What is Weknow.ac Virus
Update July 2020! What is Weknow.ac Virus ? What does Weknow.ac Virus do? How to get rid of Weknow.ac Virus on Mac ?
This article gives insights on what Weknow.ac hijacker is and why it is better to be removed from the affected browser and system. The removal of this annoying website could be realized with the help of several steps that are listed at the end of the article.
Weknow.ac Mac
Weknow.ac is a website that provides questionable searching services. It could change your browser homepage, new tab page and default search engine without your explicit consent. After these changes, the main page of Weknow.ac starts to appear each time you open the affected browser. Its intrusive behavior is one of the signs that prove it is a typical browser hijacker. Since you risk a lot by using the services of this poorly secured website it is advisable to remove it as soon as possible from your affected Mac.

Threat Summary
| Name | weknow.ac |
| Type | Browser Hijacker, Potenitally unwanted program (PUP) |
| Short Description | Poorly secured website that alters main browser settings without asking for permission. Hijacks main browser settings in order to push its deceptive services. |
| Symptoms | When you enter an affected browser you see the main page of this hijacker on the start page. Each new tab page as well as the default search engine could be also configured to load weknow.ac |
| Distribution Method | Freeware installations, Bundled packages, Infected web pages |
| Detection Tool |
See If Your System Has Been Affected by malware
Combo Cleaner
Malware Removal Tool
|
User Experience | Join Our Forum to Discuss weknow.ac. |
Weknow.ac Virus – Update July 2020
One Mac user had the following to report on Apple Community forums regarding:
Reuben_Hood
User level: Level 1
(53 points)
Apple MusicSpeciality level out of ten: 0
Question: Q:
Remove “weknow.ac” Malware in Chrome?iMac (Retina 5K, 27-inch, Late 2015), 3.3 GHz Intel Core i5, 16 GB 1867 MHz DDR3, 1.7 TB free — Running High Sierra 10.13.6 (17G65). For a variety of reasons, Chrome is my default browser, and Google is my default search engine and homepage. While browsing with Chrome two days ago, I made the idiotic mistake of clicking on a Flash download popup and immediately noticed signs of infection by this malware. The main only noticeable effect is that my homepage, tab option, and search engine in the Chrome browser now default to this alien “weknow.ac” search engine, which produces results very different from Google’s. I’ve tried three long phone troubleshooting sessions with Apple Help, including downloading and scanning with Malwarebytes, which read my computer as “clean.” Also pursued other remedial steps I’ve seen suggested in other websites. (Although there are only a few that deal specifically with Chrome on Mac.) Uninstalled Chrome application, including trashing all its support folders from Library. However, the bug still keeps coming back. The “good” news is that Safari (so far) shows no sign of the infestation — so I’m using that as my only browser. However, I don’t want my (still relatively new) iMac to go through the rest of its life with this alien entity ticking away in its innards. Can anyone here recommend a more permanent solution to my problem? Is there a third-party malware removal product that’s both effective and trustworthy? Thanks in advance for any help.
Other reports also stated that the victims have had tough time removing Weknow.ac from their devices:
how to remove weknow.ac virus
My Mac Book is infected with weknow.ac virus. How can remove this virus?MacBook, Mac OS X (10.6.8)
Posted on Sep 13, 2018 10:19 AM
Reply
maulikbhatt11
User level:Level 1
Question:Q:
want to remove weknow.ac malware
How can I remove weknow.ac malware ? I don’t have Profile under the System Preference as one of the thread explain. Can anyone help m e out on this issue?Thank you very much in advance.
sriya.ajjarapu
User level:Level 1
(4 points)
macOSSpeciality level out of ten: 0
Question:Q:
I get a pop-up we know.ac tab every time I open a new tab
Every time I open a new tab another tab with weknow.ac opens which redirects to Mac keeper. Can anybody please tell me some way to get rid of this.Posted on Sep 11, 2019 8:37 AM
It appears that the weknow.ac “virus” changes a group of Chrome policies with the idea to set a new default homepage and new tab page, as well as modify the browser’s settings. According to a discussion, you can see your current Chrome policies by typing chrome://policy/ into the URL bar. In case you’re affected, you should be able to notice the modifications of your policies immediately.
The advice here is to utilize the command line to delete or modify the affected policies by opening up “Terminal” and copying each of the following entries below:
defaults write com.google.Chrome HomepageIsNewTabPage -bool false
defaults write com.google.Chrome NewTabPageLocation -string “https://www.google.com/”
defaults write com.google.Chrome HomepageLocation -string “https://www.google.com/”
defaults delete com.google.Chrome DefaultSearchProviderSearchURL
defaults delete com.google.Chrome DefaultSearchProviderNewTabURL
defaults delete com.google.Chrome DefaultSearchProviderName
After you’ve completed this step, restart your browser. You can find additional instructions at the end of this article.

Weknow.ac Virus – Update 2019
Weknow.ac has become more widespread and now features several different versions of its PUP domains. One of those domains recently detected is called Weknow.us and it sets the same suspicious web page as a home page. When checked, the other site also turned out to be outright dangerous for users due to a sheer lack of security.
So far, the Weknow.ac family of unwanted programs has continued to affect computers on several different operating systems and web browsers. The program was recently reported by security professionals whose customers have experienced Weknow.ac issues. These reports indicate a lot of threats being detected after some time spent with the Weknow.us or Weknow.ac hijackers installed on victim machines. In addition to ths, the Weknow.ac may not only target Macs, but the program also heavily attacks web browsers as well. The main browsers fallen victims to Weknow.ac have so-far been reported to be the following:
- Safari.
