This write-up has actually been produced in order to describe to you what is the Voodoosrc as well as likewise exactly just how you can remove them along with all potentially unwanted programs provided with them.
The Voodoosrc is a widespread mac risk that attempts to obtain Apple clients right into infecting themselves with infections or divulging their passwords. Presently we do not know worrying the wrongdoers behind it. Our short post gives a thorough description of precisely how it circulates as well as likewise just how targets can attempt to remove infections.
Voodoosrc Virus
When the Voodoosrc rip-off websites is shown to the customers the fundamental sight will expose a phony presents websites that makes use of the style format and also elements of the real Apple site. The cyberpunks control the users right into thinking that a website coming from business is being accessed. Rip-offs such as this function several one-of-a-kind facets, amongst the significant ones is the fact that a number of matches of the web page can be established. They can be organized on web servers worldwide– not every one of them will certainly be provided on the specific very same domain. From a manager perspective this offers the hackers greater flexibility as they can conveniently release hundreds of them in a short quantity of time. To much more press the users right into thinking that they are accessing genuine Apple web pages they can use protection qualifications and also cross-site connecting.

Threat Summary
| Name | Voodoosrc |
| Type | PUA for Mac OS |
| Short Description | |
| Symptoms | |
| Distribution Method | |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Combo Cleaner
|
User Experience | Join Our Forum to Discuss Voodoosrc. |
Voodoosrc
The Voodoosrc fraudulence is distributed taking advantage of countless approaches. The main one is the production of websites that share a similar name to Apple in addition to their solutions. They are dispersed making use of numerous techniques:
Social Media Site Links— By utilizing phony or hacker-made accounts on popular socials media (Facebook, Twitter, Instagram as well as likewise and so on) the Voodoosrc scams can be promoted. Generally reduced links are used to link the main pages.
