
Most Secure VPNs for USA (2021)
RATING ENCRYPTION DNS Leak Protection LOGGING SERVERS 1 Hotspot ShieldSee Review AES 256-bit, IKEv2/IPsec, OpenVPN No Logging 2500 across 25 countries

RATING ENCRYPTION DNS Leak Protection LOGGING SERVERS 1 Hotspot ShieldSee Review AES 256-bit, IKEv2/IPsec, OpenVPN No Logging 2500 across 25 countries

Cybercriminals are constantly looking for ways to monetize their malicious campaigns as quickly as possible. Targeting retail websites has proven quite profitable, and it’s no surprise that this type of attack, shortly known as formjacking, has been prevalent in 2018.…
A security team has announced the discovery of a critical vulnerability found in WinRAR, one of the most popular archive and compression tools used by computer users. The issue is estimated to have been a part of the software for…

The Azorult Trojan is a dangerous weapon used against computer users worldwide. It infects mainly via infected software installers. Our article gives an overview of its behavior according to the collected samples and available reports, also it may be helpful…

This blog post has been created to best explain what is the Winlog.exe Miner malware and how you can remove it completely from your computer. A new miner virus using the Winlog.exe process to mine computer has been detected by…

This article will help you remove Routersupports.co fully. Follow the tech support scam removal instructions provided at the end of this article. Routersupports.co is a website which is connected to a tech support scam and hosts it on that Web…
In this article, you will find more information about .promos files virus as well as a step-by-step guide on how to remove malicious files from an infected system and how to potentially recover files encrypted by this ransomware. In case…

This article will aid you to remove .aqva Ransomware. Follow the ransomware removal instructions provided at the end of the article. .aqva Ransomware is one that encrypts your data and demands money as a ransom to get it restored. Files…
This article will help you to remove Searchv.oliverto.com browser hijacker efficiently. Follow the redirect removal instructions given at the end of the article. Searchv.oliverto.com.com is a typical browser hijacker redirect. The website will redirect you to its own search engine…
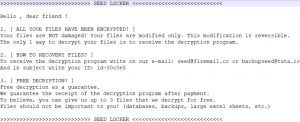
This article has been created with the main idea to explain what is SEED LOCKER ransomware and how you can remove it from your computer and try to restore .seed encrypted files. A new ransomware virus, called SEED LOCKER was…

Global online and offline surveillance seems to have become a permanent part of life. And ironically, we can’t seem to raise voice against it or take any other countermeasure accordingly. Or, can we? Before we proceed to the counter-tactics to…

