RSA has released its Fraud Attack Trends report for Q1 of 2018. The report reveals that newsjacking has become fraudsters’ favorite way of empowering phishing attacks, among other things.
A recent news that fraudsters leveraged to incite a major phishing campaign was the relaunch of Canada’s Interac payment network. Researchers also expect to see a significant rise in phishing scams that involve fake messages about the EU’s General Data Protection Regulation, with the enforcement already in action. Any popular news item of global significance should be expected to enter the realm of fraud thinking.
The Ever-Increasing Need of Fraud Analysis
The distribution of major fraud tactics and attacks can help organizations understand the current trends being employed. As each type of fraud attack requires differing levels of resourcing and technical competence, this statistic, tracked over time, can provide a glimpse into the change in preferred attack vectors in order to help organizations respond more effectively.
For the first quarter of 2018 (January 1- March 31), RSA observed and analysed a number of fraud trends. Apparently, phishing is still prevalent as it accounted for 48 percent of all cyber attacks observed by the company in the given period. Canada, the United States, India and Brazil were the top three countries with highest number of phishing attacks. Trojan horses designed for financial fraud accounted for one out of every four attacks. The mobile ecosystem continues to be targeted as well.
The first three months of 2018 had 55% of all transactions taking place in the mobile channel, with 65% of fraud transactions using a mobile application or browser for malicious purposes. On top of these statistics, at least 80% of analyzed fraudster e-commerce transactions came from new devices.
The Reddit Fraud Trend: Abused by Fraudsters
For credit card fraud masters often called carders, social media platforms provide scalability, anonymity and enormous reach to promote their virtual storefronts. Reddit has been often abused by fraudsters, to the point that the popular media aggregation site recently banned a number of fraud subreddits. Of course, Reddit is just one out of many social media platforms exploited by scammers for communication purposes, to exchange contacts, advertise their services and swap fraud information collected from Dark Web related forums.
As a matter of fact, this is not the first time that Reddit has decided to van fraud-related subreddits. Nonetheless, this latest decision is crucial because it corresponds to the volume and size of the subreddits that were banned. The most prominent of all banned sections is “/r/DarkNetMarkets”.
The ban and the change of policy driving it evoked a strong reaction among participants, who immediately shared opinions on the subject, offering other options for participants to continue operations despite the loss of their usual platform, RSA pointed out in their report.
Fraudsters, including those participating in the now-banned discussions, have been warning about such a policy change and ban action for some time. In preparation, some even claim to have backed up the data from the now-defunct subreddits and offered links to download the deleted content.
It is good that Reddit has taken a clear stance on the fraud subject and has taken actions to prevent cybercrime activities on the platform. However, fraudsters were quite quick to react, and following the ban, they moved to alternative platforms where it would be easier to exchange fraud knowledge. Even though platforms such as Reddit do everything in the power to reduce the volume of aggregated fraud-related content, fraud activity is unlikely to drop.
Fraud operators are also adopting new infrastructures such as the blockchain to host credit card stores, fraud marketplaces and underground forums. This simply means that RSA and other researchers are expecting the expansion of fraud beyond social media – to blockchain and even IoT devices.
Researchers also note that in the past, there was a clear distinction between instant messaging platforms and social media. However, this distinction has been blurring, with these platforms evolving into something bigger with fraudsters using them as social media to promote their activities.
We recently wrote about the way Telegram is being leveraged by hackers to distribute malware and for communication purposes. Alongside Reddit, Telegram is also becoming a preferred target for malicious actors as evident by the increasing number of abuse cases on the service. Taking advantage of such platforms that are used specifically for communication is not a new trend but is affecting more and more legitimate apps, with Telegram now attracting more attention from crooks of all form and proportion.
General Fraud Statistics Q1 2018
A curious fact outlined by the RSA fraud research team: “The average value of a fraudulent transaction will likely always be higher than that of a genuine transaction because fraudsters regularly use stolen credit cards to make quick, high-value purchases, since these goods are easy to resell for a profit”.
