 The creator behind the ransomware virus Petya which is connected to the recent ransomware outbreak which is still ongoing, has released the master decryption key. Dubbed Janus, the creator of Petya was not involved in the outbreak attacks and it was later established that his virus was pirated from another entity and then re-modified into what many call the NotPetya virus. It was later established by security experts that the new modified variant of Petya which hit last month was primarily created to be a cyber-weapon, than ransomware, because the virus cannot decrypt the files even if you pay the ransom. This brings us to the original author Janus who did not have anything to do with the threat and wanted to assist to the victims of the ransomware.
The creator behind the ransomware virus Petya which is connected to the recent ransomware outbreak which is still ongoing, has released the master decryption key. Dubbed Janus, the creator of Petya was not involved in the outbreak attacks and it was later established that his virus was pirated from another entity and then re-modified into what many call the NotPetya virus. It was later established by security experts that the new modified variant of Petya which hit last month was primarily created to be a cyber-weapon, than ransomware, because the virus cannot decrypt the files even if you pay the ransom. This brings us to the original author Janus who did not have anything to do with the threat and wanted to assist to the victims of the ransomware.
The Master Key Works for All Versions
Janus has officially released the master key of the virus, which was reported to work for all versions of Petya ransomware, including the GoldenEye infection.
The author (@JanusSecretary) has reportedly leaked the decryption keys in his tweet which lead to the download of a file, named natalya.aes-256-cbc.
The file, however is password-protected, bt it can easily be decrypted by security experts. After decryption process of the file with the key which is in AES-256 cipher in ECB encryption mode key that is secp192k1 private one is displayed. It is reported to be the following:
38dd46801ce61883433048d6d8c6ab8be18654a2695b4723
In a retrospect for all the Petya versions so far, the Red Petya which was the first virus has been cracked and hard drives encrypted by it can be successfully decoded, thanks to leo_and_stone(https://twitter.com/leo_and_stone) malware researcher. The second version of Red Petya, known as Green Petya or Mischa ransomware could be brute-forced and the key can be cracked for around 3 to 4 days.
The GoldenEye version, which is also a version of the Petya that came out later on, can be decrypted using this key.
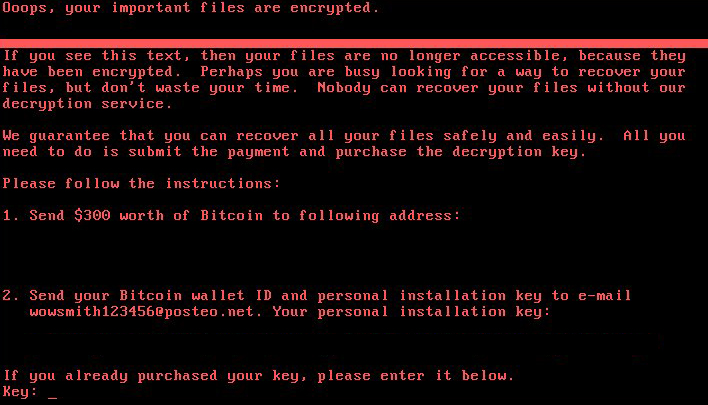
What cannot be decrypted however is the newest Petya variant, which many refer to as EternalPetya or NotPetya (PinkPetya). The main reason for this Is that the cyber-criminals behind the modified version of this virus have used a different public key to the one Janus has used and their keys (Salsa) are erased permanently. The ransomware also overwrites memory from the hard drive with empty space, which means it directly wipes it, instead of encrypting it – a very harsh action. The master key will however work for those variants of Petya:


