SIDENOTE: This post was originally published in February 2018. But we gave it an update in November 2019.
Update November 2019! Read the article to see how you can avoid PayPal Phishing Scams and remove malware which was distributed by such scams. E-mails, messages and websites are all involved in these types of spoofing. The article will also aid you to recognize PayPal Phishing Scams and the official PayPal messages from one another. If you notice that your computer system is infected or behaves strangely, we recommend that you scan it with a security tool.
PayPal Phishing Scams are common worldwide. Many variations of these scams exist, featuring websites specifically designed to generate spoofed pages, messages deliberately trying to trick you have a problem, or notifications which may lead to stolen credentials or your PC getting infected with malware. All of these types of PayPal scams are still in circulation and through them, a lot of sensitive data or money is being stolen. People keep falling victim to related spoofed messages, despite in what form they are sent on. Over the years PayPal is used in many scams and with each new one, cybercriminals improve their skills of making a scam as close as possible to the original messaging used by the big brand. If you are targeted with a spoofed message, you will be asked to login to “PayPal” or visit a Web domain and perform an action there like paying for a failed shipment.

Threat Summary
| Name | PayPal Phishing Scams |
| Type | Phishing, PUP, malware |
| Short Description | Phishing messages trying to trick you into clicking links. Once clicked, a link will redirect you on a landing page. You will be asked to do an action there, such as providing credentials, personal information or filling in a form. Occasionally, clicking a link will download malware on your computer. |
| Symptoms | You receive an e-mail message that is allegedly from PayPal. You will be urged to click on a link. You can then get malware on your computer device or land on a page that imitates the official PayPal website, while demanding of you to fill in personal details. |
| Distribution Method | Phishing Emails, Pop-up messages, Redirects |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
| User Experience | Join Our Forum to Discuss PayPal Phishing Scams. |

Phishing PayPal Scams – Update November 2019
Phishing PayPal scams are back and trying to find new victims with their landing pages. Not much else can be said in this monthly update, but PayPal continues to renovate its designs and change its Privacy Policy to stay unique and different than the phishing PayPal pages which the cybercriminals are trying to push to victims. If you continue reading down below you will see how many different scam pages are made to push the Phishing PayPal websites and redirects and how innovative they are becoming in the last year alone.

PayPal Phishing Scams – Update September 2019
Recently there are several popular campaigns that are used by PayPal scammers. They are used by several hacking groups that are not affiliated one with another. The number of scams associated with the payment service has risen in recent times in light of the attack campaigns that are currently active. A popular tactic is to create fake delivery failure reports. This is done by following a set procedure. The operators of this hoax will provide fake shipment information of an online shop order to the target users. Several attempts to deliver the item will be made until the order is classified as undeliverable. After this has happened the scammers will update the address with a legitimate one controlled by them. The order details however will bear the mark of a victim customer of which the sum will be requested. Upon the successful delivery of the goods the original address in the account of the victims will not match with the one of the “drop points” of the hackers. Henceforth the Purchase Protection policy will fail due to the difference in addressses and the hackers will keep the order.
Another option which is often abused is the PayPal feature called Friends and Family, this is the option of sending and receiving funds with lower fees. When it is used the transaction costs are lower and as such hackers take advantage of this fact by attempting to scam the users into sending them money through this option. In order for this strategy to work the hackers will need to convince the targets into thinking that that they are a friend, relative or family member. There are several common scenarios that are used effectively in the recent campaigns:
- Product Purchases — The hackers can present themselves as an e-commerce shop or service and ask for payment using this feature in order to “lower the price” for the victim customers. The payment will be requested in advance before the items are said to be sent in the post.
- Gift For a Friend Scam — The hackers will attempt to impersonate the friends of the victims in order to requests gifts for a birthday or another event. They will reach out to them via social networks and popular messengers clients and services. The funds for the gift will be requested for a special “savings” Paypal account that is actually owned by the hackers.
- Overpayment Scam — This scam is designed to look like an overpayment that has been made by mistake. This is done by targeting sellers that use the PayPal payment service. They will receive a notification from the company saying that a customer has bought an item from the target’s shop. Shortly afterwards they will receive a message from the customer stating that they have paid more than what the actual value of the item. The “extra funds” will be requested back to the hackers. This can be done by through an already compromised PayPal account or a specially made profile.

PayPal Phishing Scams – Nemty Ransomware Distribution
PayPal phishing scams have also been observed to be used to distribute samples of the dangerous Nemty ransomware. This is done by creating numerous fake Paypal sites that include the script installation. The sites appear as special promotional offers that offer cashback opportunities for prospective buyers. The Internet users are promised these lucrative deals by downloading a special app that is advertised as being made by the payment service. The name of the program is cashback.exe and if started it will lead to the Nemty ransomware.
There are two distinct characteristics associated with the attacks:
- The sites are made using the exact design layout and elements from the official PayPal site.
- The sites use homograph domain name spoofing techniques which can manipulate many users into thinking that they are accessing real and safe sites.

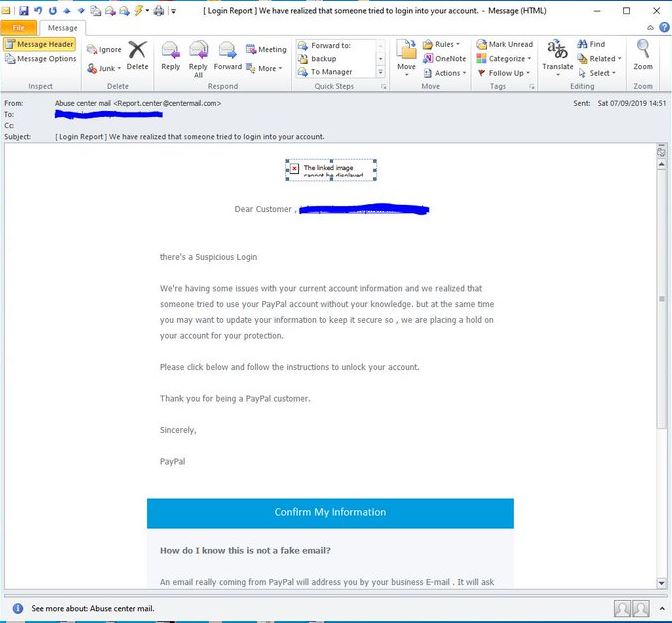
PayPal Phishing Scams – Login Report Emails
Computer hackers are coordinating email phishing messages which manipulate the recipients into thinking that they have received a login notification prompt from the PayPal service. The message is designed using the familiar design elements and layout. The message will read that there is a suspicious login attempt. Many of the email messages will have cross-referenced information about the users and use a personalized greeting while others will follow a generic template. If the users click on the shown link they will be lead to a malware login prompt that will hijack their personal information.

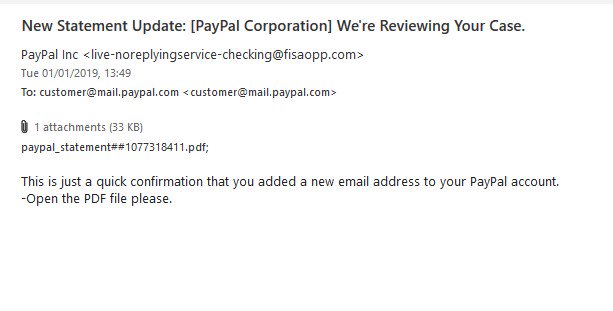
PayPal Phishing Scams – New Statement Update
A distinct email phishing campaign has been detected carrying the subject line of “New Statement Update (Paypal Corporation) We’re Reviewing Your Case” which has been launched worldwide. To this date we have not received reports of a massive infection however we assume that if the initial wave picks up a sufficient number of infected hosts then the attack may be repeated with larger resources.
The main warning sign is the senders address, it will not be from the official PayPal domain and it will include attached PDF files. The service will never send such files to any of its clients, nor will it not greet the users with a generic identifier. One of the main signs will be the lack of a proper greeting and the absence of the regular PayPal design elements. The attached PDF file will surely be one of these two malware types:
- Virus Files — All common malware types can be easily acquired through these data files by using the .pdf double extension superseeded over the executable ones (.exe, .bat and others).
- Malicious Payload Carriers — The files can include dangerous embedded scripts (macros) that will infect the victims with malware (usually ransomware and Trojans) when they interact with a certatin element. In other configurations upon opening them files a prompt will be spawned requesting that the users enable the macros. This will trigger the infection and cause the included virus to be deployed onto the system. Practically all popular document types can be payload carriers: text documents, spreadsheets, presentations and databases.

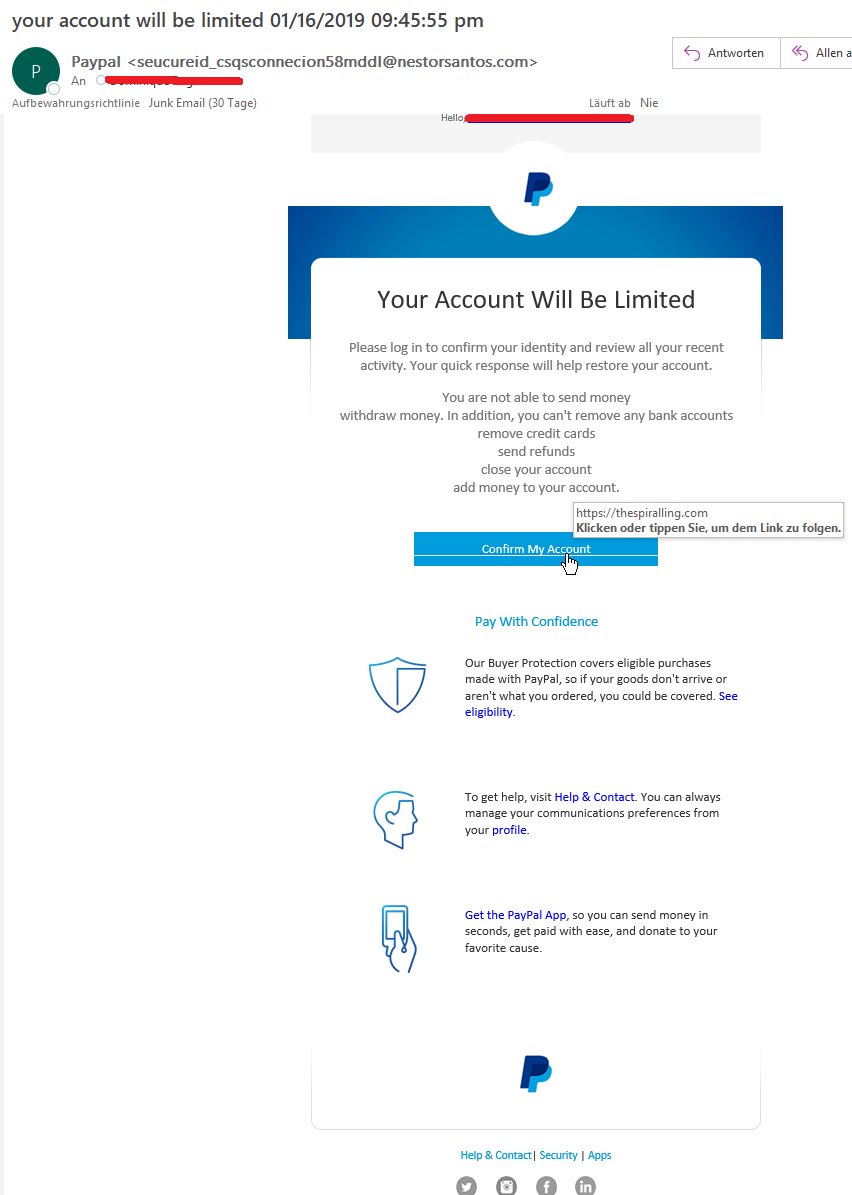
PayPal Phishing Scams – Your Account Will Be Limited
January 2019 saw the release of a new Paypal phishing email scam campaign which is orchestrated by an unknown hacker collective. So far we have no information about the identity of the hacking group. The sent emails are still relatively low in quantity which is probably explained by a test release. If the initial attack proves successful then a larger attack may be launched.
Like other similar attempts the hackers will send out messages that appear as being sent by PayPal to the chosen targets. They will mimic the online service’s design and layout by coercing the victims into interacting with the built-in content. The message will read that the accounts belonging to the recipients are limited until they confirm their activity. The most common operations are listed in the email:
- Funds Transfer
- Withdrawal of money and bank account removal
- Credit Cards Removal
- Account Closure Procedure
The recipients will be guided to click on a button called “Confirm My Account” which will redirect them to a faux landing page. If the account credentials are entered then they will instantly be transmitted to the hacker operators.

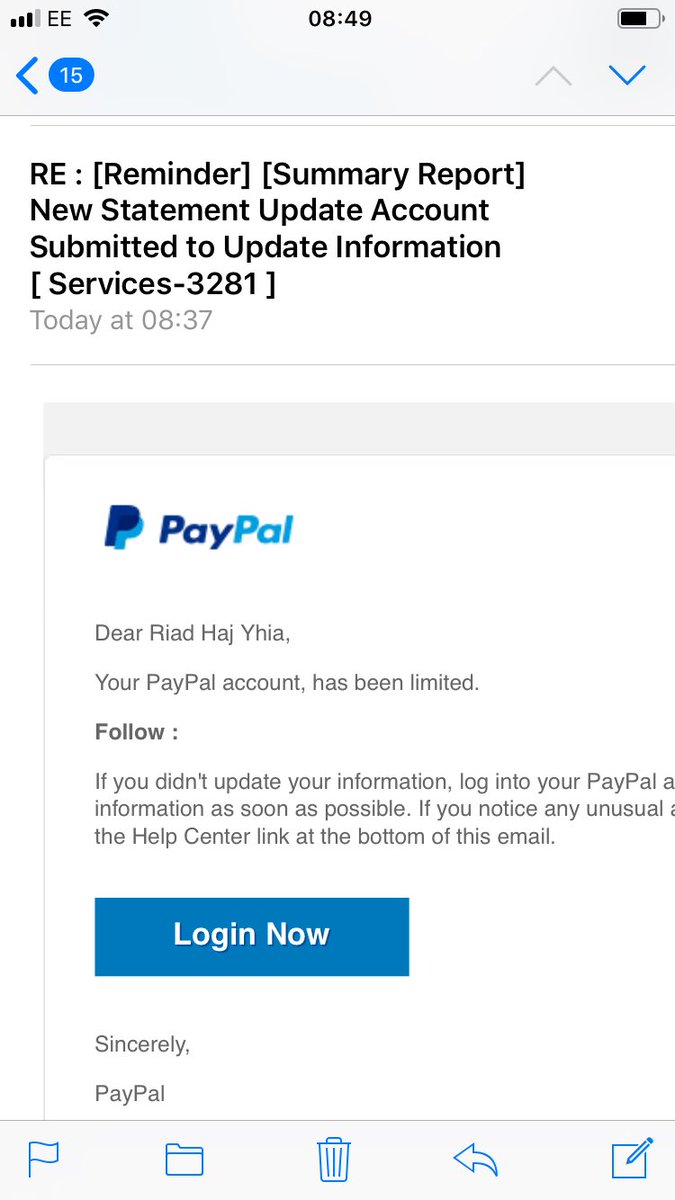
New Statement Update Paypal Phishing Scams
This is an email-based scam which is designed to appear as being sent by PayPal. Several different types of “tags” are placed in the subject line in order to make it appearing more believable. What’s interesting about this particular campaign is that the sent phishing messages are personalized — this is attributed to stolen or hacked details about the targets. Such campaigns are particularly effective as it is deemed that only the legitimate services have the personal information and address the recipients as such.
The message will read that the users accounts are limited and that they will need to login in order to continue using it. A link will be placed in the body contents that will redirect to a malicious landing page. As soon as the victims enter in their information it will be transmitted to the hacker operators. The convincing looking pages might include links to legitimate sections of the PayPal site. There are several warning signs that the visitors can watch out for:
- The correct domain associated with PayPal can easily be mistyped. Many of the hacker-controlled sites register hundreds of combinations of mistyped key combinations in order to draw in unsuspecting visitors into entering their account credentials in them. This may be the case with some of the samples send in this campaign.
- A lack of proper security certificates signals that the website is unsafe.
- Shortened URL links are never used in email notification messages.

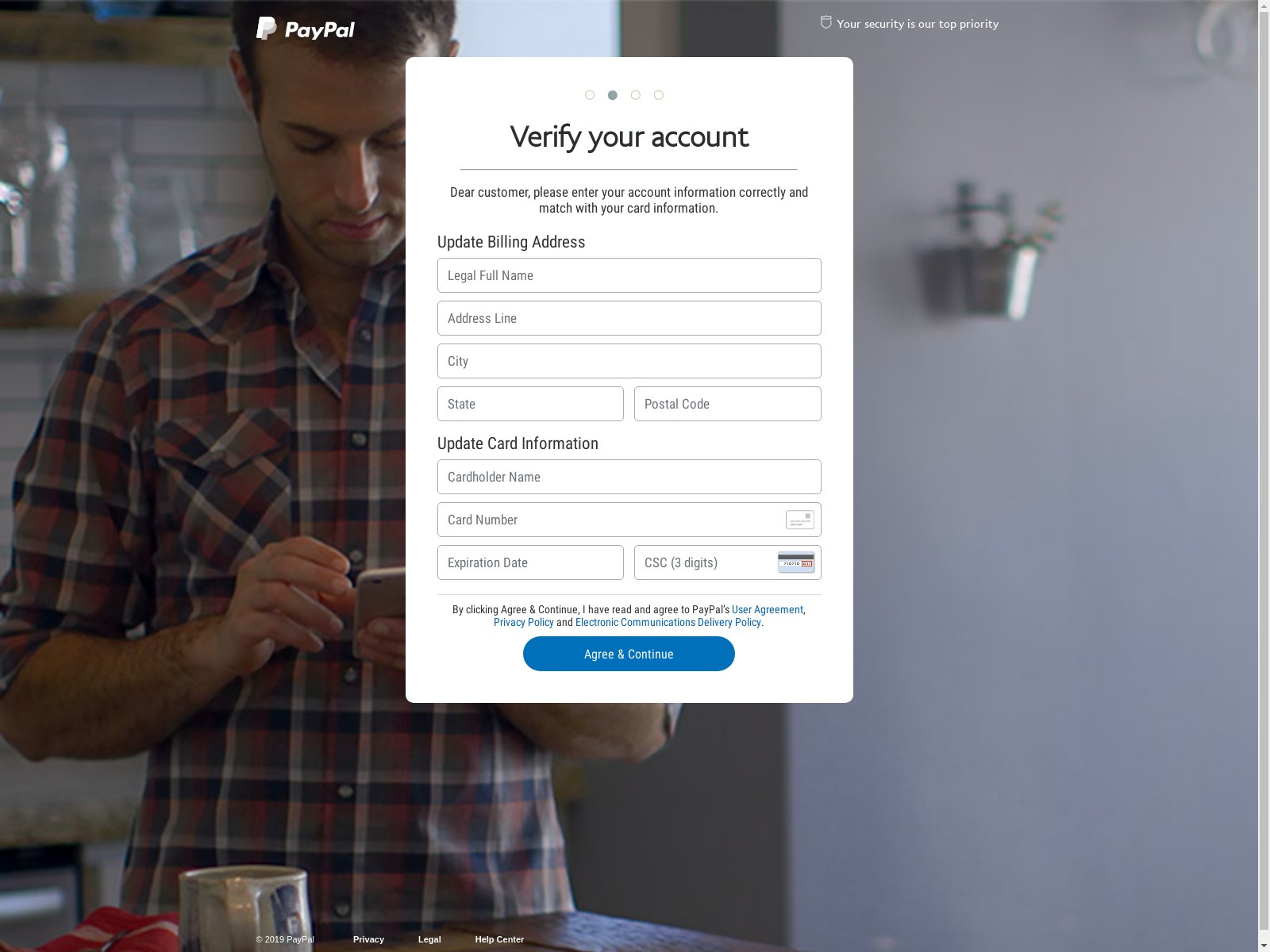
Verify Your Account Paypal Phishing Scams
Another PayPal related scam is the one that redirects the targets to a fake landing page which reads “Verify your account”. The account verification of the service is a legitimate procedure however it is not displayed in this way nor will PayPal request such services. The domains on which the phishing sites are hosted may sound almost the same as the official domain page or have PayPal-related strings. In addition advanced samples can even include security certificates which will mask the site as legitimate looking for many users.
What’s dangerous is that there is no information about the criminals behind the phishing attack. Their motives might be more than just identity theft or the account overtaking. Such websites can be used as sources of malware infections:
- Trojans — They allow the hacker operators to take over control of the infected computers giving them the ability to spy on the victims, steal their files and deploy other threats.
- Browser Hijackers — In some cases interaction with such sites can load browser hijackers that are under the form of plugins made for most of the popular web browsers. They are often found on the relevant repositories using fake web developer profiles and user reviews. When they are installed all important settings will be altered in order to redirect the victims to a hacker-controlled page. Modifications can be done to the default home page, search engine and new tabs page. Furthermore the victims may not be able to revert the changes as the malicious code will modify the Windows registry, configuration files and other data.
- Cryptocurrency Miners — Hacker-controlled sites have the ability to load miner code into the malicious sites. These scripts will run constantly as soon as they are executed by the browser and will set up a connection to a special server distributing complex mathematical tasks. During their calculation the infected machine will have their performance greatly reduced. As soon as one task is finished another will be started and for each reported workload income will be generated and allocated to the hacker operators. The funds are in the form of cryptocurrency and will be directly wired to the digital wallets of the criminal collective.

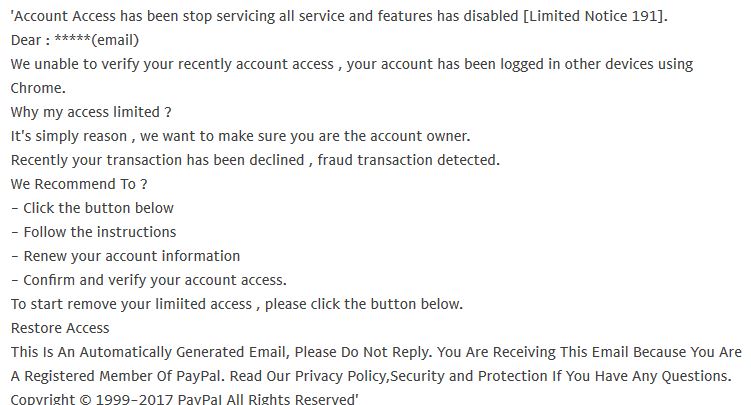
PayPal Phishing Scams – Action Required Email Scam Message
A surge of phishing attacks carrying another popular PayPal scam has recently been reported. The victims are sent email messages that imitate legitimate notifications sent by the service asking them to verify their accounts. According to the message recent suspicious activity has been detected by PayPal and the users need to enter in their details. The quoted reason is a fraud transaction according to the email message.
The victims are given a link to a malware landing pages which is designed to fool them into thinking that they have accessed the real PayPal site — a similar sounding domain name and a security certificate can be implemented to make it more believable. Note that if the victims enter in their login details they will be instantly transmitted to the hackers.

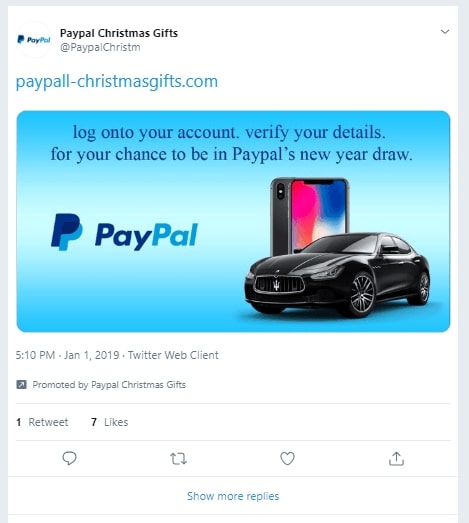
PayPal Phishing Scams – Update January 2019
In the beginning of 2019 we received numerous reports that a new PayPal phishing scam has been found. Instead of using the traditional techniques it relies on hacker-made or hacked Twitter accounts. The dangerous characteristic is that thousands of users might have interacted with the Tweet offering a “New Year Draw” enticing the targets into thinking that they can earn gifts. Upon clicking on the shown links the victims will be redirected to a phishing login page requesting PayPal account details.
An investigation into this page shows that when information is entered the victims will be redirected to another page requesting payment card details as a “verification step”.

PayPal Phishing Scams – Update December 2018
In December 2018 we received reports of a new scheme that uses a domain that poses as a Paypal notification service. Upon interaction with a malicious site or a phishing email the victim users might be redirected to it. It will spawn a pop-up notification or a new tab page that that will ask for the users’ login credentials.
We remind our readers that the sources of infection can be different and include the following typical cases:
- Email Scam Messages — The hacker operators may send out phishing messages via email messages by impersonating Paypal. The messages can be designed using the same design layout as the company itself. The only differences would be the link to the login page.
- Redirects — Links presented through browser hijackers and social networks via hacked or hacker-owned accounts.
- Virus Infections — Various malware infections can lead to the display of the PayPal phishing scam.

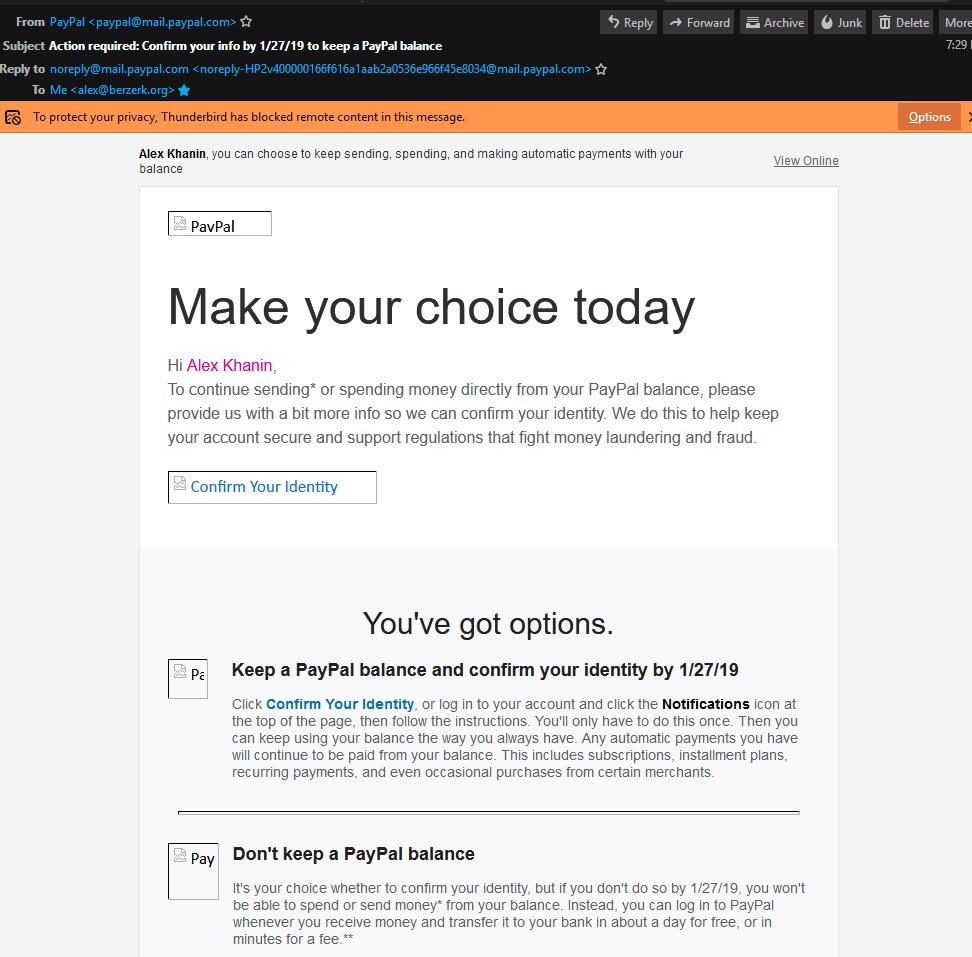
PayPal Phishing Scams – Update November 2018
A new type of phishing email message has been detected with the subject line Action required: Confirm your info by XX/XX/XX to keep a PayPal balance where in the “X” are filled with a date. The message will read that in order to continue using the service they will need to confirm their identity. The email follows the usual design template used by the service and it can be even be personalized with the recipient’s name. This is done by cross-linking the victim’s email address with publicly accessible information. If they click on the links they will be redirected to the phishing landing page where their account credentials will be requested. If entered they will automatically be forwarded to the hacker operators.

PayPal Phishing Scams – Update October 2018
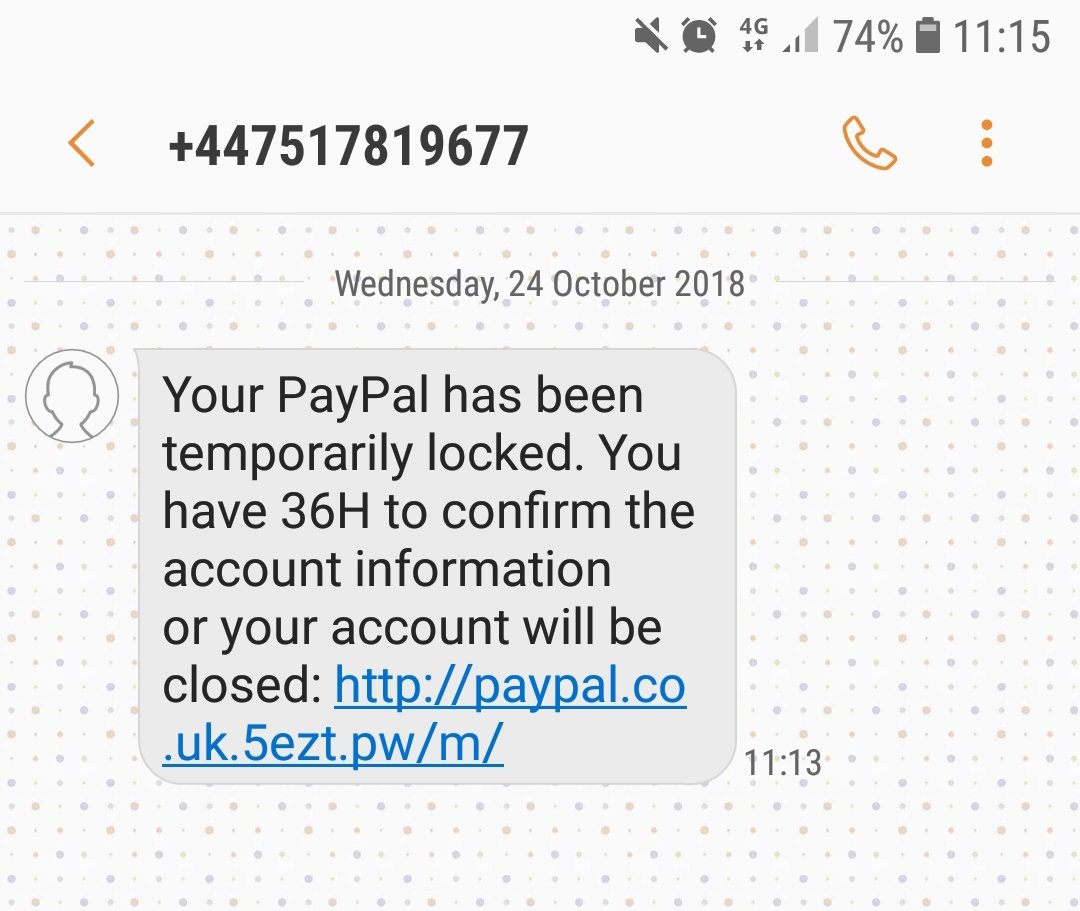
In October 2018 another phishing scam strategy was observed. This time computer criminals used SMS messages to confuse users into thinking that PayPal is contacting them about their account. The received message is written in the fashion of a security notification. The message reads the following:
Your PayPal has been temporarily locked. You have 36H to confirm the account information or your account will be closed: XXXXXXXXXXXXx
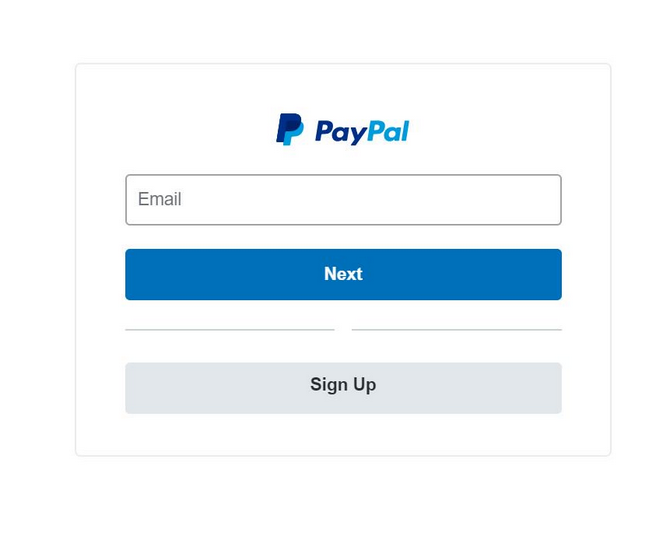
A fake login page will be sent as an URL. If the users click on it they will be taken to a screen asking for their account credentials. If entered the username and password combination will automatically be sent to the operators of the scam.
An additional PayPal phishing scheme redirects the users to a simplified login screen that uses the familiar quick sign-in prompt. The criminals have made an exact copy of how the login screens appear, the labels and layout of buttons as well as the slide animation between the username and password entry screens.