Email Messages— Mass e-mail messages having internet links to the Voodoosrc Facility page can be sent out to the individuals in both personalized and non-personalized kinds. The dangerous stars can make use of the exact same style design, body products as well as aspects as genuine Apple e-mails.
Similar Seeming Names— The Voodoosrc rip-off can be spread on different websites that all have a similar appearing domain to Apple.
Keep in mind that the Voodoosrc landing websites can be shown by software application as well as files additionally. An archetype is the changed software application installer– the croooks take the setup papers of noticeable software program application and add to them the code that shows the phishing websites. The other type is the manufacturing of contaminated papers that can be of any preferred type: abundant message documents, discussions, databases as well as spread sheets. When they are opened a timely will definitely show up asking the people to enable the incorporated manuscripts. When this is done the web links will absolutely be opened in an internet browser window or directly as an ingrained points.
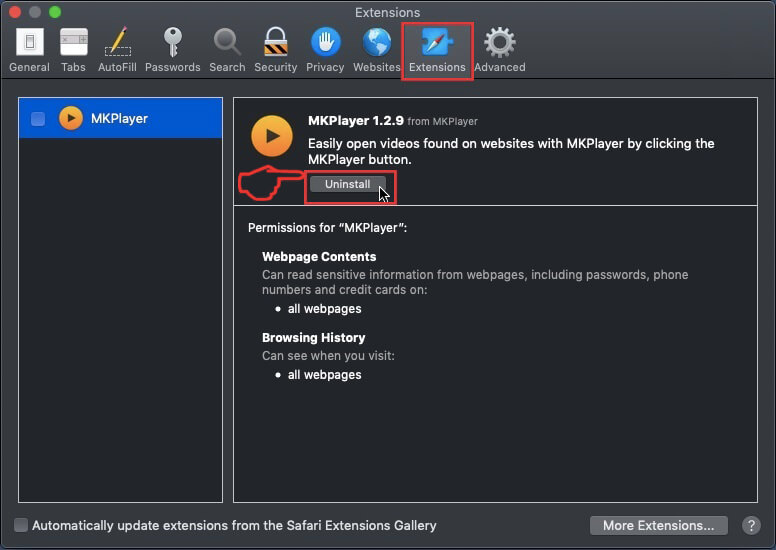
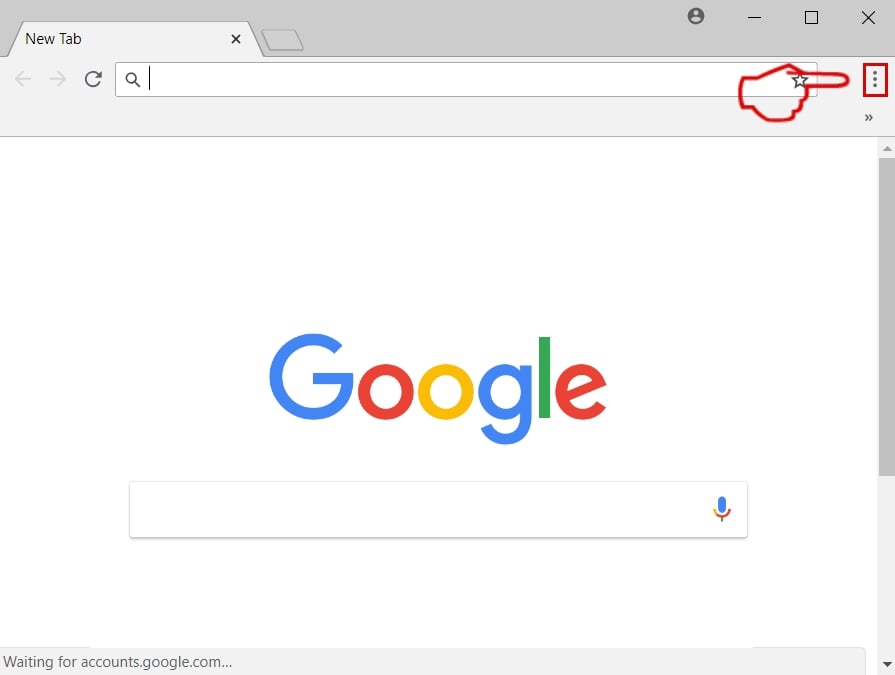
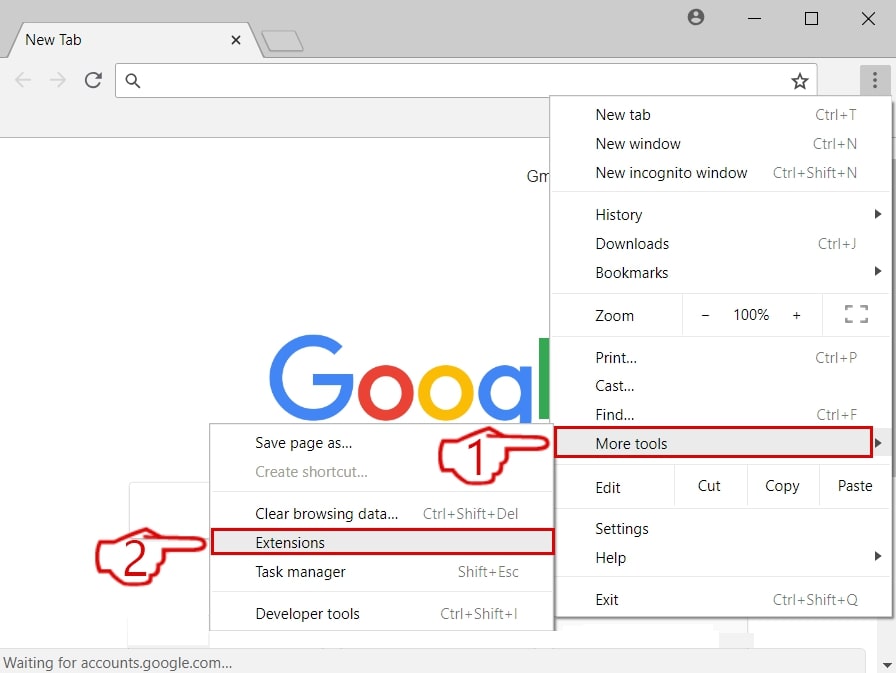
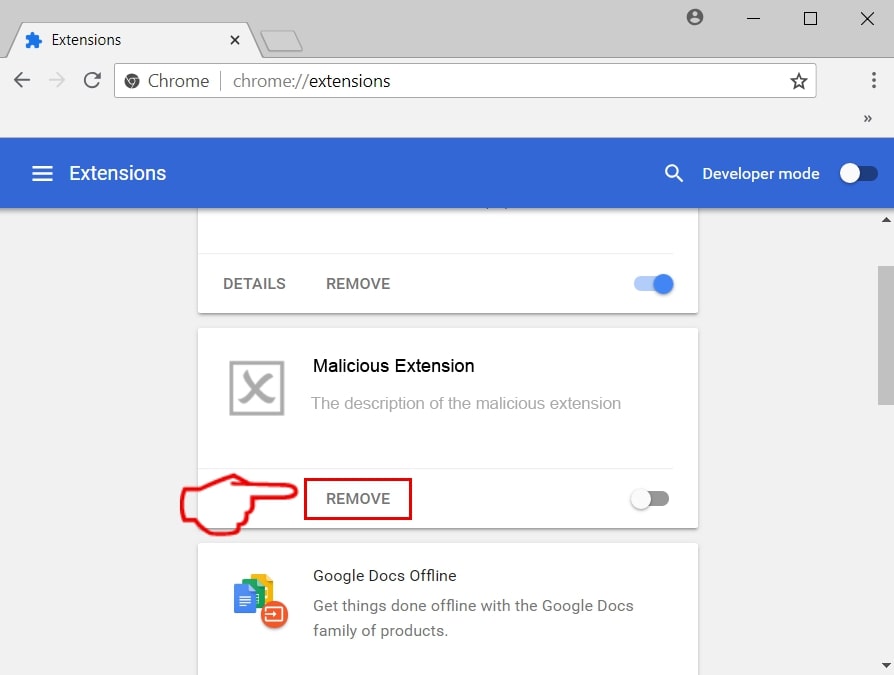
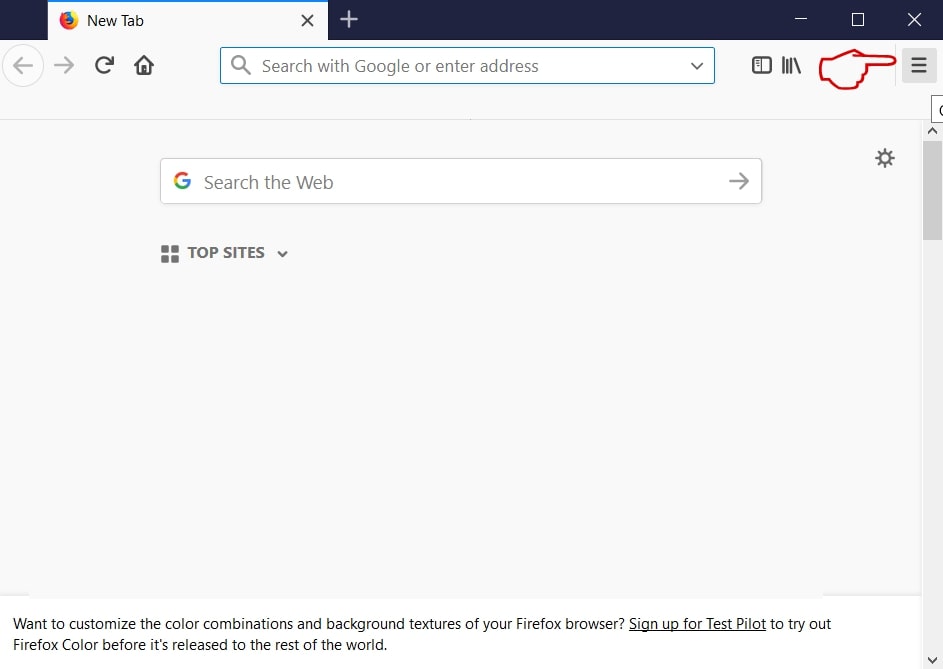
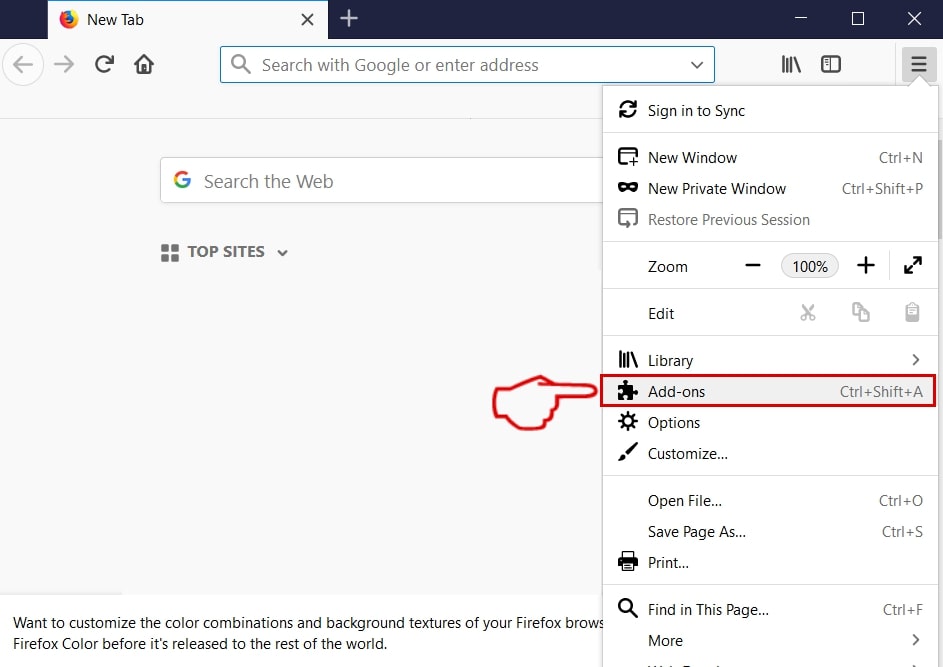
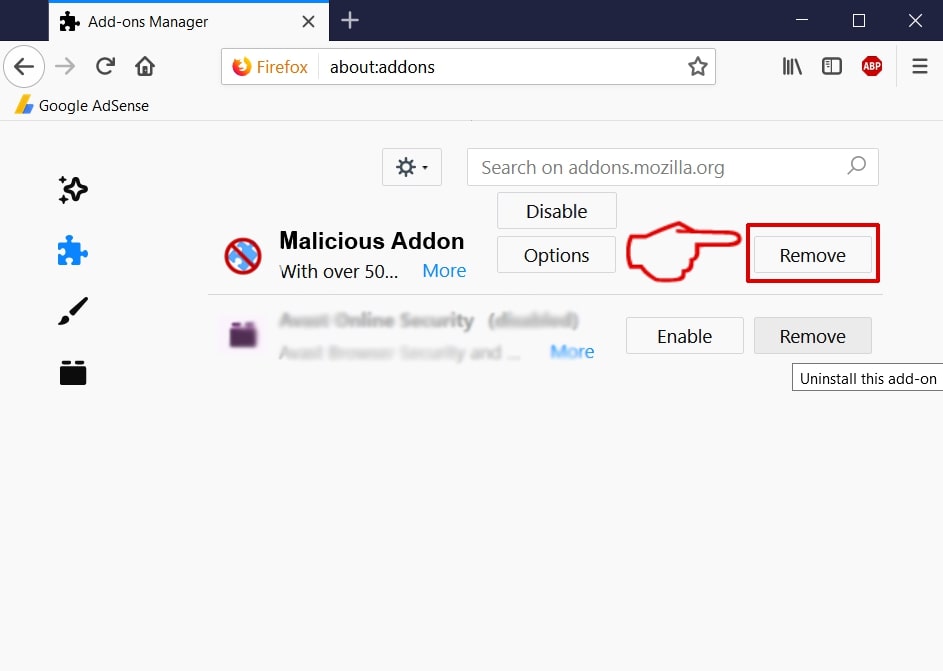
In most cases the hackers can in addition utilize malware net web browser extensions, conversely referred to as hijackers. The criminals make them ideal with one of the most recommended web net browsers in order to boost the selection of target people. They are often uploaded to the primary cyberpunk data sources using fake or swiped user examinations as well as designer qualifications. The uploaded pressures feature summaries that guarantee the optimization of the internet browsers or the improvement with newer attributes. If the clients mount them then the common hijacker practices will be observed. Straight results are the controls of the web internet browsers right into straight rerouting the customers to the Voodoosrc rip-off website. This is done by altering the default worths– web page, brand-new tabs page as well as web online search engine.
