Have you ever heard of Qual ransomware and wondered just how much of a threat it poses to your digital security? This malicious software, part of the notorious DJVU ransomware family, has quickly gained infamy for encrypting files and demanding a ransom for their release, leaving victims in a bind over lost data.
In this comprehensive guide, we delve into the intricate workings of Qual ransomware, its encryption methods, and the significant risks it carries.
Whether it’s understanding the initial signs of infection or exploring the methods to remove and recover from an attack, we’ve got you covered. Plus, we’ll share essential tips and tools to help you bolster your defenses and prevent future ransomware attacks, ensuring you are well-prepared to protect your digital life.
![QUAL Virus [.qual Files] Remove + Decrypt Guide [Solved]](https://cdn.sensorstechforum.com/wp-content/uploads/2024/07/qual-files-virus-removal-guide-1024x576.jpg)
Qual Virus Details
| Name | Qual virus, also known as UDS:Trojan.Win32.Chapak.gen, Ransom:Win32/StopCrypt.KM!MTB, Win32:PWSX-gen [Trj], Win32:PWSX-gen [Trj], A Variant Of Win32/GenKryptik.FHJB – more detections of this virus on VirusTotal |
| File Extension | .qual |
| Type | Ransomware, Cryptovirus |
| Ransom Demanding Note | _readme.txt |
| Removal Time | 5 Minutes |
| Detection Tool |
Check if your Mac has been affected by Qual
Download
Malware Removal Tool
|
Understanding Qual Ransomware: What You Need to Know
Qual ransomware is a recent discovery within the DJVU ransomware family, identified by virus researcher Michael Gillespie. This ransomware is designed to encrypt files on the victim’s computer, appending a .qual extension, therefore rendering them inaccessible.
The presence of a ransom note (_readme.txt) in affected directories is a hallmark of this attack, demanding payment for file decryption. The critical nature of Qual ransomware lies in its ability to lock away personal or business-critical data, leading to potentially severe consequences for those unprepared.
Why is Qual Ransomware a Major Threat to Your Digital Security?
Qual ransomware represents a significant threat to digital security due to its encryption technique and the method used to spread. It’s not just the encryption of files that makes it perilous but also its strategy to extort ransom from victims. The cybercriminals behind this ransomware demand payment in exchange for a decryption key, which is held on a remote server under their control.
Furthermore, the dissemination of Qual ransomware through compromised software and adware bundles indicates a sophisticated level of distribution aimed at maximizing its impact. Its capacity to bypass traditional antivirus measures and encrypt files using a unique key for each victim accentuates the level of threat it poses to individuals and businesses alike.
The Encryption Mechanism Behind Qual Ransomware
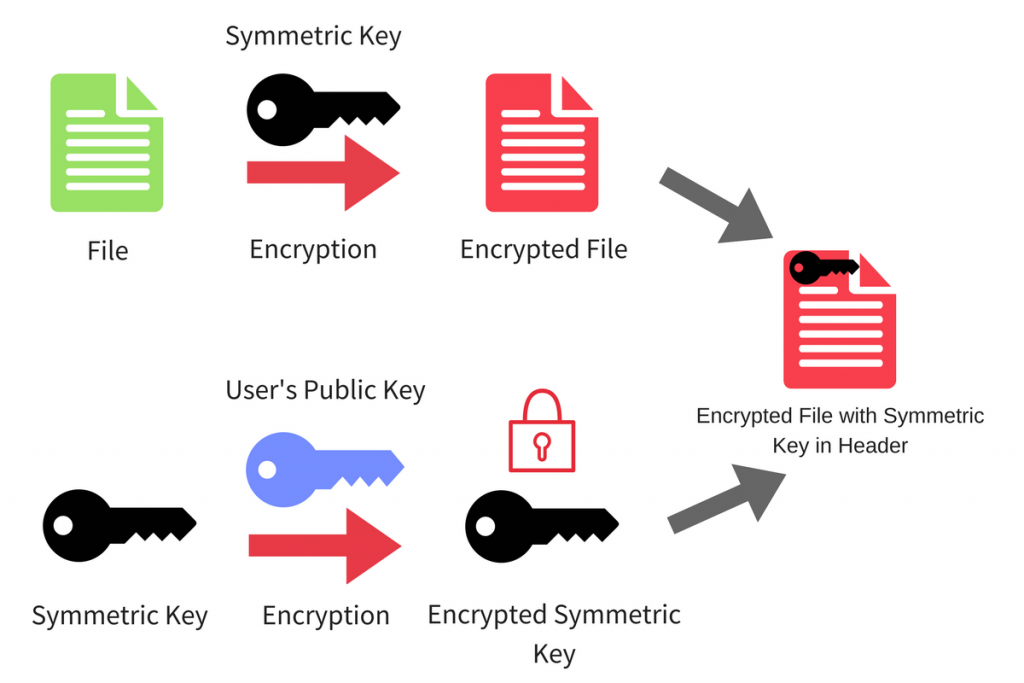
The encryption process utilized by Qual ransomware incorporates the Salsa20 encryption algorithm , noted for its robust security features.