PayPal Phishing Scams – Update August 2018
New PayPal Phishing scams have been detected within the first few days of August 2018, which scams seem to continue being delivered as spam email messages. They can contain malicios files being attached to the email and/or links that aim to redirect you to a phishing page.
Below you can see the two most common messages used both for the Subject of a message or below in its actual contents:
- _Protect your account_
- _Now check the account information that belongs to you!_
Notice how both of them are encapsulated with lower dashes ( “_” ) and mention something about checking whether your account is in order. Do not trust such messages and delete them from your e-mail inbox.

PayPal Phishing Scams – Distribution Methods
PayPal Phishing Scams might distribute via a third-party installation setup. Applications connected to PayPal Phishing Scams can intrude your computer, without your knowledge of that. Installer setups like those could be set by default to install additional components. Bundled packages and freeware setups regarded as PUPs could be distributed and push scam messages to your PC and browsers. To avoid installing unwanted applications, you can to search for the Custom or Advanced settings. If you find such, you could probably deselect anything you do not want on your machine.
Note! These types of PayPal Phishing Scams were seen to be pushed via e-mail address messages on a large scale as showcased on the screenshot below. Beware of any messages that have links to PayPal services that you do not remember using.
PayPal Phishing Scams might distribute themselves by using similar-looking websites which are hosting phishing landing pages. Websites like those use the PayPal logo without permission and to an extent you might not differentiate the original with the bogus website. Clicking on just one redirect link or an advertisement could send a virus to your computer machine. In addition, banners, pop-ups as well as more kinds of adverts could be placed on top of browser pages to push more links and phishing messages. All browsers could get affected and any operating system for that matter.

PayPal Phishing Scams – Detailed Analysis
Many scams related to PayPal are circling the World Wide Web nowadays and seem to increase every month. This article will show what the vast majority of scam types related to the PayPal Service are and how you could recognize them. Scams that are tied to PayPal are not very innovative as you can see older versions of them over the years. Unfortunately, every year each scam gets a little bit more sophisticated than its past variant, and keeps spreading to more users, who are potential victims if they do not know about it. Surprisingly, the number of people who are tricked is ever increasing, instead of that being the opposite.
Websites which are hosting PayPal Phishing Scams can load pop-ups and other advertising content as you are browsing to help popularize a type of scam page. Heaps of advertisements might show, promoting a way to obtain money via PayPal.

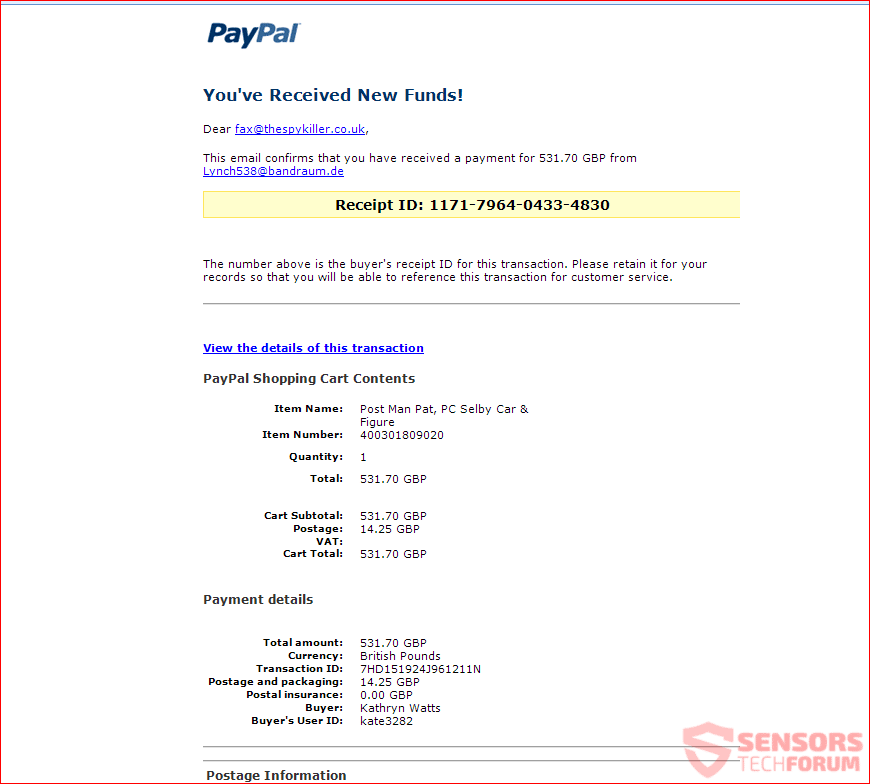
PayPal’s ”You’ve Received New Funds” Scam
This scam is a recurring one, which means that it keeps showing up, year after year, months after months. The scam shows you a notification which states “You’ve Received New Funds”.
You can preview a variant of the You’ve Received New Funds scam message below:
From the above image, you can see an e-mail message stating that you have received new funds in your PayPal account. However, PayPal uses other wording when it comes to that – either “You’ve got money” or that “Somebody sent you X” amount of money. Down here below you can see what such a message contains:
You’ve Received New Funds!
This email confirms that you have received a payment for 706.70 GBP from Garner73@tiscali.it
Receipt ID: 9880-7964-4082-4830
The number above is the buyer’s receipt ID for this transaction. Please retain it for your records so that you will be able to reference this transaction for customer service.
View the details of this transaction
PayPal Shopping Cart Contents
Item Name: Post Man Pat, PC Selby Car & Figure
Item Number: 400301809020Quantity: 1
Total: 706.70 GBP
Cart Subtotal: 706.70 GBP
Postage: 14.25 GBP
VAT:
Cart Total: 706.70 GBPPayment details
Total amount: 706.70 GBP
Currency: British Pounds
Transaction ID: 7HD151924J961211N
Postage and packaging: 14.25 GBP
Postal insurance: 0.00 GBP
Buyer: Kathryn Watts
Buyer’s User ID: kate3282Postage Information
Address Kathryn Watts
2 Haselmere Close
Bury St Edmunds, Suffolk
IP32 7JQ
United KingdomAddress status Confirmed
Have you lifted your withdrawal and receiving limits? Just log in to your PayPal account and click View Limits on the Account Overview page.
Yours sincerely,
PayPal
Copyright S 1999-2012 PayPal. All rights reserved.PayPal (Europe) S.a r.l. et Cie, S.C.A.
Societe en Commandite par Actions
Registered Office: 5th Floor 22-24 Boulevard Royal L-2449, Luxembourg
RCS Luxembourg B 118 349PayPal Email ID PP345
The above text will either be a landing page, an attached text with images to the email’s body or sent as an attachment. That attachment will go along with the email containing a file (usually an executable or JavaScript file disguised as a document). The document is most commonly pushed as a PDF one. Such an attachment will also in most cases download a malicious payload aiming to infect your computer system. Once inside, your computer device will become compromised and might be used for various nefarious purposes. Those purposes include, your computer being used as a part of a botnet or as a gateway to steal your credential data, personal information or other details related to your PayPal account.
As you can see in the screenshot shown above, it is depicted how PayPal is being spoofed with the logos, brand and the way messages are sent. You might be provided with a link that can send you to a page where you will be asked to give your password and account name (which in most cases is the email you have registered your PayPal account with), which seems suspicious in itself.

