The xHelper Android Trojan which is one of the dangerous threats has gained widespread popularity among hackers and has become among the top 10 viruses for Google’s operating system.
It can hide itself from security software or the user and is used to deliver other threats to the compromised computers.
xHelper Android Trojan Rises To The Top 10 Of Mobile Threats
The xHelper Android Trojan is a dangerous threat for Google’s mobile operating system which was first detected in the beginning of the year. What we know about the hackers behind is that they have created the Trojan with the intention of deploying other threats via it. There are two main versions of it which feature distinct infection mechanisms and behavior.
The main method of infection relies on scamming the victims into installing malware applications on their Android devices. There are several ways through which this can be achieved — either by uploading counterfeit apps on the official repository (the Google Play Store) by using fake developer credentials or creating and maintaining fake hacker-made sites. A common technique used by most criminals is to impersonate well-known applications or create elaborate descriptions for special hacker-made programs. They are usually advertised as legitimate and useful apps, the hackers can also post fake user reviews. The differences between the two versions lies within the way they work on the compromised hosts:
- First xHelper Android Trojan — As soon as the app is installed on the mobile devices it will add its icon on the launcher. The malware will begin to spam the victim users with dangerous advertisements placed in various places, one of them being the notification bar. The captured samples so far shows that the displayed ads will be for trial or paid software products and services. This technique shows that the hackers use this in order to make money from advertising.
- Second xHelper Android Trojan — This is a stealth variant which will execute itself in several different stages. It can be used to deliver other threats to the host in a stealth manner. The victims will probably not notice that they are infected with it. Potential malware infections can be spotted by looking out for a “xhelper” entry in the “App Info” menu of the delivered payload. The main engine is delivered to the victim hosts in a heavily obfuscated file.
