Apart from detecting and disposing malicious attacks, security researchers and analysts have another important job. To predict the future.
McAfee Labs have just released a prediction report that looks 5 years ahead and outlines the changes in the threat landscape by 2020. What are the types of attacks McAfee researchers predict to prevail in the next several years. The report emphasizes on 14 crucial sectors of cyber crime and its prevention:
Hardware, Ransomware, Vulnerabilities, Payment systems, Attacks through employee systems, Cloud services, Wearables, Automobiles, Warehouses of stolen data, Integrity, Cyber espionage, Hacktivism, Critical infrastructure, Sharing threat intelligence.
Let’s have a look at what concerns us the most, being malware researchers ourselves.
Hardware Attacks
Hardware Attacks are immensely magnified by the emergence of commercial attack tools. In 2015, McAfee researchers discovered the first commercial UEFI rootkit, including source code.The rootkit’s authors – the infamous – Hacking Team, offer a platform called Remote Control. Parts of the tool have already been adapted for attacks observed in the wild. Providing source code has made things very easy for malicious coders to customize the threat for their own purposes.
What experts at the Labs believe is that copycat code and similar tools will be released in 2016.
Ransomware Attacks
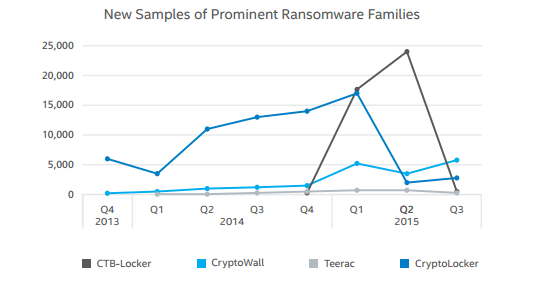
Security researchers (us included) all agree that ransomware will continue to be a prevalent threat. We have already seen ransomware become a service available to whomever is interested to participate in its multiple affiliate programs. Besides the new versions of the well-known ransomware such as CryptoWall and CTB-Locker, McAfee believes new families will emerge in the next couple of years or so. Ransomware will continue to target victims for quick cash. However, attacks on governments and financial institutions are expected to grow notably.
Jump to these articles for more intel on ransomware:
Mobile Ransomware in 2015
Top 3 Ransomware Families of 2015. Cryptowall
Vulnerabilities
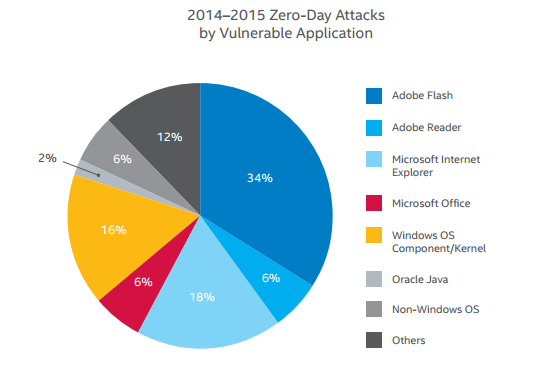
What experts expect to happen is vulnerabilities being exploited in areas beyond Windows – embedded systems, the Internet of Things, and infrastructure software will be the new targets for advanced threats and zero-day attacks. To be more precise, variants of Unix, popular smartphone platforms, IoT specific systems like Tizen and Project Brillo, and libraries (Glibc, OpenSSL, etc.). The report also emphasizes on the fact that foundation libraries and components, especially open-source framework tools, are not as secure as they should be.
Attacks through Employee Systems
Attackers will continue to think of new ways to steal companies’ data. Researchers expect attacks on employees to increases while they are at home or travelling. When attackers are continuously blocked when attempting to breach the corporate data center, it’s only logical they will start targeting the insecure home systems of the employees. Respectively, in 2016 and beyond experts expect to see organizations think ahead and provide advanced security technology for employees to install on their personal systems.
Have a look at the whole McAfee report.
More on the subject:
Cyber Crime Predictions for 2016