What makes recovery particularly challenging is the unique decryption key generated for each victim, stored on a remote server managed by the attackers.
This individualized key approach means that a universal decryption tool is ineffective, complicating efforts to regain access to encrypted files without succumbing to ransom demands.
This methodology underscores the importance of proactive measures, such as maintaining up-to-date backups and employing reliable security software, to mitigate the risks associated with ransomware attacks.
In the context of defending against threats like Qual ransomware, utilizing a comprehensive security solution like SpyHunter can significantly enhance your computer’s defenses.
Its ability to detect and remove ransomware and other sophisticated malware in real-time can be a critical asset in maintaining your digital security. Remember, the strength of your defense against ransomware lies not only in the software you choose but also in practicing cautious online behavior and having a solid backup strategy.
First Signs of Qual Ransomware Infection: What to Look For
Ransomware like Qual can stealthily infiltrate your system, but there are early signs you might notice. A sudden inability to open files, renamed files with a new “.qual” extension, and an unexpected _readime.txt message on your desktop or in file folders should raise immediate concerns.
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
Do not ask assistants from youtube and recovery data sites for help in recovering your data.
They can use your free decryption quota and scam you.
Our contact is emails in this text document only.
You can get and look video overview decrypt tool.
Price of private key and decrypt software is $999.
Discount 50% available if you contact us first 72 hours, that’s price for you is $499.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
0876qualrsa_pubkey.plain
—–BEGIN PUBLIC KEY—–
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA2iF2z8qTGWyGMtNhPR7G
MGAf/Cj6VowurSUOyORyuV6zmACc4fML4hGZe2+jMtlmPuDm9AKDe2A7ktEm+8AV
WTov1Vz9zeVkt6hy7KlP+fM+wTiEtwbYALKQV0RCYHyhH8z36Dco/dcL+M+OSwcd
J9jJ5VBro0+QMbS+FRjk0GS4DwzprGjSwPLJWp4H1iZHhEcUplB4krFkwsyNfhb/
aiJzA/4ZYz/+hPdv9YQxd3R+bgv2LdzV605176wsakPezqJxUSHxOEkkpYP4P149
XsXG76vTNjWPRW/M3+oKBtMvAXzMYuRR9q1peV++b1l6hgkiuqDicGvT9JPCUDld
4QIDAQAB
—–END PUBLIC KEY—–
These signs indicate that the ransomware has started encrypting your data. You might also experience a slower computer performance as the ransomware works in the background. Recognizing these signs early on can be crucial in preventing further damage.
Identifying Qual Ransomware on Your System
You can confirm a Qual ransomware infection through specific indicators. First, check your files for the “.qual” extension, a definitive sign that they’ve been encrypted. Secondly, locate the ransom note, usually named _readme.txt, which provides instructions from the attackers.
This note is left in folders containing encrypted files. Additionally, you might find that system recovery options, such as Volume Shadow copies, have been disabled, further signifying the presence of Qual ransomware on your device.
