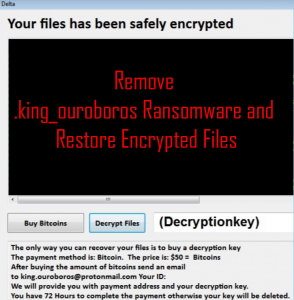
.zzz12 Files Virus – How to Remove It and Restore Your Data
This article has been created with the purpose to provide explanation on how to be able to remove the .zzz12 files virus from your computer system and then show how to try and recover files, encrypted by it. A new…