The significant objective of the web page is to encourage the consumers right into revealing their account credentials to the internet site. They will definitely be immediately relocated to the devastating chauffeurs of the Voodoosrc fraud website as quickly as they are gotten in. Nonetheless there are various other damaging activities that could be executed. Each of them are connected to the site communication somehow or one more.
Seeing the sites can bring about the installation of tracking cookies as well as additionally information collection parts. They will promptly pirate data both from the web net browsers and likewise the infected devices. There are 2 main categories of data that can be differentiated:
Anonymous Stats— The cookies will absolutely have the capability to track just how the customers connect with different internet components.
Private Data— The info collection of information that can right subject the identification of the targets.
Via the different scripts the makers can be come infected with cryptocurrency miners also. They represent applications that use the offered system sources in order to run difficult mathematical computations. When the effective tasks are reported to the proper internet servers the cyberpunk drivers will certainly obtain incomes in the form of cryptocurrency. An added consequence is the shipment of intrusive advertisements– they can create redirects to other malware websites or existing web links to financed material. In a lot of cases all popular devices can be made use of: pop-ups, banners, in-line web links as well as various other.
If any kind of type of file downloads are provided then virtually all sorts of damaging hauls can be utilized. The data themselves will possibly be relabelled with Apple pertinent services, products as well as also software application. Be cautious that amongst among one of the most often used strings used to rename such payloads include “upgrade” and also “manual”. Usual infections contain the following:
Straight Infection Downloads— Infection documents throughout all common types can be provided: ransomware, Trojans, miners in addition to various other.
Data with Malware Scripts— The Voodoosrc fraudulence website can likewise distribute malware utilizing records. The consumers will absolutely find that different documents of all popular kinds can include the damaging scripts: abundant message documents, spread out sheets, discussions and also data sources. Whenever they are opened by the sufferers a prompt will turn up requesting for the clients to make it feasible for the incorporated macros. If this is done the manuscripts will download and install an established infection from the Web as well as launch it on the local computer system.
Devastating Setup Data— The hooligans can similarly produce imitator malicious installers of favored software application. One of the most common means is to take the actual documents from the major vendor website as well as likewise include the required manuscripts to them. The reason this approach is specifically preferred is that it targets applications that are commonly utilized: imaginative assuming suites, system powers along with efficiency apps.
In some cases fraudulences such as this one can be used to spread out Trojan infections. They mean advanced malware that set up a client service to a hacker-controlled web server. The link is made both risk-free and also protected along with constant for this reason allowing the hackers to surpass control of the equipments at any sort of offered time. This also consists of the gain access to of specific info, snooping in real-time along with launching different other infections at will. Via it the hackers can likewise hire the devices to botnet networks which are especially valuable for arranging spread attacks versus pre-selected targets.
Safety educates suggest a new phishing fraudulence making use of harmful internet site in addition to social media messages as the main tool. We have actually obtained an email-based sample which is made to look like as it was sent by Apple. The message components will certainly include elements that might be mistaken genuine data:
- Consumer ID.
- Invoice data.
- Day.