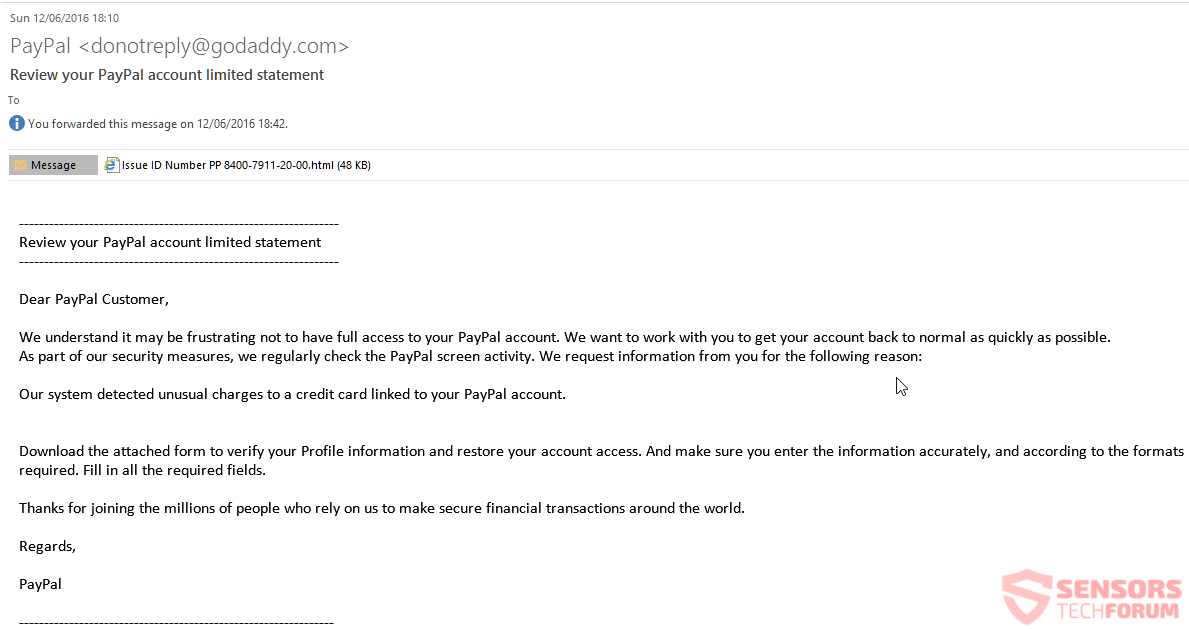
”Review your PayPal account limited statement” Phishing Scams
The PayPal Phishing Scams have many variations, but what you will see most commonly is the following message, displayed in the below screenshot:
Such an email message will state something in the lines of the following:
Review your PayPal account limited statement
—————————————————————-
Dear PayPal Customer,
We understand it may be frustrating not to have full access to your PayPal account. We want to work with you to get your account back to normal as quickly as possible.
As part of our security measures, we regularly check the PayPal screen activity. We request information from you for the following reason:
Our system detected unusual charges to a credit card linked to your PayPal account.
Download the attached form to verify your Profile information and restore your account access. And make sure you enter the information accurately, and according to the formats required. Fill in all the required fields.
Thanks for joining the millions of people who rely on us to make secure financial transactions around the world.
Regards,
PayPal
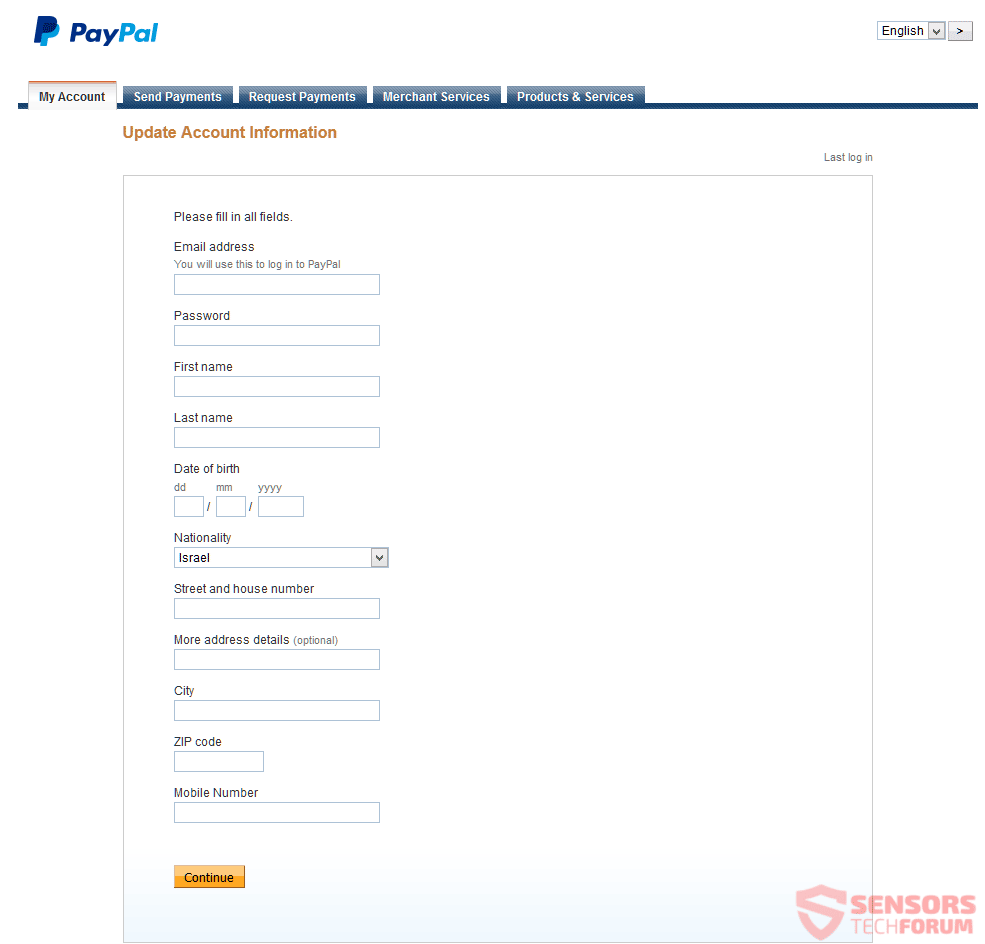
You will be asked to download an attachment with a message inside. The message will instruct you to open up a link. That link may look like the official URL address of the PayPal service but do not get fooled. The link will redirect you to a phishing page that may look very similar to a legitimate PayPal-hosted page, but has a suspicious URL that is not located on the PayPal official domain. In this case, the link “https://www.paypal.com/il/cgi-bin/webscr?SESSION=F5sJMNm-og4yRrDzVrFsSwS4Pjt6Wq1x-aFmISUJZy7xVTNjFu8OmrGhb-4&dispatch=5885d80a13c0db1f8e263663d3faee8d0b7e678a25d883d0bcf119ae9b66ba33” will land you on the “https://www.paypal.com/” page, but launch a script. The script will make it so, any detail and information that you type in will actually be sent to the “https://www.egypt-trips.co/wp-admin/includes/New/post_data.php” address. See below how the page looks like from the image below:
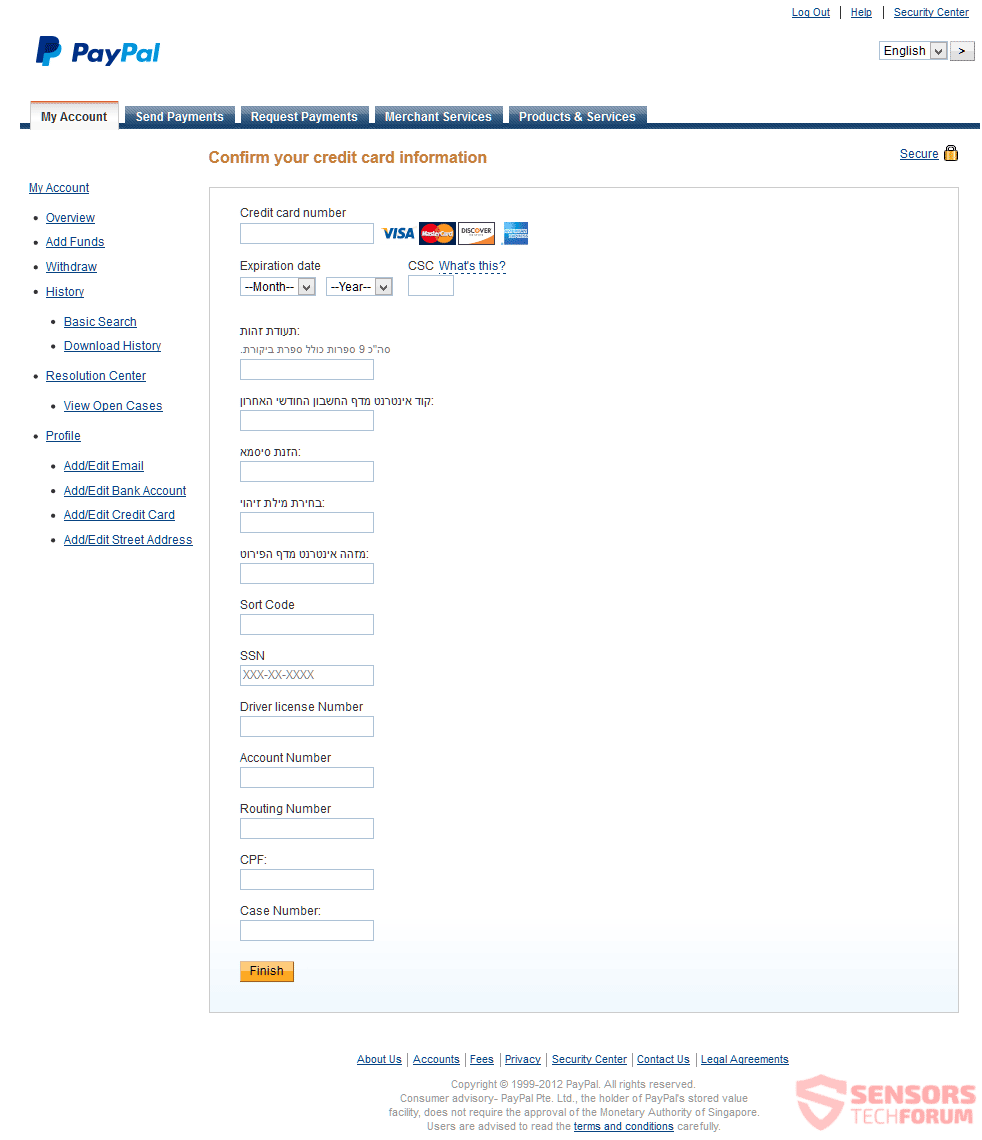
Afterward, you will be prompted to enter your details, such as an email address, password, first and last name, date of birth, nationality, city, address, zip code, mobile number and other personal data. In case you are wondering why, it is due to the fact that the cybercriminals want to steal your PayPal account along with your identity. If you proceed and enter all of these details, you will be redirected to a page that requires further details, like your credit card number and a “Finish” button at the end. This is the second page that displays with the second art of details which are asked from you:
If you didn’t get suspicious by now, then either you are a new PayPal user and do not know how their system works (like, if you enter such information once through their site it will be filled in those forms the next time you are on such a page) or you believed in what the scam is claiming. In case you entered every detail on that page, you will finally get redirected to the official page of the PayPal website. You should be wary of any such websites and if you doubt the contents of a message that is supposedly from PayPal you should ask your family household if anybody used the service or tampered with a joint account.
All of the scams described above, plus others which are similar to them might be advertised or promoted in some shape or form. Do not believe in messages that look suspicious and when you do not recollect if you indeed did any of the actions described inside the messages. Beware of such scams as they try to look like they are sent from PayPal as close as possible. To do that, criminals are using exactly or nearly the same design, fonts, logos and wording as the PayPal site network.
Below you will see how to differentiate the usage of the PayPal brand from scams and the real thing. You will also find good tips on what to do or not do, so you can avoid getting scammed. At the end of the day, you should also scan your computer in case a malware is causing such messages to show up on your computer screen.

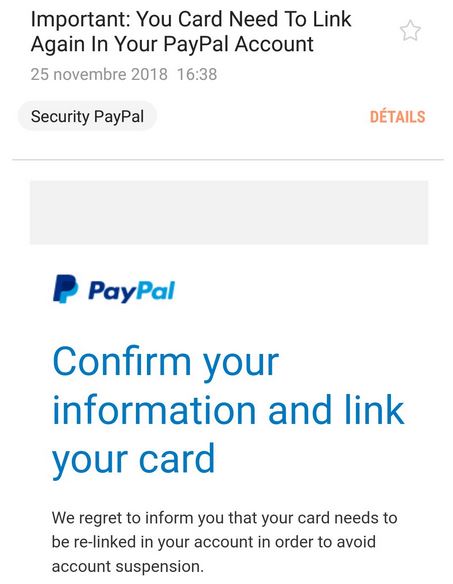
“Confirm your information and link your card” Phishing Scams
A recent email-based phishing scam targeting PayPal users was detected during its attack campaign. The victim users will receive a warning notification requesting the users to re-link their payment card in the service. The quoted reason is to “avoid account suspension”. The email message contain graphics, layout and text that is typical to the service. At the same time they are given a link that leads them to a website that is not part of the legitimate PayPal domain.
The phishing scam landing page may be designed to look just like the real login screen. It will request the account credentials used by PayPal and any additional information. All collected information can be used for additional crimes such as identity theft and financial theft.

PayPal Phishing Scams – How to Avoid Them?
In this section, you will find out how to differentiate between PayPal Phishing Scams and messages from the official PayPal brand, following a simple set of rules and guidelines. So, if you are reading this article, you should now know that there is a multitude of scams involving PayPal featuring spoofed messages. Below you will find more on the topic.
Refer to the following link that is of the official PayPal page for Common Email Scams.
As you now know about the existence of the scams and Common Email Scams page hosted on the PayPal website, refer to the following guidelines on how to avoid most scams related to the service:
- Do not provide any details about you, your addresses or similar information via email or unknown Web pages
- Do not open email attachments, as PayPal does not send such, neither it requests clients to open any
- Always use PayPal.com to refer to pages in connection with the service
- Avoid messages with grammatical or typographical errors
- Avoid emails that are not addressed to you by name
- Avoid messages sent by a service you don’t expect to hear from
- Avoid clicking on links to provide your email address for verification
- Avoid payments to someone whose identity you can’t confirm or if he wants to use a middleman service
Note! In case you remain unsure of what to do or you do not know if a message you got is actually from PayPal you can ask the US PayPal Community directly from this link to receive some feedback. Most of the scams in circulation are well-known and somebody should be able to assist you there. If you want to report a scam/spoofed message related to PayPal – refer to the official PayPal report page.
The guideline rules listed above were constructed by the SensorsTechForum team, via a research done on the matter. These rules are based on common sense and depending on the various scams related to PayPal.
A part of those scams related to PayPal can be removed by closing the message or browser. In case the scam pages continue to bother you even after that, then you probably have something else on your computer that is generating them.

Remove PayPal Phishing Scams and Related Malware
All that is required to remove some PayPal Phishing Scams is to ignore the message, never respond to it and delete it. Other scams require a bit of action, such as thoroughly scanning your computer machine with security software to determine whether you have some malware component that is pushing PayPal spoofed messages to your computer, browser or e-mail address.
We highly recommend that all computer users scan their system for active infections and malware using a security program. That could prevent many malicious actions and stop malware of distributing further.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove PayPal Phishing Scams from Windows.
Step 1: Scan for PayPal Phishing Scams with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