- Chrome.
- Mozilla Firefox.
- Opera browser.
Furthermore, the weknow.ac is a software, which has the main goal to stay persistent on your Mac for as long as possible, making it’s removal this harder. To reach its end goal, Weknow.ac creates System Preferences “profile” that changes a lot of your browser’s default settings and may even change your browser’s default proxy or VPN address. This menace of a software is so invasiv, that even if you use your URL box to type something, you get redirects to the weknow.ac page.
Further analysis of Weknow.ac has indicated that it may belong to a family of adware viruses, known as CrossRider Ads. This W32 aware has been first detected back in 2015 and has been very active ever since. In addition to this, the adware may also flood your computer system with the following ads:
- Redirects.
- Pop-ups.
- Animated ads with media.
- Highlighted text ads.
- Banner advertisements.
- Ad-supported search results.
The main idea is for the CrossRider adware to work in combination with the hoax search site Weknow.ac in order to get you to visit a suspicious website, where you might be tricked into downloading or getting infected with another unwanted program or a virus.
Despite that users have told on forums that they have removed their settings and profiles for User Library directories of Chrome and Safari browsers, the virus was still reported to remain dangerous.

Weknow.ac – Ways of Distribution
Often times browser hijackers like Weknow.ac find their way to target Mac devices by being part of software bundles. There are various supposedly useful free third-party apps available across the web that feature potentially unwanted programs in their installers. And it is not that easy to reveal the presence of extras because the purpose of all these apps is to trick you into installing added apps without noticing their presence. So the information about these extras is usually well hidden. The majority of online users just keep clicking the Next button until the Finish button appears when installing newly downloaded apps. And that’s how the magic with Weknow.ac hijacker happens.
Recent cases of infected users uncover that rogue applications like [wplinkpreview url=”https://sensorstechforum.com/adware-crossrider-win32-35-removal-guide/”]CrossRider first spotted back in 2015 as well as [wplinkpreview url=”https://sensorstechforum.com/remove-fake-flash-player-update-mac/”]Fake Adobe Flash Player Updates have been utilized for the spread of Weknow.ac browser hijacker. These nasty apps could be in turn released on fake download sites, pages associated with redirecting ads, P2P networks and other channels of malicious files.
To prevent such unwanted consequences you should always choose the Advanced or Custom install settings. Before installing a new app on your Mac you should read carefully the details listed in these steps as the information may inform you about the presence of additional apps that are going to be installed by default if you don’t opt out their installation.
Тhe program is known to attack the preferences of Mac operating systems as well as those of popular web browsers like:
- Safari
- Chrome
- Mozilla Firefox
- Opera browser

Weknow.ac – More About It
Weknow.ac is classified as a browser hijacker due to the changes that occur after its start on the system. Actually, its activities are most likely supported by an undesired program that has managed to trick you into allowing its installation on your Mac.
When this program first starts on your device it initiates several changes that usually affect essential browser settings. After changes the hoax search engine Weknow.ac becomes able to appear every time while you are browsing the web. Its simplistic main page could load as start page, new tab page while its deceptive search engine may be set as default one. Since all changes happen on the background you may not be aware of them until you open your preferred browser and see the main page of the hijacker:
To make its presence even more persistent the undesired program associated with Weknow.ac hijacker could create a configuration profile in the browser and control various settings through it. This, in turn, could be one of the reasons why you cannot fix browser settings and eventually get rid of this annoying hijacker.
Additionally, the presence of this browser hijacker on your Mac may be the reason why you see an increased number of annoying online ads including but not limited to pop-ups, pop-unders, banners, in-text links and images in the browser. This may result in sluggish browser performance and regular crashes of running apps.
What’s more some of the generated ads may endanger the security of your Mac as well as your privacy. Since the main purpose of Weknow.ac’s authors is revenue, they could skip checking the security of promoted pages. As a result, some ads generated by their bogus product may land you on poorly secured or even corrupted web pages.

Weknow.ac – Privacy Policy
When we first entered the Privacy Policy of Weknow.ac we noticed that it is quite the same of the one provided by another nasty hijacker called [wplinkpreview url=”https://sensorstechforum.com/remove-chumsearch-com-effectively/”]Chumsearch.com. Apparently, these bogus websites are managed by the same people.
As of the information collected by these hijackers, it is stated to be both personally and non-personally identifiable.
Information that may be collected according to that policy:
- Your device, apps, type, name and version of OS and other software you have
- Internet Protocol (IP) address, e-mail address
- Anonymous user identifiers, device configs and identifiers, advertising ID
- Your use and interactions of the site and services
- Your web page visits and the content you see
- Your search queries and the time and date of your searches
- Your interactions on social networks
- Your name, company name, birth date and gender
- Your home or work addresses, location, telephone and fax numbers
Furthermore, the policy states that the unintentional collection of email addresses, social security numbers, credit card numbers, and login information is not excluded.
By using the site and services of Weknow.ac you grant approval for all of that information to be collected. All information may be shared with third parties.