According to the known information the majority of the victims are located in the United States, it is suspected that the controllers operate from the country as well. Already made infections will be very difficult to remove, numerous user reports indicate that the infections are very persistent and can even bypass many of the professional-grade mobile security software.
Preparation before removal of malware.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Turn off your phone until you know how bad is the virus infection.
- Open these steps on another, safe device.
- Make sure to take out your SIM card, as the virus could corrupt it in some rare cases.
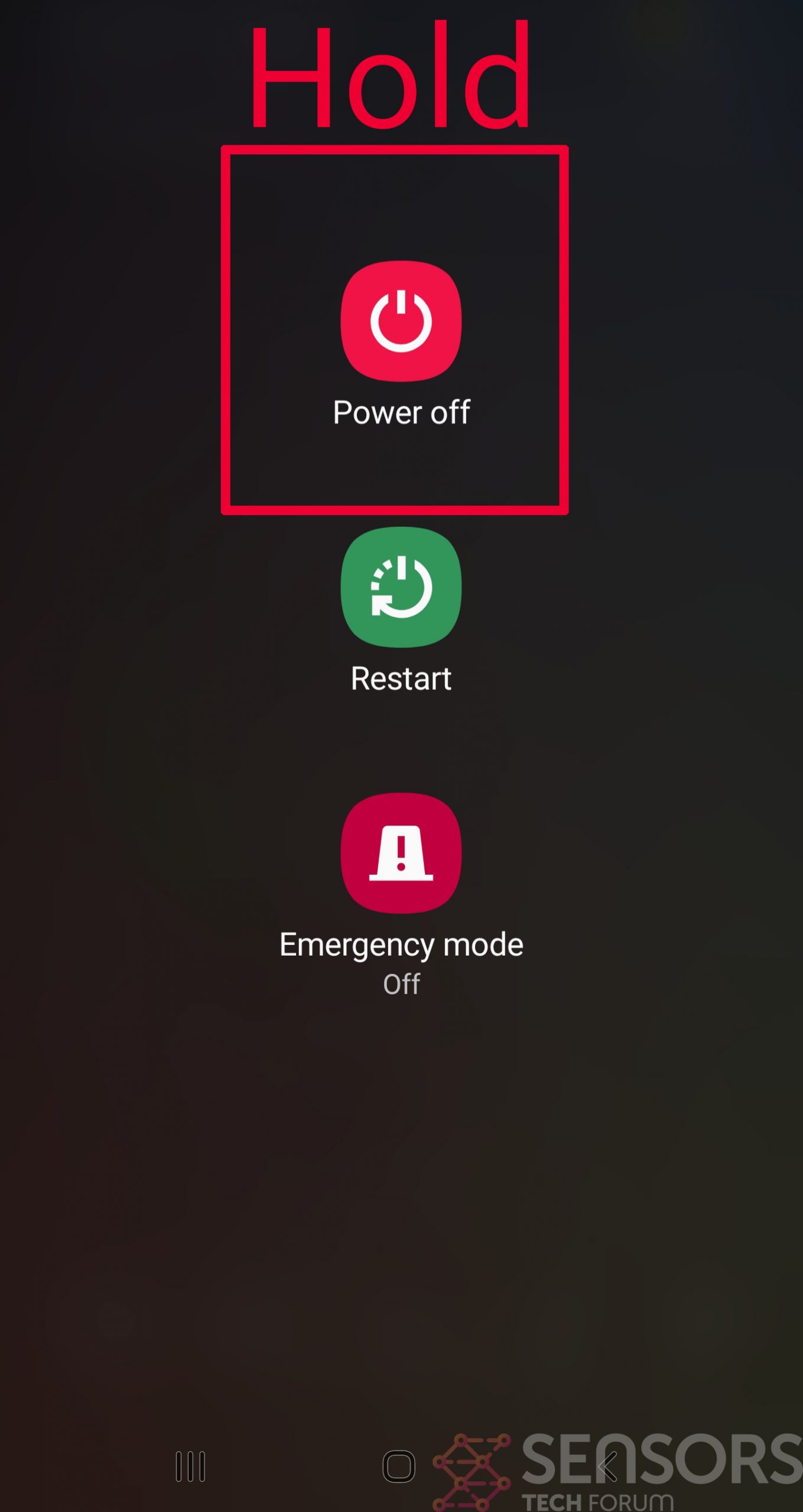
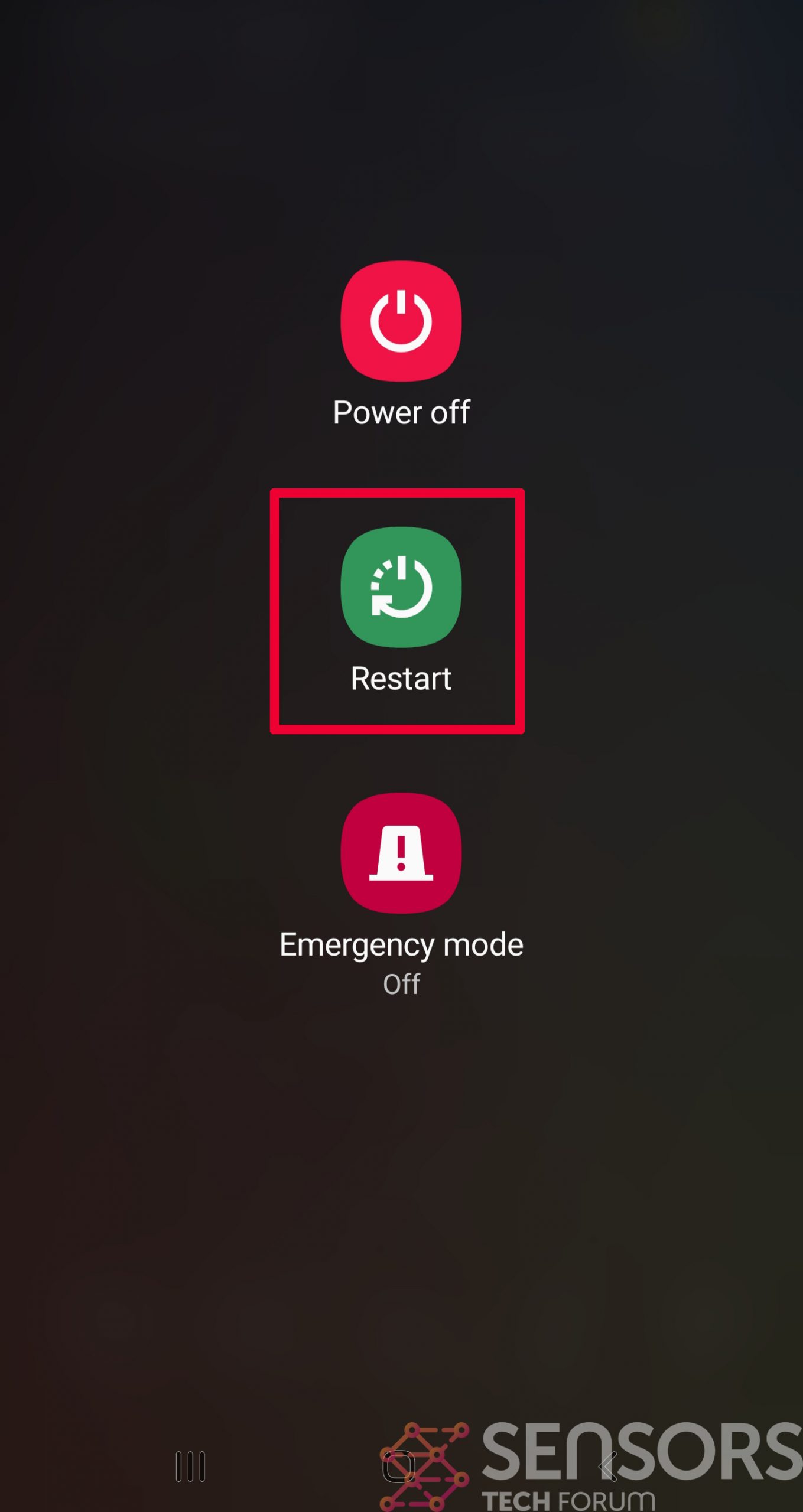