Step 3: Uninstall PayPal Phishing Scams and related software from Windows
Uninstall Steps for Windows 11
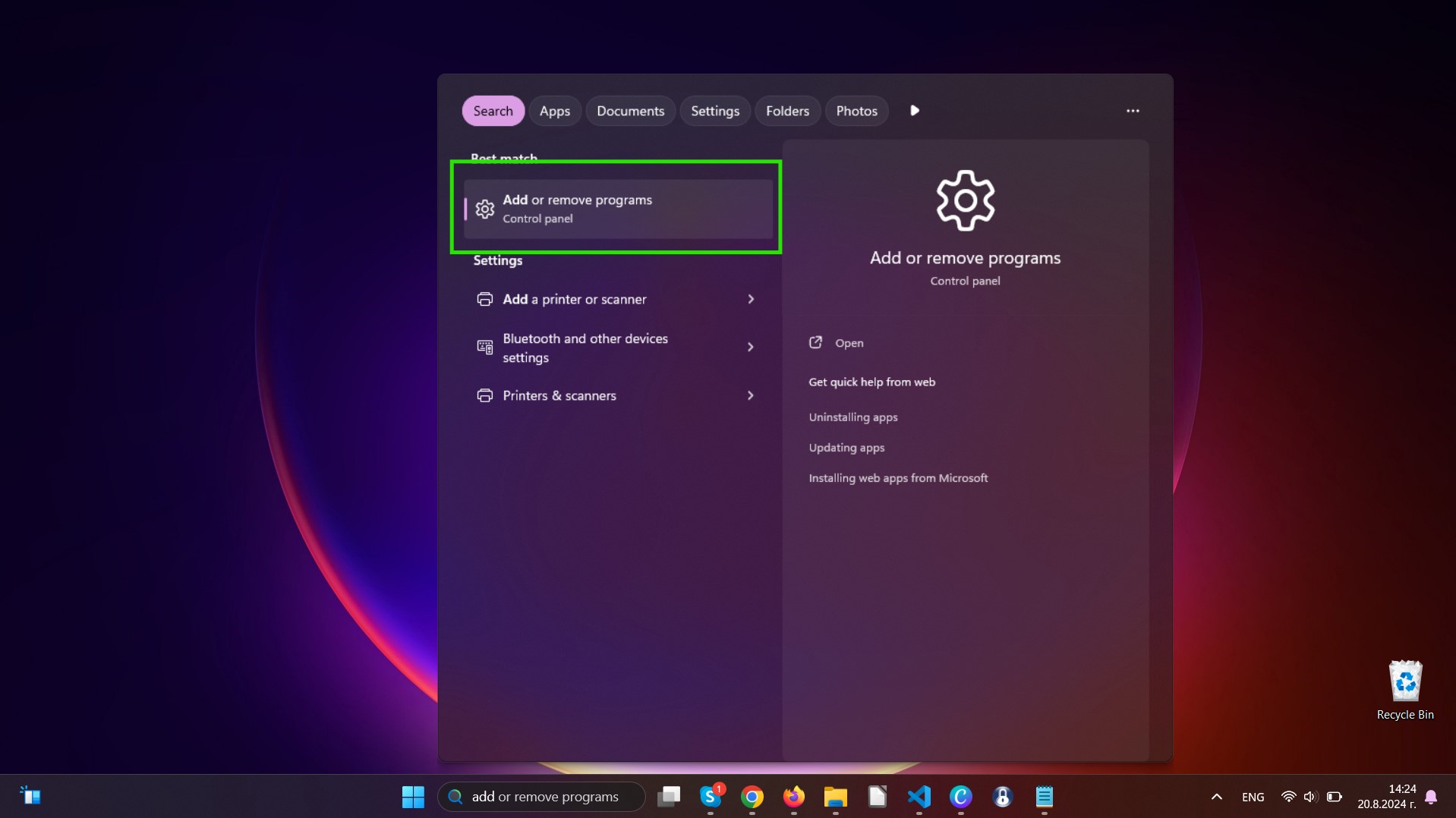
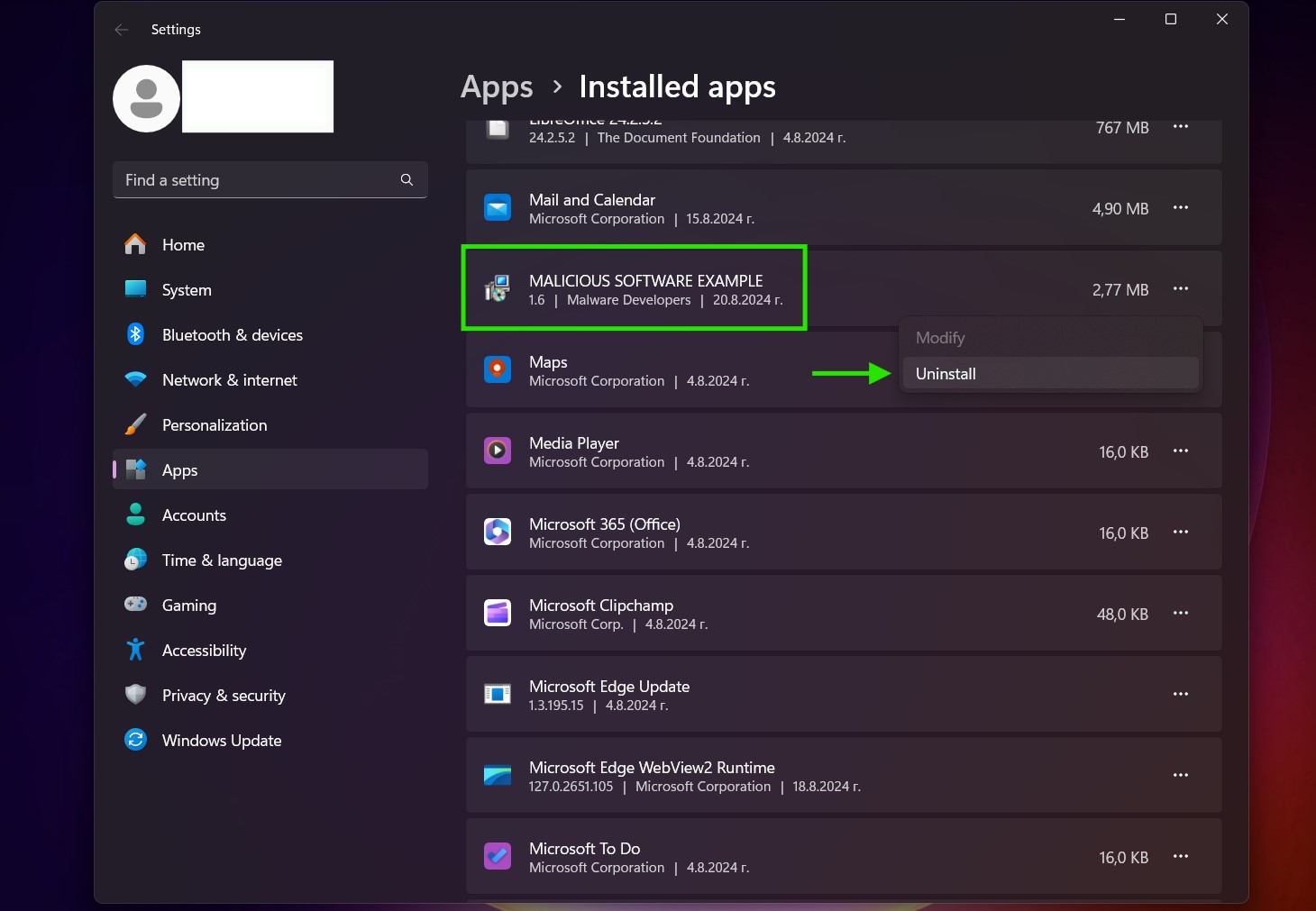
Uninstall Steps for Windows 10 and Older Versions
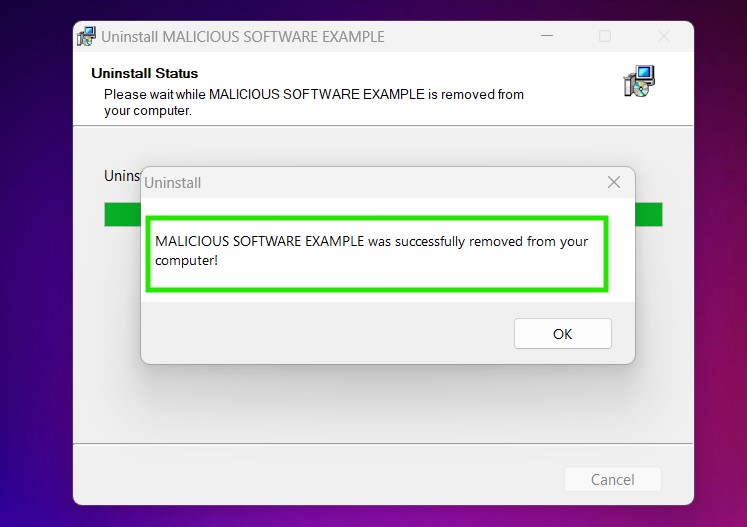
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by PayPal Phishing Scams on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by PayPal Phishing Scams there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for PayPal Phishing Scams (Windows).
Get rid of PayPal Phishing Scams from Mac OS X.
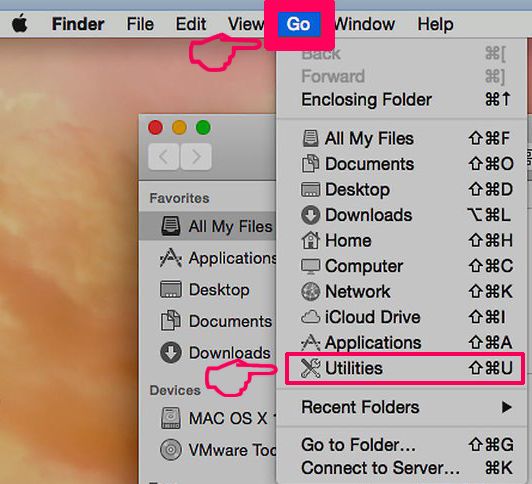
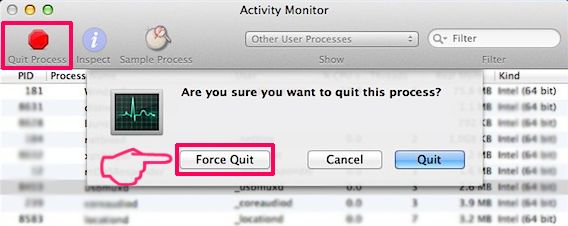
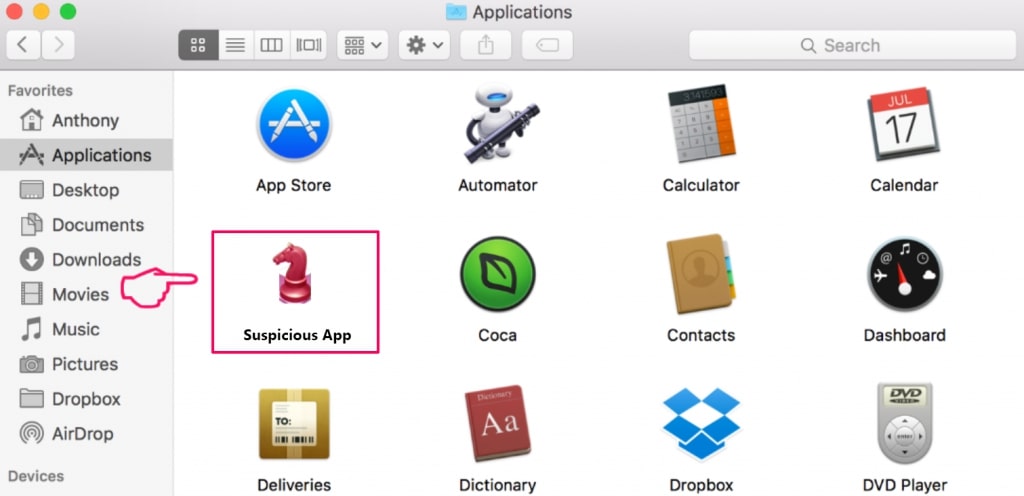
Step 1: Uninstall PayPal Phishing Scams and remove related files and objects
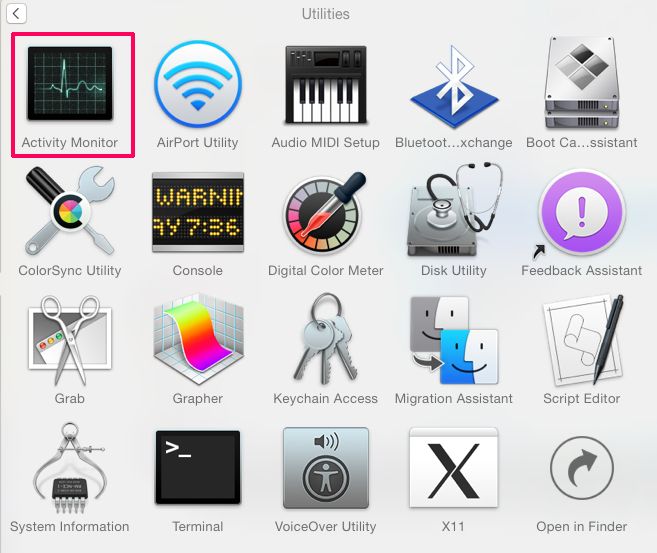
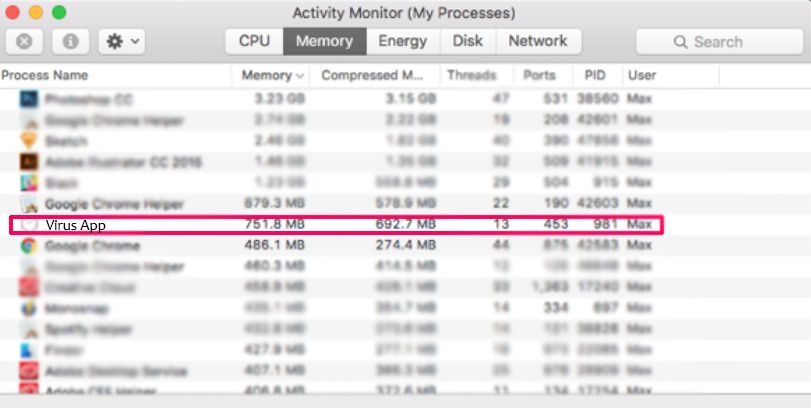
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to PayPal Phishing Scams. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove PayPal Phishing Scams via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
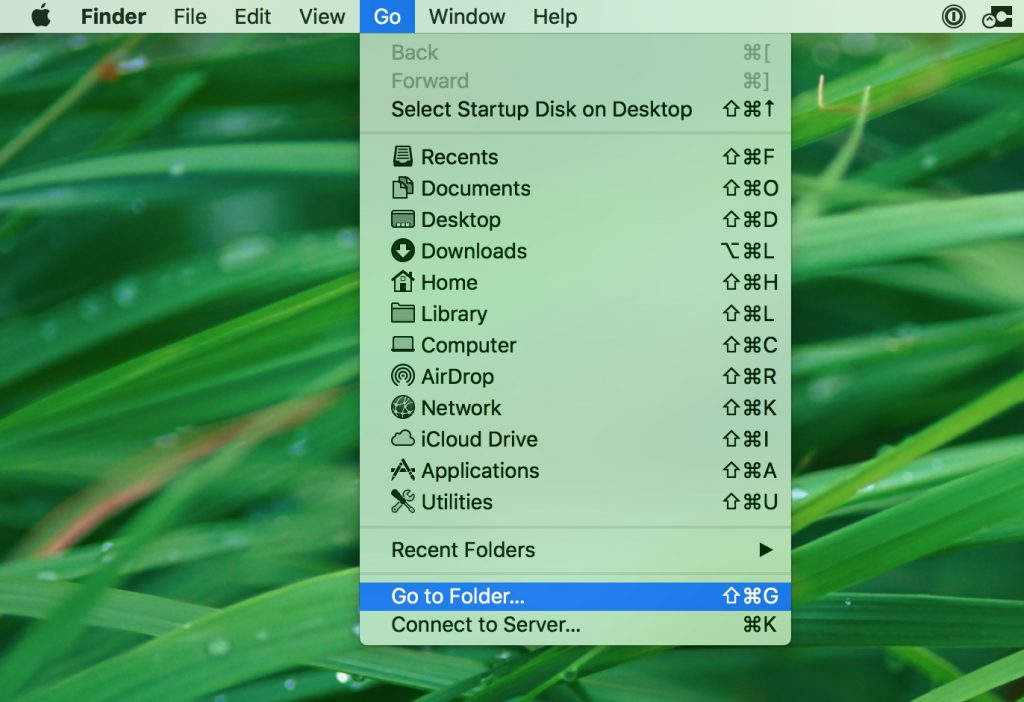
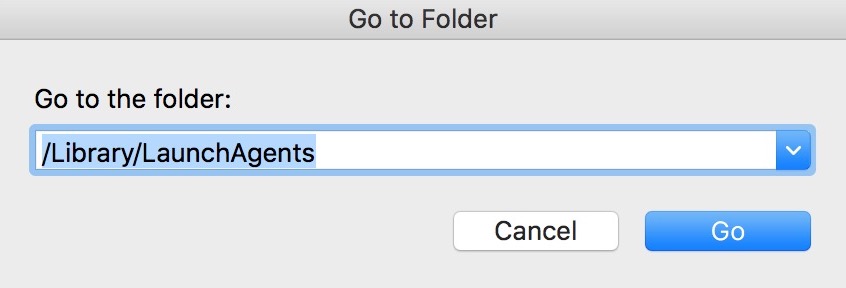
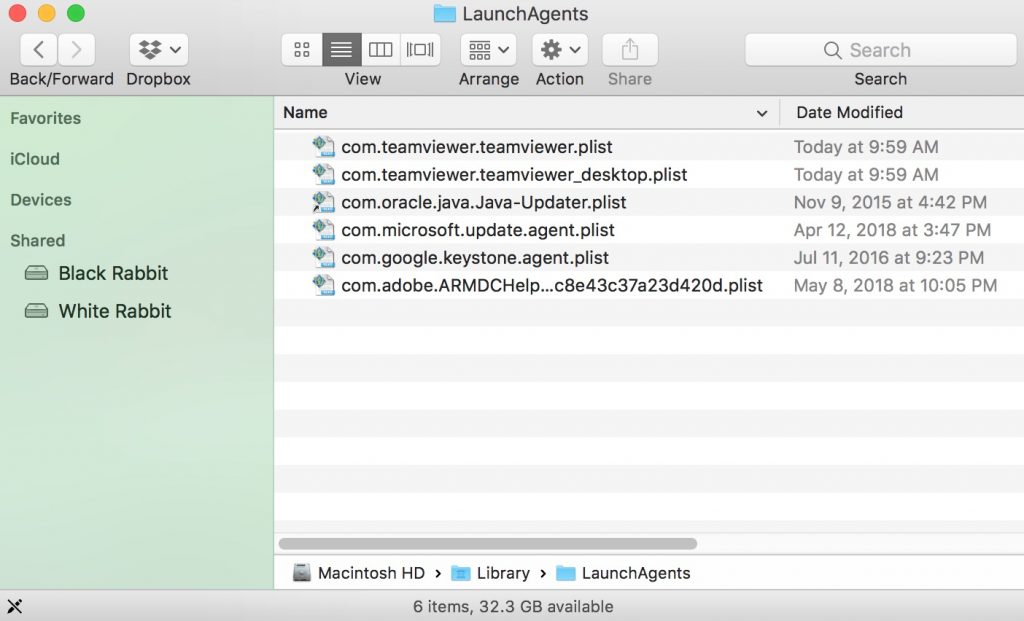