There are, however, differences in the spending levels related to legitimate and illegitimate transactions. During the first three months of 2018, the biggest difference was seen in Europe (the U.K. excluded) where the average value of a fraudulent transaction was $439, or 152 percent higher than the average genuine transaction. The Americas were not far behind with the value of a fraudulent transaction estimated at $508, or 144 percent higher.
Which countries are mostly targeted by phishing?
According to the data gathered and analysed by RSA, these are the top 10 countries mostly affected by phishing attacks:
1.Canada
2. United States
3. India
4. Brazil
5. Netherlands
6. Colombia
7. Spain
8. Mexico
9. Germany
10. South Africa
As for the regions observed to host ISPs related to phishing attack, the list looks like this:
1. United States
2. Russia
3. India
4. Australia
5. Canada
6. France
7. Luxembourg
8. Germany
9. China
10. Italy
How to Protect Yourself from Phishing?
Phishing emails designed to steal credit card details usually drop a piece of specific Trojan horse to harvest the needed credentials. Furthermore, malware of various types is known to infect victims as a result of the interaction with such fraudulent e-mails. The latter typically contain Microsoft documents designed to trigger malicious macros causing the infection.
These types of documents are attached to the e-mails and may pose as updated privacy policies that the user is obliged to read. They may lead too different malware infections, including:
- Ransomware;
- Cryptocurrency miners;
- Trojans and Information Stealers;
- Rootkits.
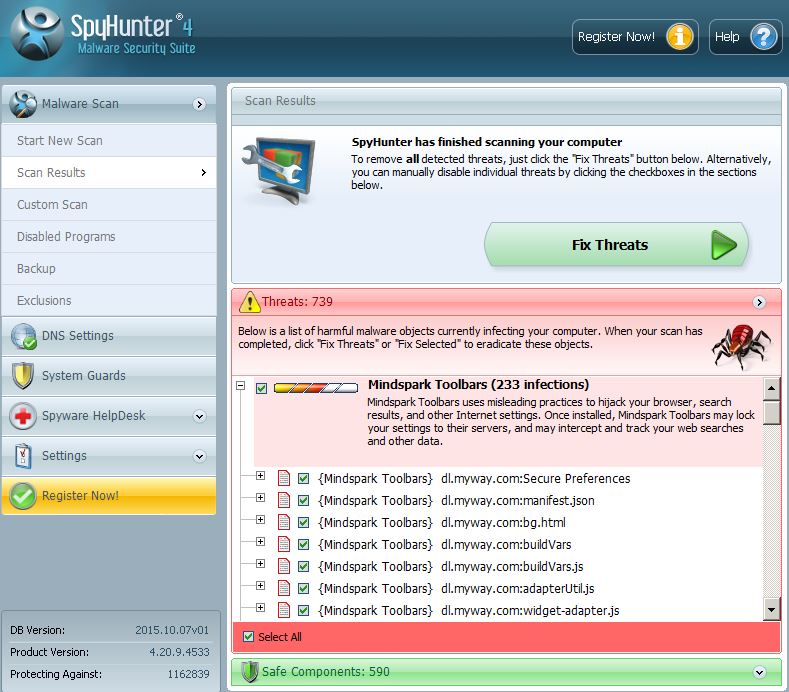
In case you believe that your personal or financial information has been endangered by e-mail scam or some other form of online fraud, you may want to scan your PC for malware. Just in case. Down below you will find some useful instructions to guide you through the removal process of malware, may it be brought to you by Facebook or phishing.
Automatically scan your computer to see if it has been compromised by a scam spread on Facebook or via e-mail:
In order to protect yourself manually from such phishing e-mails in the future, we do recommend to learn how to do that by reading the related article underneath:
Furthermore, when it comes to checking if an e-mail attachment is legitimate or fake, you can also use the free service ZipeZip. You can simply forward the e-mails to it, and shortly after you will receive a reply, telling you whether or not the attachment is legitimate. More information on how to use this free service can be found in the guide below:



 1. Install SpyHunter to scan for and remove .
1. Install SpyHunter to scan for and remove .