Deciphering the Ransom Note: Guidance and Misdirection
The ransom note left by Qual ransomware is both a guide and a misdirect. It informs victims about the encryption and demands a ransom for a decryption key, claiming that paying the ransom is the only way to recover files.
Among the main risky activities of this malware on your device are:
- Checks computer location settings.
- Looks up country code configured in the registry, likely geofence.
- Modifies file permissions.
- Adds Run key to start application.
- Looks up external IP address via web service.
- Suspicious use of SetThreadContext
- Uses a legitimate IP lookup service to find the infected system’s external IP.
The note might offer to decrypt a single file for free as “proof” of their ability to reverse the encryption. However, following the ransom note’s instructions often leads to financial loss without data recovery. Cybersecurity experts strongly advise against paying the ransom.
The note’s promises are unreliable, and paying can further encourage criminals. Instead, affected users should focus on safe recovery methods and protect their systems against future attacks.
Proven Methods to Remove Qual Ransomware From Your Computer
When your computer falls victim to Qual ransomware, it is a serious blow to your data’s integrity and safety. Removing this malicious software promptly and correctly is essential.
Two predominant methods emerge for dealing with this threat: manual removal and employing a professional approach. Manual removal may appeal to those with technical skills, as it involves navigating the system’s depths to identify and eradicate the malware’s components.
However, this method is not without risks. It might not only prove time-consuming but also poses the threat of accidental deletion of essential files, further complicating the system’s state.
On the other hand, a professional approach, utilizing reliable security software, offers a safer and more efficient solution. Security programs are specifically designed to detect and remove such threats without jeopardizing the system’s integrity. This approach saves time and ensures that no remnants of the ransomware remain.
Manual Removal vs. a Professional Approach: What Works, Best?
Deciding between manual removal and professional intervention hinges on several factors, including the user’s technical expertise, the severity of the infection, and the value of the data at risk.
While manual removal may grant immediate, albeit risky, results, a professional approach using advanced malware removal tools embodies a safer, more reliable solution. Choosing a reputable and powerful antivirus or anti-malware software can make a significant difference in effectively neutralizing threats like Qual ransomware without risking further damage to your system or files.
Decrypting Your Files: Can You Restore Your Data?
Discovering that your personal files have been encrypted by ransomware can be incredibly stressful. However, understanding your options for potentially decrypting those files can provide a glimmer of hope. When dealing with the Qual ransomware, it’s essential to assess the situation realistically to determine the feasibility of restoring your data.
Understanding the Feasibility of Qual File Decryption
The Qual ransomware, a variant of the STOP/Djvu family, employs strong encryption methods that often make file recovery challenging without the decryption key. In instances where Qual utilizes an offline key, there’s a higher chance of successful decryption with available tools.
Nonetheless, it’s important to recognize that each case varies significantly based on the ransomware’s attack specifics and the affected files’ nature.
Before attempting any recovery efforts, it’s crucial to remove the ransomware from your system to prevent further encryption. Utilizing reputable security software like SpyHunter can efficiently identify and eliminate threats, setting a clean stage for file recovery attempts.
Free Tools vs. Paid Services: Evaluating Your Options for File Recovery
Several free tools and resources can assist in the recovery of files encrypted by ransomware like Qual. Tools such as the STOP Decryptor cater to specific ransomware strains and may offer a solution for recovering your files without the need to pay a ransom.
However, the success rate of these tools hinges on whether the ransomware used a unique or a generic key for encryption.
While free tools present a cost-effective method to attempt file recovery, their effectiveness is not guaranteed. Complex ransomware variants might render these tools less successful.
On the other hand, paid file recovery services offer specialized expertise and might have access to more advanced decryption technologies. Although they come with a cost, these services might increase your chances of recovering valuable data.
Regardless of the chosen recovery method, it’s vital to maintain realistic expectations and prepare for the possibility that not all files can be restored. Regularly backing up your data remains the most reliable defense against data loss due to ransomware.
