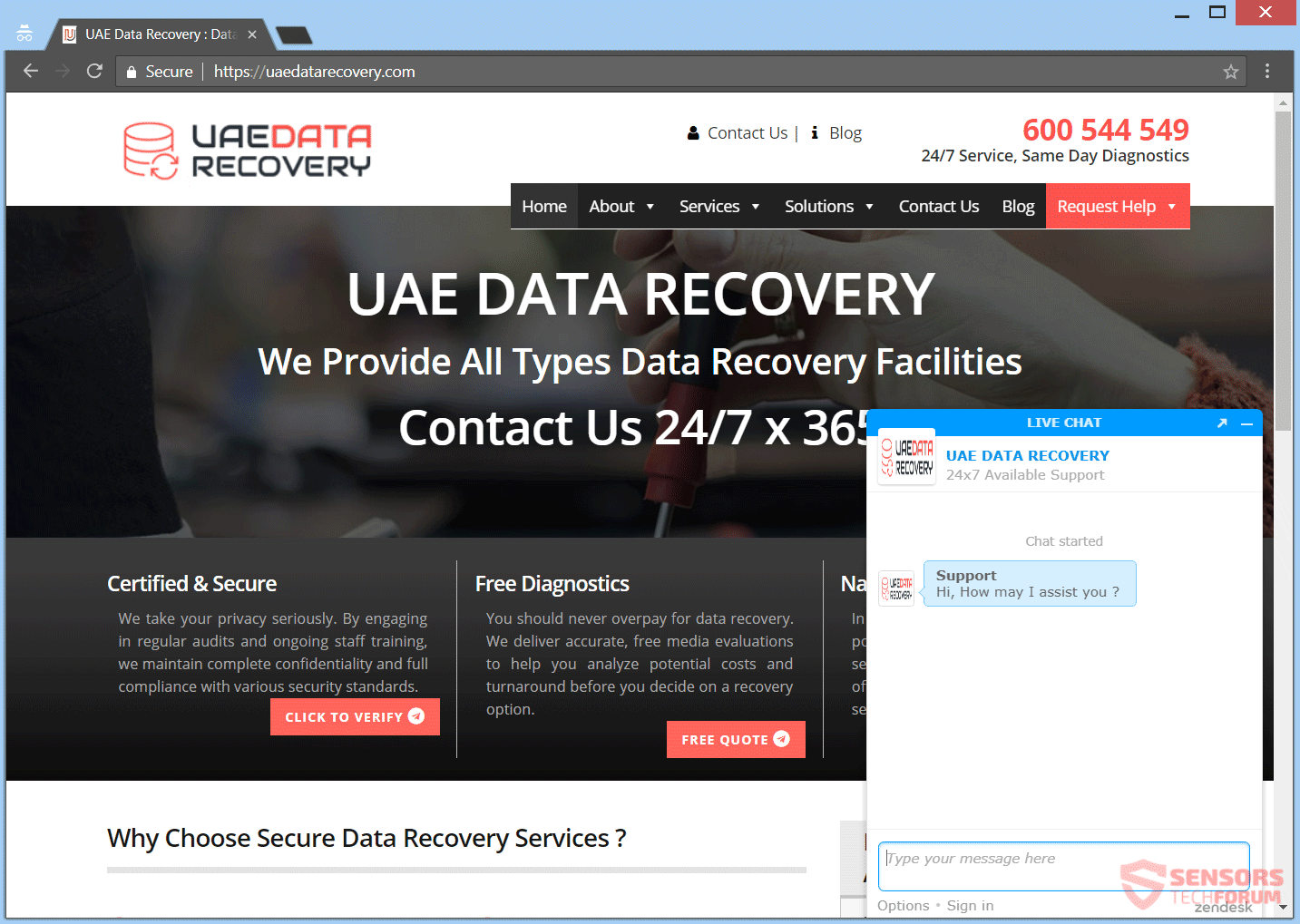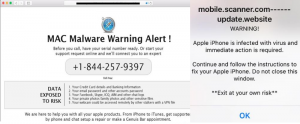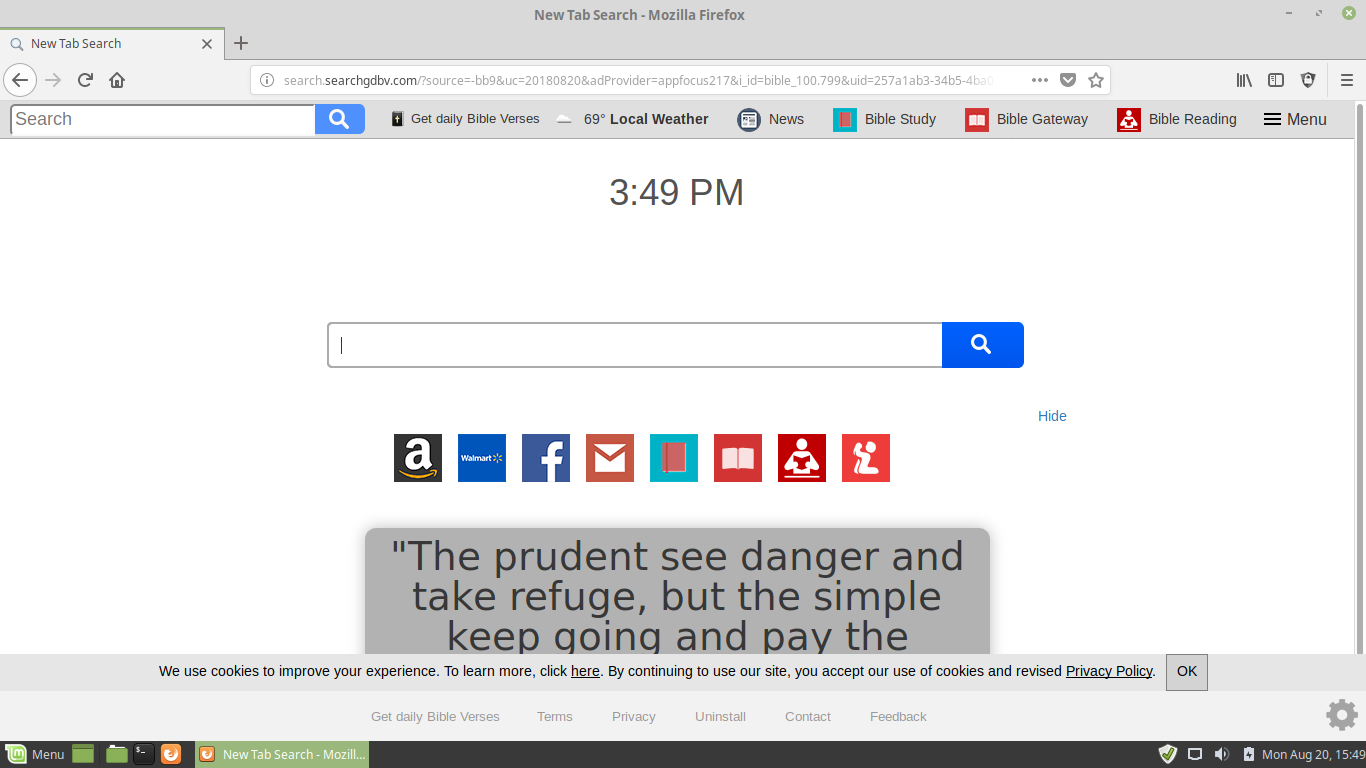
MyShopcoupon Mac OS X Adware Removal Instructions
MyShopcoupon Mac OS X Adware is dangerous virus infection that can lead to many serious consequences. Typically they are acquired through interaction with hacker-controlled sites or downloading of infected files. Read our article to learn more about it and find…