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove PayPal Phishing Scams files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as PayPal Phishing Scams, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for PayPal Phishing Scams (Mac)
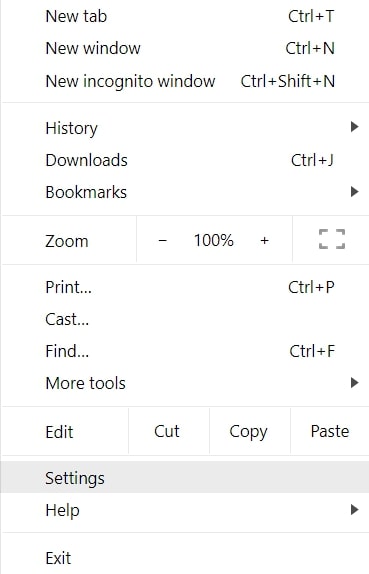
Remove PayPal Phishing Scams from Google Chrome.
Step 1: Start Google Chrome and open the drop menu
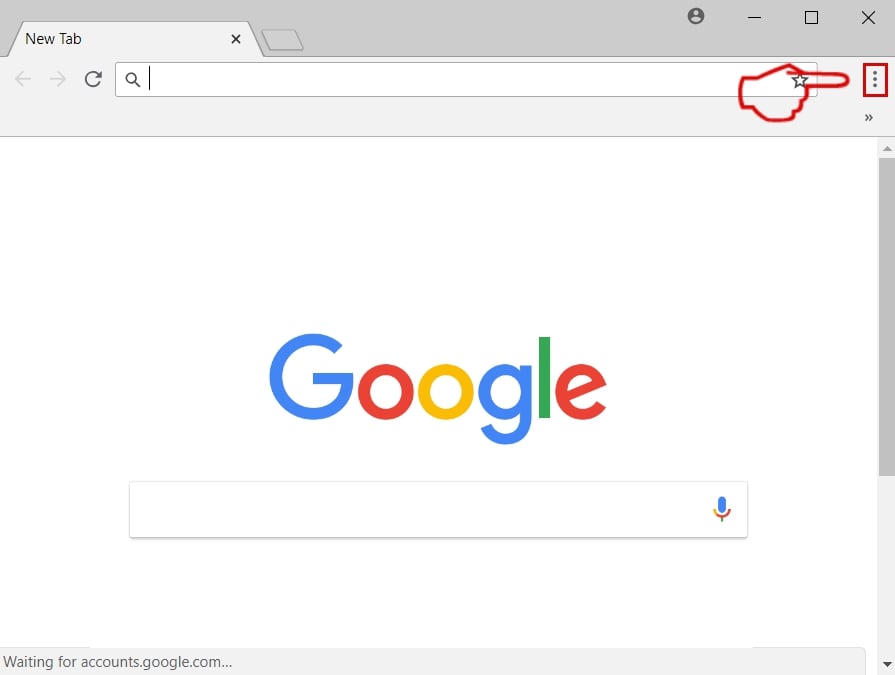
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
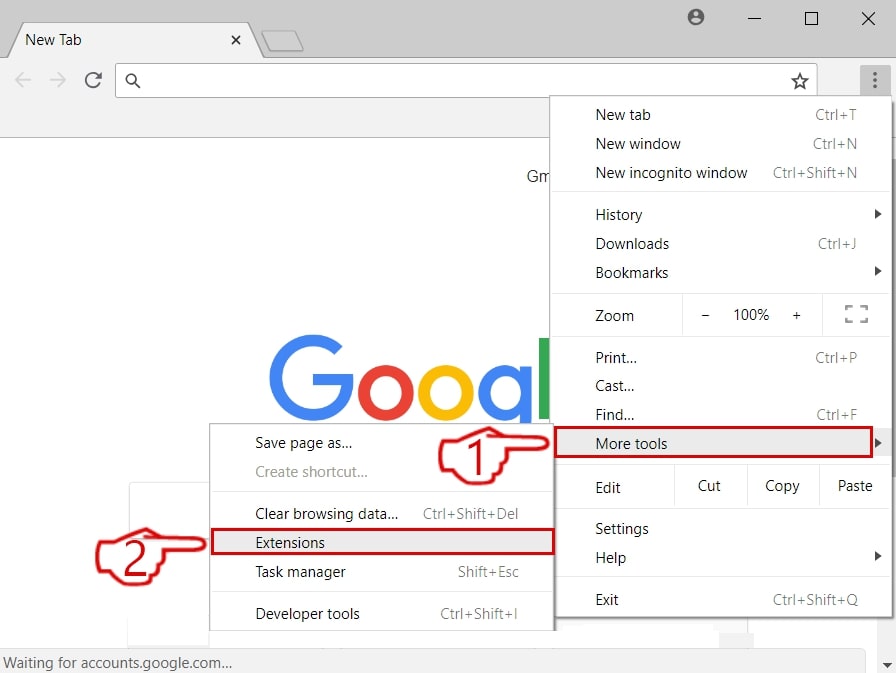
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
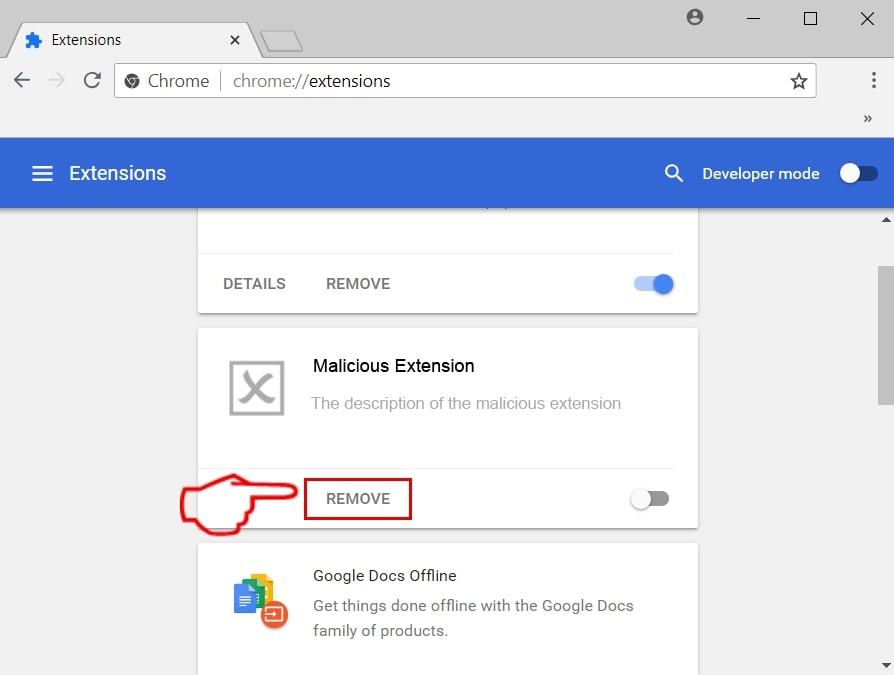
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase PayPal Phishing Scams from Mozilla Firefox.
Step 1: Start Mozilla Firefox. Open the menu window:
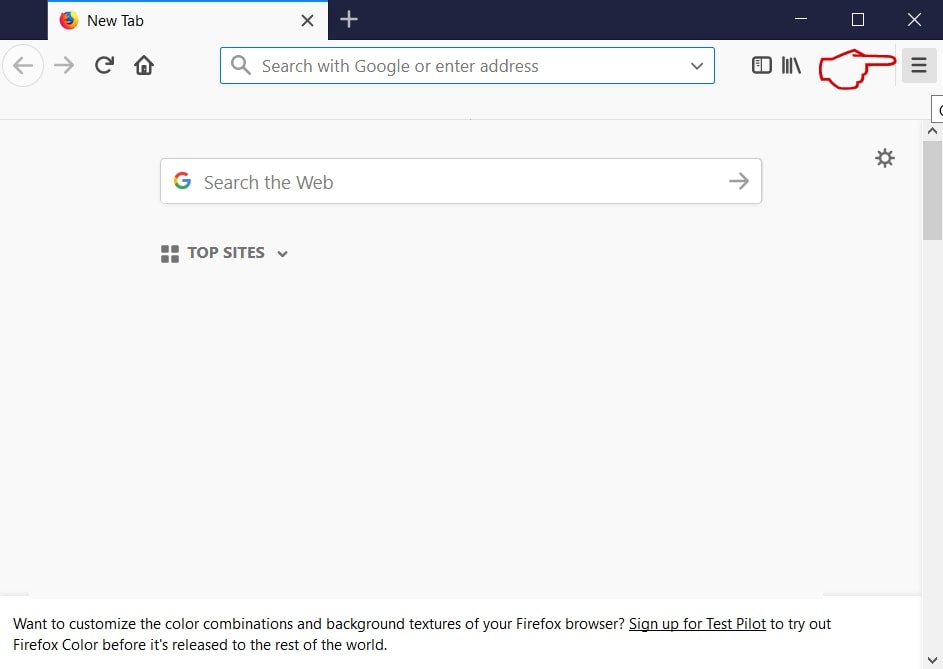
Step 2: Select the "Add-ons" icon from the menu.
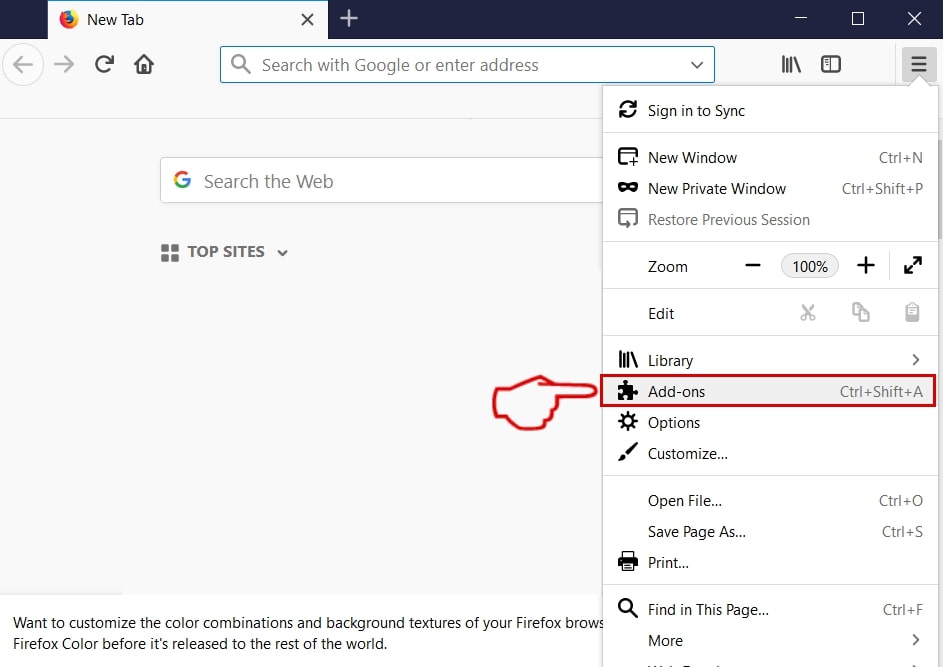
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
Uninstall PayPal Phishing Scams from Microsoft Edge.
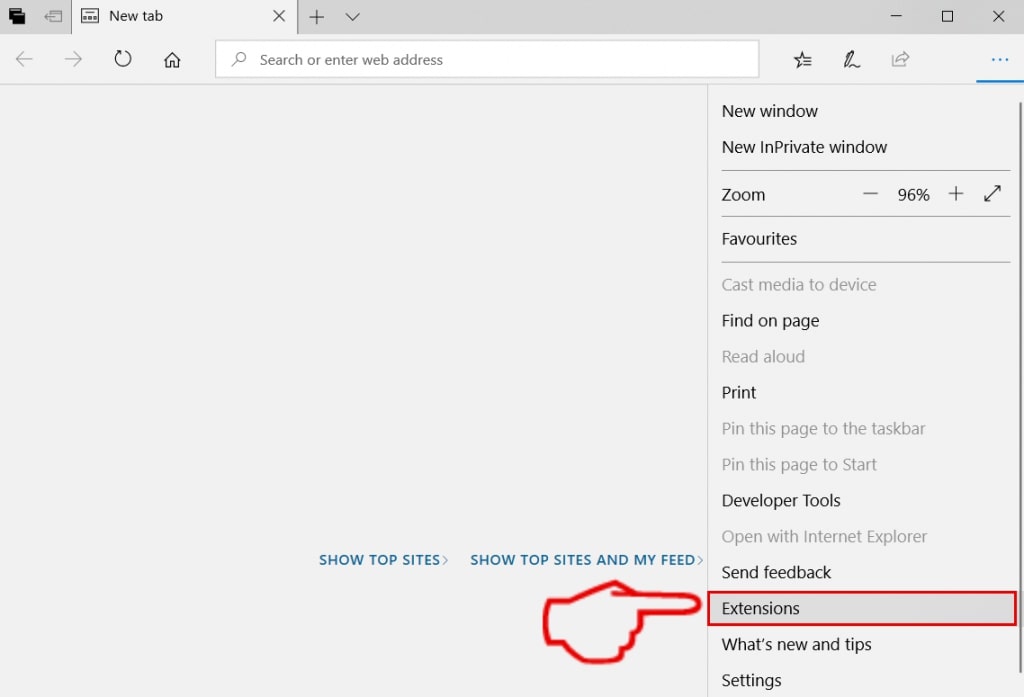
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
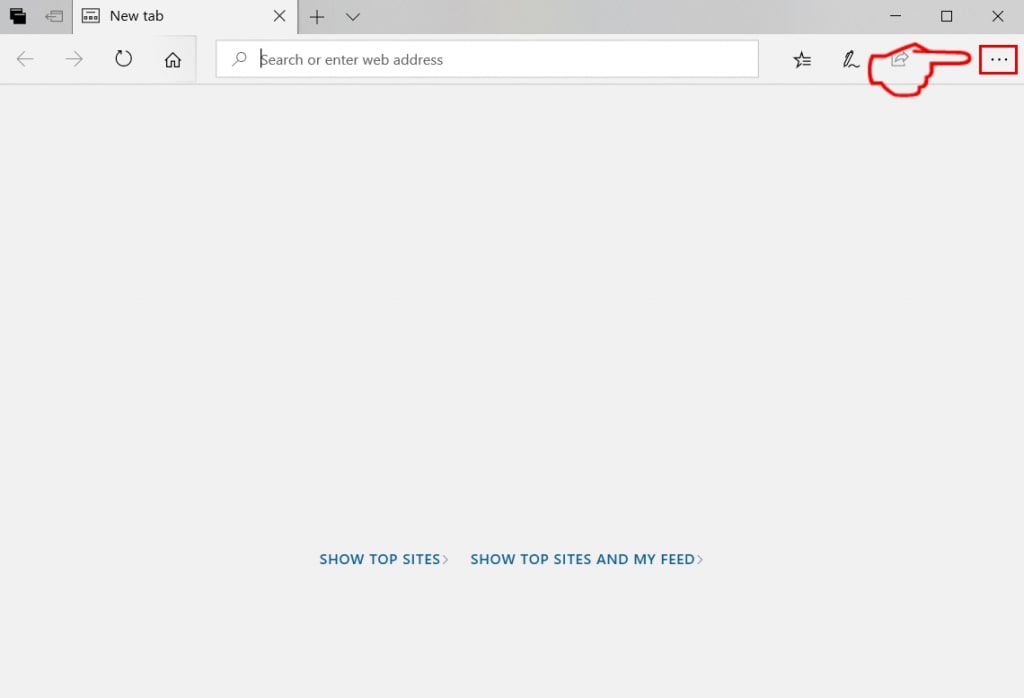
Step 3: From the drop menu select "Extensions".
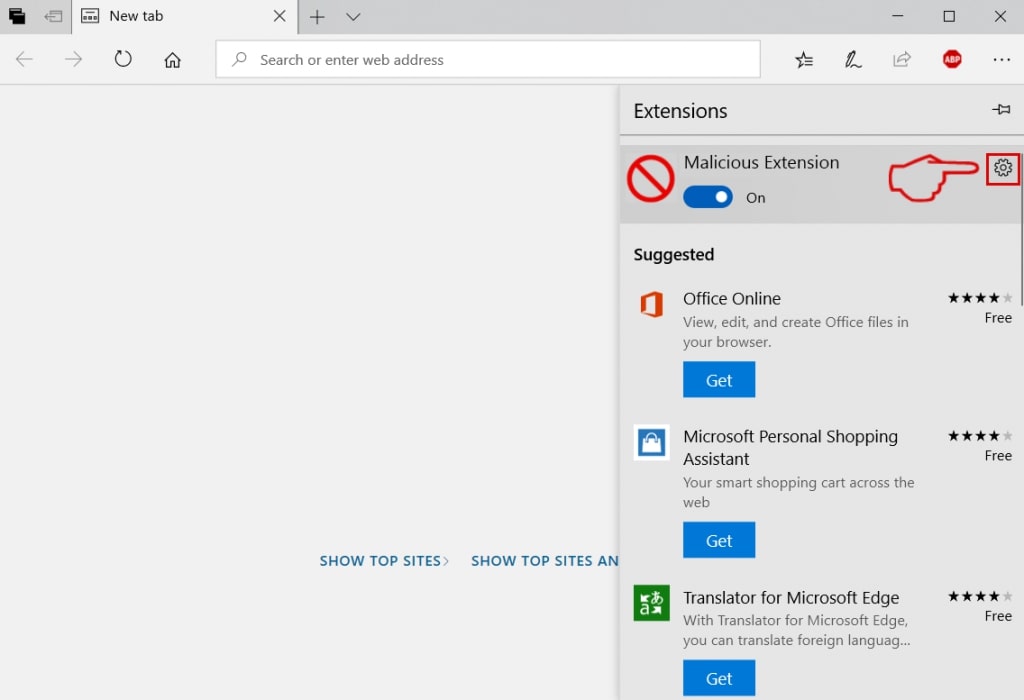
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
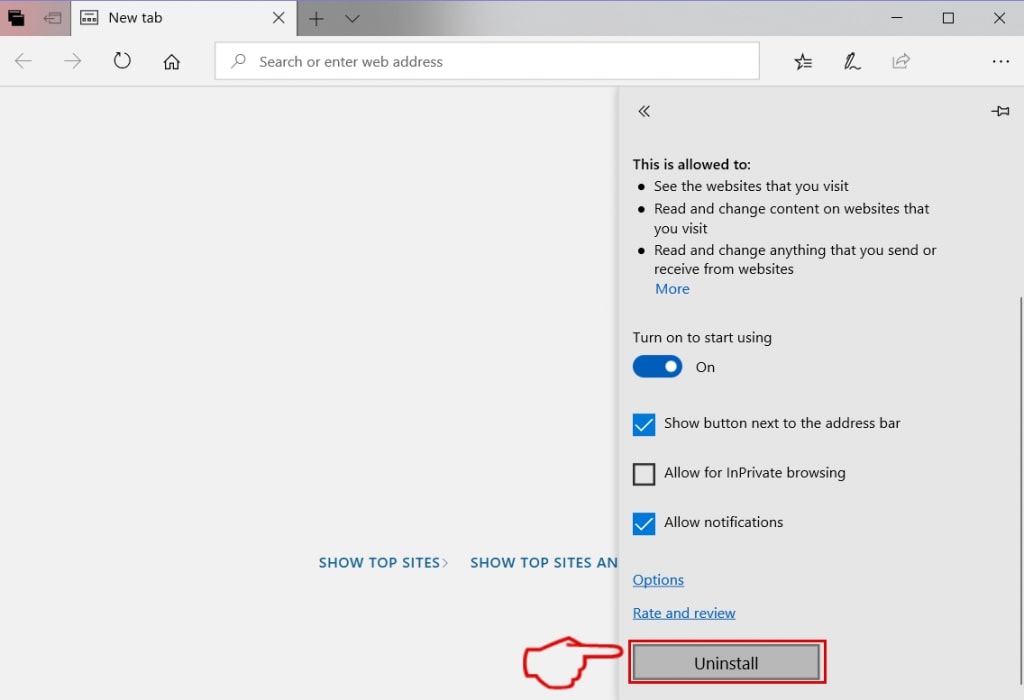
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