Preventing Future Ransomware Attacks: Essential Tips and Tools
In today’s digital world, safeguarding your computer against ransomware attacks is more crucial than ever. Ransomware, a type of malicious software that threatens to publish the victim’s data or perpetually block access to it unless a ransom is paid, has seen a significant rise.
However, there are proactive measures you can take to fortify your security posture and significantly reduce the risk of falling victim to such attacks.
Strengthen Your Defense: Practical Security Habits to Adopt
Building a strong line of defense against ransomware involves more than just installing any security software; it requires adopting a constellation of diligent habits and practices. Here are some essential steps everyone should follow:
- Be cautious of suspicious emails and links: Always scrutinize emails, especially those with attachments or links, even if they appear to come from known contacts. Phishing scams are a common entry point for ransomware.
- Download software from reputable sources: Avoid downloading applications from third-party websites. Always opt for official websites or verified stores to reduce the risk of accidental malware installation.
- Keep your software updated: Regular updates are crucial as they often include patches for security vulnerabilities that could otherwise be exploited by hackers to deliver ransomware.
- Use robust security software: Not all security programs are created equal. Choose a reliable anti-malware solution like SpyHunter that delivers comprehensive protection against a wide range of malware, including ransomware.
- Enable on-run protection: Features that prevent the execution of malware-infected files can be a critical line of defense. SpyHunter offers capabilities to identify potential threats before they wreak havoc.
By integrating these practices into your regular computing habits, you create a formidable barrier that can deter most ransomware attacks, keeping your data secure and your peace of mind intact.
Why Regular Backups Can Be Your Best Defense Against Ransomware
While adopting strong preventive measures is essential, having a reliable backup strategy can act as a fail-safe in the event of a ransomware attack. Regular backups can significantly mitigate the risks associated with such threats, here’s how:
- Minimize data loss: Regularly backing up your important files means that in the case of an attack, you can restore your data from a point before the infection occurred, minimizing data loss.
- Reduce reliance on terrorists: If your files are securely backed up, the leverage that ransomware attackers hold over you diminishes. This means you don’t have to consider paying the ransom, which is never a guaranteed solution.
- Multiple backup locations: Storing your backups in multiple locations, including offline storage, offers an added layer of security. Even if one backup is compromised, others remain intact.
Effectively, regular backups not only serve as an essential component of your cybersecurity strategy but also ensure continuity for businesses and peace of mind for individuals. By understanding and implementing these recommendations, you can significantly enhance your defense mechanisms against the ever-evolving threat of ransomware.
Success Stories: How Victims Successfully Recovered Their Data
The fight against Qual ransomware is far from hopeless. Many have found paths to data recovery that did not involve succumbing to the demands of cybercriminals. For instance, one common theme among success stories is the utility of backup systems.
Victims who had maintained regular backups of their data to external drives or cloud storage services were able to restore the majority of their files following an attack.
It’s critical to note, however, that success often depended on these backups being disconnected from the main network at the time of infection, highlighting the importance of offline or cloud-based backup strategies.
Another vein of success comes through the use of data recovery tools. As mentioned, Qual ransomware does not always permanently delete the original files but rather makes them inaccessible through encryption.
Tools for data recovery have been instrumental in retrieving lost data for some, particularly when used promptly before the lost data could be overwritten by new files.
Additionally, the discovery of flaws within the ransomware’s encryption algorithm occasionally provides another avenue for data recovery.
In rare instances, cybersecurity researchers have been able to exploit these weaknesses to develop decryption tools that can unlock files without the need for the ransomware’s decryption key.
When Data Recovery Isn’t Possible: Learning from Loss
Unfortunately, not all stories end with successful data recovery. In cases where backups were not available, recovery tools ineffective, and decryption keys unobtainable, individuals and organizations have faced the harsh reality of permanent data loss.
Such scenarios underscore the critical lesson of the importance of proactive measures against ransomware attacks. The implementation of robust cybersecurity practices, such as regular system updates, avoidance of suspicious email attachments and links, and the use of reputable security software like SpyHunter, is crucial in defending against ransomware infections.
