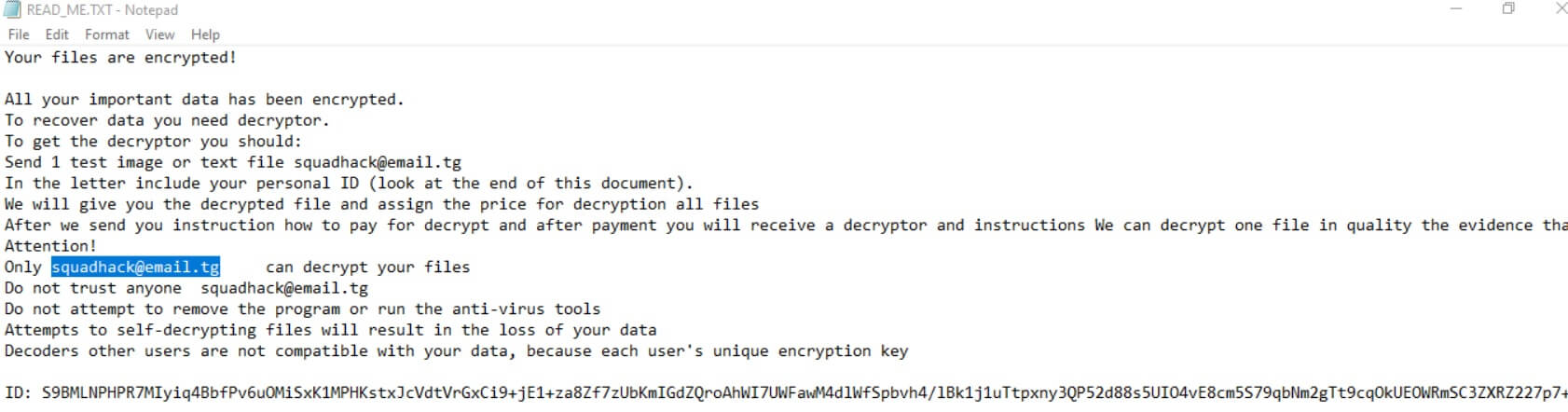
.chch Virus File (Squad Ransomware) – Remove It
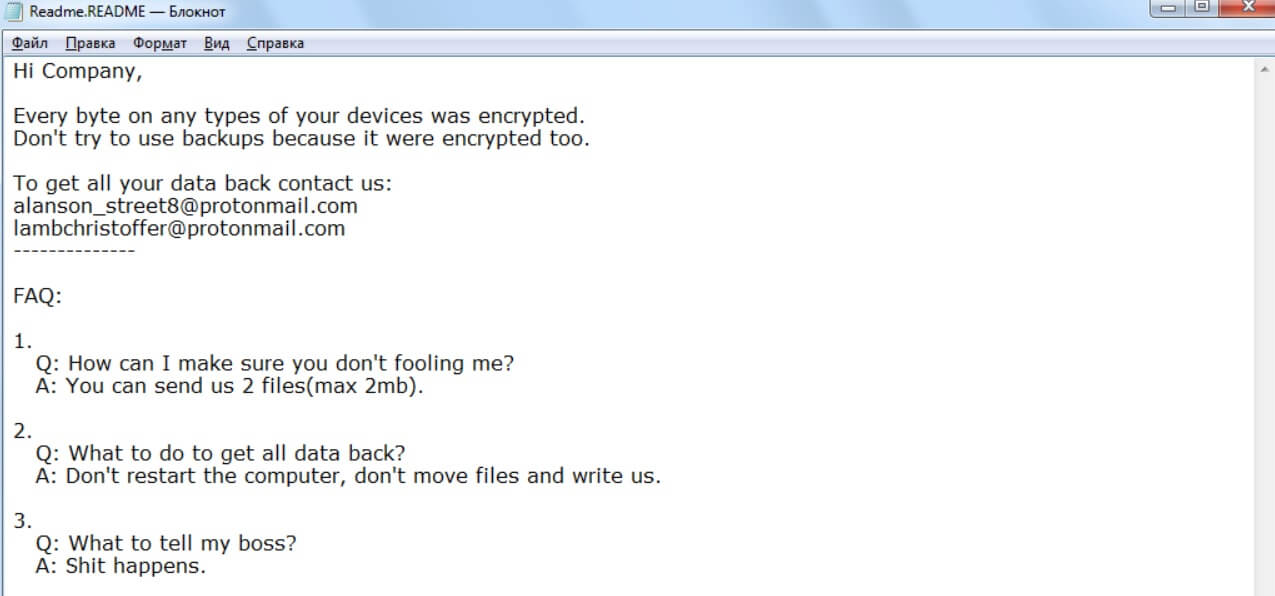
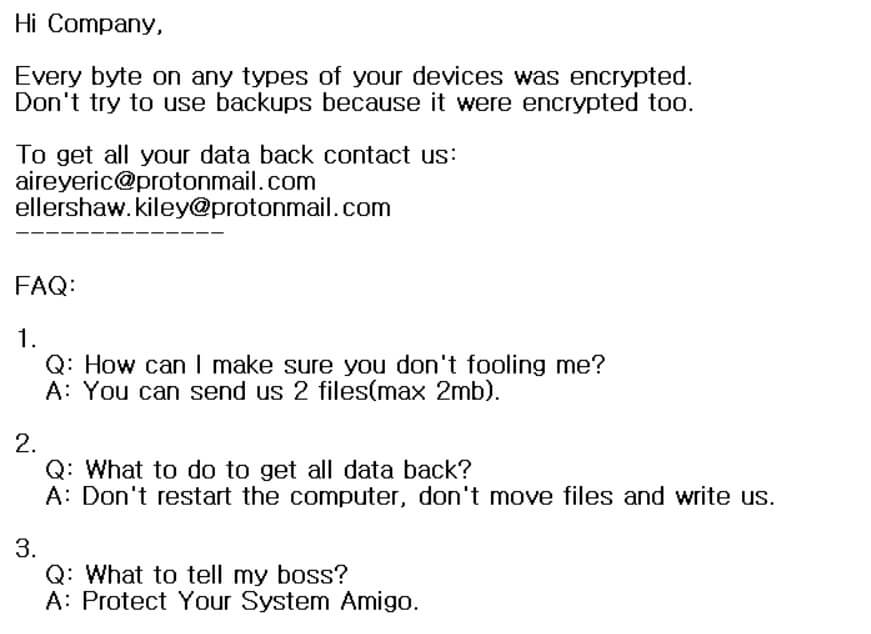
.chch file extension is placed on all of your files? .chch Virus File is also known as Squad ransomware which locks files on a computer and demands money to be paid as a ransom for unlocking them. Squad Ransomware (.chch…