Spoilers alert!
Have you been impatiently looking forward to Mr. Robot’s second season? Do you always have questions about the hacks that take place during the show? Are you often pausing to have a closer look at what’s written on that PC screen? Stay tuned! We’re also hooked on Mr. Robot and we’ll be looking for answers ourselves on an episode-basis.
Jump to Mr. Robot’s the Phreaker and the Hot Wallet (Episode Three, Kernel Panic)
Before we begin, let’s pay some attention to the titles of Mr. Robot’s episodes, and respectively to the events that took place in the first season.
First, Let’s Roll Back to Mr Robot’s Season 1!
Because of Mr. Robot’s story duality, everything about the series deserves a second look. The rule applies to the episodes’ titles which always carry more meanings. One meaning is usually about a hack- or tech-related term that is being exploited throughout the series, and the other typically is involved with a character struggle.
Let’s take first season’s eps1.3_da3m0ns.mp4. On one hand, it obviously refers to the computer program Daemon, and on the other, we have the true color of Elliot’s demons. Or the demons of Evil corp(orations)? Everything is open to interpretation, and that’s what’s great about Mr. Robot – the abundance of dubiosity that imperceptibly directs us through the story.
Here’s a list of season 1’s episodes:
- eps1.0_hellofriend.mov
We are introduced to Elliot Alderson; “Hello World!” is the standard first message displayed by a new programmer; it’s also a “sanity test” used to make sure a language’s compiler, development and run-time environment are correctly installed. We are yet to be introduced to the insanity of our beloved character Elliot.
- eps1.1_ones-and-zer0es.mpeg
It’s a binary code, ones and zeros; we see Elliot facing a life-changing (binary) decision; “Are you a one or a zero? Are you a yes or a no?” Mr. Robot asks Elliot. “Life’s not that binary,” he replies.
- eps1.2_d3bug.mkv
It’s about the multiple senses of debugging. Elliot is attempting to live a bug-free life, trying to free himself from the grasp of fsociety. “Most coders think debugging software is about fixing a mistake, but that’s bullshit. Debugging’s actually all about finding the bug, about understanding why the bug was there to begin with, about knowing that its existence was no accident,” Elliot explains.
- eps1.3_da3m0ns.mp4
In addition to the explanation above a daemon refers to anything that runs in the background of an operating system without the user having control over it. Mr. Robot has quite the daemons, does he not?
- eps1.4_3xpl0its.wmv
An exploit is basically a hack that leverages vulnerabilities. In this episode (and throughout the whole series) we see that “people always make the best exploits,” in Elliot’s own words. He takes advantage of a low-level employee to gain access to Steel Mountain security facility.
- eps1.5_br4ve-trave1er.asf
This one is an exception as it has nothing to do with hacking. Shayla, Elliot’s alleged girlfriend, is kidnapped.
- eps1.6_v1ew-s0urce.flv
View Source is a command that can be executed by almost any browser. Also, in this episode Elliot is telling the story of his first attempts in coding, when all he had to do was click View Source and paste the code. Overall, the episode is about studying your sources.
- eps1.7_wh1ter0se.m4v
Elliot meets White Rose. Obviously, the episode is named after the infamous hacker who is an epitome of the hacker cult.
- eps1.8_m1rr0r1ng.qt
Mirroring has many applications. It can refer to a real-time copy of something, like disk mirroring, which refers to the replication of disk volumes onto other physical drives simultaneously. Also, we have Elliot who finally realizes that he has been Mr. Robot all along the journey.
- eps1.9_zer0-day.avi
The title refers to a zero day vulnerability. Also, everybody is running out of time. Zero time.
Perhaps you’ve noticed that the episodes are titled like computer programs. Whenever a new piece of software is launched, it’s titled version 1.0, its next release being 1.1. This is how Mr. Robot’s second episode becomes eps1.1, instead of S1E2 which is the typical way to number episodes.