The ServHelper Trojan is a dangerous weapon used against computer users worldwide. It infects mainly via phishing email messages. Our article gives an overview of its behavior according to the collected samples and available reports, also it may be helpful…
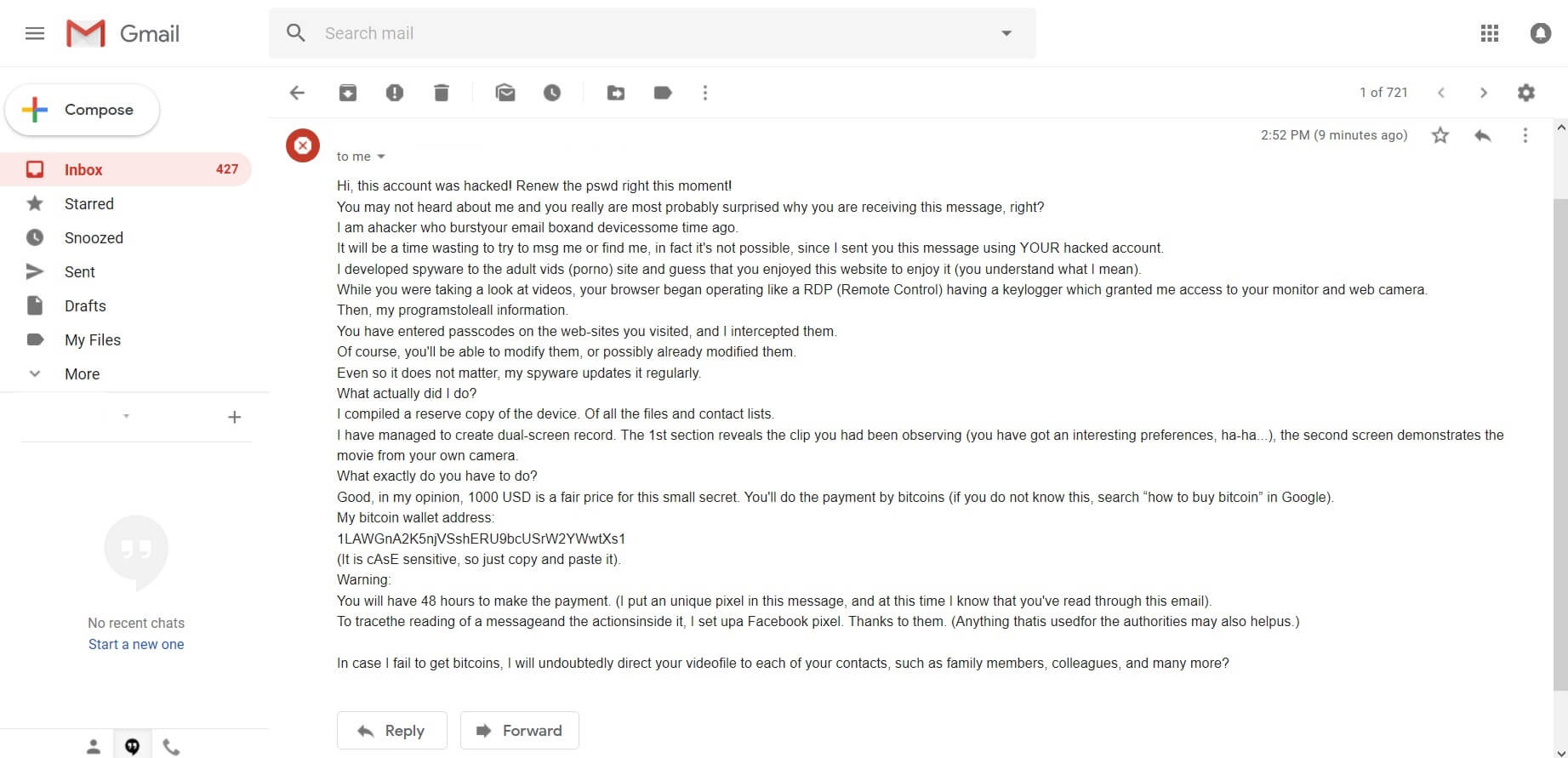
The “This account was hacked” scam has been circling the Internet these past few days, trying to scare people that hackers made a fake video of them watching porn. People receiving the message are demanded to pay a ransom fee…
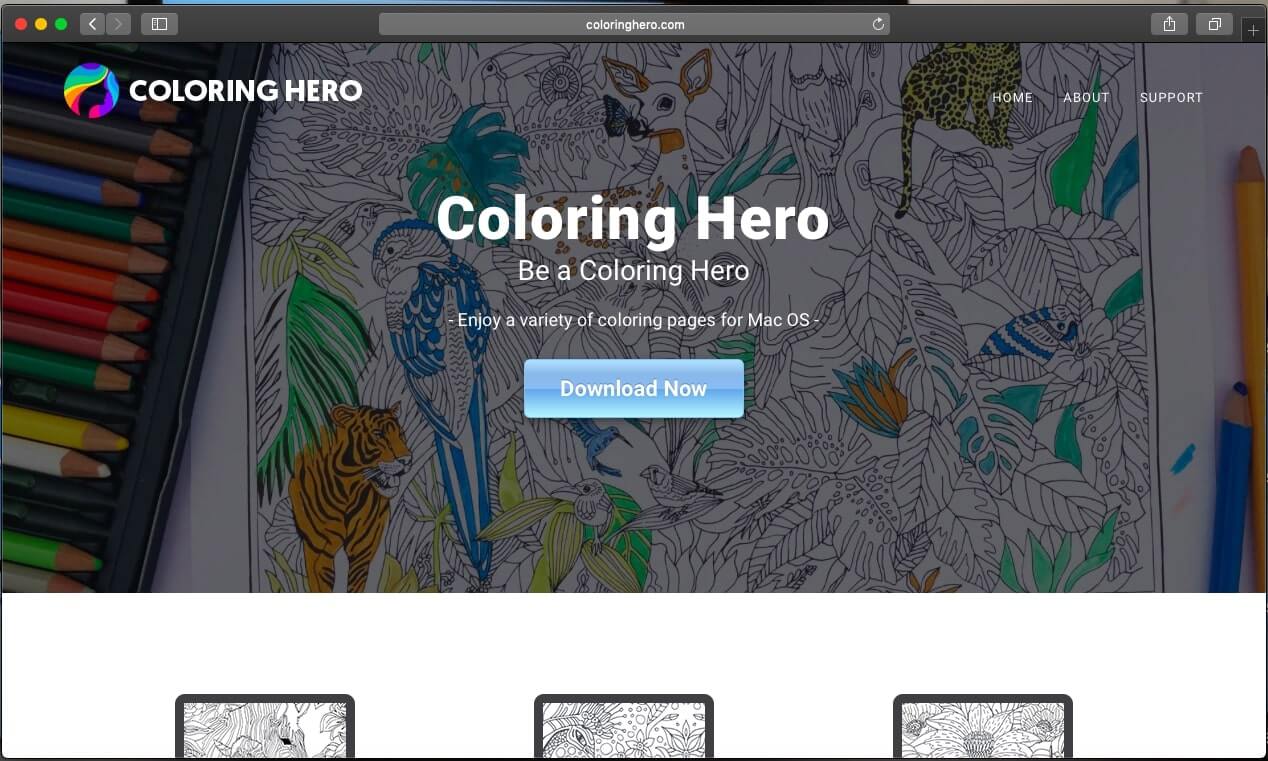
