A new security report shows that Alcatel smartphones contain an Android malware called TCL Weather. It was found installed on two phones and available on the Google Play Repository as well.
TCL Weather Android Malware Bundled with Alcatel Phones
Embedding malware code in Android apps and attempting to coerce victims into installing it is one of the most popular tactics used by criminals. However a recent attack campaign has been identified to be caused by an even easier and more alarming method — pre-installed applications by the manufacturers. This is the case with Alcatel phones which were found to contain such instances. Public disclosure about the problem was reported by Upstream, a carrier billing fraud company. We remind our readers that Alcatel is owned by the TCL Corporation who release devices under various brands, including BlackBerry.
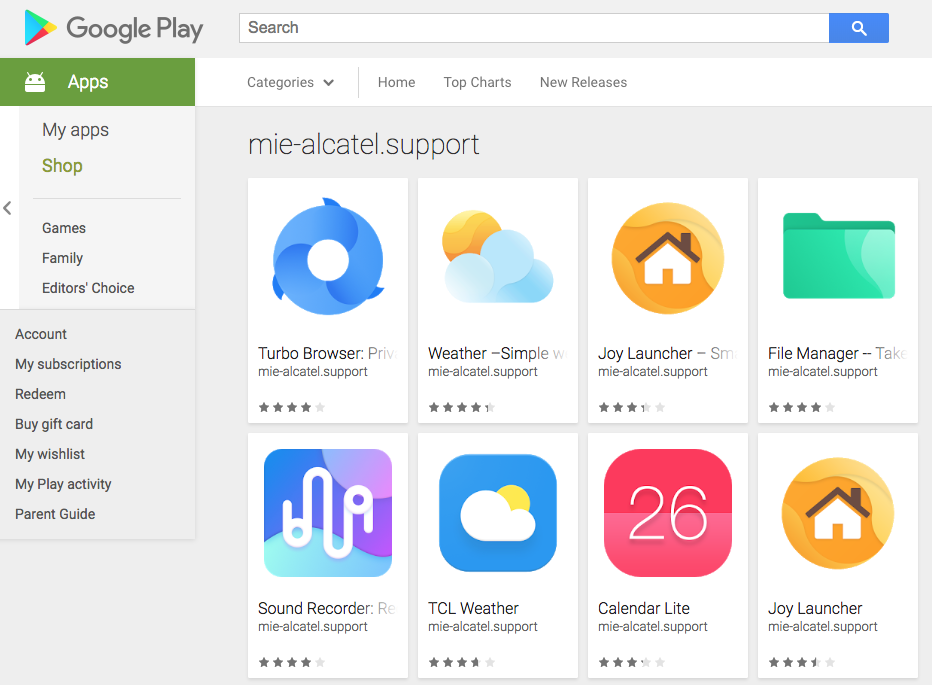
The malicious code itself is found in the application called TCL Weather which itself is developed by the same company and pre-installed on their devices. Additionally it is available on the Google Play repository — more than ten million downloads have been recorded so far. The security issue is not intentional, it was found that at one point during last year the application was infected with malicious code. Even after the bug was fixed TCL has not responded as to how this service was hacked.
The weather service was found to harvest user data and send them to a server located in China. According to the investigation this includes the following information:
- Geographical Location
- Email Addresses
- IMEI Codes
- Other data as configured in the code
Two models have been to be affected by the bug as the weather service was pre-installed on them — the Pixi4 and A3 Max. Other devices can also be affected as well as any Android user who has downloaded the dangerous plugin from the Google Play Store repository.
What The TCL Weather Malware Could Do to Your Phone?
The security reports indicate that the Android malware has impacted quite a few devices. The dangerous code attempts to subscribe the impacted devices to premium phone numbers which leads to expensive phone bills.
One of the largest incidents involving this particular malware was done in Brazil where 2.5 million transaction attempts were confirmed to be coming from the weather service. The contaminated devices all sent SMS messages to premium phone numbers attempting to pay for expensive digital services. Fortunately they were blocked by the carriers. This short-lived campaign took place in July and August 2018 before changing its tactics. The first wave of attacks numbered 128,845 unique phone numbers. The second attempt was for another premium service which was also blocked in due time. This happened in the same time period totaling 428,291 transaction attempts.
Two other campaigns which were confirmed by this malware are the following:
- The Kuwait Attack — Another impacted country is Kuwait where 78,940 transaction attempts were detected during the Brazil campaign.
- Africa Attacks — Blocked transaction requests were detected in several African countries including Nigeria, Egypt, South Africa and Tunisia.
According to the news reports the Android malware was found in seven markets and if it was successful it would lead to losses of around $1.5 million to device owners.
Upstream purchased a device from a former owner and reported that adware-like behavior has also been identified. Analysis of the weather app code reveals that upon launch it will start a hidden browser data with preset landing pages. This process will click on the placed ads which will generate income for the hacker operators. As a result of this the analysts report that between 50 to 250 MB data was recorded each day in such automated activities.
Investigation of the infected phones also shows that the malicious APK files include excessive Android permissions:
- CHANGE_WIFI_STATE — Allows the application to change the state of the Wi-Fi network
- MOUNT_UNMOUNT_FILESYSTEMS — Allows mounting and unmounting of file systems (i.e. external SD cards). Android documentation says the permission is NOT intended for 3rd party applications
- READ_PHONE_STATE — Allows read only access to phone state, including the phone number of the device, current cellular network information, the status of any ongoing calls, and a list of any PhoneAccounts registered on the device. Documentation says that this permission is DANGEROUS
- READ/WRITE_EXTERNAL_STORAGE — Allows reading and writing of the external storage. This is dangerous (as the application can have access to other user files and/or 3rd party app logs, system logs. This means that the application can read/write everything it wants and the read data might be sent to the server
- ACCESS_KEYGUARD_SECURE_STORAGE — This permission was removed in the OS since 4.4 (KitKat). But for devices that are below that version, this permission is able to control a flaw in the OS to lock and unlock the device at any time (like pressing the power button and unlocking the phone)
- READ_LOGS — Allows an application to read the low-level system log files. Not for use by third-party applications, because Log entries can contain the user’s private information.
- SET_DEBUG_APP — Configure an application for debugging
Even though the company has not announced announced the origins of the malicious code there are two possible reasons which are considered the most likely:
- Application Vulnerability — The criminals behind the malware code installation could have identified weaknesses in the application and used it to embed the dangerous code.
- App Overtake — The hackers could have hacked the repository or the facility producing the phones in order to reconfigure them with the necessary malware.
All dangerous versions were subsequently removed from the Google Play store.