Step 1: Shut Down your phone to win some time
Shutting down your phone can be done by pressing and holding its power button and choosing shut down.
In case the virus does not let you do this, you can also try to remove the battery.
In case your battery is non-removable, you can try to drain it as fast as possible if you still have control over it.
Notes: This gives you time to see how bad the situation is and to be able to take out your SIM card safely, without the numbers in it to be erased. If the virus is on your computer, it is espeically dangerous to keep the sim card there.
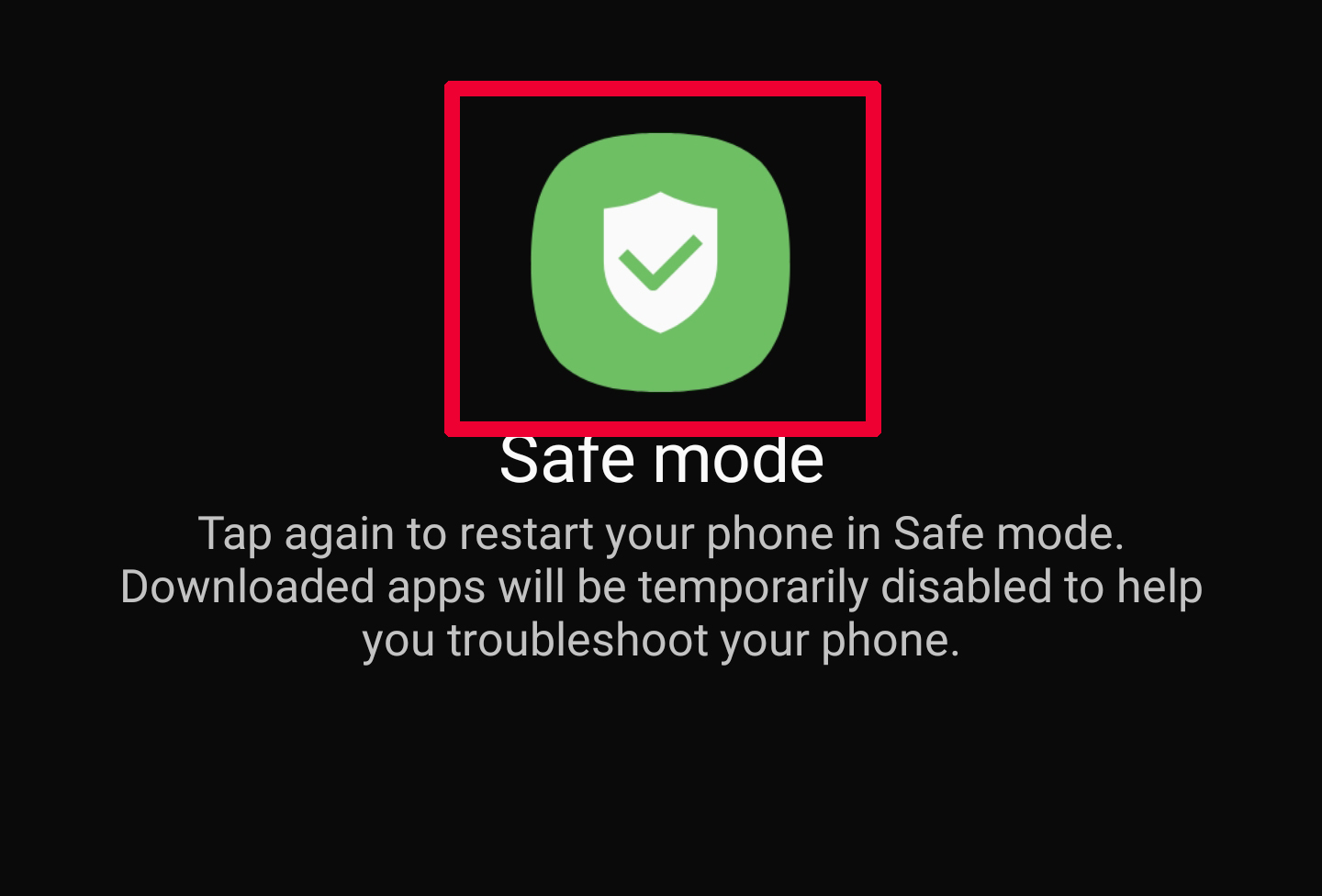
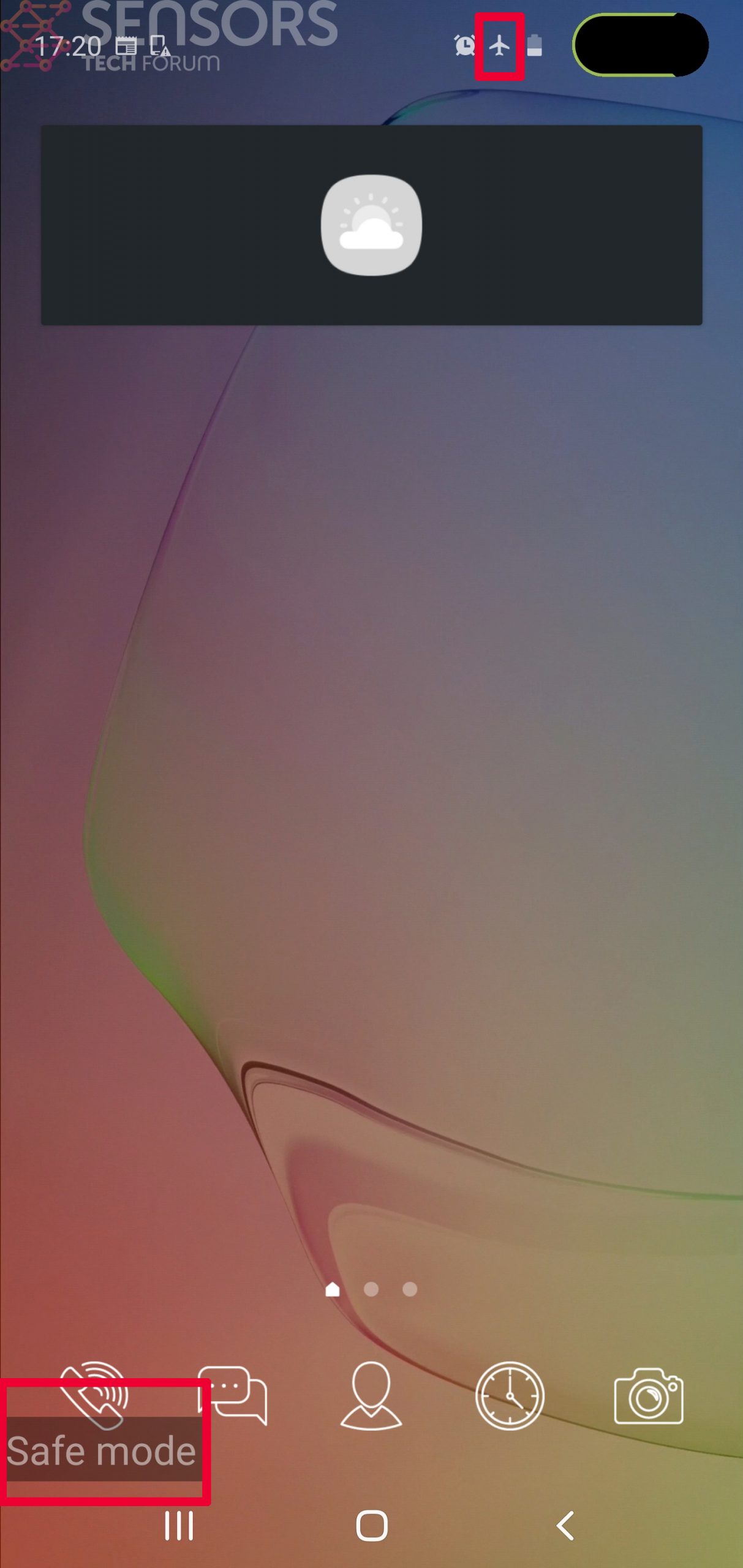
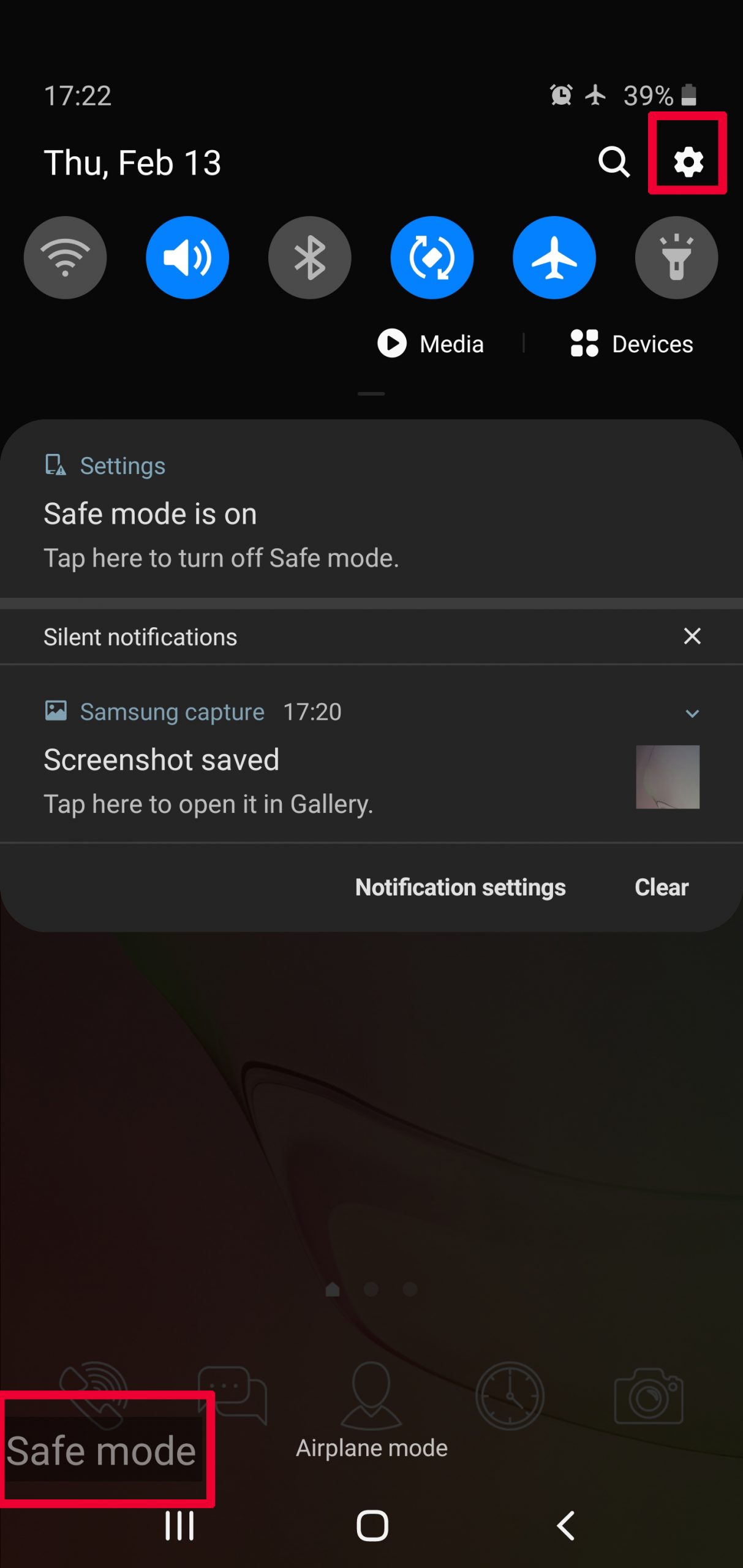
Step 2: Turn on Safe Mode of your Android device.
