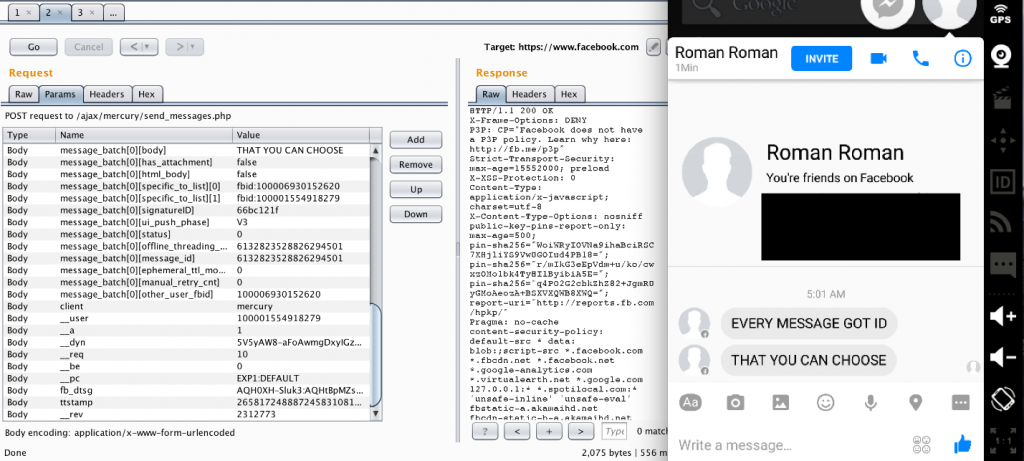
All a malicious actor needs to do is identify the unique ID for the targeted sent message (“message_id”) by sending a request to the specific link. This is the needed request:
www.facebook.com/ajax/mercury/thread_info.php
For this process to take place, only basic HTML knowledge is required, and a browser debug tool. Such tools are freely available on all browsers. The worst part of the exploit is that it can happen without the user’s knowledge or suspicion of any fraudulent activity.
This is a resume of the malicious activities that can be performed upon successful exploit:
- Attackers can manipulate chat history as part of fraud campaigns. The history of a conversation can be changed, and this can be used in further manipulations.
- Attackers can tamper important information and this can have legal consequences. Facebook chats can be admitted as evidence in legal investigations. For example, an innocent person can be easily incriminated.
- Attackers can use the vulnerability to distribute malware across Facebook users. Legitimate links can be replaced with malicious ones, and the user can be tricked to open them.
Why Would Attackers Target Facebook Chat and Messenger App?
It’s simple – Facebook is used by millions of users. At the beginning of 2016, the company announced that it had 1.65 billion monthly active users. The Messenger app alone had more than 800 million monthly members.
As already mentioned, the vulnerability has already been fixed.