Remove Weknow.ac Browser Hijacker
In order to remove Weknow.ac hijacker along with all associated files that enable its appearance in the browser, you should complete several removal steps. In the guide below you will find all removal steps in their precise order. You could choose between manual and automatic removal approaches. In order to fully get rid of present undesired programs and strengthen the security of your device we recommend you to combine the steps. Have in mind that installed files associated with this hijacker may be detected with names different than Weknow.ac.
In case you have further questions or need additional help with the removal process, don’t hesitate to leave a comment or contact us at our email.
Steps to Prepare Before Removal:
Before starting to follow the steps below, be advised that you should first do the following preparations:
- Backup your files in case the worst happens.
- Make sure to have a device with these instructions on standy.
- Arm yourself with patience.
- 1. Scan for Mac Malware
- 2. Uninstall Risky Apps
- 3. Clean Your Browsers
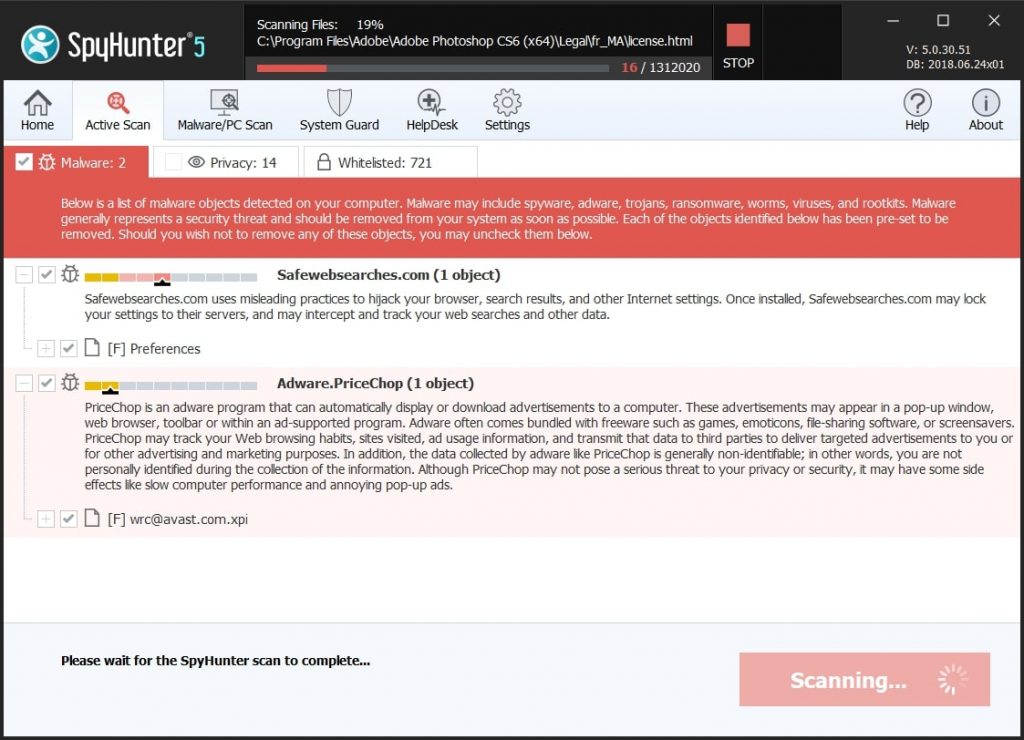
Step 1: Scan for and remove weknow.ac files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as weknow.ac, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Quick and Easy Mac Malware Video Removal Guide
Bonus Step: How to Make Your Mac Run Faster?
Mac machines maintain probably the fastest operating system out there. Still, Macs do become slow and sluggish sometimes. The video guide below examines all of the possible problems that may lead to your Mac being slower than usual as well as all of the steps that can help you to speed up your Mac.
