Five security vulnerabilities, called JekyllBot:5 (CVE-2022-1066, CVE-2022-26423, CVE-2022-1070, CVE-2022-27494, and CVE-2022-1059) were fixed in Aethon TUG smart autonomous mobile robots. Fortunately, the vulnerabilities haven’t been exploited in the wild.
JekyllBot:5 Vulnerabilities in Aethon TUG Mobile Robots
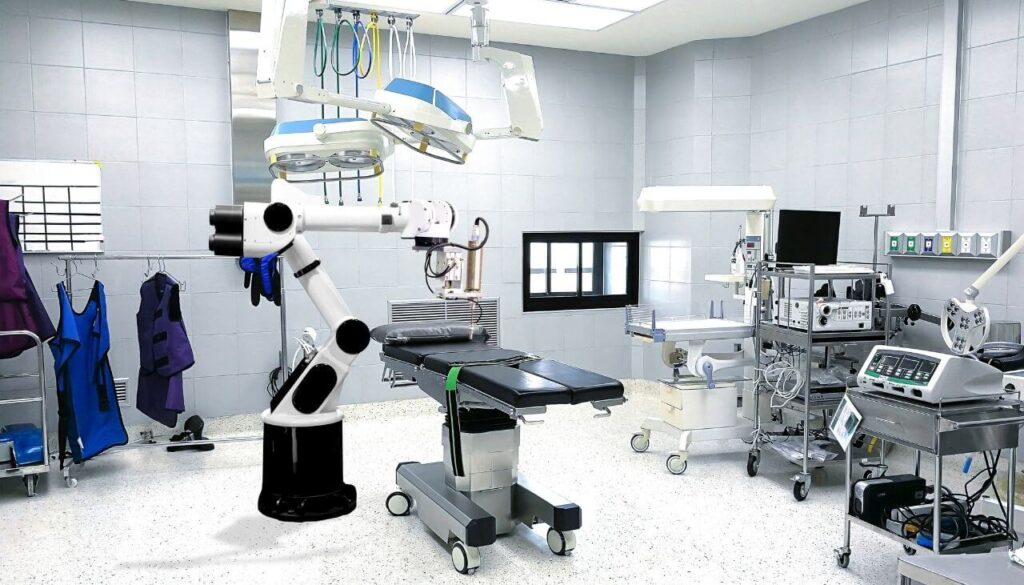
The mobile robots are widely used in hospitals to deliver medicines and hospital maintenance supplies. They are also capable of executing simple manual labor tasks. The robots, however, were found vulnerable to a series of issues, including remote control, which could enable threat actors to access user credentials and medical records, among other malicious tasks. Any vulnerabilities in hospital robots are threatening to medical patients, equipment and staff, as they deal with lots of sensitive details, and require freedom of movement to carry out their jobs.
The JekyllBot:5 vulnerabilities could allow attackers to perform any of the following malicious activities:
- See real-time footage via the robot’s camera;
- Access patient medical records;
- Take videos and pictures of patients and hospital interior;
- Interfere with patient care and obstruct hospital elevators and door-locking systems;
- Take control of the robot and crash it;
- Disrupt regular maintenance tasks;
- Disrupt (or steal) robot delivery of patient medication;
- Hijack legitimate administrative user sessions in the robots’ online portal to inject malware through their browser, and carry out further cyberattacks on IT and security team members at healthcare facilities.
JekyllBot: 5 Vulnerabilities: Technical Description (CVE-2022-1066, CVE-2022-26423, CVE-2022-1070, CVE-2022-27494, and CVE-2022-1059)
CVE-2022-1066 has been rated 8.2 out of 10 on the CVSS scale. The vulnerability interferes with the software’s ability to perform an authorization check. As a result, an unauthenticated attacker can arbitrarily add new users with administrative privileges and delete or modify existing users.
CVE-2022-26423, also rated 8.2 out of 10 on the CVSS scale, could enable an unauthenticated threat actor to freely access hashed user credentials.
CVE-2022-1070 has a highly critical rating of 9.8 out of 10 on the CVSS scale. The flaw allows an unauthenticated attacker to connect to the TUG Home Base Server websocket and take control of the vulnerable robots.
CVE-2022-27494, with a rating of 7.6, is an XSS vulnerability. According to the official description, “the “Reports” tab of the Fleet Management Console is vulnerable to stored cross-site scripting (XSS) attacks when creating or editing new reports.”
Lastly, CVE-2022-1059, again with a 7.6 rating, is a reflected XSS vulnerability. More specifically, the load tab of the Fleet Management Console is prone to reflected XSS attacks.
More technical details are available in the report compiled by Cynerio researchers.
More about Aethon TUG Robots
The Aethon company was founded in 2001. It released its first TUG robot on the market in 2004. One of the robots’ principal use cases is for hospitals, as they are programmed to handle common healthcare-related tasks such as transporting medicine, cleaning floors, collecting meal trays, among other similar tasks.
Other Recently Revealed Medical Vulnerabilities
In March 2022, the so-called Access:7 vulnerabilities were reported, affecting PTC’s Axeda agent used by various vendors in a range of industries, mostly healthcare and financial. Access:7 flaws could enable remote code execution and full device takeover. They could also allow hackers to access sensitive data or change the configurations of exposed devices.