Remove PayPal Phishing Scams from Safari
Step 1: Start the Safari app.
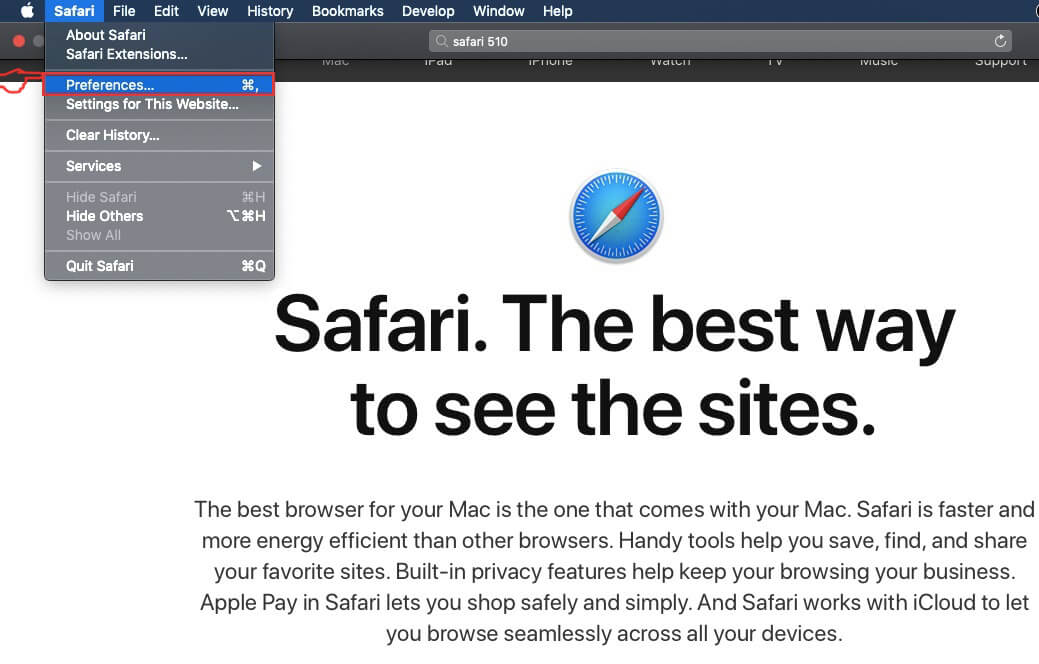
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
Step 4: After that, select the 'Extensions' Tab.
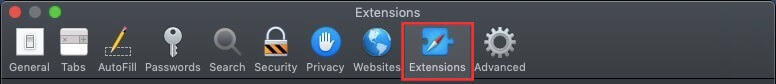
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
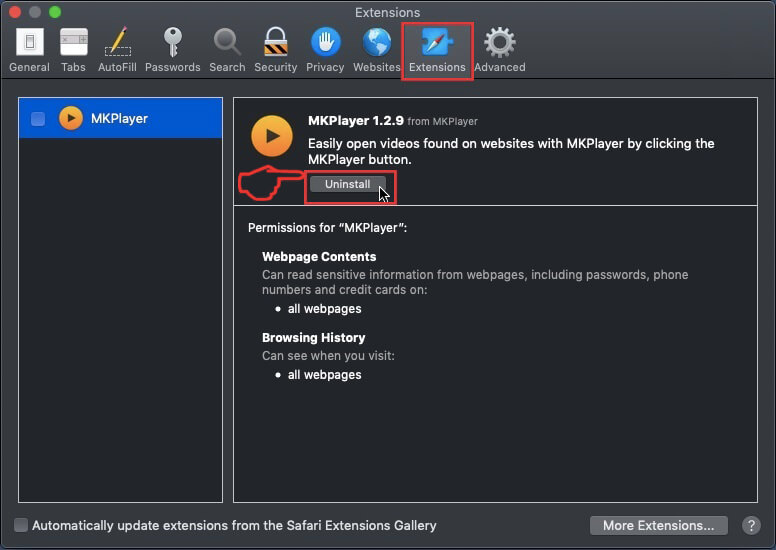
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the PayPal Phishing Scams will be removed.
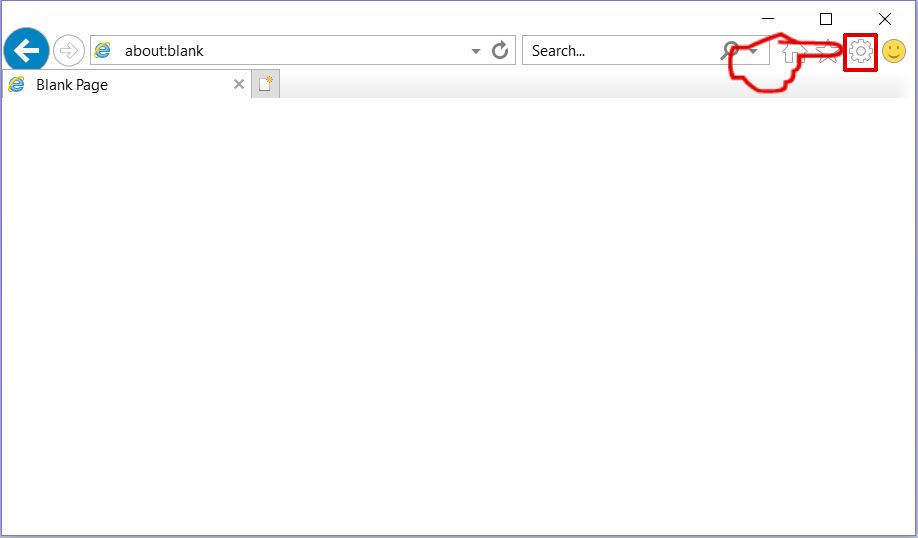
Eliminate PayPal Phishing Scams from Internet Explorer.
Step 1: Start Internet Explorer.
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
Step 3: In the 'Manage Add-ons' window.
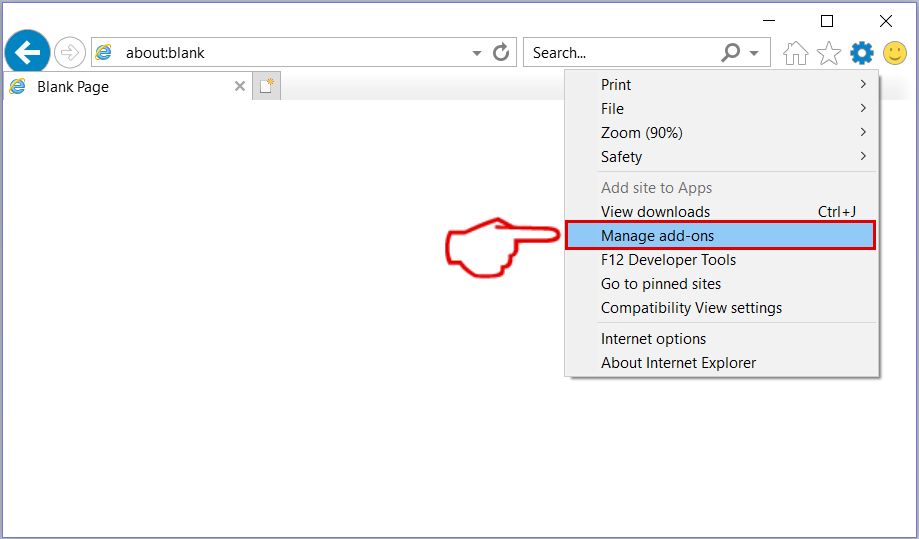
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
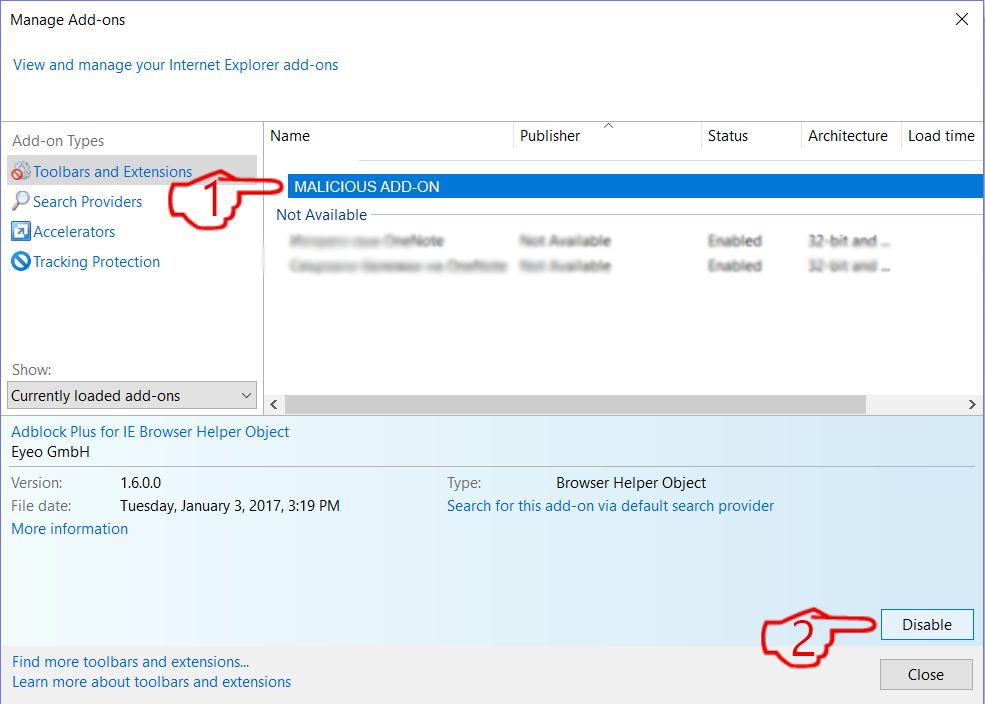
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
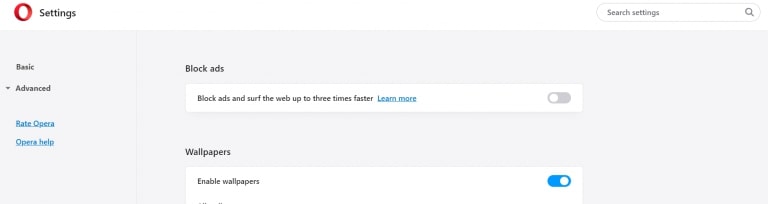
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
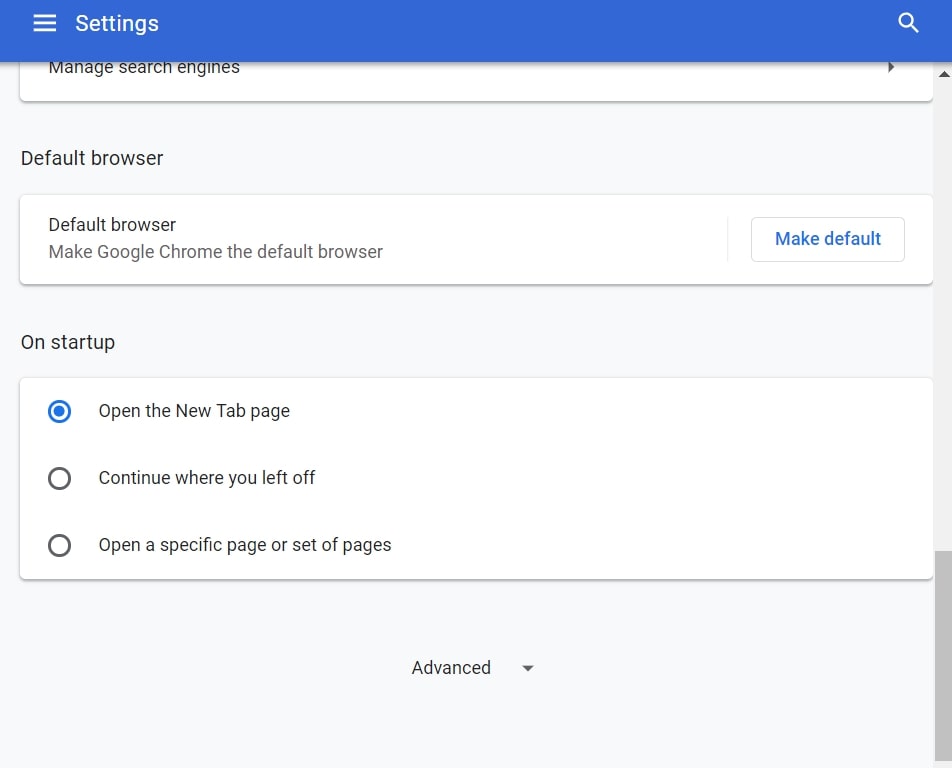
Step 3: Click “Content Settings”:
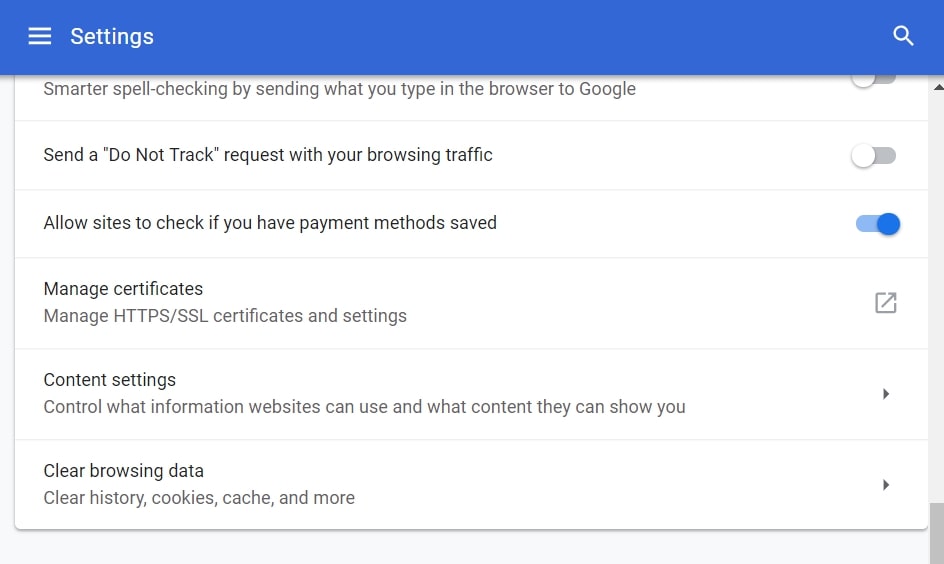
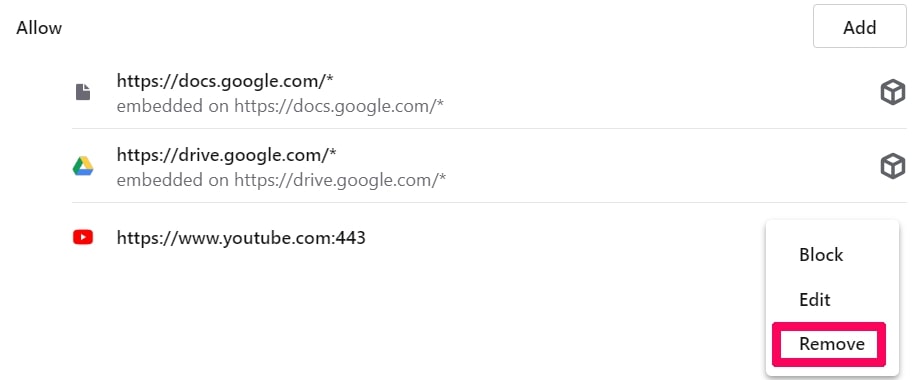
Step 4: Open “Notifications”:
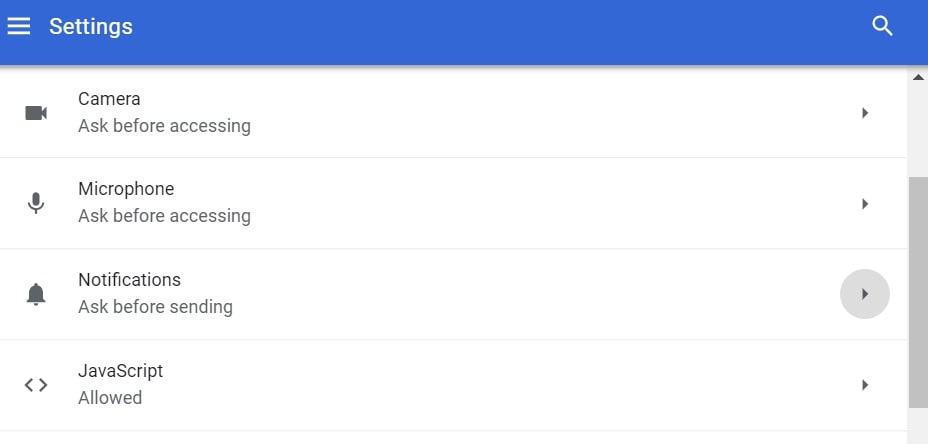
Step 5: Click the three dots and choose Block, Edit or Remove options:

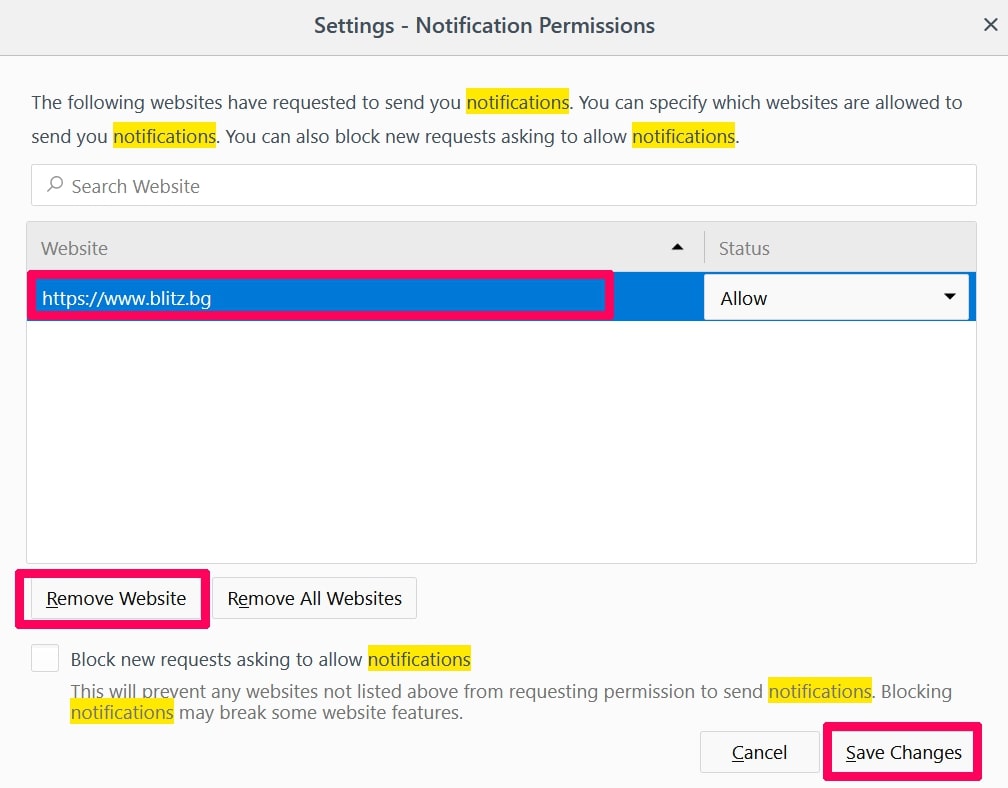
Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
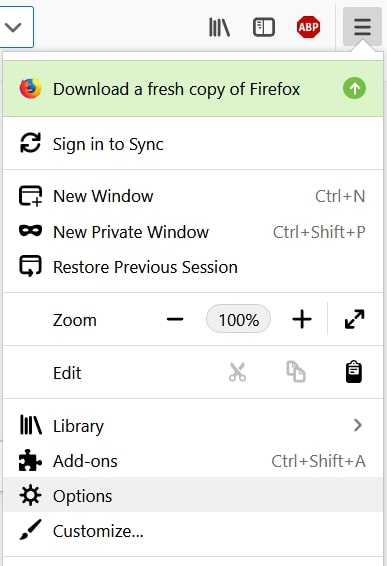
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
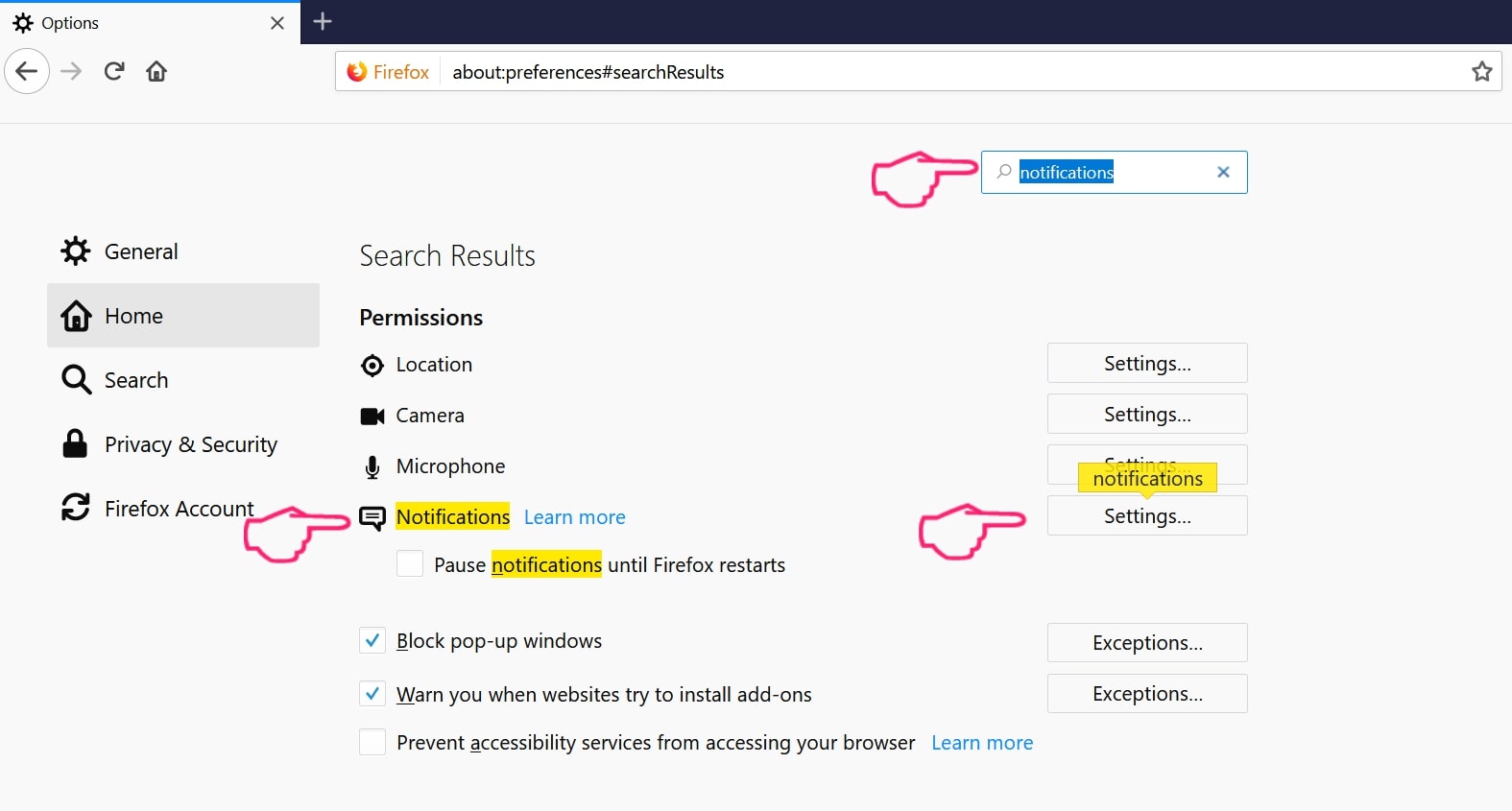
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
Step 2: In Setting search, type “Content” to go to Content Settings.
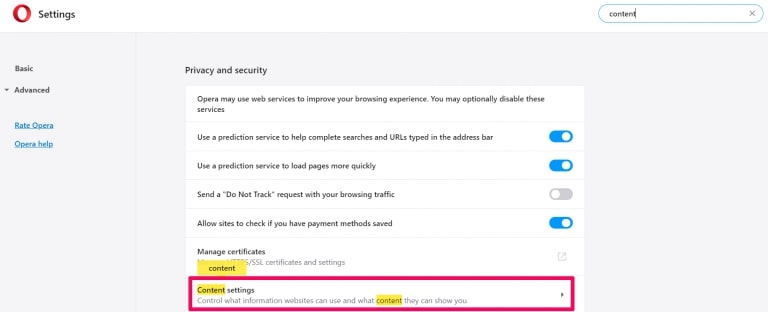
Step 3: Open Notifications:
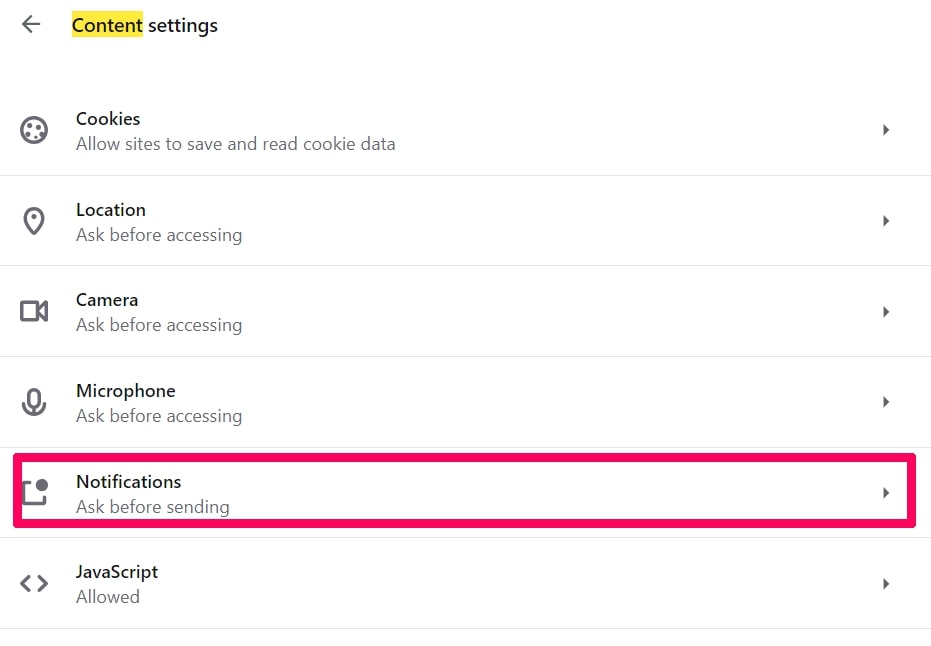
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
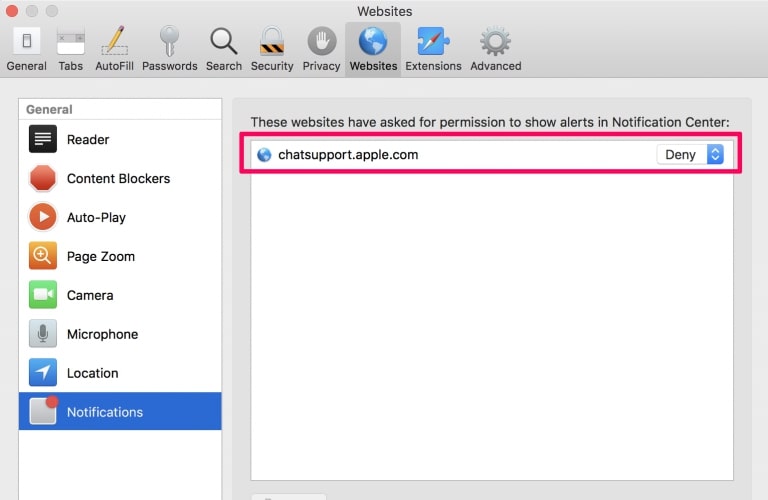
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
PayPal Phishing Scams-FAQ
What Is PayPal Phishing Scams?
The PayPal Phishing Scams threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of PayPal Phishing Scams?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like PayPal Phishing Scams?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does PayPal Phishing Scams Work?
Once installed, PayPal Phishing Scams can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
PayPal Phishing Scams can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is PayPal Phishing Scams Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the PayPal Phishing Scams Research
The content we publish on SensorsTechForum.com, this PayPal Phishing Scams how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on PayPal Phishing Scams?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the PayPal Phishing Scams threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.