For most Android devices, switching to Safe Mode is the same. Its done by following these mini-steps:
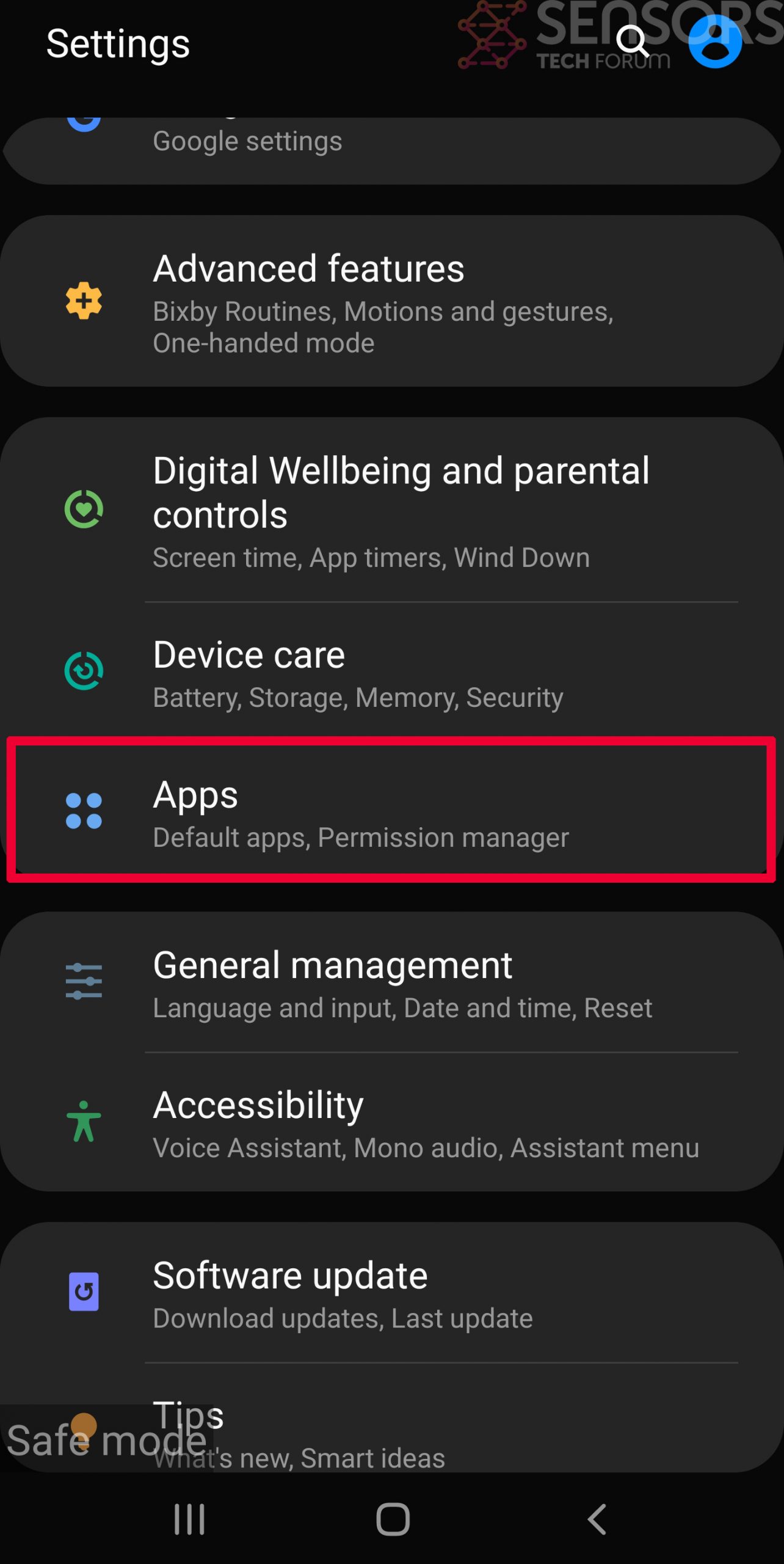
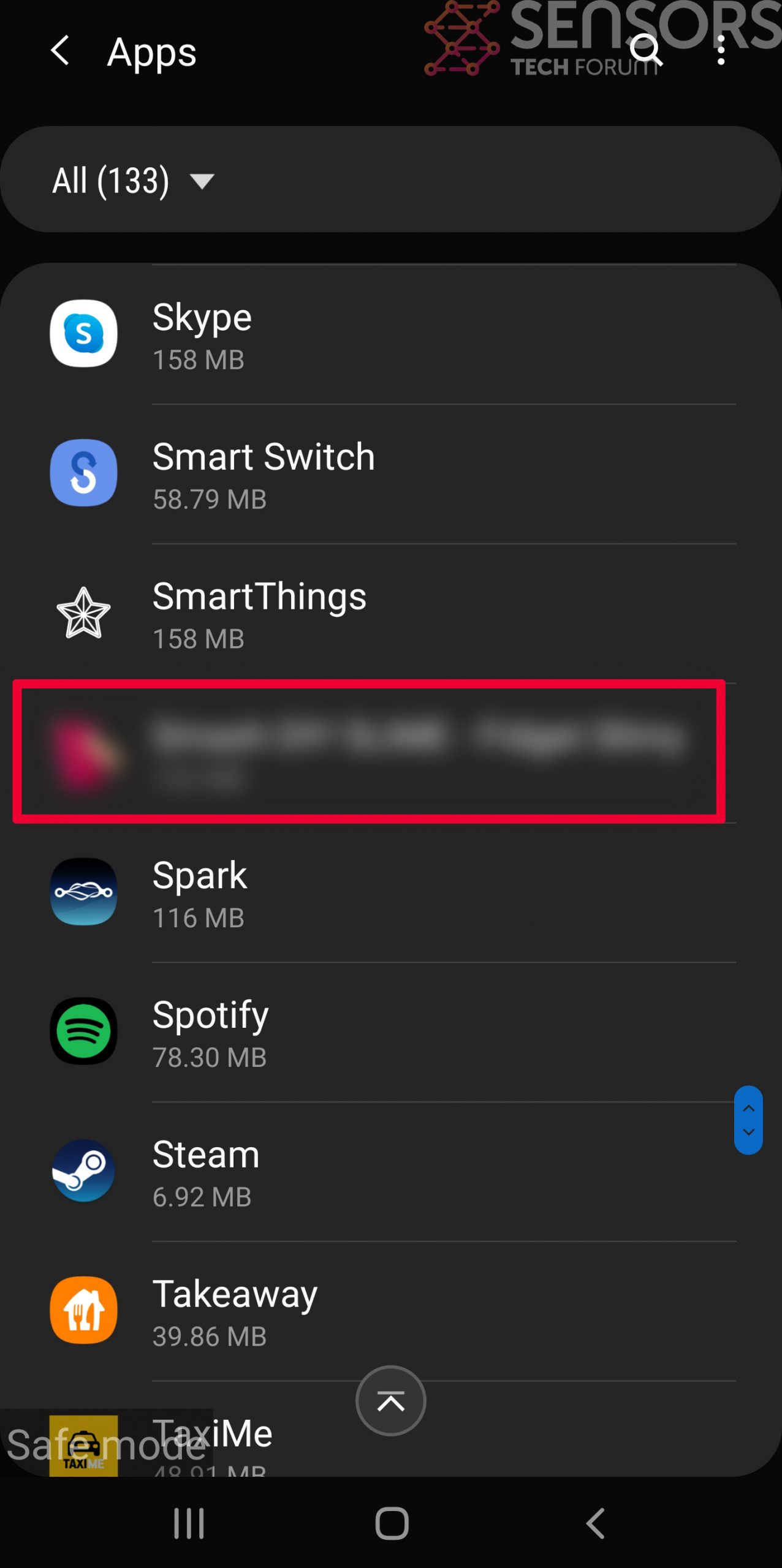