Learning from these experiences also means acknowledging the importance of education on cyber threats. Awareness of how ransomware spreads and the early signs of an infection can enable individuals and organizations to respond more effectively, potentially mitigating damage before it becomes irreparable.
In conclusion, while the threat of Qual ransomware and its ilk looms large, the tales of both triumph and hardship serve as invaluable lessons. They remind us of the power of preparedness, the potential for recovery, and the unyielding human spirit in the face of adversity. Let these stories inspire not only caution but also a commitment to fostering more secure digital environments for all.
Closing Thoughts: A Resilient Approach to Digital Security
In today’s interconnected world, the importance of maintaining robust digital security cannot be overstated. As we navigate through an ocean of digital information and resources, the challenges of protecting our data and privacy become increasingly complex.
However, adopting a resilient approach towards digital security can significantly mitigate these challenges, providing peace of mind and safeguarding our digital presence.
A resilient approach to digital security involves several key strategies. First and foremost, staying informed about the latest security threats and understanding how they can impact our digital activities is crucial.
This knowledge enables us to anticipate potential risks and take proactive measures to avoid them. Additionally, implementing strong, unique passwords and changing them regularly can drastically reduce the likelihood of unauthorized access to our personal and professional accounts.
- Regularly update software and security applications to protect against known vulnerabilities and exploit attempts.
- Deploy a reliable security solution, like SpyHunter, that offers comprehensive protection against malware, ransomiership, and other cyber threats.
- Practice cautious online behavior by avoiding suspicious links, verifying the authenticity of emails before responding, and being wary of sharing personal information on unsecured websites.
- Back up important data consistently to ensure that, in the event of a cyber-attack, recovery is possible with minimal loss.
Moreover, fostering a culture of security within organizations and among peers can amplify individual efforts, creating a more formidable defense against cyber threats. This involves sharing knowledge about best security practices and encouraging a collective responsibility towards digital hygiene.
In essence, resilience in digital security is not just about employing the right tools, like SpyHunter, but also about adopting a mindset that prioritizes vigilance, education, and collaboration in the face of evolving cyber threats.
In conclusion, securing our digital environment requires more than just advanced technology; it demands a thorough understanding of the digital threats we face and a committed approach to mitigating them.
By embracing a resilient strategy that combines knowledge, preparedness, and the right security solutions, we can navigate the digital world with confidence, protecting ourselves and others from the myriad of cyber risks that abound in this digital era.
- Step 1
- Step 2
- Step 3
- Step 4
- Step 5
Step 1: Scan for Qual with SpyHunter Anti-Malware Tool



Ransomware Automatic Removal - Video Guide
Step 2: Uninstall Qual and related malware from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Step 3: Clean any registries, created by Qual on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Qual there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Boot Your PC In Safe Mode to isolate and remove Qual





Step 5: Try to Restore Files Encrypted by Qual.
Method 1: Use STOP Decrypter by Emsisoft.
Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.
Follow the instructions below to use the Emsisoft decrypter and decrypt your files for free. You can download the Emsisoft decryption tool linked here and then follow the steps provided below:
1 Right-click on the decrypter and click on Run as Administrator as shown below:

2. Agree with the license terms:

3. Click on "Add Folder" and then add the folders where you want files decrypted as shown underneath:

4. Click on "Decrypt" and wait for your files to be decoded.

Note: Credit for the decryptor goes to Emsisoft researchers who have made the breakthrough with this virus.
Method 2: Use data recovery software
Ransomware infections and Qual aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on the top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
Qual-FAQ
What is Qual Ransomware?
Qual is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files.
Many ransomware viruses use sophisticated encryption algorithms to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back.
What Does Qual Ransomware Do?
Ransomware in general is a malicious software that is designed to block access to your computer or files until a ransom is paid.
Ransomware viruses can also damage your system, corrupt data and delete files, resulting in the permanent loss of important files.
How Does Qual Infect?
Via several ways.Qual Ransomware infects computers by being sent via phishing emails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users.
