URLhaus is a cybersecurity project launched by the well-known abuse.ch non-profit organization in Switzerland. The project is focused on sharing malicious URLs, and it just succeeded in taking down nearly 100,000 websites exploited for malware distribution.
The take-down operation requires the cooperation of hosting companies whose infrastructure was used. However, this is not an easy task since most companies tend to take the time to respond to such reports.
More about URLhaus and Its Take-Down Operation
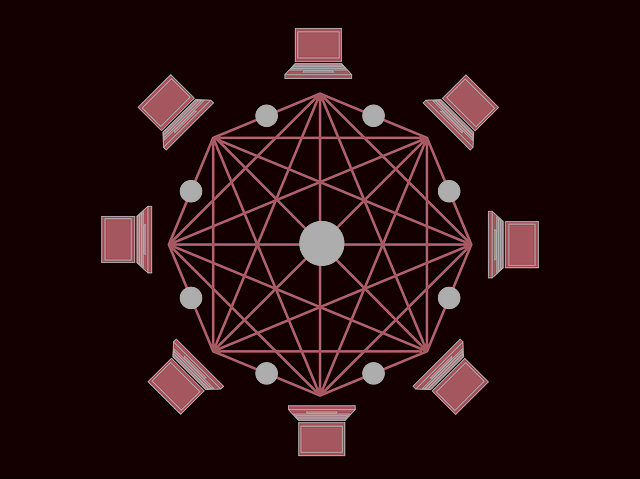
URLhaus was launched at the end of March last year, with the idea to collect and share URLs used for malware distribution. The 100,000 malware distribution sites were taken down within 10 months. It took 265 security researchers from around the world to identify and submit approximately 300 malware sites on a daily basis.
According to their own report on the matter, the project managed to “get the attention of many hosting providers, helping them to identify and re-mediate compromised websites hosted in their network”. Large hosting providers have tens of thousands of customers, a significant amount of which hijacked websites in their network that are getting abused by cybercriminals to distribute malware, the researchers said.
It is noteworthy that Chinese hosting providers took the longest to respond. “The three top Chinese malware hosting networks have an average abuse desk reaction time of more than a month,” the report says. More specifically, ChinaNet, ChinaUnicom and Alibaba left the compromised websites running for more than a month. The negligence to respond left 500 malware URLs active and running, hence spreading malware.
The most adequate response came from Unified Layer, a hosting provider in the United States.
Most Malware Sites Are Related to Emotet
The average number of active malware distribution sites that URLhaus counts is between 4,000 and 5,000 on a daily basis.
Emotet gets propagated through spam that hits users inbox almost every day, the researchers noted.
Malicious spam campaigns usually contain a rogue office document with macros, which upon opening and enabling automatically downloads and executes Emotet from the compromised website. There is a way for these campaigns to bypass spam filters, and it is to redirect to a compromised website hosting the malicious document rather than attach it to the email message.
There is still a long way to go with regards to response time of abuse desks, the researchers said in conclusion, hoping that hosting providers will improve their response rates and take the malware distribution matter seriously.