Step 3: Eliminate the App that Your Believe is the Virus
Usually Android viruses get masked in the form of applications. To eliminate apps, follow these mini-steps:

Step 4: Find Hidden Virus Files on Your Android Phone and Remove Them
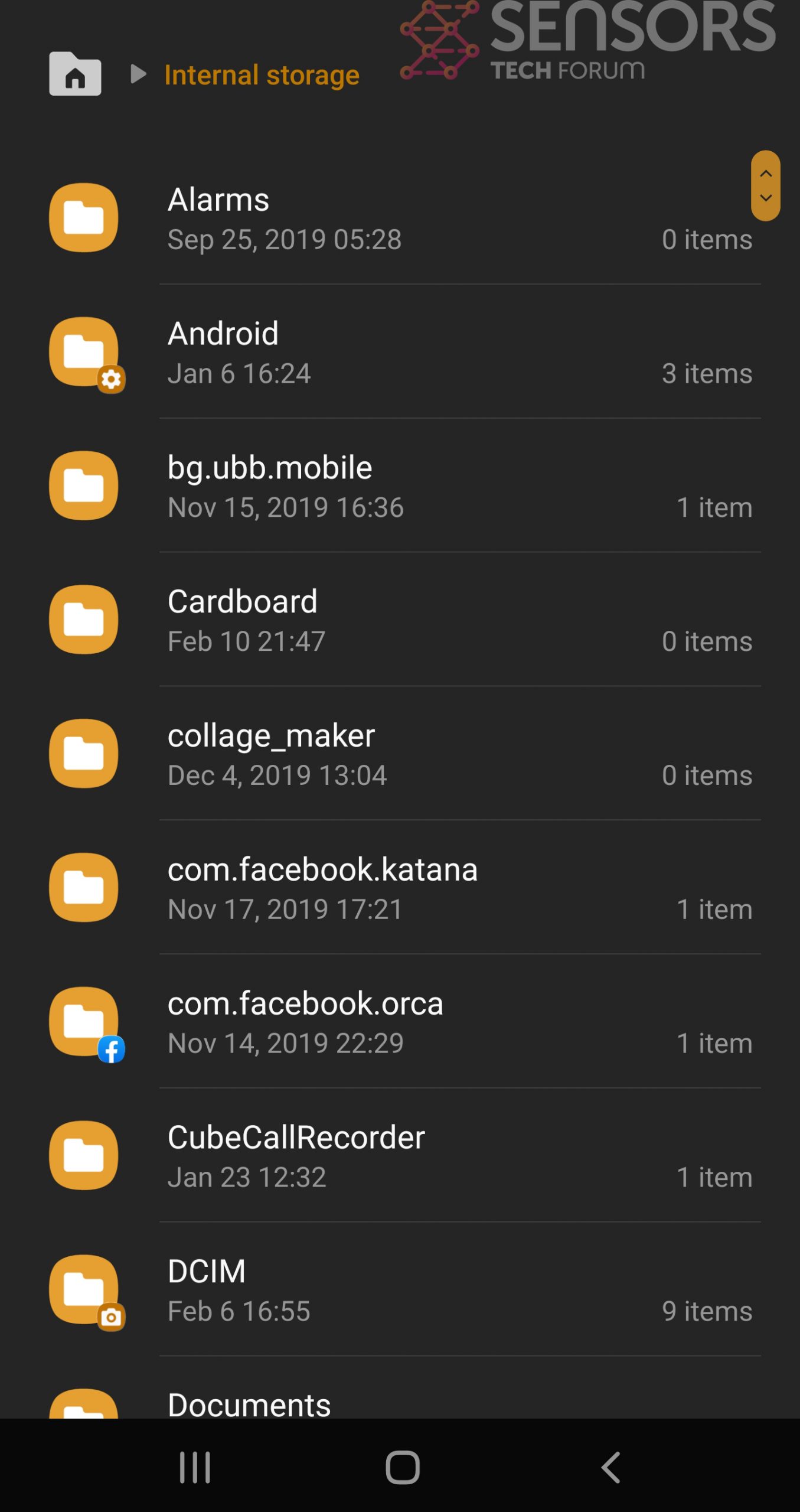
Simply locate the virus and hold-tap on the virus file to delete it.