This article aims to help you with the removal of the suspicious program Coloring Hero from the affected system. Follow the detailed guide at the end to get rid of it in full. Coloring Hero is promoted as an app…
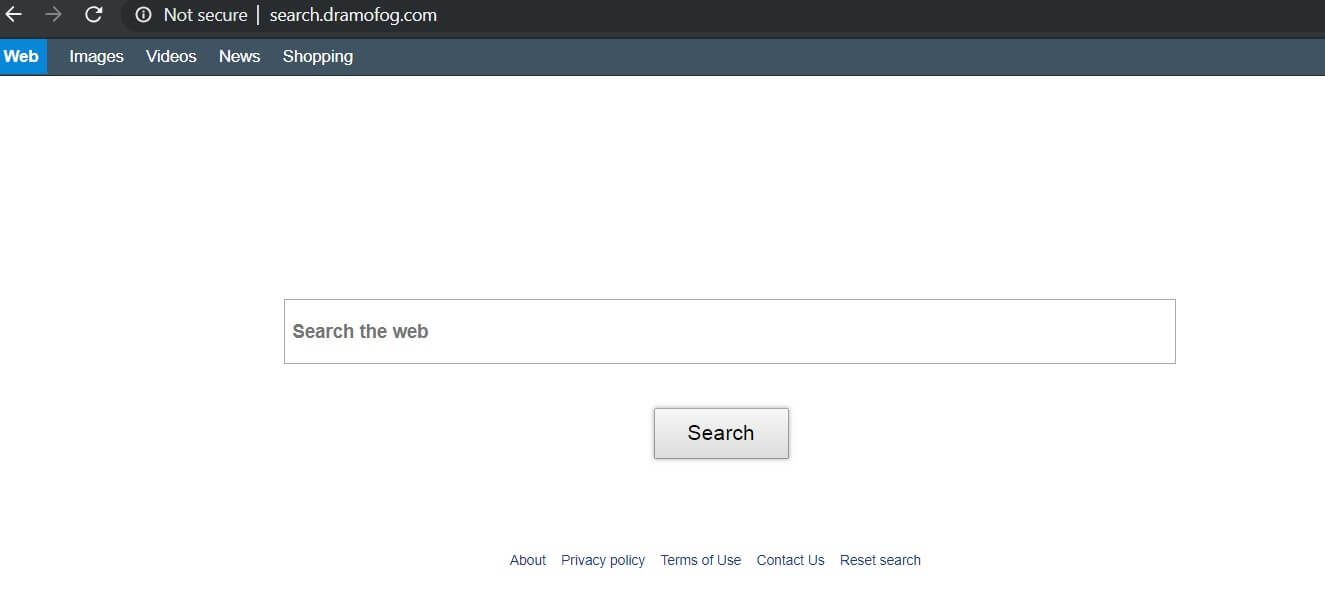
This article will help you to remove Search.dramofog.com browser hijacker efficiently. Follow the redirect removal instructions given at the end of the article. Search.dramofog.com.com is a typical browser hijacker redirect. The website will redirect you to its own search engine…