The message motions to the targets that a repayment by means of Apple has actually been made pricing quote randomly-generated locations such as client in addition to order ID and also the day of completion. This rip-off is regarded extremely efficient as Apple negotiations are generally made use of in some locations and also individuals could not comprehend that this is a frauds notification. The e-mail may put web links to various end web pages. Several of the possible ones include the following:
Fake Login and Info Filling Up Pages— The victims can be sent to fake Apple login websites where the victims are requested to enter in their Apple ID credentials. The pages can be developed to look just like the genuine ones along with the only distinction can be the domain name or security certificate. As quickly as the details is gone into the cyberpunk motorists will absolutely have the ability to take control of the accounts. This makes it practical to execute both monetary abuse and also identification break-in.
Infection Downloads— The other possible objective is to provide an unsafe haul using amongst the links found in the e-mails. It can be any of the preferred infection kinds: miners, Trojans, ransomware as well as also and so on.
Advertisements— The different other viable result is to direct the targets to a website with intrusive advertisements. For each click an earnings of various cents will certainly be produced the motorists. Larger tasks can generate an excellent income for the criminal collective routing such strikes.

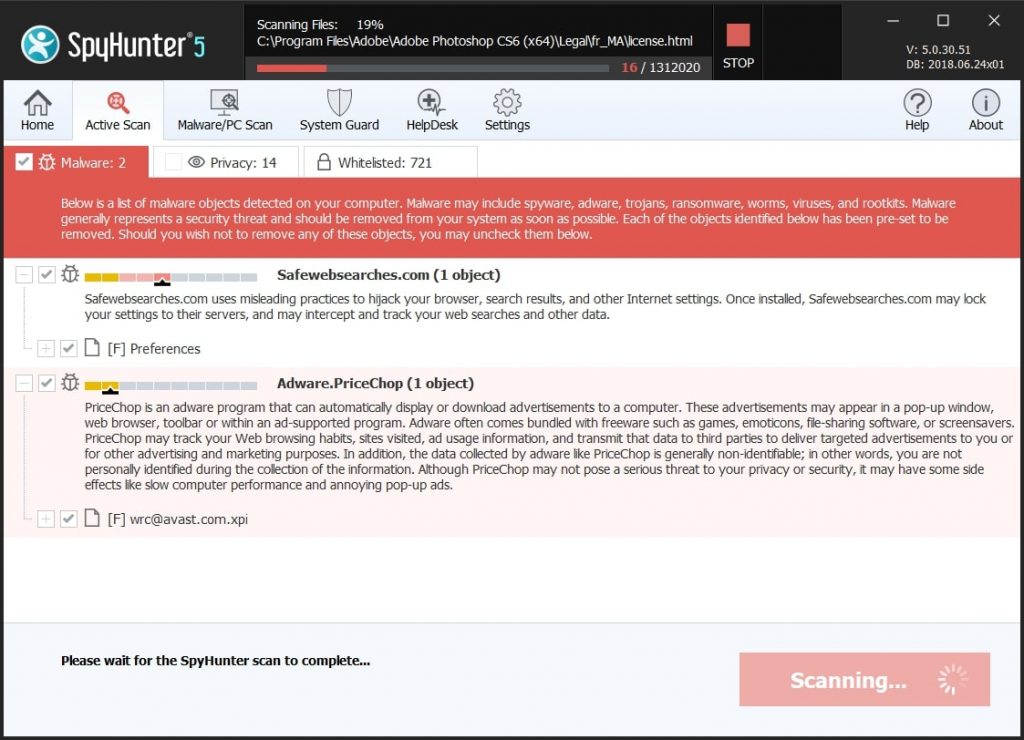
How to Remove Voodoosrc from Your Mac
If you want to remove the Voodoosrc Rip-off from your computer system, we highly recommend that you follow the removal instructions uploaded under this blog post. They have been generated with the main point In mind to assist you remove this virus either by hand or automatically. Be motivated that according to experts the best way to attempt and also do away with the software program that is creating the Voodoosrc Scamming pop-ups is to make use of a cutting-edge anti-malware software application. Such program is created with the suggestion in mind to totally check your computer system as well as also try to get rid of any type of type of traces of undesirable programs while securing your computer system versus future infections also.
Steps to Prepare Before Removal:
Before starting to follow the steps below, be advised that you should first do the following preparations:
- Backup your files in case the worst happens.
- Make sure to have a device with these instructions on standy.
- Arm yourself with patience.
- 1. Scan for Mac Malware
- 2. Uninstall Risky Apps
- 3. Clean Your Browsers
Step 1: Scan for and remove Voodoosrc files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Voodoosrc, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Quick and Easy Mac Malware Video Removal Guide
Bonus Step: How to Make Your Mac Run Faster?
Mac machines maintain probably the fastest operating system out there. Still, Macs do become slow and sluggish sometimes. The video guide below examines all of the possible problems that may lead to your Mac being slower than usual as well as all of the steps that can help you to speed up your Mac.