Step 2: Uninstall weknow.ac and remove related files and objects
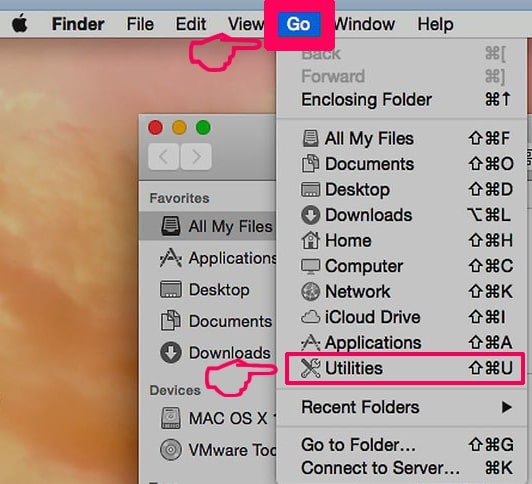
1. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on “Go” and then click “Utilities”, like the image below shows:
2. Find Activity Monitor and double-click it:

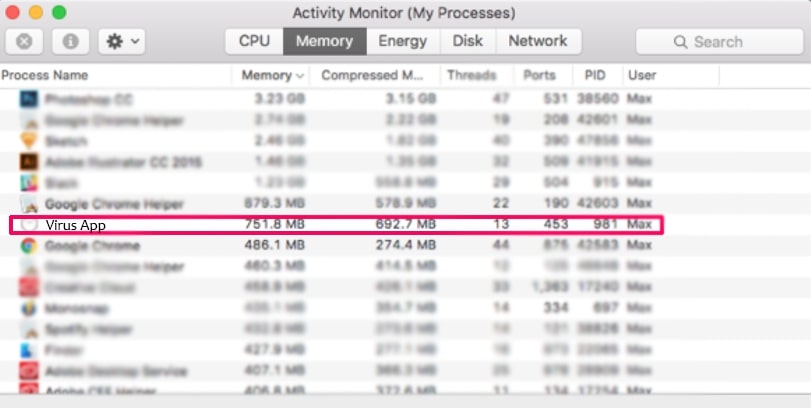
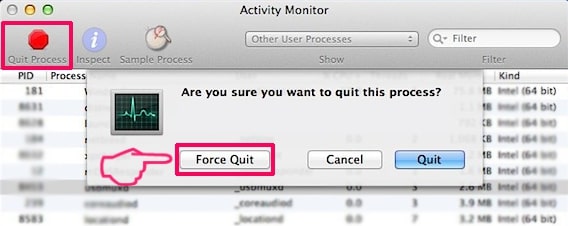
3. In the Activity Monitor look for any suspicious processes, belonging or related to weknow.ac:
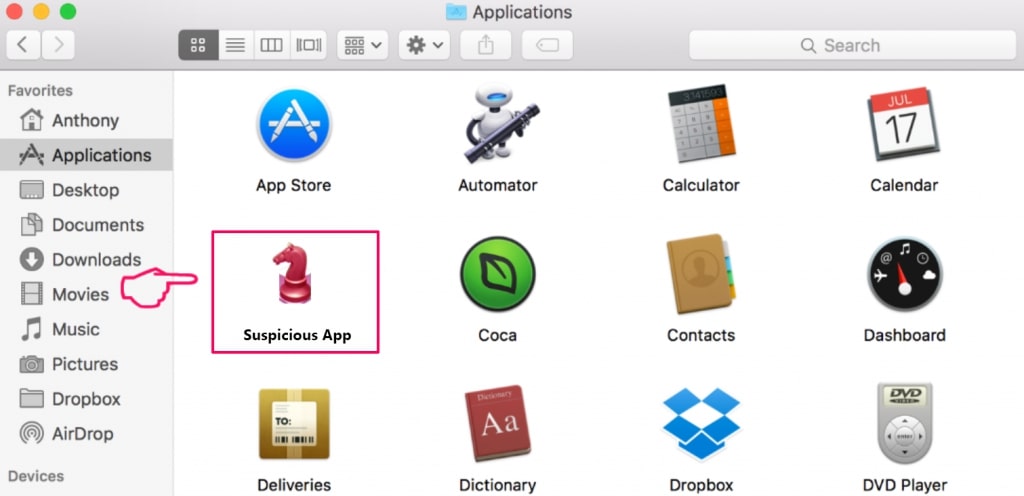
4. Click on the "Go" button again, but this time select Applications. Another way is with the ⇧+⌘+A buttons.
5. In the Applications menu, look for any suspicious app or an app with a name, similar or identical to weknow.ac. If you find it, right-click on the app and select “Move to Trash”.
6. Select Accounts, after which click on the Login Items preference. Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to weknow.ac. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
7. Remove any leftover files that might be related to this threat manually by following the sub-steps below:
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove weknow.ac via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
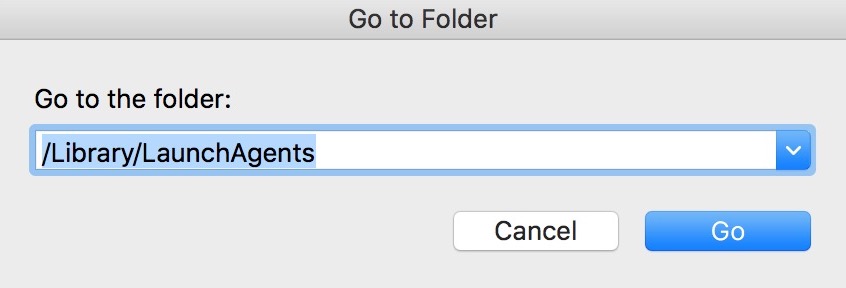
1. Click on "Go" and Then "Go to Folder" as shown underneath:
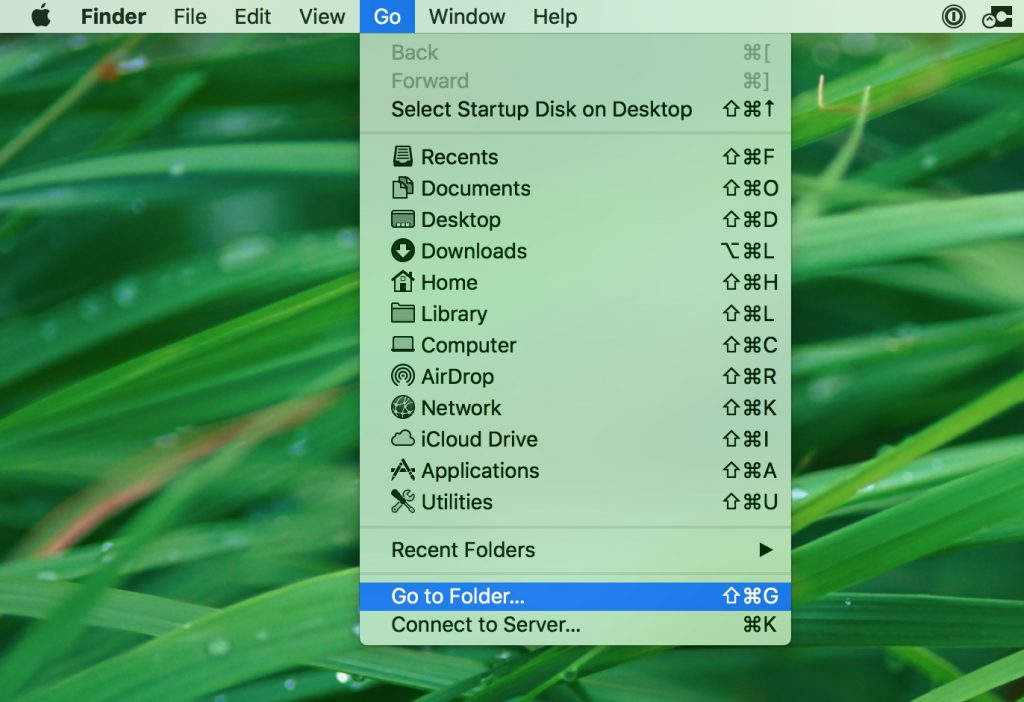
2. Type in "/Library/LauchAgents/" and click Ok:
3. Delete all of the virus files that have similar or the same name as weknow.ac. If you believe there is no such file, do not delete anything.