A recent report carried out by Nightwatch Cybersecurity indicates that a third-party Android app with Facebook API access was copying user data into storage outside of Facebook. Moreover, the data was stored insecurely in two locations. Android App with Facebook…

The Rietspoof Malware is a dangerous weapon used against computer users worldwide. It infects mainly via hacker social network profiles. Our article gives an overview of its behavior according to the collected samples and available reports, also it may be…

This article has been created in order to help explain what is the Microsoft License has expired tech support scam and how you can remove it from your computer effectively. A new computer voice type of phone call and error…
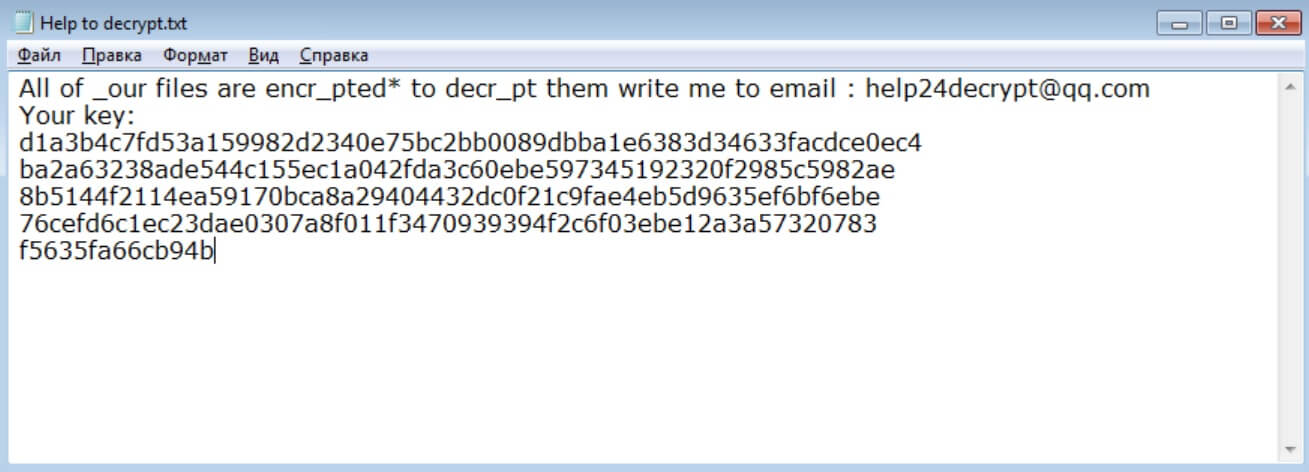
This article will aid you to remove .help24decrypt@qq.com files virus efficiently. Follow the ransomware removal instructions given at the end of the article. .help24decrypt@qq.com files virus is from the FenixLocker ransomware family. The virus encrypts your files and demands money…
In this article, you will find more information about .X3 files virus as well as a step-by-step guide on how to remove malicious files from an infected system and how to potentially recover files encrypted by this ransomware. .X3 files…