Step 2: Uninstall Voodoosrc and remove related files and objects
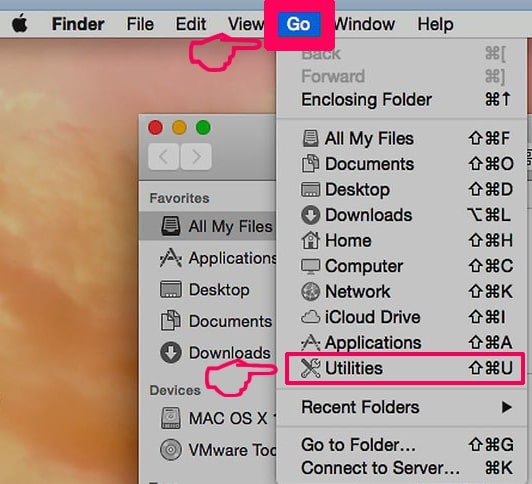
1. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on “Go” and then click “Utilities”, like the image below shows:
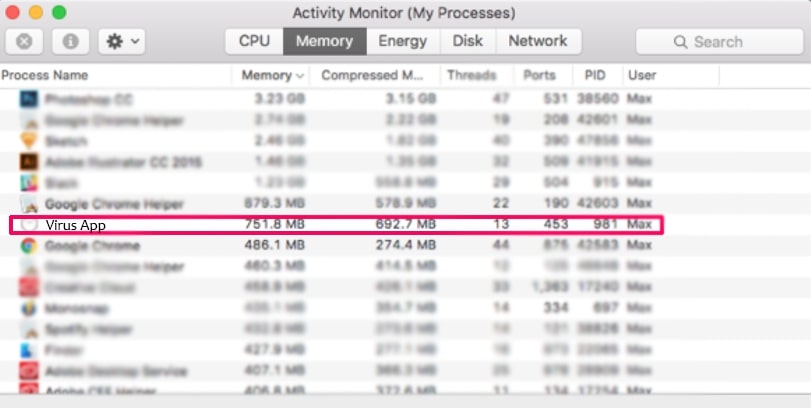
2. Find Activity Monitor and double-click it:

3. In the Activity Monitor look for any suspicious processes, belonging or related to Voodoosrc:
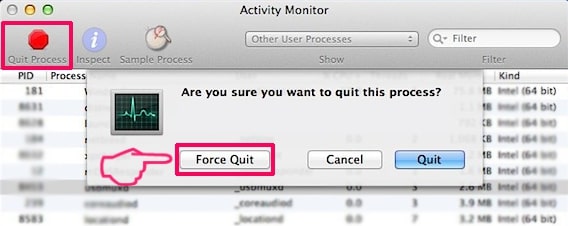
4. Click on the "Go" button again, but this time select Applications. Another way is with the ⇧+⌘+A buttons.
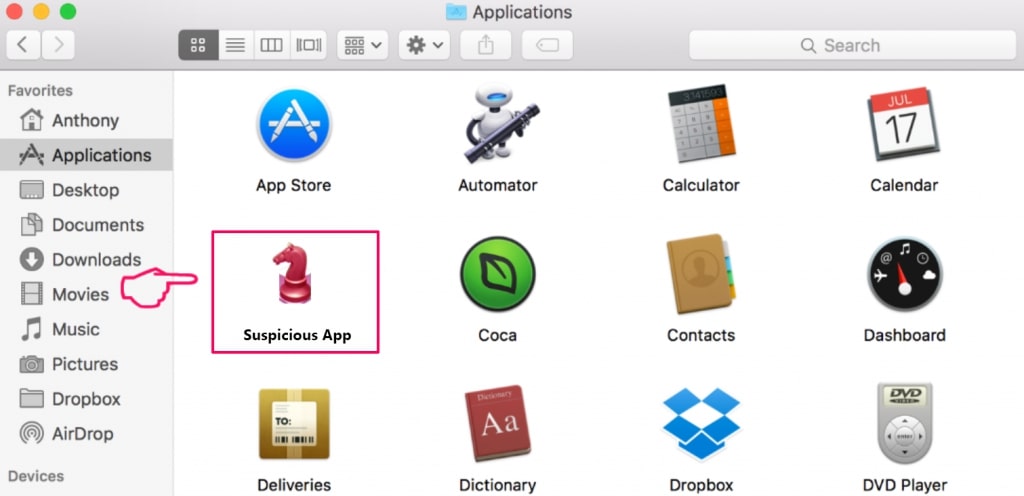
5. In the Applications menu, look for any suspicious app or an app with a name, similar or identical to Voodoosrc. If you find it, right-click on the app and select “Move to Trash”.
