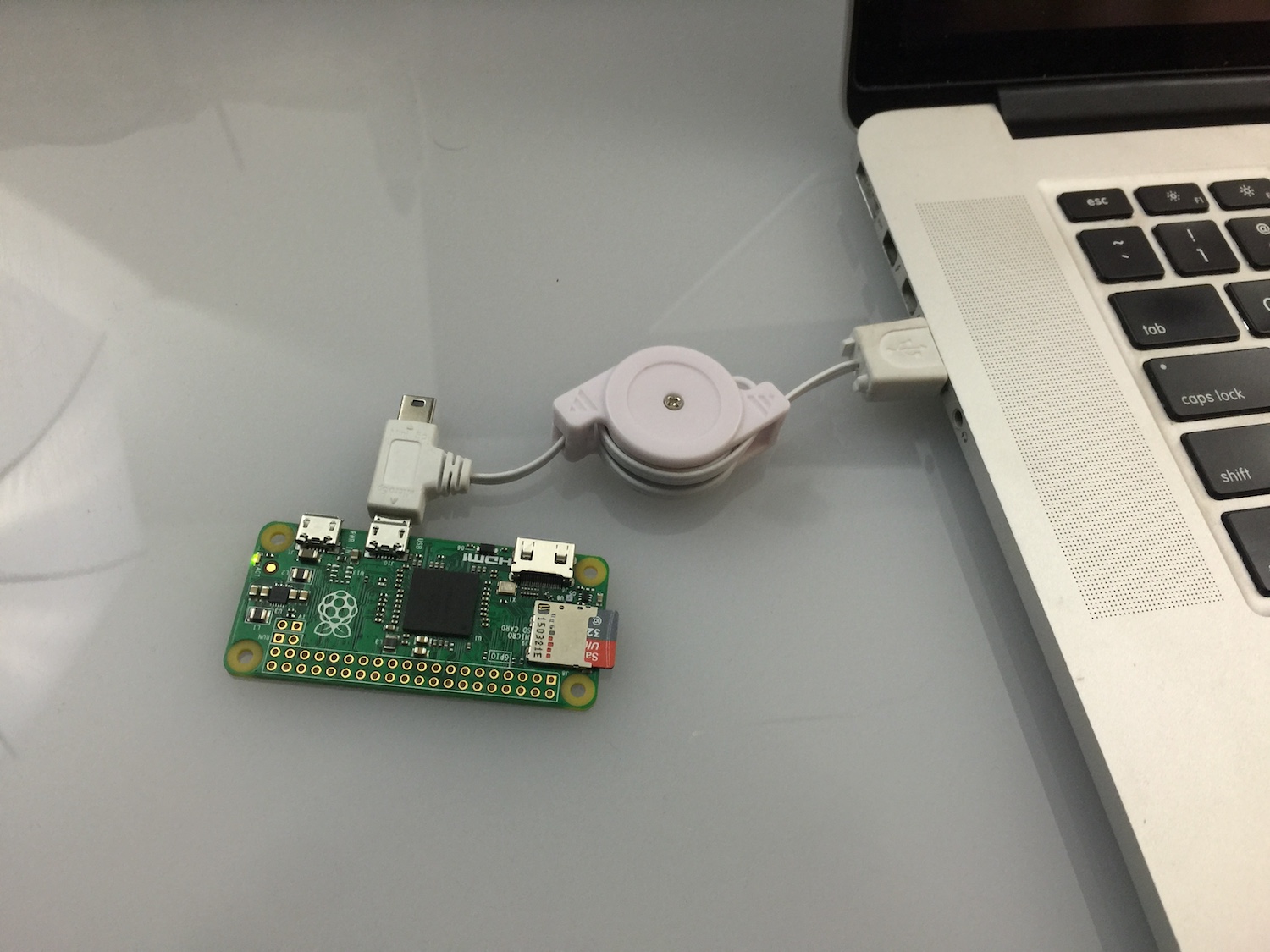
The exploit tool arsenal just got bigger. Meet PoisonTap, a tool created by the infamous Samy Kamkar. PoisonTap is designed to run freely available software on a $5 Raspeberry Pi Zero device. But how does it work?
The tiny tool only needs to be plugged into a computer’s USB slot. Then it will intercept all encrypted Web traffic, authentication cookies included. These cookies are needed to access private accounts. Once this is done, PoisonTap will send the data to an attacker’s server. Additionally, the tool also installs a backdoor to allow remote control over the PC owner’s browser and local network.
Why did Samy Kamkar create PoisonTap in the first place?
In a conversation with ArsTechnica he gave the following explanation:
The primary motivation is to demonstrate that even on a password-protected computer running off of a WPA2 Wi-Fi, your system and network can still be attacked quickly and easily. Existing non-HTTPS website credentials can be stolen, and, in fact, cookies from HTTPS sites that did not properly set the ‘secure’ flag on the cookie can also be siphoned.
Related: Mr. Robot Season 2 Hacks and Exploits: Master/Slave and Rubber Ducky
This is a resume of what PoisonTap is capable of:
- Emulating an Ethernet device over USB;
- Hijacking all Web traffic from the computer;
- Siphoning and storing HTTP cookies and sessions from the browser for the Alexa top 1,000,000 sites;
- Exposing the internal router to the attacker and making it remotely accessible via outbound WebSocker and DNS rebinding;
- Installing a persistent web-based backdoor in HTTP cache;
- Allowing an attacker to remotely force the user to make HTTP requests and proxy back responses via the user’s cookies on any backdoored domain;
- The tool doesn’t require the targeted computer to be unlocked. And the backdoor access remains even after the tool is removed!
- Hijacking all Web traffic from the computer;
Besides computers, home and office routers are also at risk.
Attackers can utilize PoisonTap to obtain remote access to a browser. They can also gain admin control over the connected router. Nonetheless, attackers still need to defeat password protections safeguarding the targeted router. Because of the high number of unpatched authentication flaws, this won’t be a big obstacle.
Related: Microsoft Edge Application Guard Will Protect against the Mimikatz Tool
Considering the highly privileged man-in-the-middle position the tool has, it can also install backdoors that allow access to the browser and the router. To access the browser, PoisonTap drops a mix of HTML and JavaScript in the browser cache that creates a persistent WebSocker. As for the router, the tool applies a DNS rebinding attack.
Read more about it here.