Another way you may become a victim of Qual is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents.
How to Open .Qual files?
You can't without a decryptor. At this point, the .Qual files are encrypted. You can only open them once they are decrypted using a specific decryption key for the particular algorithm.
What to Do If a Decryptor Does Not Work?
Do not panic, and backup the files. If a decryptor did not decrypt your .Qual files successfully, then do not despair, because this virus is still new.
Can I Restore ".Qual" Files?
Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore .Qual files.
These methods are in no way 100% guaranteed that you will be able to get your files back. But if you have a backup, your chances of success are much greater.
How To Get Rid of Qual Virus?
The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti-malware program.
It will scan for and locate Qual ransomware and then remove it without causing any additional harm to your important .Qual files.
Can I Report Ransomware to Authorities?
In case your computer got infected with a ransomware infection, you can report it to the local Police departments. It can help authorities worldwide track and determine the perpetrators behind the virus that has infected your computer.
Below, we have prepared a list with government websites, where you can file a report in case you are a victim of a cybercrime:
Cyber-security authorities, responsible for handling ransomware attack reports in different regions all over the world:
Germany - Offizielles Portal der deutschen Polizei
United States - IC3 Internet Crime Complaint Centre
United Kingdom - Action Fraud Police
France - Ministère de l'Intérieur
Italy - Polizia Di Stato
Spain - Policía Nacional
Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Greece - Cyber Crime Unit (Hellenic Police)
India - Mumbai Police - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
Reports may be responded to in different timeframes, depending on your local authorities.
Can You Stop Ransomware from Encrypting Your Files?
Yes, you can prevent ransomware. The best way to do this is to ensure your computer system is updated with the latest security patches, use a reputable anti-malware program and firewall, backup your important files frequently, and avoid clicking on malicious links or downloading unknown files.
Can Qual Ransomware Steal Your Data?
Yes, in most cases ransomware will steal your information. It is a form of malware that steals data from a user's computer, encrypts it, and then demands a ransom in order to decrypt it.
In many cases, the malware authors or attackers will threaten to delete the data or publish it online unless the ransom is paid.
Can Ransomware Infect WiFi?
Yes, ransomware can infect WiFi networks, as malicious actors can use it to gain control of the network, steal confidential data, and lock out users. If a ransomware attack is successful, it could lead to a loss of service and/or data, and in some cases, financial losses.
Should I Pay Ransomware?
No, you should not pay ransomware extortionists. Paying them only encourages criminals and does not guarantee that the files or data will be restored. The better approach is to have a secure backup of important data and be vigilant about security in the first place.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, the hackers may still have access to your computer, data, or files and may continue to threaten to expose or delete them, or even use them to commit cybercrimes. In some cases, they may even continue to demand additional ransom payments.
Can a Ransomware Attack Be Detected?
Yes, ransomware can be detected. Anti-malware software and other advanced security tools can detect ransomware and alert the user when it is present on a machine.
It is important to stay up-to-date on the latest security measures and to keep security software updated to ensure ransomware can be detected and prevented.
Do Ransomware Criminals Get Caught?
Yes, ransomware criminals do get caught. Law enforcement agencies, such as the FBI, Interpol and others have been successful in tracking down and prosecuting ransomware criminals in the US and other countries. As ransomware threats continue to increase, so does the enforcement activity.
About the Qual Research
The content we publish on SensorsTechForum.com, this Qual how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific malware and restore your encrypted files.
How did we conduct the research on this ransomware?
Our research is based on an independent investigation. We are in contact with independent security researchers, and as such, we receive daily updates on the latest malware and ransomware definitions.
Furthermore, the research behind the Qual ransomware threat is backed with VirusTotal and the NoMoreRansom project.
To better understand the ransomware threat, please refer to the following articles which provide knowledgeable details.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum’s recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Always check "About Us" web page.
- Profile of the content creator.
- Make sure that real people are behind the site and not fake names and profiles.
- Verify Facebook, LinkedIn and Twitter personal profiles.