6. Select Accounts, after which click on the Login Items preference. Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Voodoosrc. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
7. Remove any leftover files that might be related to this threat manually by following the sub-steps below:
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Voodoosrc via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
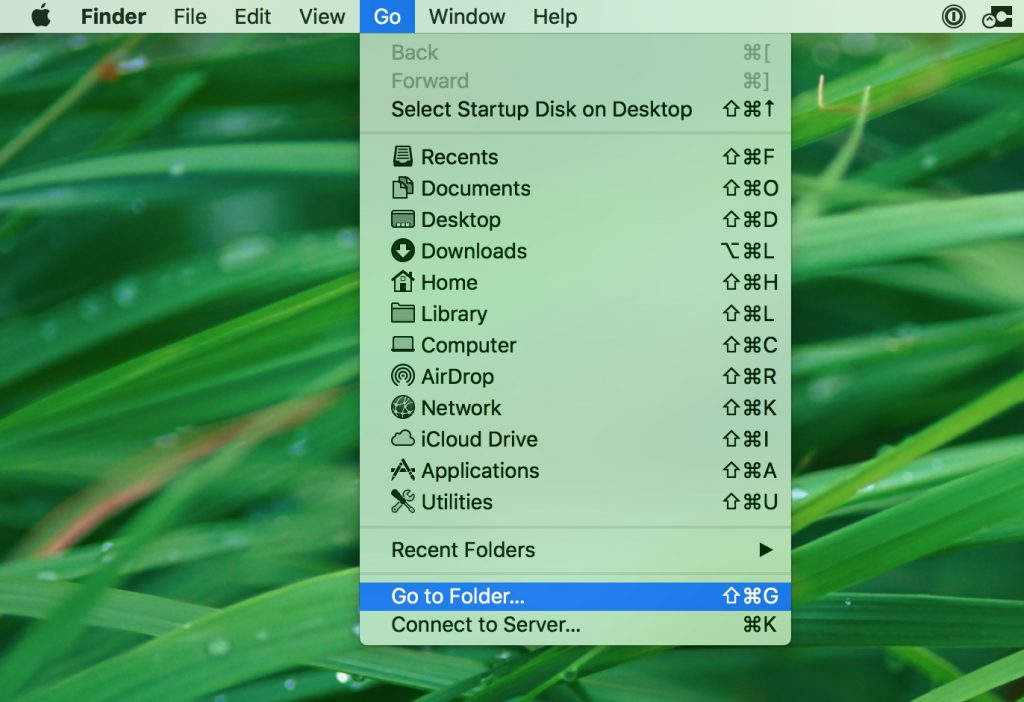
1. Click on "Go" and Then "Go to Folder" as shown underneath:
2. Type in "/Library/LauchAgents/" and click Ok:
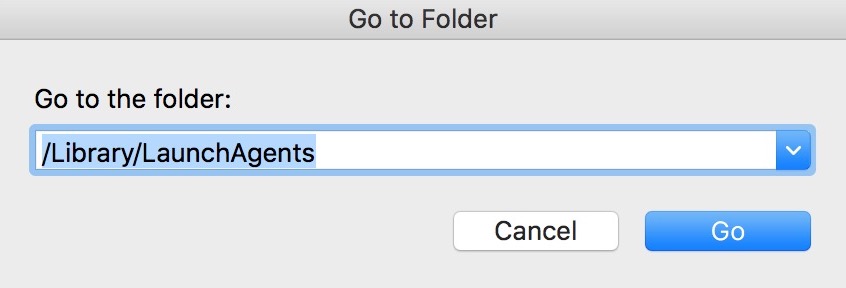
3. Delete all of the virus files that have similar or the same name as Voodoosrc. If you believe there is no such file, do not delete anything.
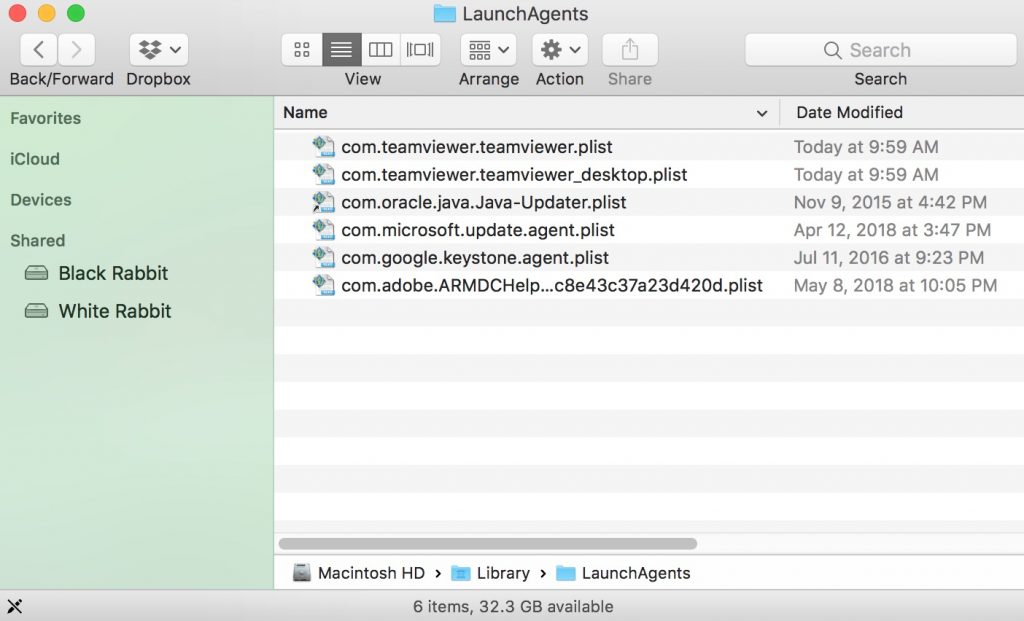
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
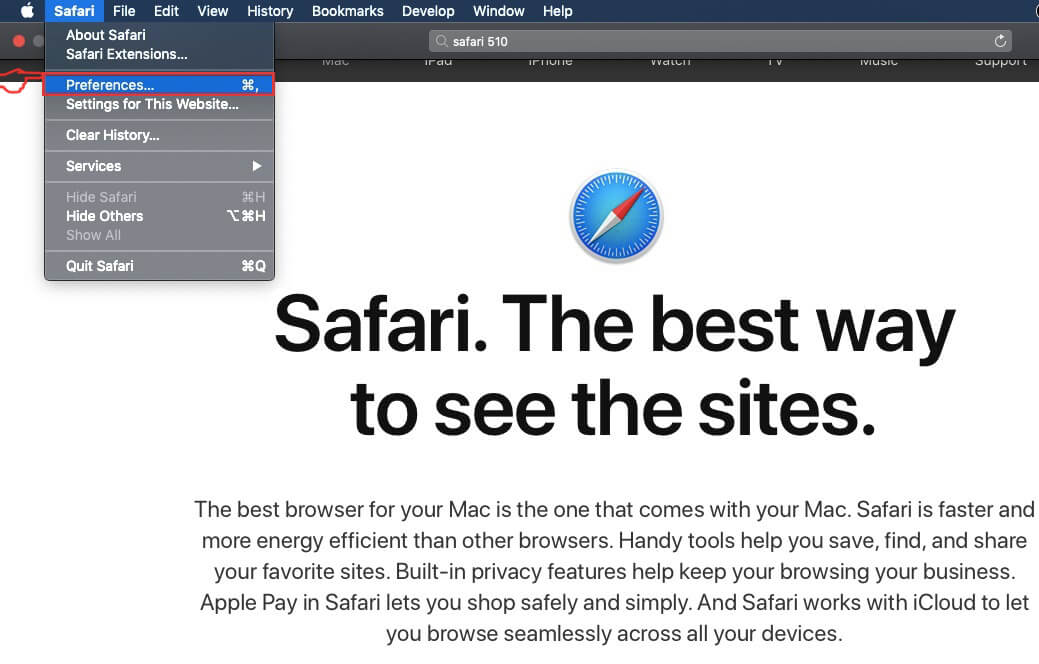
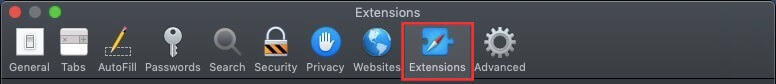
Step 3: Remove Voodoosrc – related extensions from Safari / Chrome / Firefox
Voodoosrc-FAQ
What is Voodoosrc on your Mac?
The Voodoosrc threat is probably a potentially unwanted app. There is also a chance it could be related to Mac malware. If so, such apps tend to slow your Mac down significantly and display advertisements. They could also use cookies and other trackers to obtain browsing information from the installed web browsers on your Mac.
Can Macs Get Viruses?
Yes. As much as any other device, Apple computers do get malware. Apple devices may not be a frequent target by malware authors, but rest assured that almost all of the Apple devices can become infected with a threat.
What Types of Mac Threats Are There?