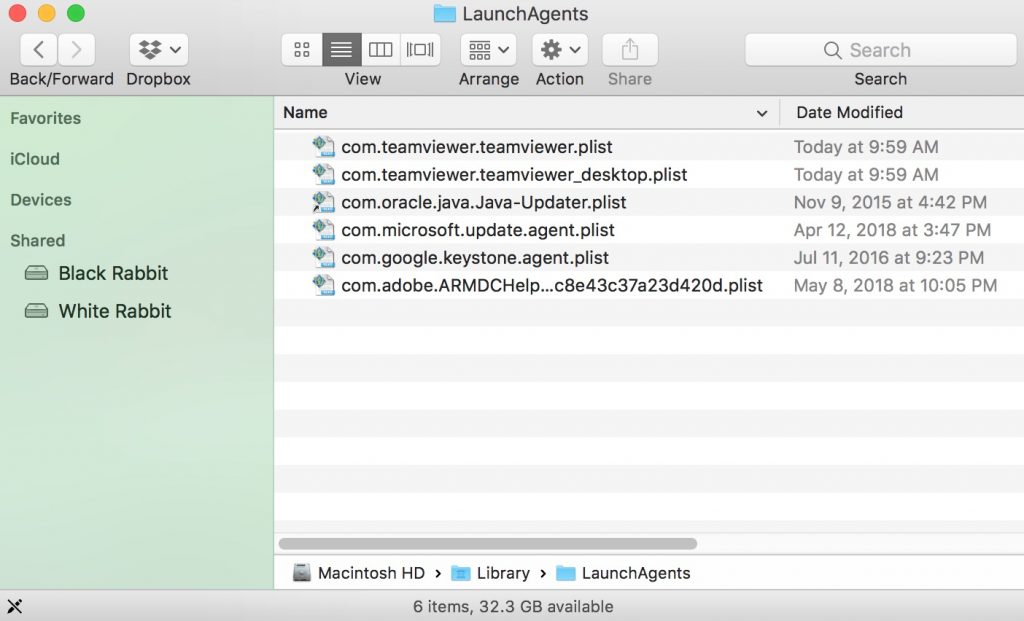
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
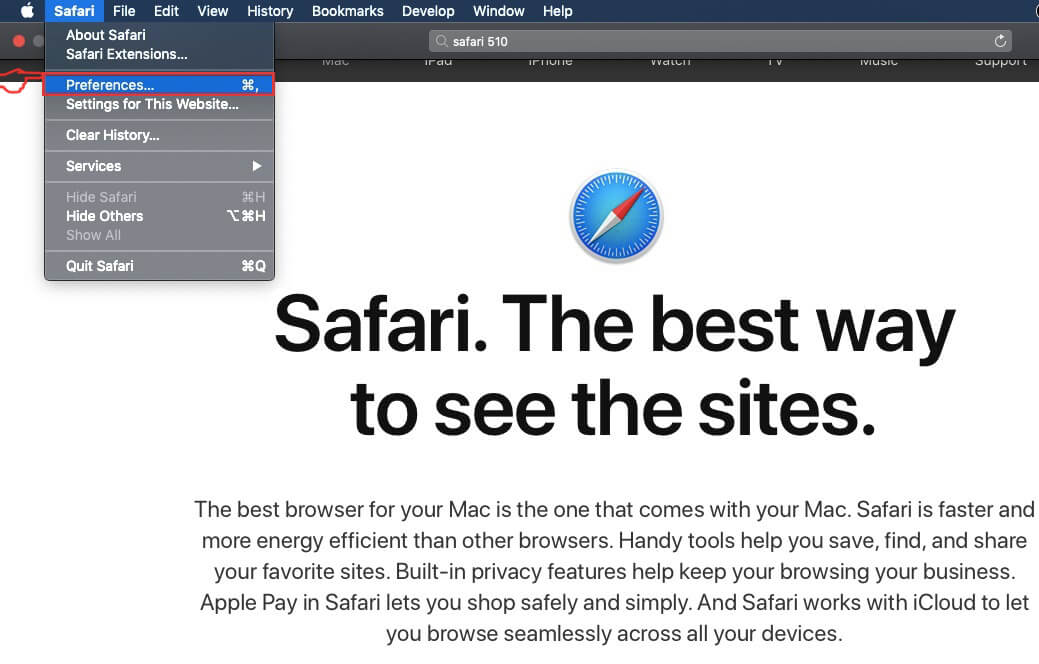
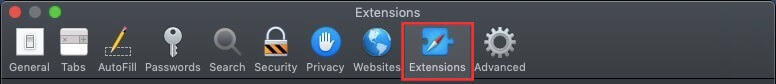
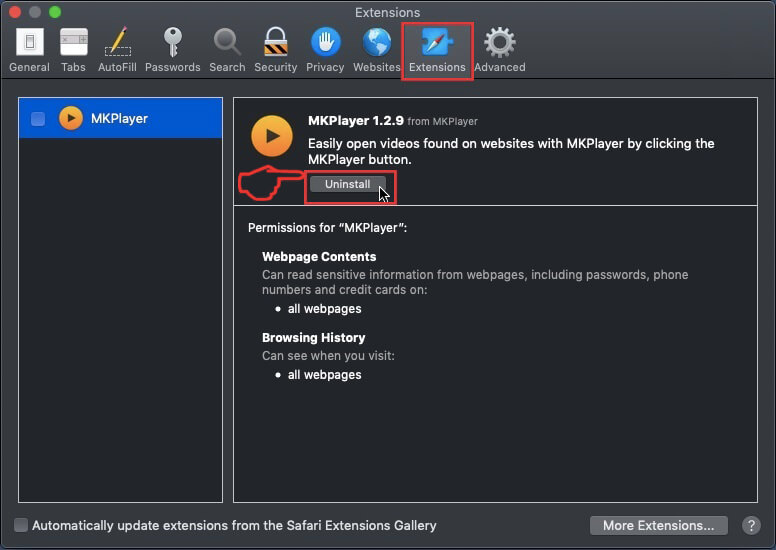
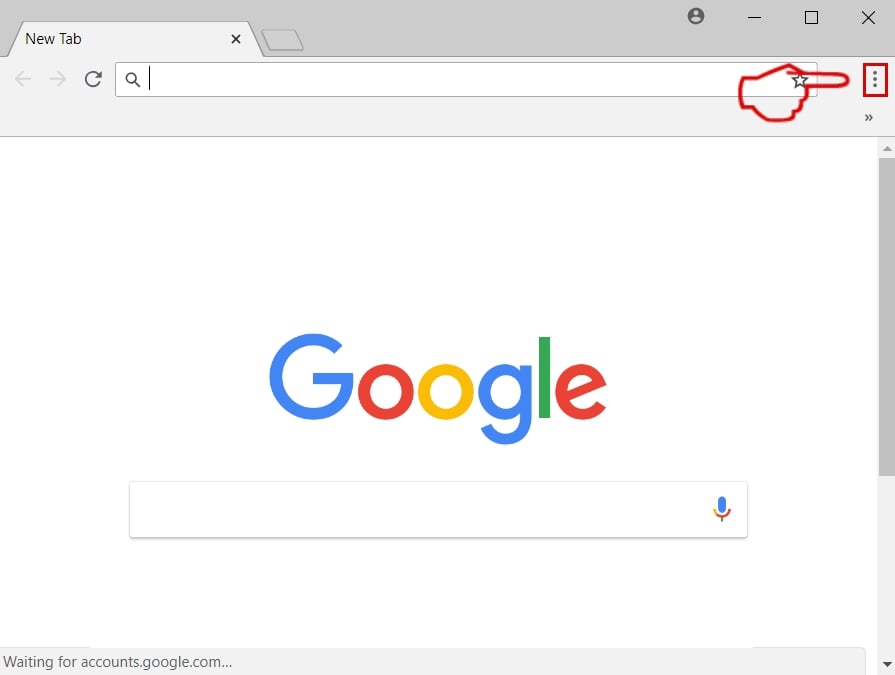
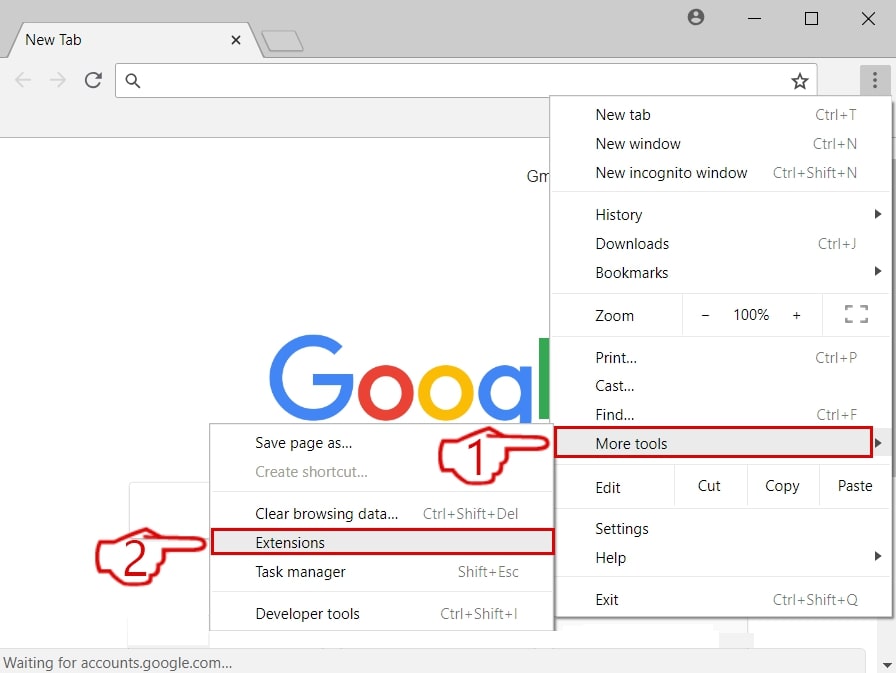
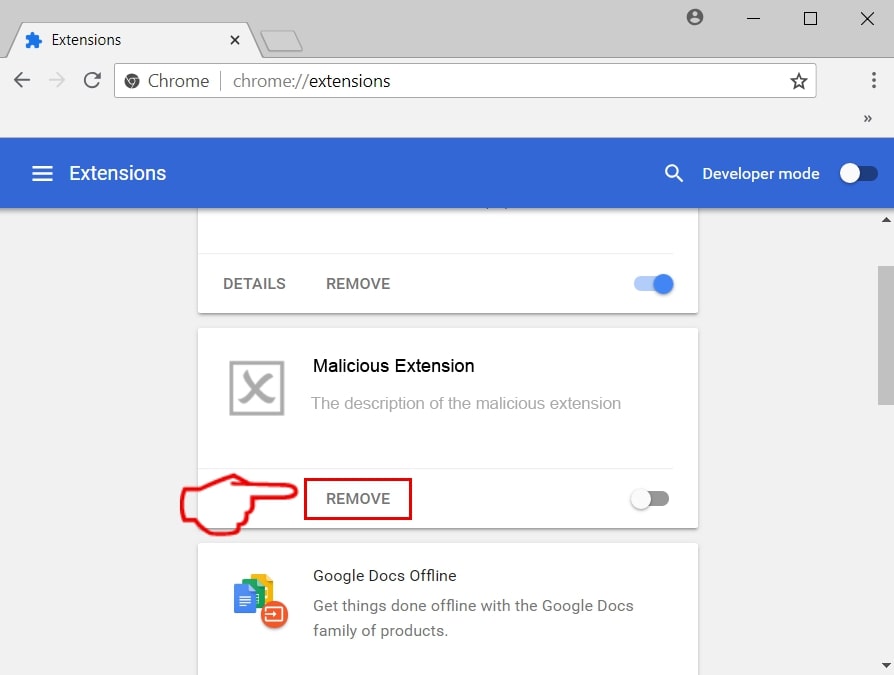
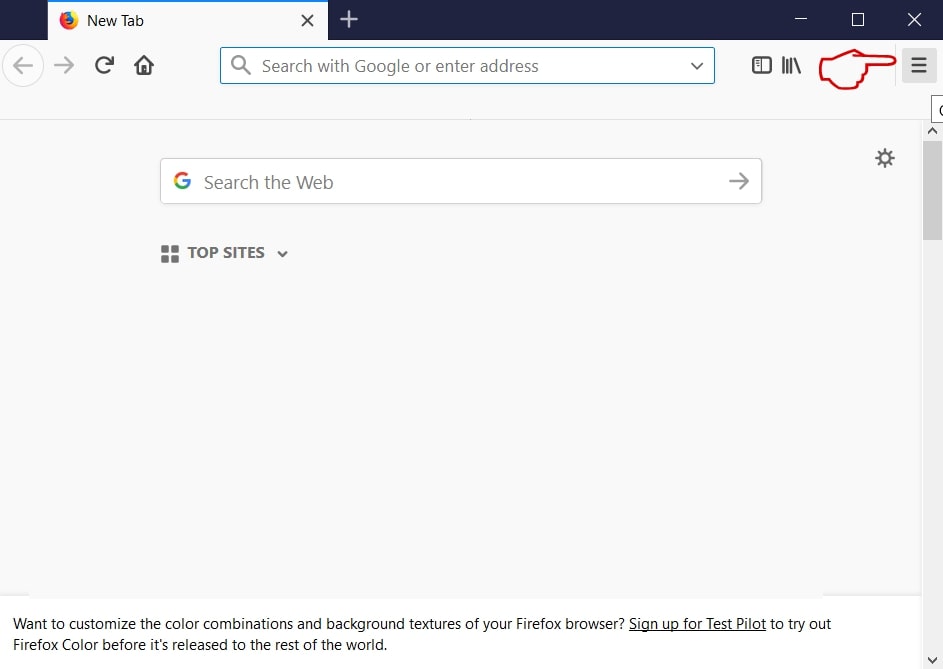
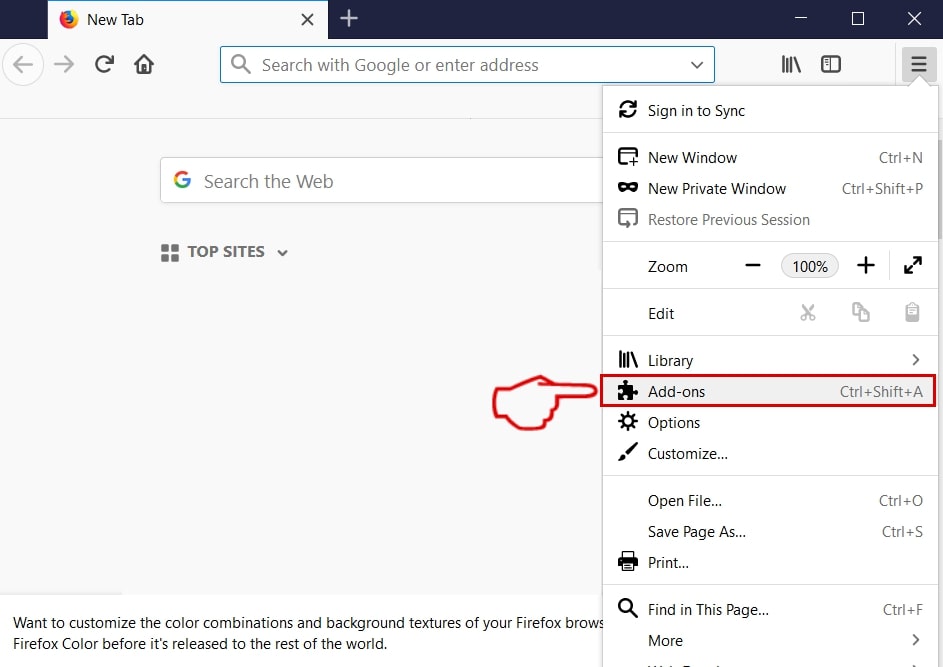
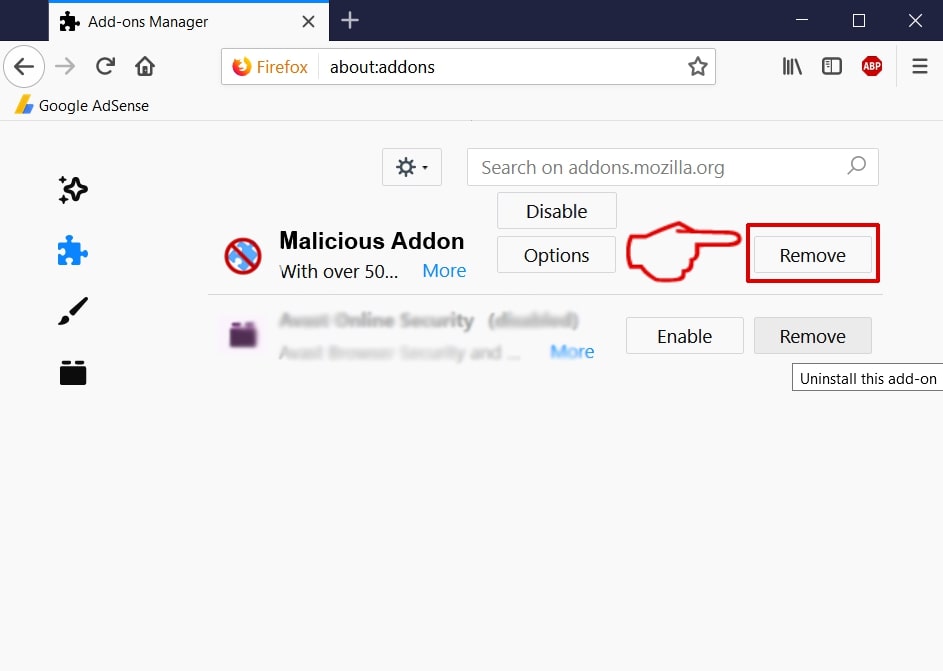
Step 3: Remove weknow.ac – related extensions from Safari / Chrome / Firefox
weknow.ac-FAQ
What is weknow.ac on your Mac?
The weknow.ac threat is probably a potentially unwanted app. There is also a chance it could be related to Mac malware. If so, such apps tend to slow your Mac down significantly and