Season 2 starts off with a two-part chapter: eps2.0_unm4sk-pt1.tc and eps2.0_unm4sk-pt2.tc. We have Elliot who is trying to keep himself as sane (and unmasked) as possible in a repetitive everyday pattern he has built for himself (it’s clear he’s trying to keep Mr. Robot “unplugged”). We see him keeping a journal of all his daily routines, trying to keep everything under control, including his reluctant talks with Mr. Robot, who is trying to lure him back in the exploit void. We see Elliot becoming more persistent – Mr. Robot is repeatedly shooting him in the head (metaphorically, although we see real blood being spilled), but Elliot is getting stronger and is no longer intimidated. However, will his strength endure?
Then we have fsociety’s mask this time to be worn by an unexpected party in a ritual-like scene of setting a million-dollar-pile on fire, and “our infinite loop of insanity” of camouflage living. And, of course, let’s not forget unmasking in the sense of hacking people! This episode’s hack on a person is different than the hacks on people Elliot carried out in the first season.
(And despite the controversial relationship with his frustrated female psychiatrist, we see him back at her office. I am curious to know where the writers are taking this story line.)
The hacks seen in the two-part beginning of season 2 are pretty much inspired by real life hacks. If you’re following infosec news, there is no way you could have missed the multiple ransomware attacks (on users, businesses, governments, hospitals) and the increasing number of APTs (advanced persistent threats) deployed for high-level cyber espionage. The potential vulnerability of the Internet of Things is another subject explored at the start line of season 2.
There’s definitely something phishy going on in every minute of every day on any device, and Mr. Robot is just a sheer reminder of that parallel reality.
So, What type of Hacks Did We See at the Start of Mr. Robot’s Season 2?
The fociety IoT Smart Home Hack
Susan Jacobs is an important member of E Corp’s General Counsel and is nicknamed “The executioner”. She’s “malicious” and she’s getting hacked! At least her smart home is. The attack starts with her smartwatch’s fitness app being bugged, and then continues in her dreamy high-tech home. Then her whole house goes completely out of control, and after the pointless phone call to the vendor, she’s left with no choice but to leave. This is when fsociety, now headed by Darlene, enters the premises.
One question that pops to mind is whether the smart home was realistic. Quite conveniently, it seemed somehow exaggerated. On one hand we see a perfect depiction of a smart home where all devices run smoothly and simultaneously without a glitch (at least they were prior to the attack). But on the other, this perfect home was way too easy to hack! Perhaps the vendor wasn’t too interested in applying patches? Oh, and how come Susan didn’t suspect for a second that she was being hacked?
Nonetheless, the hackability of IoT devices is evident. This smart home hack may just serve as a warning as to what is coming in the future if vendors don’t take their products’ security seriously enough.
And a reminder of what has already gone wrong. Like when Kashmir Hill (Forbes) gained control over a stranger’s house in 2013. This is what Hill wrote back then:
Googling a very simple phrase led me to a list of “smart homes” that had done something rather stupid. The homes all have an automation system from Insteon that allows remote control of their lights, hot tubs, fans, televisions, water pumps, garage doors, cameras, and other devices, so that their owners can turn these things on and off with a smartphone app or via the Web. The dumb thing? Their systems had been made crawl-able by search engines – meaning they show up in search results — and due to Insteon not requiring user names and passwords by default in a now-discontinued product, I was able to click on the links, giving me the ability to turn these people’s homes into haunted houses, energy-consumption nightmares, or even robbery targets. Opening a garage door could make a house ripe for actual physical intrusion.
Dangerously amusing, isn’t it? Overall, despite the picturesqueness of the smart home hack, it seemed a bit over the top.
