Not enough users are acquainted with the risks associated with their routers, and there’s a research that proves it. Broadband Genie researchers surveyed 2,205 people across the U.K. whether they had performed any router security hygiene like changing Wi-Fi passwords анд router admin passwords, or updating their routers’ firmware. The answers were staggering but perhaps not that surprising after all.
What researchers found out is that “there are potentially millions of home Wi-Fi hubs left vulnerable because many people are not making use of key features in their home broadband routers”.
Apparently, 82% of the survey participants never took the time to change their admin passwords, which is considered a high risk factor as the default passwords are often insecure and shared across all routers of the particular brand or model range. Many users have never updated the firmware of their routers. This means that their routers are unpatched making them vulnerable to attacks and exploits.
The most concerning finding however is that 51% of the surveyed users have never done anything of the security measures mentioned earlier. This leaves them open to a range of security issues that could affect their broadband and any devices connected to their routers.
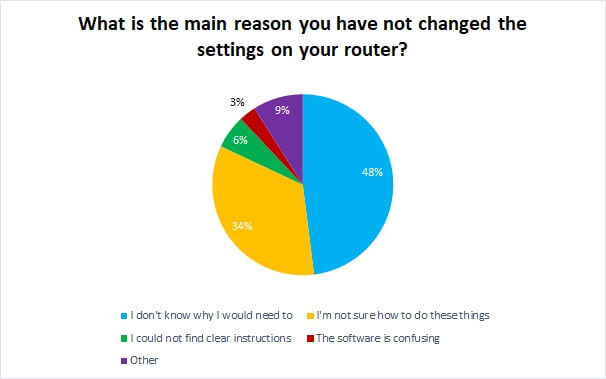
These 2,205 users were also asked whether they have left their router security to chance.
48% said they did not know why they would need to make these changes, while 34% said they didn’t know how, the researchers said. A small percentage of these users said they could not find clear instructions on how to perform these tasks.
This suggests that as well as patching security holes and upgrading hardware when it becomes outdated, broadband ISPs should also be ensuring they offer help pitched at complete beginners, including explanations of why it is important to secure Wi-Fi routers.
Router Security 101
A vulnerable router puts the user’s privacy at various risks, including malware attacks. Furthermore, all devices connected to the router are also exposed to the same risks. Fortunately, there are steps that would ensure the privacy and security of a router.
The very first step here is to be able to access the admin panel. Unfortunately, there aren’t specific instructions on this as it depends on the router’s model. Nonetheless, a web browser is needed to connect to the router’s IP address and then enter a password. Specific instructions should be found in the router’s user manual or in some cases, they should be located on a sticker on the router itself.
In a nutshell, you should:
- Change the admin password of your router;
- Change the Wi-Fi network name and password;
- Regularly check what devices are connected to the router by viewing all devices connected;
- Update the router’s firmware. It is as needed as it is to update your operating system.
And if you think that router security is overrated, let us remind you of the highly sophisticated attack dubbed Slingshot that’s capable of cyber espionage via targeting routers. The malware has been used in malicious campaigns on victims in the Middle East and Africa for several years. And it is a dangerous piece of malware – a complex APT (Advanced Persistent Threat), with “one of the most complex frameworks” as explained by malware analyst Alexey Shulmin.
What happens after a targeted router is infected with a piece of malware such as Slingshot? Slingshot will proceed with downloading more malware modules. In this particular attack, Cahnadr and GollumApp have been downloaded. The two components are connected to one another and can support each other in harvesting information.
If you believe that your router has been infected with malware, refer to this article to find specific instructions on how to remove malware from a router.
And while we are at it, you can also check some of the most secure routers out there.