display advertisements. They could also use cookies and other trackers to obtain browsing information from the installed web browsers on your Mac.
Can Macs Get Viruses?
Yes. As much as any other device, Apple computers do get malware. Apple devices may not be a frequent target by malware authors, but rest assured that almost all of the Apple devices can become infected with a threat.
What Types of Mac Threats Are There?
According to most malware researchers and cyber-security experts, the types of threats that can currently infect your Mac can be rogue antivirus programs, adware or hijackers (PUPs), Trojan horses, ransomware and crypto-miner malware.
What To Do If I Have a Mac Virus, Like weknow.ac?
Do not panic! You can easily get rid of most Mac threats by firstly isolating them and then removing them. One recommended way to do that is by using a reputable malware removal software that can take care of the removal automatically for you.
There are many Mac anti-malware apps out there that you can choose from. SpyHunter for Mac is one of the reccomended Mac anti-malware apps, that can scan for free and detect any viruses. This saves time for manual removal that you would otherwise have to do.
How to Secure My Data from weknow.ac?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your e-mail passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activiites with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these reccomendations, your network and Apple devices will become significantly more safe against any threats or information invasive software and be virus free and protected in the future too.
More tips you can find on our MacOS Virus section, where you can also ask any questions and comment about your Mac problems.
About the weknow.ac Research
The content we publish on SensorsTechForum.com, this weknow.ac how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific macOS issue.
How did we conduct the research on weknow.ac?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of Mac threats, especially adware and potentially unwanted apps (PUAs).
Furthermore, the research behind the weknow.ac threat is backed with VirusTotal.
To better understand the threat posed by Mac malware, please refer to the following articles which provide knowledgeable details.