A serious issue has been identified in the Microsoft Edge and Safari browsers as they have been found to allow address bar spoofing. This vulnerability allows malicious code to redirect the users and lead to potential virus infections.
Address Bar Spoofing Vulnerability Affects Microsoft Edge and Safari
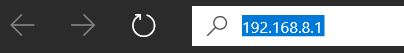
A Pakistani-based security specialist Rafay Baloch reported that both Microsoft Edge and Safari posses an address bar spoofing vulnerability. The statement was made after he tested the browsers with proof-of-concept JavaScript code. The tests indicate that upon a request from a non-existent port a race condition is triggered in the memory process which allows malicious code to spoof the address. Following the report a security advisory was assigned and the two companies were notified. The issue is tracked in CVE-2018-8383 and its description reads the following:
A spoofing vulnerability exists when Microsoft Edge does not properly parse HTTP content, aka “Microsoft Edge Spoofing Vulnerability.” This affects Microsoft Edge. This CVE ID is unique from CVE-2018-8388.
Abuse of this flaw can be be done by dangerous script interaction. A web site plugin (Adobe Flash for example) can trigger the race condition by including JavaScript code. This can be either automatic or due to user interaction. Microsoft has patched the bug the Patch Tuesday August update. According to their own research it is likely that hackers will attempt and exploit the Microsoft Edge vulnerability. There are many payload carriers that can embed JavaScript code and this is a legitimate concern.
The same problem was observed in Safari — the usual security measures can be bypassed by injecting specific code. Apple was given 90 days to fix the vulnerability however they have not patched it in due time. As a consequence details about the issue are now publicly available.
The browser itself does not allow the victims to type user data into input boxes while the pages are loading. This is the default protective measures however the proof-of-concept code clearly shows that these restrictions can be bypassed. This is done by simulating keyboard input into the spoofed page.
At the end of the address bar spoofing vulnerability the criminals can redirect the victims to a predefined hacker-controlled page. It can lead to any of these dangers:
- Malware Virus Delivery — The pages can trigger an automatic virus file delivery. Upon interacting with the malicious element the users will infect themselves with the relevant payload: ransomware, Trojan, miner and etc.
- Script Redirect — The spoof code can be used to make the users visit an ad-infested page. This can also trigger the opening of banners, pop-ups, redirects and etc. Every visit will result in the income generation for the operators.
- Miner Infection — In several cases the end goals are cryptocurrency miner infections. They take advantage of the available system resources in order to carry out complex calculations. When they are successfully completed by the hosts digital currency will automatically be credited to the hacker operators.
So far major incidents have not been reported. Once again we highly recommend that all Microsoft Windows users will apply the latest security updates and that Apple will release a patch as soon as possible to address the vulnerability.