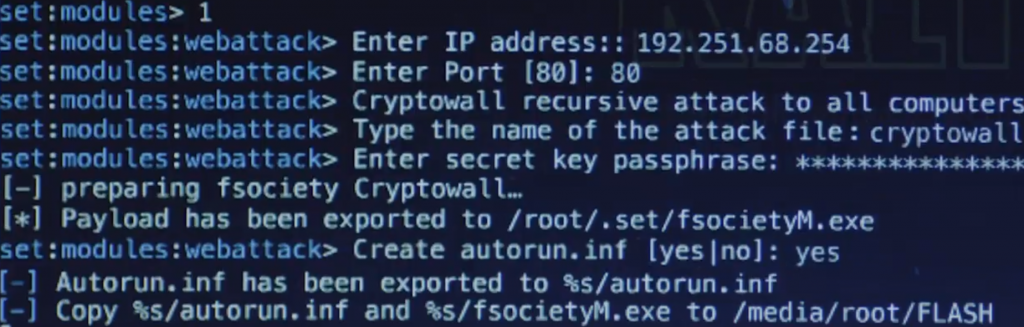
fsociety CryptoWall Ransomware/ Worm Attack
We have been writing about ransomware on a daily basis. CryptoWall has become the embodiment of ransomware, along with CryptoLocker, Locky, Cerber. Ransomware, also referred to as a crypto virus, is the malicious threat that holds your files hostage until a ransom, typically in Bitcoin or another crypto currency is being delivered. fsociety’s CryptoWall is a bit different as it doesn’t require a payment in Bitcoins and the demanded amount is skyrocket high – $5.9 million. Also, it should be delivered in person, at a public place, not via a Tor address. It’s also quite obvious that fsociety is not interested in money. A bunch of money ends up burned. The purpose of fsociety’s malicious payloads lies within the realms of pure moralism. What is bad should be punished. What is bad should be revoked. Evil Corp.
Was the social engineering toolkit Darlene used real? Such a toolkit can be bought online, no need to browse the Dark Web, because it’s aimed for pentesters. Pentesters are hired by companies to test their systems and check whether they are penetrable. If pentesters succeed at penetrating a system, they inform the company so that it can fix the vulnerability.
How was the ransomware attack carried out? We’re not given the details but it’s somehow implied that Mobley had something to do with it. He appears to have landed a part time job in the IT department of an E Corp branch. It’s easy to assume that he planted a worm there. What’s left uncovered is what kind of data the ransomware encrypted. Whatever it was, it had to be valuable, more valuable than nearly $6 million.
How did all PC screens at Bank of E end up with a ransomware desktop? This can be done by very capable hackers. Such cases were registered by security researchers some time ago. In two published cases, believed to be conducted by Iran (“Anti-WMD Team”) and North Korea (“#GOP Hackers”), many employee computers were all compromised to display a scary message, similarly to what happened in Mr. Robot.
Was the fsociety ransomware attack realistic? Well, it depends. Like we said, we’re not given many details. One question that needs to be asked is how partitioned the local network that Mobley had access to was. Was there enough data accessible from that local system? Nonetheless, fsociety is the hacking team that put the worst corporation to its knees, so their professionalism and handiness is somehow implied.
Apart from the hacks, many questions that we were impatiently awaiting to be addressed in the first episode of season 2 remained unanswered. Like, where the hell is Tyrell Wellick?
References
https://www.hopesandfears.com/
https://www.forbes.com/
https://blog.avast.com/
https://www.theverge.com/








Re: “Was the fsociety ransomware attack realistic? Well, it depends. Like we said, we’re not given many details” — In particular, we’re not given details on how the ransomware did spread, only how it was introduced at first (ie, the initial vector of infection: an USB key handed to the “IT guy” by Darlene).
To spread like this, to that amount of computers at once, there would be the need for a worm exploiting flaws in said computers, carrying the ransomware as a payload.
Yes, you are correct! It’s also mentioned in the article (It’s easy to assume that he
planted a worm there.)
What do you think will happen next? What cyber attacks are we going to witness?
Well, something will happen with the computer of the “guy with the dog” :) that will result in Elliot escaping from wherever he is now (apparently his mom’s house, but fans theorize that this is actually a prison or a mental hospital).
But if it’s a prison or a mental hospital.. how come he’s out so much? Or is it all in his head all over again?
Yes, it’s in his head, since for him, he’s at “his mom’s place”. But the said mom looks a lot like a nurse to me, actually. Also, all the meals at the same cafeteria, every day, with this same guy, whom he wouldn’t have been able to socialize with “in the real world”. Finally, the basketball playground is surrounded by more or less symbolic grids. Oh, and the guy with the dog looks like a guard to me.
It makes sense when you put it this way :) The only thing that bothers me is that we saw the all-in-the-head scenario play out in the first season.. The story would get quite repetitive… But it makes sense nonetheless!