According to most malware researchers and cyber-security experts, the types of threats that can currently infect your Mac can be rogue antivirus programs, adware or hijackers (PUPs), Trojan horses, ransomware and crypto-miner malware.
What To Do If I Have a Mac Virus, Like Voodoosrc?
Do not panic! You can easily get rid of most Mac threats by firstly isolating them and then removing them. One recommended way to do that is by using a reputable malware removal software that can take care of the removal automatically for you.
There are many Mac anti-malware apps out there that you can choose from. SpyHunter for Mac is one of the reccomended Mac anti-malware apps, that can scan for free and detect any viruses. This saves time for manual removal that you would otherwise have to do.
How to Secure My Data from Voodoosrc?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your e-mail passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activiites with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these reccomendations, your network and Apple devices will become significantly more safe against any threats or information invasive software and be virus free and protected in the future too.
More tips you can find on our MacOS Virus section, where you can also ask any questions and comment about your Mac problems.
About the Voodoosrc Research
The content we publish on SensorsTechForum.com, this Voodoosrc how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific macOS issue.
How did we conduct the research on Voodoosrc?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of Mac threats, especially adware and potentially unwanted apps (PUAs).
Furthermore, the research behind the Voodoosrc threat is backed with VirusTotal.
To better understand the threat posed by Mac malware, please refer to the following articles which provide knowledgeable details.